Incident Response Playbook for Healthcare Supply Chains
Post Summary
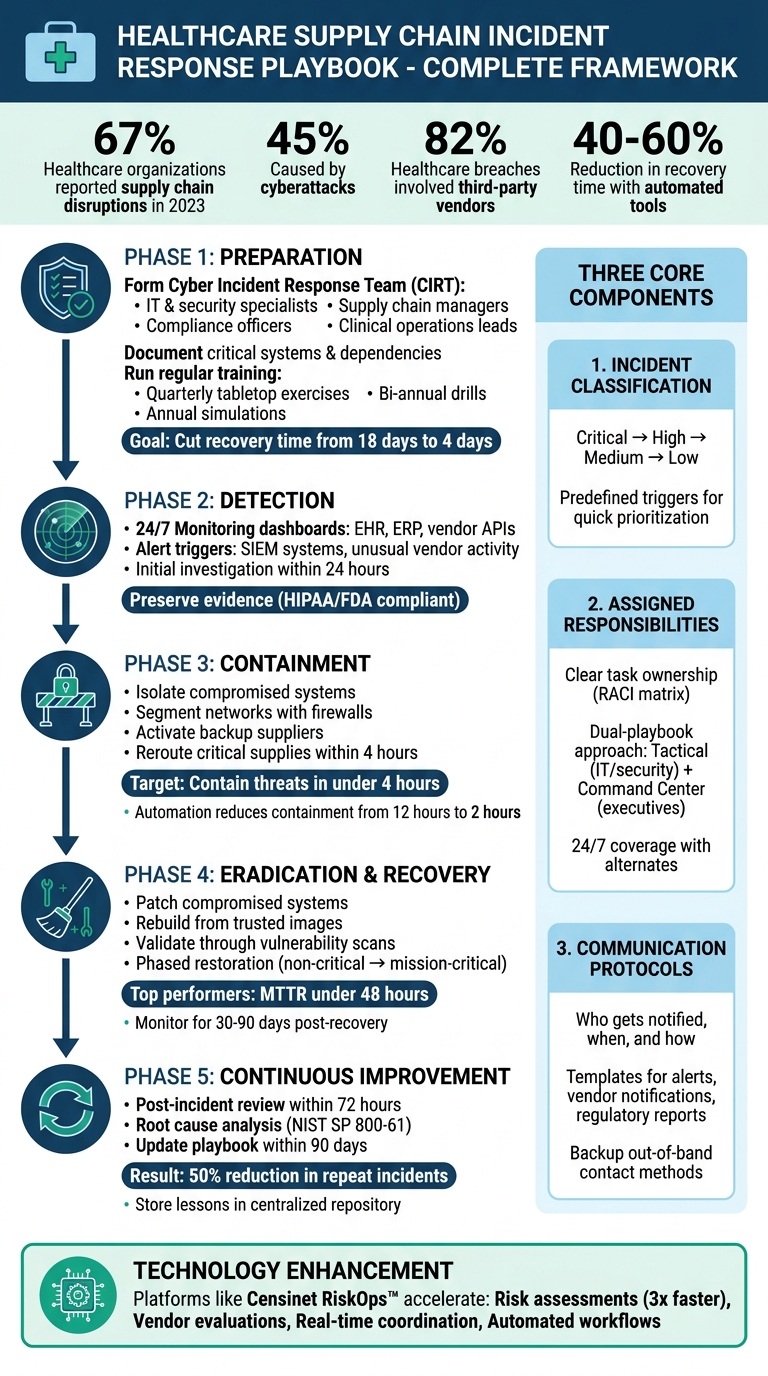
In healthcare, supply chain disruptions can directly impact patient safety. Delays in critical supplies like ventilators or chemotherapy drugs can postpone surgeries or even increase mortality risks. 67% of healthcare organizations reported supply chain disruptions in 2023, with 45% caused by cyberattacks. High-profile cases, like the October 2023 ransomware attack on UnitedHealth Group's Change Healthcare, highlight the severe financial and operational consequences.
A structured incident response playbook is essential to reduce downtime, ensure patient care, and maintain compliance. Key components include:
- Incident Classification: Categorize disruptions by severity for quick prioritization.
- Assigned Responsibilities: Define clear roles for IT, supply chain, compliance, and clinical teams.
- Communication Protocols: Establish who needs to be notified, timelines, and methods.
Preparation is critical. Organizations should form a Cyber Incident Response Team (CIRT), document critical systems, and conduct regular simulations. Using automated tools like Censinet RiskOps™ can further enhance response efficiency, cutting recovery times by 40–60%.
