Top Challenges in Federated Identity for Healthcare
Post Summary
Federated identity in healthcare simplifies access to patient data across multiple systems using a single login. While it improves convenience and security, it faces several hurdles:
- Fragmented Systems: Disconnected platforms make data sharing difficult, leading to inefficiencies and errors in patient care.
- Security Risks: Centralized identity providers (IdPs) are prone to attacks, with breaches potentially impacting all connected systems.
- Patient Identification Errors: Duplicate records and mismatched data disrupt care and increase costs.
- Regulatory Compliance: Meeting HIPAA and other privacy laws while maintaining seamless access is challenging.
- User Adoption Issues: Credential fatigue and slow onboarding reduce engagement among staff and patients.
Key Solutions:
- Use standard protocols like SAML and OpenID Connect for integration.
- Implement advanced security measures like FIDO2/WebAuthn and continuous monitoring.
- Adopt digital identifiers and biometric verification to reduce errors.
- Simplify access with Single Sign-On (SSO) and automated onboarding.
- Automate compliance monitoring to handle privacy and regulatory requirements efficiently.
Addressing these challenges requires a focus on open standards, secure practices, and user-friendly designs to improve healthcare data management and patient outcomes.
LISA15 - What Is Federated Identity and Why Should I Care?
sbb-itb-535baee
Challenge 1: Fragmented Data and System Incompatibility
Healthcare organizations often operate in silos, with disconnected systems creating barriers to unified identity management. Hospitals and clinics frequently juggle a mix of Electronic Health Records (EHRs), lab systems, imaging platforms, and patient portals that don't communicate effectively. This fragmentation forces both patients and providers to manage multiple sets of credentials, leading to manual password handling that weakens security and increases risks to patient care [1].
A staggering 73% of organizations cite legacy application integration as their biggest challenge to implementing identity federation. Many healthcare IT vendors rely on proprietary technology, locking organizations into costly middleware solutions rather than enabling consistent, federated connectivity [8][9].
"The lack of integration common throughout health care would be unacceptable on safety grounds alone in any other high-risk field." - National Academy of Medicine [8]
This lack of interoperability adds up to $36 billion in annual waste in inpatient settings alone, driven by manual data transcription that heightens clerical errors, contributes to clinician burnout, and results in nearly 100,000 deaths annually in the U.S. [8]. Shockingly, fewer than 1 in 3 hospitals can electronically find, send, receive, and integrate patient data from external providers [8]. These gaps not only inflate operational costs but also disrupt timely patient care - a critical issue explored further below.
Effects on Patient Care and Data Access
When systems fail to share identity and health data seamlessly, patient care takes a direct hit. Clinicians often face delays in accessing vital information during urgent situations, forcing them to make decisions based on incomplete records. The lack of standardized data storage across different systems further complicates matters, resulting in redundant data entry and unnecessary repeat tests [7].
In 2023, while 70% of U.S. non-federal acute care hospitals engaged in all four interoperability domains (send, receive, find, and integrate), only 43% did so consistently [10]. Even more troubling, only 42% of clinicians routinely use electronic information from outside providers during patient care, despite 71% of hospitals having access to it [10]. This disconnect between capability and actual use underscores how fragmentation slows real-time clinical decision-making.
Smaller facilities feel the impact even more acutely. System-affiliated hospitals are more than twice as likely (53%) to engage in routine interoperable data exchange compared to independent hospitals (22%) [10]. Rural and independent hospitals, often operating with limited resources, struggle to keep pace, leaving their patients at a disadvantage. The problem is particularly severe in long-term care and behavioral health settings - only 16% of hospitals routinely send summary of care records to long-term or post-acute care providers [10].
Solution: Using Standard Protocols for System Integration
Standard protocols like SAML, OAuth, and OpenID Connect (OIDC) offer a way to bridge the gap between siloed identity systems. These protocols enable a single identity to be shared and managed centrally, even when the underlying systems remain separate. Organizations that adopt federated identity using these standards report a 65% drop in identity-related security incidents [9].
