Best Practices for Key Rotation in Healthcare Clouds
Post Summary
In healthcare, protecting sensitive data like patient records and billing information stored in the cloud is critical. Cryptographic keys are essential for securing this data, but they must be updated regularly to minimize risks. This practice, known as key rotation, prevents potential breaches and ensures compliance with regulations like HIPAA and NIST. Here's what you need to know:
-
Why Rotate Keys?
- Protects data if a key is compromised.
- Limits the risk of attacks by reducing the time a single key is in use.
- Meets regulatory requirements for secure key management.
-
Key Rotation Strategies:
- Time-Based: Rotate keys on a fixed schedule (e.g., every 90 days).
- Usage-Based: Rotate after encrypting a set volume of data.
- Event-Driven: Trigger rotation after incidents like breaches or when upgrading encryption methods.
-
Automation:
Use tools like AWS KMS, Azure Key Vault, or Google Cloud KMS to automate key rotation, reducing errors and ensuring consistent adherence to policies. -
Storage Best Practices:
Store cryptographic keys securely using hardware security modules (HSMs) or cloud-native key management services. Separate key access from data access to reduce risks. -
Monitoring and Auditing:
Log all key rotation activities. Use monitoring tools to detect anomalies and conduct regular audits to ensure compliance. -
Integrate with Risk Management:
Link key rotation to broader healthcare risk management platforms to identify vulnerabilities and improve security practices.
Regular key rotation is a cornerstone of healthcare cloud security, reducing risks and ensuring compliance. Automating the process and integrating it with monitoring systems helps maintain seamless operations while safeguarding sensitive data.
Flexible automatic key rotation with AWS Key Management Service | Amazon Web Services
sbb-itb-535baee
Setting the Right Key Rotation Frequency
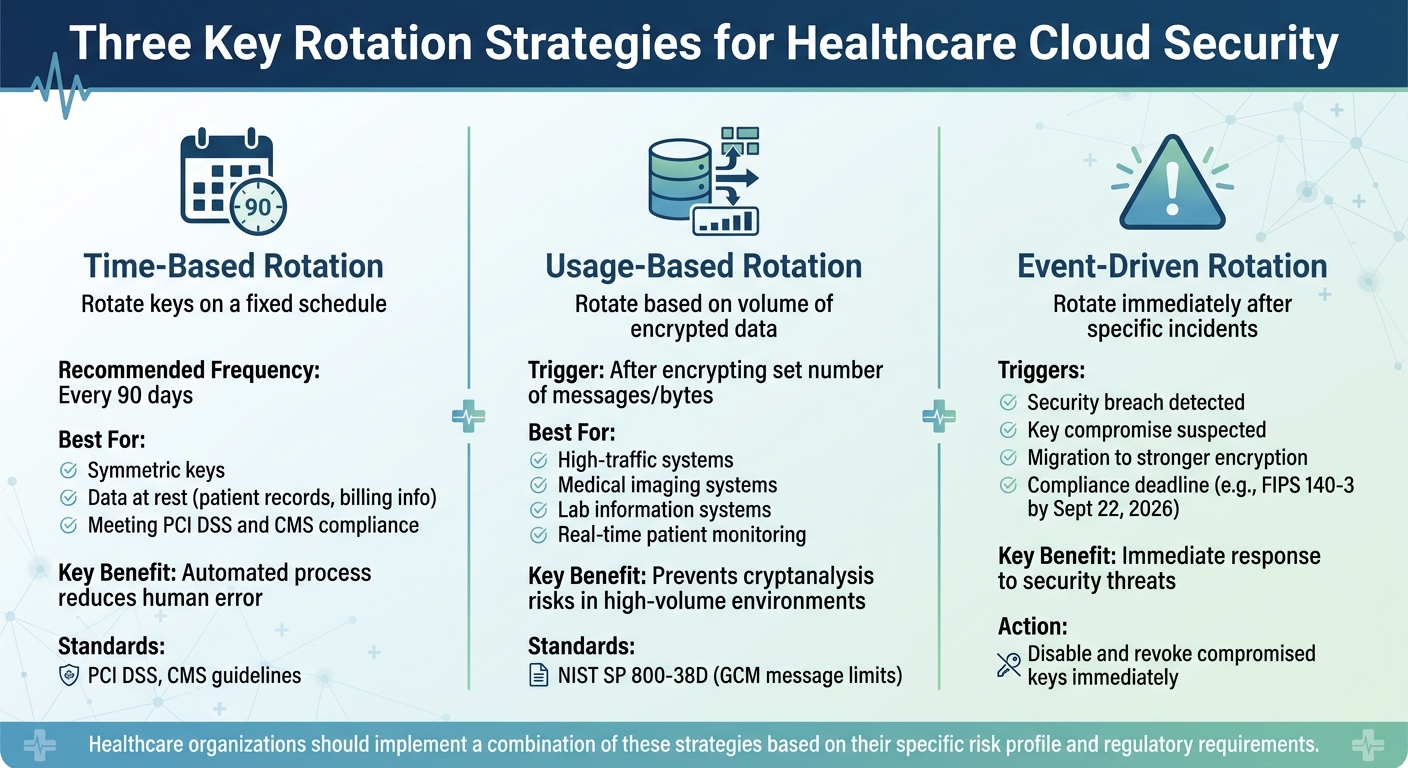
Three Key Rotation Strategies for Healthcare Cloud Security
Figuring out how often to rotate cryptographic keys is a balancing act. On one hand, you want strong security; on the other, you need to account for operational demands. For healthcare organizations, this decision involves considering regulatory requirements, data volumes, and potential security risks. To help navigate this, we’ll explore three approaches to key rotation - time-based, usage-based, and event-driven - that can align security goals with practical needs.
