HIPAA Compliance and Vendor Network Access
Post Summary
Healthcare organizations depend on vendors for critical services like EHR updates, medical billing, and cloud hosting. However, granting network access to these vendors introduces risks, including potential HIPAA violations. Without proper safeguards, sensitive patient data (ePHI) can be exposed, leading to severe fines and operational disruptions.
Key Takeaways:
- Vendors often need network access for updates, monitoring, and support.
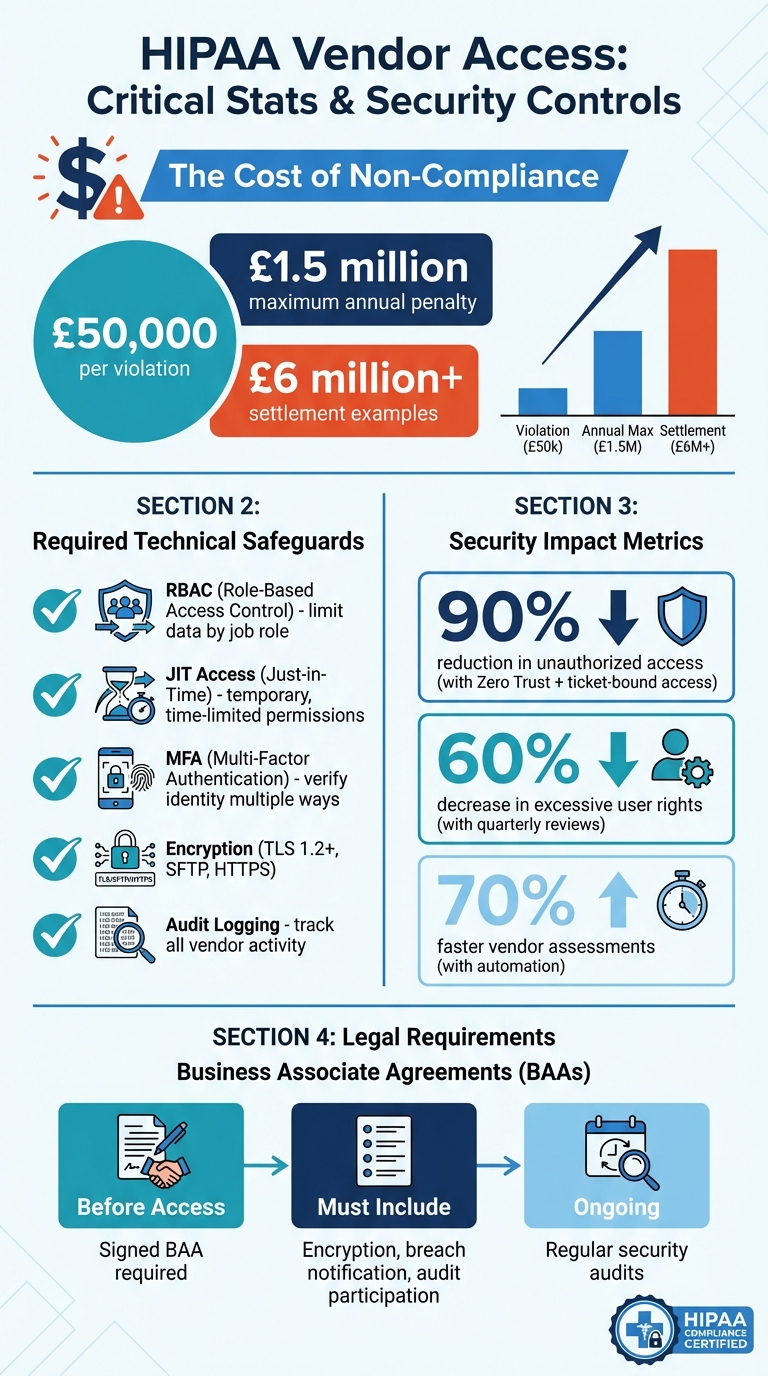
- HIPAA breaches can cost up to $50,000 per violation or $1.5 million annually, with some settlements exceeding $6 million.
- Remote access risks can be minimized through strict access controls, encryption, and Business Associate Agreements (BAAs).