The industry is increasingly favoring open standards, with 83% of new integrations now using OIDC instead of the older SAML standard. This shift reflects a preference for API-friendly, flexible authentication methods [9]. Federal requirements, such as the CMS Interoperability and Patient Access Final Rule and the ONC 21st Century Cures Act, further push for secure data exchange via APIs [4].
"Federated identity systems with SSO offer a solution; a member is provided one login for access to multiple disparate systems. The systems themselves remain siloed, but the member's identity is shared and administered from one central location." - Ryan M. Harrison, Pavan Jagalur, and Mukundan Srinivasan, Amida Technology Solutions [4]
SMART on FHIR (Substitutable Medical Applications, Reusable Technologies) serves as a practical example of how standard protocols can enable interoperability. By combining HL7's FHIR with OAuth2 and OIDC, this framework creates a unified approach for third-party applications to work across different EHR systems [4]. When selecting vendors, healthcare organizations should prioritize those supporting open standards to avoid vendor lock-in and reduce technical complexity [4]. Starting with high-priority applications before tackling more complex legacy systems can make the transition smoother [9].
Challenge 2: Security Risks in Federated Identity Systems
Federated identity simplifies access but also introduces concentrated risks that attackers can exploit. The Identity Provider (IdP) becomes a critical focal point and a single point of failure. If an attacker gains access to the IdP's private keys, they can generate fake assertions and impersonate users across all connected systems [12]. A breach at the IdP can quickly spread throughout the federation, allowing someone to jump from one system, like a hospital, to another facility's records with ease [11]. These vulnerabilities open the door to a variety of sophisticated attacks.
This is especially concerning in healthcare, where 86% of cyberattacks targeting internet-facing systems involve stolen or compromised credentials [17]. A notable example is Banner Health, an Arizona-based hospital system. In February 2023, the organization agreed to a $1.25 million settlement with the HHS Office for Civil Rights after failing to implement adequate authentication measures to protect electronic protected health information (ePHI) during a hacking incident [17].
Common Attack Methods Targeting Federated Identity
Attackers often exploit weaknesses in the communication between IdPs and relying parties (RPs). Some common methods include:
- Assertion reuse: Intercepting and replaying valid bearer assertions within their time window.
- Assertion redirect: Redirecting assertions meant for one RP to attacker-controlled systems.
- Assertion substitution: Hijacking sessions to replace legitimate user assertions [11][14].
Beyond these assertion-based attacks, healthcare systems face risks from SIM-swapping and credential theft, especially when using "shared secret" multi-factor authentication (MFA) methods like one-time passwords (OTPs) or SMS codes. These methods are vulnerable to phishing, where attackers trick users into providing authentication details on fake websites [15][17]. Additionally, the integration of Internet-of-Medical Devices (IoMT) and Medical Cyber Physical Systems (MCPS) increases exposure to risks from outdated firmware, unsecure operating systems, and weak data encryption during transmission [13].
"In federated systems, successful attacks on the IdP can propagate through to the RPs that rely on that IdP... an attack against the IdP that targets one agency's RP could potentially move laterally to another agency's RP." - NIST [11]
These attack strategies highlight the critical vulnerabilities in centralized IdP systems.
Solution: Stronger Authentication and Continuous Monitoring
To address these risks, healthcare systems need to adopt advanced authentication and monitoring strategies. Moving beyond traditional MFA, they should implement phishing-resistant methods like FIDO2/WebAuthn and PKI. These hardware-based tokens or platform authenticators are designed to eliminate threats like SIM-swapping and credential theft [15][17]. IdPs should integrate these methods with risk-based security for all subscriber-facing pages [12].
"Not all MFA is the same. Attackers have found ways to phish authentication technologies such as one-time passwords (OTPs) that are based on 'shared secrets.' Wherever possible, use high assurance, phishing-resistant tools such as FIDO or Public Key Infrastructure (PKI)." - Health-ISAC [15]
Cryptographic protections are essential for securing federated identity systems. Assertions should always be cryptographically signed at the IdP, with short validity windows (just a few minutes). RPs must verify both the issuer and the audience to prevent unauthorized access [11][14]. Using back-channel methods like OpenID Connect's Authorization Code flow can enhance security by sending assertions directly from the IdP to the RP, bypassing the user agent entirely [14].