Time-Based Key Rotation
Rotating keys on a set schedule is a straightforward way to maintain security and meet compliance requirements. Many standards, like PCI DSS and CMS guidelines, recommend rotating keys every 90 days to strike a balance between security and operational simplicity [1][2]. This approach is particularly effective for symmetric keys used to encrypt data at rest, such as patient records or billing information stored in cloud databases.
The best part? Automating time-based rotations reduces the chance of human error while ensuring sensitive healthcare data remains protected. This makes it an ideal choice for organizations managing cloud environments.
Usage-Based Key Rotation
For systems that handle a large volume of data, usage-based rotation can offer added protection. Instead of relying on time, this method rotates keys based on how many messages or bytes have been encrypted. It’s especially useful for preventing cryptanalysis risks in high-traffic systems.
Guidelines like NIST Special Publication 800-38D recommend monitoring GCM message limits to avoid exceeding cryptographic safety thresholds [1]. For healthcare organizations running imaging systems, lab information systems, or real-time patient monitoring platforms, this approach can be a game-changer. High message volumes might push a key to its safety limit before its scheduled rotation, making usage-based triggers more effective in these scenarios. However, this method does require close monitoring of encryption activity to catch potential risks early.
Event-Driven Key Rotation
Sometimes, key rotation can’t wait for a schedule or usage threshold. Event-driven rotation kicks in after specific incidents, such as a security breach or a migration to stronger encryption algorithms [1]. As Google Cloud KMS advises:
"If you suspect that a key version is compromised, disable it and revoke access to it as soon as possible." [1]
Healthcare organizations should regularly test their manual rotation processes to ensure they’re ready for emergencies. This preparation is vital for maintaining system resilience, especially during transitions to new standards. For example, all cryptographic modules must comply with FIPS 140-3 by September 22, 2026, as FIPS 140-2 certifications will no longer be valid for new deployments after that date [2].
Automating Key Rotation Processes
Relying on manual key rotation can lead to mistakes like missed schedules, misconfigurations, or referencing the wrong keys. Automating this process ensures consistent adherence to policies and eliminates the need for human intervention, reducing errors and maintaining continuous protection [3][6].
Using Cloud-Native Tools
Cloud providers offer built-in tools to simplify and automate key rotation. For instance:
- AWS KMS automatically rotates AWS-managed keys annually (around 365 days) [3]. For customer-managed keys, you can customize the rotation period, choosing anywhere between 90 and 2,560 days [6].
- Azure Key Vault allows you to set a rotation policy that creates new key versions at intervals you specify, with a minimum rotation interval of seven days [4].
- Google Cloud KMS supports automatic rotation schedules ranging from 1 day to 100 years [5].
These tools maintain consistent key identifiers - like Key IDs, ARNs, and versionless URIs - ensuring that healthcare applications continue to function without disruption during rotations [4][6]. Pricing varies: AWS KMS, for example, charges for the first two rotations of key material each month, while subsequent rotations are free [3]. Azure Key Vault, on the other hand, incurs additional costs for every scheduled key rotation [4].
