How Audit Trails Support Regulatory Compliance
Post Summary
Audit trails are digital logs that track every action taken on sensitive data, such as electronic health records (EHRs). In healthcare, they’re crucial for ensuring compliance with regulations like HIPAA, FDA 21 CFR Part 11, and ISO 27001. These logs record who accessed data, what they did, when, where, and why, creating a detailed, tamper-proof record of activity.
Here’s why they matter:
- Compliance: Audit trails provide proof that healthcare organizations meet regulatory requirements.
- Security: They help detect suspicious activity, such as unauthorized logins or data breaches.
- Accountability: Every action is tied to a specific user, ensuring transparency.
- Data Integrity: Logs are immutable, ensuring records remain trustworthy over time.
- Audit Preparation: They simplify compliance audits by automating evidence collection.
What is an Audit Trail in Healthcare? (Explained - 2026)
sbb-itb-535baee
Regulatory Requirements for Audit Trails
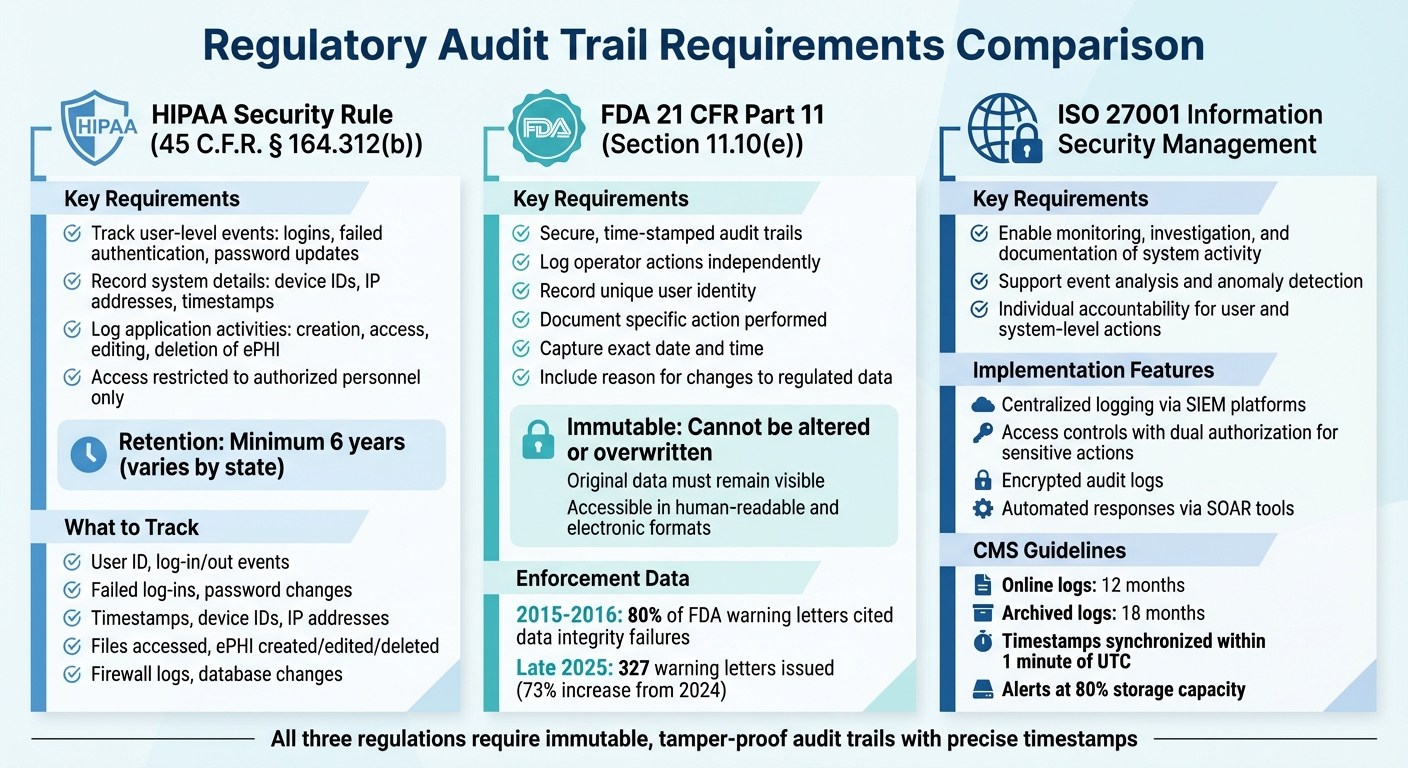
HIPAA, FDA 21 CFR Part 11, and ISO 27001 Audit Trail Requirements Comparison
Healthcare organizations in the United States must adhere to strict legal requirements for audit trails to protect patient data. Knowing the specific regulations helps these organizations create systems that comply with the law while safeguarding sensitive information.