Since a breach at the IdP can affect all connected systems, continuous monitoring is crucial. Tools like Censinet RiskOps™ enable independent threat assessments and rapid responses across federated identity networks. These platforms help identify compromised accounts and support shared signaling between IdPs and RPs [11]. RPs should also perform regular negative testing - submitting unsigned or expired assertions to confirm proper rejection. Without this, systems might appear functional even if critical signature checks are bypassed [14].
Challenge 3: Patient Identification Errors and Duplicate Records
Beyond security concerns, federated identity systems face another major hurdle: ensuring accurate patient identification. This issue directly impacts patient safety and the continuity of care.
Errors in patient identification can disrupt everything. When a patient’s record is mismatched or duplicated across systems, critical information - like lab results or radiology reports - can be misinterpreted or lost. Up to 50% of shared data exchanges involve patient record mismatches [18]. This isn’t just a logistical headache; it’s a financial burden, costing the U.S. healthcare system $6 billion annually [18].
The consequences for patient safety are alarming. A 2012 survey revealed that nearly 1 in 5 hospital CIOs reported instances of patient harm due to record mismatches [18]. In just the second quarter of 2019, 37 out of 436 sentinel events - serious safety incidents - were linked to identification errors [19]. Duplicate records, in particular, fragment a patient’s medical history, leading to incomplete information for clinicians. The results? Medication errors, unnecessary testing, and even wrong-site surgeries.
"When a patient is incorrectly matched to another patient's record, patient care and safety are jeopardized as incorrect data can cascade to a multitude of internal and external systems." - Lauren Riplinger, JD, AHIMA [19]
Duplicate records are a widespread issue. On average, U.S. healthcare organizations report an 8% duplicate record rate, with larger systems seeing rates as high as 15% to 16% [21]. In 4% of these cases, clinical care is directly affected [21]. For example, at Children’s Medical Center Dallas, duplicate records cost about $96 each, with 4% causing delays in emergency room treatments or surgeries due to missing reports [21]. These delays and repeated tests can add an average of $1,100 to a patient’s care costs [21].
Root Causes of Patient Misidentification
The core issue lies in fragmented identifier systems. Most healthcare providers assign their own internal patient IDs, making it extremely difficult to track individuals across multiple platforms. In the U.S., the absence of a universal Unique Patient Identifier (UPI) - prohibited by federal law - forces reliance on demographic data that is often inconsistent or outdated.
Manual data entry introduces errors like typos, spelling variations, or the use of nicknames, all of which disrupt record matching. A Houston-area health system reported 138,000 cases where patients shared the same first name, last name, and date of birth [18], leading to false matches.
Frequent changes in addresses, phone numbers, or names further complicate matters. These updates often don’t sync across systems, creating data decay that worsens matching accuracy. For instance, middle name discrepancies contribute to over 50% of duplicate records [21]. Even Social Security Numbers are mismatched in 53.54% of duplicate cases, often due to default or missing values [21].
Another challenge is syntactic heterogeneity, or inconsistent formatting. For example, one system may record "Street" while another uses "St." Similarly, date formats like MM/DD/YYYY versus DD/MM/YY can confuse algorithms. Misspellings also play a role, causing 53.14% of first name mismatches and 33.62% of last name mismatches [21]. Poor interoperability between different EHR platforms only amplifies these problems, forcing reliance on less reliable matching methods.
Solution: Digital Identifiers and Improved Matching Technology
Federated Digital Identifiers (FDIs) could provide a solution by offering a unique, verified identity for individuals across various sectors, including healthcare, banking, and government. These identifiers ensure that each person has only one identity within a system, addressing the root cause of duplicate records [1][3]. Australia’s national federated identity system, with its 90% adoption rate, shows how effective this approach can be when implemented with an opt-out model [1][3].