It’s worth noting that automatic rotation generally applies to symmetric keys. Asymmetric keys still require manual rotation since the updated public key must be distributed to external systems or partners [3][1].
Integrating these automated tools into your system can make key management more seamless and efficient.
Connecting with Existing Systems
To integrate automated rotation into your healthcare infrastructure, tools like Azure's versionless key URIs and AWS aliases are essential. These ensure that applications automatically use the latest key version without requiring code changes [4][6]. As AWS documentation explains:
"Because AWS KMS transparently decrypts with the appropriate key material, you can safely use a rotated KMS key in applications and AWS services without code changes." [3]
When rotating keys, keep older versions active until all encrypted data has been re-encrypted or is no longer needed. Deleting old keys prematurely can result in data loss [4][1]. Governance tools like Azure Policy can help enforce rotation schedules across your cloud environment, ensuring no keys are overlooked [4].
Maintaining Service Continuity
In most cloud-native setups, key rotation doesn’t cause interruptions to cryptographic operations. Current key material remains available until the new material is fully synchronized across all regions [3]. For Azure, this synchronization can take anywhere from 1 to 24 hours [4].
To avoid disruptions, integrate key rotation events into monitoring systems like AWS CloudTrail, Amazon EventBridge, or Azure Event Grid. These tools allow you to confirm successful rotations and quickly detect any issues [3][4]. Additionally, set up alerts for near-expiry notifications, especially for keys requiring manual updates [3][4]. For multi-region infrastructures, rotating the primary key triggers synchronization of new material across all regions [3].
If old key versions need to be retired - whether for cost savings or compliance reasons - you’ll need to manually re-encrypt data [5][1]. These practices help ensure secure and reliable key management while aligning with broader risk management strategies in healthcare.
Storing and Managing Cryptographic Keys
The way you store and manage cryptographic keys plays a critical role in maintaining both security and compliance.
Hardware Security Modules (HSMs)
HSMs offer a high level of physical protection for cryptographic keys by keeping them in tamper-resistant hardware. For instance, AWS Key Management Service utilizes HSMs validated under FIPS 140-2 Level 3 [8]. This level of validation is particularly important for healthcare organizations that must adhere to stringent regulatory standards, as it ensures key material is safeguarded within a secure hardware boundary.
You can choose from several options depending on your needs: software-backed keys for general workloads, multi-tenant HSMs for FIPS-validated shared hardware, or single-tenant HSMs for complete isolation [7].
Key attributes like NONEXTRACTABLE (which prevents keys from being exported in plaintext) and WRAP_WITH_TRUSTED (which restricts key wrapping to authorized admin keys) are essential for enhancing security [9]. If you're using Azure Cloud HSM, it's recommended to wait 24 hours after creating a key before deploying it in production. This allows time for synchronization and backup across all cluster nodes [9].
While HSMs provide robust physical security, cloud-native key management services are often more convenient for application integration.
Cloud Key Management Services
Cloud-native key management services streamline secure key storage and integrate directly with healthcare applications. These services handle the complexities of key storage, replication, and availability, sparing you the need to manage physical hardware.
To meet data residency requirements and reduce latency, store keys in the same region as the associated data and use dedicated accounts for production [7]. This approach enforces strict access controls and reduces the risk of exposure.
Cloud providers typically implement a grace period for key deletion, often set to 30 days [7][8]. This period provides a safety net, allowing recovery from accidental deletions before key material is permanently destroyed. To further protect critical keys, apply project-level liens or legal holds on key management projects, preventing unintended deletion of the entire project [7].
Separating Key Access from Data Access
Unencrypted key material should never be accessible to human users [8]. All cryptographic operations should be executed through API calls made by service accounts, not by individual users.
To ensure proper separation of duties, assign specific roles: a cryptographic officer for key management and a separate user role for encryption operations [7]. For example, a healthcare administrator might be allowed to create objects in a storage bucket, but only the storage service agent should have permission to use the encryption key [7].
| IAM Role | Job Function | NIST SP 800-152 Designation |
|---|---|---|
| KMS Admin | Manages key lifecycle (create, rotate, delete) | Cryptographic Officer |
| CryptoKey User | Performs encrypt/decrypt operations | CKMS User |
| KMS Viewer | Audits key settings and usage logs | Audit Administrator |
Follow the principle of least privilege by using predefined, restricted roles [7]. You can enforce customer-managed encryption key (CMEK) usage across your organization with policies like constraints/gcp.restrictNonCmekServices, which block the creation of any healthcare resource not specifying a customer-managed encryption key [7].