HIPAA Audit Trail Requirements
Under the HIPAA Security Rule (45 C.F.R. § 164.312(b)), covered entities and business associates are required to implement systems that log and monitor activity involving electronic protected health information (ePHI). According to the Department of Health and Human Services, these audit trails must "maintain a record of system activity by application processes and by user activity within systems and applications" [2].
HIPAA audit trails track a range of activities, including:
- User-level events: Log-ins, failed authentication attempts, password updates.
- System details: Device IDs, IP addresses, timestamps.
- Application activities: Creation, access, editing, and deletion of ePHI.
Access to audit logs must be "strictly restricted" to authorized personnel, typically those responsible for audits or IT security. Organizations are required to retain these logs for at least six years, though some states enforce even stricter retention timelines [3]. These logs play a critical role in enforcing the minimum necessary standard, ensuring that employees only access the PHI they need for their job roles. This helps identify potential misuse, such as internal abuse or credential theft.
| Audit Trail Category | Key Data Points to Track |
|---|---|
| User Audit Trail | User ID, log-in/out events, failed log-ins, password changes |
| System Audit Trail | Timestamps, device IDs, IP addresses, firewall activity |
| Application Audit Trail | Files accessed, ePHI created, edited, or deleted |
| Security Logs | Firewall logs, malware logs, database changes |
While HIPAA doesn’t provide a definitive list of required data points, conducting risk assessments can help organizations determine which activities to monitor. Synchronizing system clocks using Network Time Protocol (NTP) servers ensures consistent and accurate timestamps across all audit logs.
FDA 21 CFR Part 11 Compliance
Healthcare organizations involved in clinical trials, drug manufacturing, or medical device development must also comply with FDA 21 CFR Part 11. This regulation sets stringent standards for electronic records and signatures. Section 11.10(e) mandates secure, time-stamped audit trails that independently log operator actions, including the date and time of each entry [4][7].
"An audit trail is the who, what, when, and why of a company's data. It's a log containing metadata that essentially allows you to reconstruct all user actions and events involving data."
- Seyed Khorashahi, CTO, Regulatory Compliance Associates [6]
To meet FDA requirements, audit trails must record:
- The unique identity of the user.
- The specific action performed.
- The exact date and time of the action.
- The reason for any changes to regulated data.
Audit trails must be immutable, meaning they cannot be altered or overwritten, and the original data must remain visible. Records must also be accessible in both human-readable and electronic formats [4][5][7].
Data integrity issues are a significant focus of FDA enforcement. Between 2015 and 2016, roughly 80% of FDA warning letters cited failures in data governance or integrity [7]. In late 2025, the FDA issued 327 warning letters - a 73% increase from the same period in 2024 - with data integrity remaining a top concern [7]. To avoid penalties, organizations should automate logging to capture all actions (e.g., create, modify, delete) in real time, prohibit shared accounts, and test their ability to export audit logs for inspections.
ISO 27001: Information Security Management
For a broader approach to data security, ISO 27001 provides international standards for information security management. Audit trails are a key component of these standards, enabling organizations to monitor, investigate, and document system activity for event analysis and anomaly detection [8]. The standard emphasizes individual accountability, requiring detailed records of both user and system-level actions.
ISO 27001-aligned systems often include:
- Centralized logging: Using SIEM (Security Information and Event Management) platforms to consolidate logs for real-time monitoring.
- Access controls: Restricting log access to privileged users and requiring dual authorization for sensitive actions like data deletion.
- Data protection: Encrypting audit logs to prevent unauthorized access or tampering.
- Automated responses: Leveraging SOAR (Security Orchestration, Automation, and Response) tools to execute pre-defined actions during incidents.
CMS guidelines add further requirements, such as maintaining online logs for 12 months and archiving them for 18 months. Timestamps must be synchronized within one minute of UTC, and alerts should notify administrators when log storage reaches 80% capacity or when errors occur [8]. These measures ensure the integrity of patient data while holding users accountable for their actions.
How Audit Trails Support Regulatory Compliance
Audit trails go beyond simply meeting regulatory requirements - they actively enhance how healthcare organizations safeguard patient data, ensure accountability, and prepare for audits. By creating a permanent, tamper-proof record of every system action, audit trails shift compliance from a checkbox exercise to a proactive measure for security and transparency. These features form the backbone of accountability and make audits more efficient.