- Tools like Role-Based Access Control (RBAC), Just-in-Time (JIT) access, and Multi-Factor Authentication (MFA) help secure vendor interactions.
- Platforms like Censinet RiskOps™ streamline vendor risk management and compliance reporting.
HIPAA Vendor Access Compliance: Key Statistics and Security Controls
HIPAA Requirements for Vendor Network Access
HIPAA Security Rule Standards for Vendor Access
The HIPAA Security Rule lays out essential safeguards that healthcare organizations must follow when granting vendors access to electronic protected health information (ePHI). According to §164.308(a)(4), covered entities must enforce access controls to ensure only authorized users can interact with ePHI. This means vendors need unique user IDs, role-based access controls that limit data access based on job responsibilities, and automatic logoff systems to prevent unauthorized access during inactivity [7][2][3].
Additionally, §164.312 mandates audit controls and secure transmission protocols. Organizations are required to log all vendor interactions with ePHI for accountability and ensure that transmitted data is encrypted and shared through secure channels [7][5][2]. Because remote vendor access poses increased risks, policies should limit access to only necessary systems, define strict timeframes for access, and require multi-factor authentication alongside unique credentials [1].
Real-world examples highlight the importance of these measures. The 2015 Anthem breach, for instance, exposed millions of records due to weak vendor access controls, including poor authentication practices and insufficient logging. This incident not only led to significant data loss but also resulted in heavy penalties, underscoring the importance of audit trails and proper network segmentation [1].
While technical safeguards are vital, they must be reinforced through binding agreements.
Business Associate Agreements (BAAs) and Vendor Responsibilities
Technical measures alone aren't enough to secure vendor access; legally binding Business Associate Agreements (BAAs) are equally critical. Before vendors can handle ePHI, healthcare organizations must establish a BAA that outlines the vendor’s responsibilities to protect patient data and comply with HIPAA requirements [5][6][2][4]. These agreements are non-negotiable and serve as a legal framework to hold vendors accountable for safeguarding ePHI.
A compliant BAA must include several key provisions. Vendors and their subcontractors are required to encrypt data, implement both physical and logical security controls, meet breach notification timelines, and participate in third-party risk assessments [6][2][4]. The agreement should also specify how ePHI can and cannot be used, while detailing incident response protocols. Without a signed BAA in place, granting vendors access to ePHI would directly violate HIPAA regulations.
sbb-itb-535baee
What Is HIPAA BAA Compliance For Third-party Vendor Access In Healthcare? - AI and Technology Law
How to Manage Vendor Network Access Securely
Protecting vendor network access is crucial for third-party risk management and preventing HIPAA breaches. Below are strategies to help maintain secure access while adhering to compliance standards.
Using Role-Based Access Control (RBAC)
Role-Based Access Control (RBAC) ensures vendors can only access the systems and data necessary for their specific tasks - nothing beyond that. This aligns with HIPAA's "Information Access Management" standard, which emphasizes limiting access to essential information [2]. For example, a billing vendor would only access billing records and payment details, not the full patient database.
Setting clear boundaries is key. A medical device technician might require access to diagnostic equipment but has no need for scheduling systems. Similarly, an IT support vendor may need access to network infrastructure but not clinical applications. By defining these boundaries upfront, organizations reduce data exposure and make it easier to adjust or revoke permissions as vendor contracts evolve.
Once roles are established, adding Just-in-Time (JIT) access and Multi-Factor Authentication (MFA) enhances security even further.
Applying Just-in-Time (JIT) Access and Multi-Factor Authentication (MFA)
JIT access provides vendors with temporary, time-limited access rather than ongoing credentials. For instance, a vendor addressing a technical issue would only have access for the duration of that task.
Meanwhile, MFA strengthens security by requiring vendors to confirm their identity through multiple verification methods. This might include something they know (like a password), something they have (such as a security token or mobile device), or even something they are (like a fingerprint). HIPAA's Security Rule explicitly requires verifying the identity of anyone accessing ePHI, and MFA meets this requirement [2].
Together, JIT and MFA create a controlled environment that significantly limits potential risks while supporting HIPAA’s requirement to guard against unauthorized access and threats [2].