These storage practices, combined with automated key rotation, strengthen security and ensure compliance with regulatory requirements.
Monitoring and Auditing Key Rotation Activities
Detailed logging is essential for compliance and effective post-incident analysis. Logs should include timestamps in the MM/DD/YYYY HH:MM:SS format, the user or service account initiating the activity, key identifiers, the reason for rotation, status, and any affected resources. For example, HIPAA mandates retaining immutable logs for at least six years to demonstrate compliance with access controls under 45 CFR § 164.312(b) [10][11]. Below, we’ll explore strategies for logging, anomaly detection, and auditing to strengthen your key rotation processes.
Logging All Key Rotation Events
To ensure thorough tracking, enable diagnostic settings in your cloud provider’s key management service. This allows logs to be sent to centralized platforms such as Azure Log Analytics or Google BigQuery. For instance, Google Cloud KMS automatically logs key rotation events to BigQuery. A lack of adequate logging was a factor in 60% of healthcare data breaches in 2023, according to the Verizon DBIR, leading to costly HIPAA penalties [12][13].
Detecting Unusual Rotation Activities
Once logging is in place, tools like Splunk or AWS GuardDuty can help identify anomalies. These SIEM tools establish baselines for typical rotation patterns and alert you to irregularities. For example:
- More than five rotations per hour for a single key family.
- Rotations initiated from unapproved IP addresses, especially during off-hours.
Google Cloud Security Command Center uses machine learning to compare current activity against historical trends, making it easier to spot deviations [14][15]. According to the AWS Security Report from 2023, automated monitoring significantly reduces the time it takes to detect key rotation anomalies compared to manual methods.
Conducting Regular Compliance Audits
Audits are a critical step to ensure logging accuracy and bolster your cyber risk management strategy. Schedule quarterly internal audits and annual reviews by third-party experts, following NIST 800-53 AU family controls and HIPAA Security Rule guidelines. During these audits:
- Export logs covering the past 90 days.
- Sample 10% of rotation events using tools like AWS Audit Manager.
- Verify adherence to policies, such as maintaining a maximum key age of 90 days and avoiding manual overrides.
Document your findings, include remediation timelines, and retain audit records for seven years, as recommended by HHS. In 2023, HIPAA violation fines averaged $1.5 million, a 20% increase from the prior year, largely due to inadequate logging and auditing [HHS OCR data].
To further enhance oversight, track cybersecurity KPIs such as:
- Rotation frequency per key.
- Failure rates: Aim for less than 1%.
- Rotation latency: Keep it under five minutes.
- Cross-region inconsistencies.
Monitor these metrics daily through dashboards and conduct weekly reviews. A 2024 HIMSS report found that organizations actively tracking these KPIs reduced their incident response times by 40%, aligning with HITRUST’s continuous monitoring standards [16].
Connecting Key Rotation with Risk Management Platforms
Key rotation efforts that operate in isolation can leave critical security gaps. When healthcare organizations handle rotation events without integrating them into a broader strategy, they risk overlooking the connection between cryptographic hygiene and overall cybersecurity health. According to Ponemon Institute research, 72% of healthcare breaches in 2024 stemmed from misconfigured or unrotated cryptographic keys [19]. By integrating key rotation with risk management platforms, organizations can connect key lifecycle events to vulnerabilities, compliance issues, and operational risks. This approach provides a more complete view of potential threats, extending continuous monitoring into a broader framework that strengthens the overall security posture.
Tracking Rotation Events in Censinet RiskOps™

Censinet RiskOps™ takes logging and monitoring a step further by integrating with cloud key management services. This integration centralizes key rotation events on a single dashboard, offering real-time insights into rotation frequency, success rates, and anomalies [10]. Automated alerts can be configured to ensure compliance with HIPAA, maintaining a detailed audit trail of key lifecycle events. For example, dashboards not only track rotation metrics but also enforce role-based access controls to separate monitoring from execution [17]. A healthcare delivery organization (HDO) can use these tools to generate reports, showing metrics like 95% on-time key rotations each quarter. This aligns with broader risk management strategies and has been shown to reduce compliance audit findings by an average of 35%, according to the 2025 Deloitte Healthcare Cybersecurity Report [20].