Healthcare systems should also adopt probabilistic matching algorithms, which analyze patient attributes as variables and calculate the likelihood that two records belong to the same person [20][19]. While traditional algorithms achieve match rates of about 90%, more advanced referential matching - which incorporates third-party data like credit reports - can push match rates to 98% to 100% [19].
Biometric verification offers another layer of accuracy. Technologies like palm vein scanning, iris recognition, and facial recognition can reliably differentiate individuals - even twins - and link them to their digital records [19]. Privacy-conscious options, such as match-on-device systems, store encrypted biometric data on a patient’s smartphone rather than in centralized databases.
Implementing NIST 800-63 standards for Identity Assurance Levels (IAL) ensures identity proofing is done with a high degree of confidence, crucial for secure data exchanges [22][23]. For accessing health records, a minimum assurance level of IDIAL1.8 is recommended to prevent unauthorized access [23]. Systems should also verify previous addresses during identity checks, as these are often the only records available in older databases [22][23].
Standardizing data entry at the point of registration is another critical step. Healthcare providers should enforce strict naming conventions and use standardized formats for addresses, phone numbers, and dates of birth. For example, following U.S. Postal Service standards for addresses can reduce formatting inconsistencies [19][21]. Capturing patient photos during registration adds a simple yet effective layer of verification for clinicians [19]. Finally, continuous monitoring by identity experts who regularly review and merge duplicate records identified by algorithms can help maintain data integrity over time [21].
Challenge 4: Regulatory Compliance and Privacy Requirements
Navigating regulatory compliance is a cornerstone of ensuring federated identity systems not only improve data access but also maintain patient trust and security. In healthcare, this means balancing the stringent requirements of HIPAA with varying state laws, all while safeguarding sensitive patient information.
The HIPAA Security Rule mandates that organizations implement administrative, physical, and technical safeguards to protect electronic protected health information (ePHI) [24]. Additionally, HIPAA requires entities to retain documentation for six years, adding a layer of administrative responsibility [24]. The HITECH Act takes it a step further, extending these obligations to business associates, who are held civilly and criminally liable for noncompliance [24]. This makes it essential for all partners, including identity providers and credential service providers, to meet these high standards.
Data minimization is another critical consideration. Both HIPAA and NIST SP 800-63C emphasize sharing only the minimum necessary attributes for a transaction [24][25]. Yet, many systems still transmit more information than needed - for instance, sharing full birth dates instead of simply confirming if a patient is over 18. NIST highlights the risks of this approach:
"Processing attributes for different purposes from the original collection purpose can create privacy risks when individuals do not expect or are not comfortable with the additional processing" [25].
Compliance Obstacles in Federated Systems
Keeping up with evolving regulations while maintaining seamless system access is a significant challenge. For federal healthcare systems, introducing a federated identity system may trigger requirements like a System of Records Notice (SORN) and a Privacy Impact Assessment (PIA) under the Privacy Act of 1974 and the E-Government Act [25].
Consent management is another hurdle. Federated systems must secure explicit patient approval before transmitting attributes to a Relying Party unless an enterprise allowlist is in place [25]. However, as NIST points out:
"A link to a complex, legalistic privacy policy or general terms and conditions that a substantial number of subscribers do not read or understand is never an effective notice" [25].
Patients need clear, straightforward explanations about who is accessing their data and why. These challenges highlight the importance of automated compliance tools.
Solution: Automated Compliance and Privacy Management
Automated systems simplify compliance by integrating NIST-compliant frameworks. At Federation Assurance Level 2 (FAL2) and above, systems require assertion injection protection and pre-established trust agreements [16]. For FAL3, additional safeguards like holder-of-key assertions or bound authenticators are necessary [16]. These measures reduce reliance on manual processes while ensuring robust security.
Platforms like Censinet RiskOps™ are designed to automate compliance monitoring. They streamline risk assessments, provide continuous oversight of business associates, and help healthcare organizations manage Business Associate Agreements (BAAs) with all federated partners handling ePHI [24]. Automated audit controls also track and review activity in systems containing ePHI, meeting HIPAA's technical safeguard requirements [24].