To complement these measures, tracking vendor activity is equally important.
Tracking and Logging Vendor Activity
Keeping detailed logs of vendor actions not only meets HIPAA’s audit trail requirements but also allows for real-time monitoring of suspicious behavior. Automated systems can flag unusual activities, such as a vendor accessing files outside their assigned role or transferring large amounts of data unexpectedly.
Every vendor action - logins, file accesses, system changes, and data transfers - should be recorded with timestamps, user IDs, and descriptions. These logs are invaluable during audits and can serve as critical forensic evidence if a security breach occurs. Proactive monitoring helps mitigate risks to patient care caused by system downtime or unauthorized data access.
Integrating logging with JIT access ensures that all activities during temporary sessions are documented [2]. This level of visibility helps identify vulnerabilities, policy violations, or insider threats before they turn into more serious issues.
Technical Controls for Securing Vendor Access
Healthcare organizations need robust technical safeguards to manage vendor access and control the flow of data. These measures act as critical barriers, protecting ePHI even if vendor credentials are compromised. They also strengthen the access management strategies discussed earlier.
Network Segmentation and Zero Trust Models
Network segmentation breaks your infrastructure into isolated sections, allowing vendors to access only the systems they specifically need. Instead of granting broad access through VPNs or modems, microsegmentation limits vendor activity to a single, non-critical area. This approach prevents lateral movement within the network if a vendor's credentials are compromised.
This method complements the earlier strategy of restricting vendor permissions. Taking it a step further, Zero Trust architecture eliminates the assumption of "trusted" users. Vendors must verify their identity using individual credentials backed by MFA, with access granted only on a just-in-time basis tied to specific support tickets. Shared "support" accounts, which are a common security risk, are completely eliminated. Organizations that implement ticket-bound access and automated alerts for unauthorized activity have reported a 90% drop in unauthorized access [8].
Using virtual desktop infrastructures (VDI) ensures that ePHI is streamed rather than stored locally on vendor devices. This "zero data at rest" approach means no patient data is at risk if a vendor's device is lost or stolen. Standardizing access in this way simplifies administration, allowing IT teams to enforce consistent security policies across all vendor connections.
Data Encryption and Secure Communication Protocols
Encryption is essential for securing ePHI both at rest and in transit. All email communications with vendors should require TLS 1.2 or higher, while file transfers must use SFTP or HTTPS to replace outdated, less secure protocols. For vendor integrations that rely on APIs, deploying API gateways with rate limits and schema validation ensures that only authorized data is shared and prevents accidental over-disclosure.
Recording all privileged vendor sessions adds another layer of accountability. These session recordings create a detailed forensic trail, which can be invaluable during audits or breach investigations, documenting every action taken during a vendor's access.
Virtual Private Networks (VPNs) and IP Allowlists
In addition to encryption, VPNs and IP allowlists provide extra layers of security. VPNs establish encrypted tunnels for vendor connections, while IP allowlists restrict access to specific, pre-approved devices and locations. This ensures vendors cannot log in from unauthorized networks or personal devices that might lack proper security measures.
Regular reviews are also critical. Quarterly assessments by business owners ensure vendor roles remain current, while periodic "crown-jewel" data reviews have helped organizations cut excessive user rights by 60% [8]. These practices tighten control over who can access sensitive information, reducing unnecessary exposure to risk.
How Censinet RiskOps™ Supports Vendor Risk Management

Censinet RiskOps™ provides a streamlined approach to managing vendor risks while adhering to HIPAA requirements. Healthcare IT teams often face challenges in balancing extensive vendor oversight with compliance demands. This platform simplifies that balancing act by offering a cloud-based risk network that automates workflows, centralizes vendor management, and ensures consistent security standards across all vendors.
Automating Third-Party Risk Assessments
Manual vendor assessments can be time-consuming and resource-intensive. Censinet RiskOps™ changes the game by using HIPAA-compliant templates and real-time vendor data submissions to digitize the process. It quickly identifies critical issues - like missing multi-factor authentication or unsigned Business Associate Agreements - so teams can focus on urgent remediation efforts. This automation speeds up evaluations by as much as 70% compared to traditional manual methods [7]. By reducing vendor effort and minimizing human errors, the platform efficiently scales to handle large vendor ecosystems while maintaining continuous HIPAA compliance.