Linking Key Rotation to Third-Party Risk Assessments
Vendor relationships often come with hidden cryptographic risks. When key rotation is integrated with third-party risk assessments, healthcare organizations can verify whether vendors comply with rotation policies. This process helps identify risks, such as vendors with infrequent rotation cycles [17]. For instance, by incorporating AWS KMS rotations into RiskOps™, a mid-sized HDO discovered a vendor operating on a six-month rotation cycle. Addressing this issue reduced the organization’s risk score by 25% [17]. This unified approach also enables risk scores that include key management metrics, making proactive remediation more effective. Healthcare organizations using integrated platforms have reported identifying encryption-related vulnerabilities 40% faster when key rotation data is tied to third-party assessments [18][21].
Benchmarking and Reporting on Key Rotation
Censinet RiskOps™ provides anonymized benchmarking data, allowing organizations to compare their rotation practices against industry averages. These benchmarks can reveal gaps, such as delays in event-driven rotations [17]. Reports include executive summaries with key metrics, peer comparisons, detailed audit logs, and trend analyses, all of which support compliance with HIPAA and NIST standards. Additionally, formatted reports can be exported as evidence for auditors. Gartner observed a 28% year-over-year increase in 2025 for tools combining key management telemetry with third-party risk data [21]. Scheduling quarterly benchmarks of key rotation metrics within a risk platform can help identify weaknesses and create actionable compliance reports, driving continuous improvements in healthcare cloud security [18].
Conclusion
Healthcare organizations face a pressing need to rotate cryptographic keys to safeguard cloud-based patient data. Incidents like the 2021 Scripps Health breach, where static keys allowed ransomware to compromise the protected health information (PHI) of 147,000 patients at a staggering cost of $113 million, highlight the risks of inadequate key management. With 74% of healthcare breaches linked to credential issues, robust key rotation is essential - not just for protecting PHI, but also for meeting HIPAA encryption requirements [11][12].
Key Takeaways
- Automate key rotation: Use cloud-native tools like AWS Key Management Service (KMS) or Azure Key Vault to reduce manual errors and maintain seamless operations.
- Secure key storage: Ensure cryptographic keys are stored in FIPS 140-2 compliant hardware security modules (HSMs) to separate key material from data access.
- Time-based rotation cycles: Follow HIPAA-aligned schedules, such as rotating high-risk keys every 90 days, to minimize exposure.
- Leverage risk management platforms: Integrate key rotation into tools like Censinet RiskOps™ to log events, detect anomalies, and connect rotation activities to third-party risk assessments.
- Benchmark against industry standards: Regularly compare practices to frameworks like NIST SP 800-57 to identify gaps and reduce compliance risks [12].
Next Steps for Healthcare Organizations
Start by conducting a 30-day audit of your current key management processes. Begin automating key rotation on non-critical systems with tools like AWS Secrets Manager or Google Cloud KMS, then expand to production environments. Annual reviews of key rotation policies can cut cryptographic risks by up to 60% [11]. Use platforms like Censinet RiskOps™ to track rotations, automate third-party risk assessments, and receive alerts for delays. Additionally, benchmark key rotation metrics quarterly and conduct annual training simulations to ensure full compliance. These measures can lower breach risks by 50% [10], strengthening data security in the face of evolving threats.
FAQs
Which keys should we rotate first?
To keep sensitive systems and data secure, focus on regularly rotating keys associated with high-risk areas, like those protecting Protected Health Information (PHI) - whether it's stored or being transmitted. A good rule of thumb is to rotate these keys every 90 days or immediately after any security breach. This approach not only strengthens security but also helps meet regulatory standards.
How do we rotate keys without breaking apps?
Rotating encryption keys without causing disruptions to your applications requires automated, zero-downtime strategies. Techniques like lazy re-encryption, key versioning, or blue-green deployment can make the process seamless. To manage keys securely, rely on tools such as Key Management Services (KMS) or Hardware Security Modules (HSMs).
Automation plays a critical role here. By automating key rotation, closely monitoring key usage, and maintaining detailed audit logs, you can ensure smooth transitions while staying compliant with security standards. For the best protection, aim to rotate keys regularly - ideally every 90 days or after specific key-related events.
What should we do after a suspected key compromise?
When there's a suspected key compromise in a healthcare organization, swift action is critical. Start by disabling the compromised key to prevent further unauthorized access. Next, revoke access tied to that key and promptly rotate to a new key to restore security.
It's also essential to follow established key management best practices. This includes updating encryption policies to address vulnerabilities and conducting a comprehensive risk assessment. These steps help ensure compliance with regulations and safeguard sensitive data effectively.