For privacy management, organizations can adopt derived attribute values instead of sharing full personal details. For instance, transmitting a simple "Yes/No" for age verification instead of a full date of birth enhances privacy [25]. Additionally, blinding technologies like multi-level proxying prevent patient activity from being tracked [25]. These methods align with NIST's focus on making personal information usage predictable and manageable [25].
Challenge 5: User Adoption and Implementation Barriers
Even the most secure federated identity system can stumble if people don’t use it. This is where user adoption becomes a major challenge. One of the biggest frustrations for healthcare staff is credential fatigue - juggling multiple usernames and passwords for various applications. Many resort to risky shortcuts, like writing passwords on sticky notes, which not only adds to their frustration but also exposes security vulnerabilities.
Another pain point is the slow onboarding process. Manual provisioning often leaves new clinicians waiting days or even weeks for access to critical systems. This delay can disrupt patient care and frustrate staff. Multi-role providers face additional headaches with duplicate identities and mismatched profiles, making their workflows even more cumbersome.
The numbers tell a clear story: 71% of users abandon sign-up processes that are too complicated [5]. On top of that, 25% of patients who avoid accessing their online medical records cite security or privacy concerns as the main reason [5].
Obstacles to User Adoption
Technical barriers are a major deterrent. For example, requiring in-person identity verification at banks or government offices to set up digital identifiers can discourage participation right from the start [3][1]. For healthcare staff already overwhelmed by technology, the idea of learning yet another system - especially one with unclear benefits - can feel like just another burden.
Trust is another hurdle. In healthcare, internal actors cause more security incidents than external ones [5], which makes both staff and patients wary of centralized systems. Fragmented user experiences, such as requiring separate logins for different roles or facilities, only add to the frustration. To overcome these challenges, healthcare organizations need to simplify login processes and speed up onboarding.
Solution: Simplified Access with Single Sign-On
Single Sign-On (SSO) can ease credential fatigue by allowing users to access all healthcare resources with just one set of credentials. A great example of this is the Centers for Medicare & Medicaid Services (CMS) initiative. By partnering with the U.S. Digital Service (USDS), they replaced three separate identity systems with a single, API-driven interface for the Quality Payment Program (QPP). This change led to 15% of Medicare claims being submitted via the new API [5]. As David Koh, an engineer at USDS, explained:
"Identity was one of the biggest hurdles we had to cross, but we also wanted to provide a good experience to QPP users. Okta helped us achieve both those goals." [5]
SSO, combined with automated lifecycle management, not only reduces password fatigue but also enables immediate onboarding and de-provisioning. By integrating with systems like HR databases, Active Directory, and credentialing platforms, organizations can ensure "Day-1 access" for new hires and revoke credentials instantly for departing staff. This creates a centralized system of record for every individual.
Australia’s "My Health Record" system shows how an opt-out consent model can drive high adoption rates [3][1]. Similarly, progressive profiling - asking for information only when it’s needed - can make registration less intimidating and more user-friendly [5].
For managing third-party risks, platforms like Censinet RiskOps™ offer a way to streamline oversight of business associates and federated partners. These tools automate risk assessments and compliance checks, balancing ease of use with the need to protect patient data effectively.