In addition to automation, the platform provides detailed reports to validate compliance efforts.
Cybersecurity Benchmarking and Compliance Reporting
Demonstrating HIPAA compliance to auditors and regulators becomes much easier with Censinet RiskOps™. The platform gathers data into exportable, HIPAA-aligned reports that include audit logs, risk scores, and remediation tracking [7]. These reports meet HHS documentation requirements for safeguards like transmission security and access controls. The Peer Benchmarking feature adds another layer of value, enabling healthcare organizations to compare their cybersecurity posture with industry peers. This helps identify gaps, align with HIPAA standards, and allocate resources more effectively [9].
The platform goes beyond assessments and reporting by ensuring secure access management.
Enforcing HIPAA-Compliant Access Controls
Censinet RiskOps™ also strengthens vendor collaboration through secure access controls. With Censinet Connect™, vendors can work seamlessly within a framework of strict security measures. AI-powered tools further enhance the process, enabling faster risk identification and response. The Connect Copilot feature supports vendors in completing assessments accurately, cutting down on back-and-forth communications while ensuring consistent and compliant submissions [9]. Additionally, the platform is designed to address healthcare-specific risks, such as medical device security and supply chain vulnerabilities, ensuring HIPAA compliance across all areas of operation.
These combined features allow healthcare organizations to efficiently manage vendor access and maintain robust HIPAA compliance throughout their networks.
Conclusion
Core Strategies for Maintaining HIPAA Compliance
Healthcare organizations face the challenge of granting vendors network access while ensuring patient data stays protected. A key step is securing Business Associate Agreements (BAAs), which legally bind vendors to safeguard patient information. Alongside this, role-based access control (RBAC) helps ensure each vendor representative only gets the exact level of access they need for their specific tasks [1].
On the technical side, tools like just-in-time (JIT) access offer temporary permissions, reducing unnecessary exposure to sensitive data [5]. By layering technical controls, organizations can enforce the "minimum necessary" access principle. This layered approach - spanning physical safeguards to advanced encryption - keeps vendor access tightly restricted [7].
These measures provide a strong foundation for improved oversight, especially when paired with specialized tools.
How Censinet RiskOps™ Streamlines Vendor Risk Management
Implementing these strategies effectively often requires automation to prevent overwhelming IT teams. Censinet RiskOps™ simplifies vendor oversight by automating risk assessments and enforcing access controls. It quickly flags gaps like missing multi-factor authentication (MFA) or unsigned BAAs.
With features like HIPAA-aligned reporting, peer benchmarking, and AI-driven assessment tools, Censinet RiskOps™ supports scalable vendor management while maintaining strong security. This solution ensures vendor access stays secure, compliant, and aligned with the latest healthcare cybersecurity standards.
FAQs
When is a BAA required for vendor network access?
A Business Associate Agreement (BAA) is a must-have when a healthcare organization shares Protected Health Information (PHI) with a vendor or subcontractor for reasons beyond treatment, payment, or healthcare operations. Its purpose is to comply with HIPAA regulations and protect sensitive patient data during these interactions.
What’s the safest way to give vendors temporary access to ePHI?
The best way to give vendors temporary access to electronic Protected Health Information (ePHI) is by implementing strict security measures. Start by using access controls, network segmentation, and continuous monitoring to safeguard sensitive data. Apply the Principle of Least Privilege and role-based access control (RBAC) to ensure vendors only access the systems they need and nothing more.
To further protect ePHI, track vendor activity in real time and maintain detailed audit logs to document their actions. Clear policies, along with Business Associate Agreements (BAAs), are also essential to ensure compliance with HIPAA regulations. These steps help create a secure environment while minimizing risks.
What should we log and monitor during vendor remote sessions?
To maintain HIPAA compliance, it's crucial to log and monitor critical activities during vendor remote sessions. Keep track of actions like user access, modifications, deletions, and configuration changes. Make sure to include timestamps and IP addresses in these logs. This level of detail helps you spot potential security issues as they happen, ensuring sensitive data stays protected.