Protecting Patient Data and Preventing Breaches
Every interaction with electronic health records (EHRs) - whether adding, editing, or deleting data - leaves a traceable footprint linked to a specific user ID. This level of traceability acts as a deterrent against unauthorized access, making it harder to hide suspicious activity. Audit trails follow ALCOA+ principles, ensuring records remain accurate and reliable.
One of the key strengths of audit trails is their immutability. Entries are "append-only", meaning even system administrators cannot alter or delete them. This tamper-proof design ensures that unauthorized changes cannot be concealed. Automated timestamps, synchronized through NTP (Network Time Protocol), create a dependable sequence of events.
Regularly reviewing these logs helps organizations reconstruct incidents, resolve issues, and detect fraudulent activities early. For example, unusual access patterns or multiple failed login attempts could signal credential theft or insider threat indicators, allowing for swift action to protect patient data.
Ensuring Accountability and Transparency
Audit trails tie every action to a unique user account, eliminating the ambiguity caused by shared or generic logins. Role-based access control (RBAC) ensures that each user’s permissions align with their job responsibilities, and the audit trail records every instance these permissions are used.
When a compliance issue arises - whether through error or intentional misconduct - audit trails provide clear evidence of who was involved and what occurred. This level of detail is crucial for meeting regulatory standards. For example, the FDA’s finalized Computer Software Assurance (CSA) guidance from September 24, 2025, emphasizes the importance of maintaining accurate and attributable logs[1]. Failure to do so can result in enforcement actions. This transparency not only supports compliance but also builds trust within the organization.
By maintaining a clear, detailed record of user actions, organizations simplify the process of identifying accountability and preparing for audits.
Simplifying Compliance Audits and Reporting
Audit trails automate the collection of evidence, eliminating the need for time-consuming manual log reconstruction. They allow organizations to generate detailed compliance reports that outline user activity and access. Advanced platforms now enable healthcare organizations to align internal activities with regulatory standards like the NIST Cybersecurity Framework (CSF) 2.0 and the HHS Healthcare and Public Health Sector Cybersecurity Performance Goals.
Real-time dashboards and automated reporting tools further streamline the process. These tools consolidate evidence, reducing the time and cost associated with audit preparation. They also highlight gaps in security controls or policies before an official audit takes place. By centralizing all compliance evidence in one searchable platform, healthcare organizations can respond to auditor requests efficiently and confidently. For example, solutions like Censinet RiskOps™ simplify audit trail management by integrating compliance reporting into their platforms.
This combination of automation and transparency helps healthcare organizations navigate audits with ease while maintaining high standards of data security.
How to Build Compliant Audit Trails
Creating compliant audit trails demands thoughtful planning and consistent execution. Healthcare organizations must develop systems that capture essential data, safeguard it against tampering, and ensure it remains accessible for review. The objective? To maintain a permanent record that not only meets regulatory requirements but also supports daily operations.
Core Components of Audit Trails
Every entry in an audit trail should answer five key questions: who, what, when, where, and why. Here’s what that looks like:
- Who: Tracks the user ID to ensure individual accountability, avoiding shared accounts.
- What: Records the specific action, such as creating, modifying, or deleting data. For critical changes, both the "before" and "after" values should be logged.
- When: Uses precise timestamps synchronized via NTP (Network Time Protocol).
- Where: Identifies the system, application, or device involved in the action.
- Why: Captures the reason for the action, especially for changes to validated records.
These components work together to provide a complete view of system activity, ensuring audit trails can support investigations and meet regulatory standards. Once these elements are in place, the focus shifts to implementing practices that protect the integrity of the audit trail.
Implementation Best Practices
To meet HIPAA and FDA compliance standards, follow these best practices:
- Use Write Once, Read Many (WORM) or immutable storage to prevent tampering with logs.
- Synchronize all systems to NTP with clear thresholds for acceptable clock drift.
- Develop a Standard Operating Procedure (SOP) that outlines how data is collected, which tools are used, and how evidence is captured.
- Standardize usernames, object IDs, and event codes to make it easier to compare activities across systems.
- Introduce a dual-review process for significant findings, ensuring independence and accuracy in reporting.
- Conduct unscheduled reviews after incidents, software updates, patches, or regulatory audits.
These steps help ensure that audit trails remain reliable and secure, even under scrutiny.