Strategies for Implementing Federated Identity in Healthcare
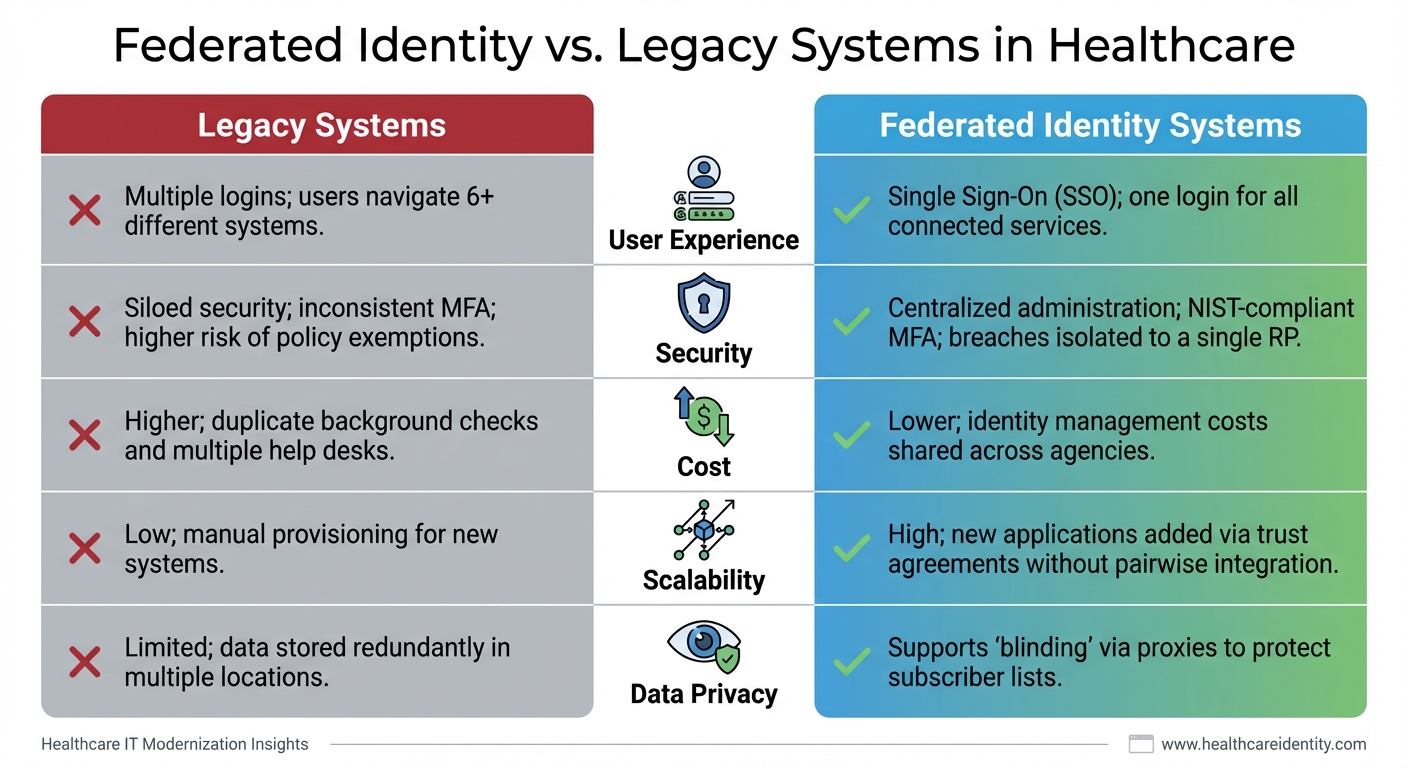
Federated Identity vs Legacy Systems in Healthcare: Key Differences
To tackle the challenges of federated identity in healthcare, a well-thought-out implementation strategy is essential. Both technical and organizational hurdles must be addressed to fully realize its potential. Success hinges on building a solid foundation and following a clear plan.
Start with three foundational elements: Trust Agreements, Identifier and Key Establishment, and a Federation Protocol [2]. Without these, even the most advanced system could falter.
Next, define the key roles involved:
- Credential Service Provider (CSP): Verifies user attributes.
- Identity Provider (IdP): Bridges accounts across systems.
- Relying Party (RP): Processes identity assertions [2].
Choose from three integration patterns based on your current infrastructure. These include using existing SSO (Pattern 1), temporarily relying on non-SSO identities (Pattern 2), or deploying a new SSO-supported IdP (Pattern 3) [4].
Adopt open standards like OpenID Connect (OIDC) and SAML 2.0 to ensure compatibility across systems. As Ryan M. Harrison, Pavan Jagalur, and Mukundan Srinivasan of Amida Technology Solutions caution:
"Vendor-locking to a closed standard is a death knell to innovation" [4].
Prepare support infrastructure before launching. Equip support teams with resources like FAQs and training on FHIR standards to handle increased inquiries and password resets [4]. To ensure smooth integration, consider using federation proxies to bridge gaps between protocols and formats [2].