Audit Trail Retention and Review
Retention and regular review are just as important as implementation. Retention policies should comply with regulatory standards, such as FDA 21 CFR Part 11, though some organizations may choose to retain records longer for legal or business purposes. The frequency of reviews should match the system’s risk level:
- High-risk systems (e.g., Laboratory Information Management Systems or Manufacturing Execution Systems): Daily or weekly reviews.
- Moderate-risk systems (e.g., Enterprise Resource Planning platforms): Monthly reviews.
- Low-risk systems: Quarterly reviews.
During reviews, correlate audit entries with change tickets or clinical records to confirm that actions were authorized. If discrepancies arise, use root-cause analysis techniques like the "5 Whys" to identify the issue. Maintain a strict chain-of-custody for evidence to ensure it remains admissible.
For routine events, statistical sampling may be sufficient. However, privileged actions - such as changes to permissions or configurations - should undergo a complete review. Keeping audit trails under consistent scrutiny not only ensures compliance but also strengthens their role as essential tools for safeguarding data.
Conclusion
Audit trails go beyond simply meeting regulatory requirements - they act as a critical layer of defense for protecting patient information, ensuring accountability, and easing the burden of compliance audits. By recording both system and user activities, audit trails become essential tools for identifying breaches early, holding individuals accountable, and satisfying regulatory demands.
The stakes are high: healthcare data breaches are projected to cost an average of $9.77 million in 2025, marking the highest costs across industries for 14 consecutive years [9]. Alarmingly, 72% of healthcare breaches in 2023 were linked to third-party vendor relationships [9]. These figures highlight the pressing need for proactive compliance and continuous monitoring rather than reactive approaches.
Key Takeaways for Healthcare Organizations
To integrate audit trails effectively into compliance frameworks, healthcare organizations should consider the following strategies:
- Automate monitoring with compliance management tools, enabling IT teams to focus on identifying anomalies rather than sifting through manual reviews.
- Restrict access to audit trails, limiting interactions to authorized personnel involved in audits or specific IT management roles, which helps reduce tampering risks.
- Assign dedicated IT staff to oversee and regularly review logs, ensuring consistent monitoring and quick responses to potential issues.
Compliance programs must go beyond being mere checklists. Instead, they should weave governance, technology, and organizational culture into daily operations. As Natalie Dytrych, Senior Product Marketing Manager at Optro, explains:
"Compliance programs fail when they're treated as checklists. The ones that work integrate governance, technology, and culture into daily operations" [9].
This perspective emphasizes the importance of moving away from fragmented tools like spreadsheets and adopting platforms that offer real-time oversight across regulations like HIPAA, GDPR, and state privacy laws.
Additionally, conducting risk-based assessments can help organizations pinpoint critical audit trail data. Treat audit trails not as static records but as evolving tools that enhance security while meeting regulatory requirements.
Ultimately, robust audit trail practices do more than ensure compliance with standards like HIPAA, FDA, and ISO 27001 - they also create a proactive approach to security. Platforms like Censinet RiskOps™ enable healthcare organizations to align risk management seamlessly across patient data, clinical systems, and supply chains, simplifying compliance while strengthening overall security.
FAQs
What events should an audit trail log in an EHR system?
An audit trail in an EHR system serves as a critical tool for maintaining compliance and ensuring security. It should document key events such as:
- Access events: Who accessed the system and when.
- Modifications: Any changes made to patient records or data.
- Transfers of PHI: Details on when and where protected health information (PHI) was transferred.
- User identities: The specific individuals performing actions within the system.
- Timestamps: Exact dates and times for all logged activities.
- Data accessed or altered: Specifics on the information viewed or modified.
- Disposal actions: Records of data deletion or other disposal activities.
- Security-related activities: Events like failed login attempts or system alerts.
These logs are essential for ensuring accountability and safeguarding sensitive patient information from unauthorized access or misuse.
How can we prove audit logs are tamper-proof and time-synced?
To keep audit logs secure and reliable, it's important to use methods like WORM (Write Once, Read Many) storage and cryptographic hashing. These tools help prevent tampering and ensure the logs remain unaltered. Pair them with independent time-stamping mechanisms that provide accurate and fixed timestamps for every recorded action. This combination safeguards data integrity and ensures traceability, helping you comply with regulatory standards.
How often should we review audit trails to stay compliant?
Organizations should examine audit trails at least once a year to confirm compliance and spot any unauthorized activities. However, conducting these reviews more often - like quarterly or after major events - can help ensure regulatory requirements are met and allow for faster responses to potential risks.