These measures directly address earlier challenges, creating a clear path for effective implementation.
Comparison Table: Federated Identity vs. Legacy Systems
Below is a comparison of legacy systems and federated identity systems, showing how federated identity offers significant improvements.
| Feature | Legacy (Siloed) Systems | Federated Identity Systems |
|---|---|---|
| User Experience | Multiple logins; users navigate 6+ different systems [4] | Single Sign-On (SSO); one login for all connected services [4] |
| Security | Siloed security; inconsistent MFA; higher risk of policy exemptions [4] | Centralized administration; NIST-compliant MFA; breaches isolated to a single RP [4][12] |
| Cost | Higher; duplicate background checks and multiple help desks [4] | Lower; identity management costs shared across agencies [4] |
| Scalability | Low; manual provisioning for new systems [4] | High; new applications added via trust agreements without pairwise integration [2] |
| Data Privacy | Limited; data stored redundantly in multiple locations [4] | Supports "blinding" via proxies to protect subscriber lists [2] |
These strategies align with the earlier challenges, ensuring a secure, efficient, and scalable federated identity deployment in healthcare.
Conclusion
Federated identity systems tackle some of the toughest challenges in healthcare today. They address issues like fragmented data, security gaps, patient misidentification, and regulatory compliance - offering a streamlined solution that older systems simply can’t provide.
The numbers paint a stark picture. Between 2018 and 2023, large-scale data breaches doubled, and the number of affected individuals skyrocketed by over 1,000% [6]. At the same time, the average person now juggles about 90 online accounts, leading to password fatigue and risky behaviors like reusing credentials [6]. Federated identity systems step in by centralizing authentication, minimizing vulnerabilities, and incorporating robust identity proofing to combat these challenges effectively. These trends highlight the growing need for practical solutions that work in real-world scenarios.
And the results speak for themselves. Organizations that have implemented federated identity systems report improved interoperability and security. This demonstrates the potential healthcare systems can unlock by focusing on user-friendly and interoperable designs.
Jason Barr of ID.me sums it up well:
"Federated identity systems provide a unified and secure method for managing user identities across multiple platforms... reducing vulnerabilities associated with disconnected authentication methods" [6].
By adopting standardized protocols like SAML and OpenID Connect, healthcare organizations can offer seamless Single Sign-On experiences without compromising security.
The road ahead requires a strong commitment to open standards, centralized identity management, and adherence to NIST-compliant frameworks. By prioritizing these elements, healthcare providers can not only strengthen security and compliance but also deliver the integrated, patient-focused experiences that modern healthcare demands.
FAQs
How do we choose between SAML and OpenID Connect for our systems?
When deciding between SAML and OpenID Connect (OIDC), it’s all about your specific use case and infrastructure.
- SAML works best for legacy systems and enterprise single sign-on (SSO) in web-based applications. It provides robust security, especially in internal, web-focused environments.
- OIDC, on the other hand, is built on OAuth 2.0 and excels in modern setups like mobile apps, APIs, and cloud-native platforms.
Think about your environment, how scalable your solution needs to be, and your security priorities to choose the one that aligns with your organization’s needs.
What prevents an IdP breach from exposing all connected applications?
When an IdP (Identity Provider) is breached, it doesn’t automatically jeopardize all connected applications. This is because relying parties - the applications or services that depend on the IdP - take steps to verify the authenticity and integrity of the assertions they receive. These validation mechanisms serve as critical safeguards, ensuring that a compromise in one IdP doesn’t trigger a domino effect across the federation.
How can we reduce duplicate patient records without a national patient ID?
Reducing duplicate patient records in the absence of a national patient ID might seem tough, but it’s entirely doable with the right approach. One effective method is leveraging advanced algorithms that match records using demographic data, such as names, birthdates, and addresses. Standardizing data formats also plays a big role in maintaining consistency across systems.
Another powerful tool? Biometric identifiers like fingerprints or facial recognition, which can significantly improve accuracy in patient matching. On top of that, implementing cross-organizational frameworks helps healthcare systems share and follow best practices, ensuring more reliable patient record management across the board.