Healthcare Supply Chain Incident Response Framework: 5 Critical Phases
Stryker Cyberattack Disrupts Surgeries And Medical Supply Chains Across US | WION Podcast
sbb-itb-535baee
Core Elements of a Healthcare Supply Chain Incident Response Playbook
A well-crafted healthcare supply chain incident response playbook is essential for managing disruptions while safeguarding patient care. To be effective, it must be clear, actionable, and structured to prevent confusion, delays, or adverse impacts on patient outcomes. Three key components form the backbone of such a playbook: incident classification, assigned responsibilities, and communication protocols. Together, these elements ensure a seamless response during every phase of incident management.
Incident Classification and Severity Levels
Organizing incidents by severity is crucial for prioritizing resources and ensuring timely responses. A typical classification system ranges from Critical to Low, enabling teams to triage alerts as they arise and allocate resources effectively [9][10]. This process relies on predefined triggers, such as alerts from Security Information and Event Management (SIEM) systems, unusual vendor activities, or compromised credentials, to activate the appropriate response protocols [9]. By clearly defining severity levels, organizations can focus on critical disruptions immediately, directly safeguarding patient care.
Roles and Responsibilities
Assigning tasks to specific individuals or teams eliminates ambiguity during an incident. From isolating affected systems to notifying regulators, every step should have a designated owner. As John Hollenberger from CISO Collective explains, defining these responsibilities ensures a streamlined response [11]. Many healthcare organizations adopt a dual-playbook approach: one for tactical responses managed by IT and security teams, and another command center plan for executives like the CFO, Chief Medical Officer, and Chief Legal Officer [12]. Including backup communication methods, such as out-of-band contact details, is essential in case traditional channels like email are compromised [11]. This clarity in roles and responsibilities ensures uninterrupted supply chain operations and minimizes risks to patient care.
Communication Protocols
Clear communication protocols are essential for coordinating responses and maintaining transparency. These protocols should outline who gets notified, when, and through which channels. The playbook should include templates for internal alerts, vendor notifications, and regulatory reports, along with timelines for each notification step [9][10]. For example, if a vendor breach compromises patient data, the playbook must provide detailed instructions for notifying internal teams and external stakeholders, complying with regulatory requirements. Checklists for incident reporting - covering detection methods, affected systems, and response timelines - help ensure no critical details are overlooked [9]. By establishing these protocols, organizations can maintain transparency and regulatory compliance across the supply chain.
Preparation: Establishing Your Playbook Infrastructure
Building an effective incident response playbook goes beyond simply writing it down - it’s about creating a system that can withstand real-world challenges. This requires assembling the right team, mapping out critical systems, and practicing regularly to minimize costly disruptions. For example, one organization faced a ransomware attack that highlighted the price of being unprepared, with recovery delays leading to losses of $872 million. In response, they formed a 15-member Cyber Incident Response Team (CIRT) that included supply chain experts and began quarterly simulations. These efforts cut simulated recovery times from 18 days to just four, proving the value of preparation.
Assembling a Cyber Incident Response Team (CIRT)
A well-rounded CIRT is crucial for tackling the unique challenges of healthcare supply chain incidents. This team should include:
- IT and security specialists to handle technical issues.
- Supply chain managers who understand vendor relationships and logistics.
- Compliance officers familiar with HIPAA and FDA regulations.
- Clinical operations leads to evaluate patient care impacts.
The team leader - often the Chief Information Security Officer (CISO) - should report directly to the executive team and oversee all response activities. Use a RACI matrix (Responsible, Accountable, Consulted, Informed) to define each member’s role and appoint alternates to ensure 24/7 coverage.
A ransomware breach at Ascension Health in February 2024 showed how insufficient training can prolong outages. The organization later improved its response by implementing cross-functional teams and running regular tabletop exercises. This underscores the importance of a trained and coordinated CIRT. Once the team is established, the next step is mapping critical systems and vendor dependencies to streamline response times.
Documenting Critical Systems and Dependencies
To recover quickly, thorough documentation of critical systems and dependencies is essential. Start by creating an inventory that includes:
- Electronic health record (EHR) systems
- Inventory management software
- Key vendors, such as medical device suppliers and pharmaceutical distributors
- Dependencies like IoT devices and third-party logistics APIs
Use asset management software to maintain an up-to-date inventory, refreshed quarterly, and prioritize your top 20 critical vendors. Include network diagrams, data flows, recovery time objectives (RTOs), and single points of failure in this documentation. Store everything in a centralized repository, such as Microsoft 365, to ensure easy access and version control during emergencies. With 80% of healthcare breaches involving third-party vendors, mapping these dependencies is critical for identifying vulnerabilities. This documentation not only streamlines immediate responses but also serves as a foundation for training and simulations.
Running Regular Training and Simulations
Practice makes perfect, especially in high-pressure situations. Regular training ensures your team can execute the playbook effectively and helps uncover any weaknesses. Aim to conduct:
- Quarterly tabletop exercises with realistic scenarios, like a ransomware attack on a drug supplier.
- Bi-annual functional drills to test specific response elements.
- Annual full-scale simulations to mimic real incidents.
After each exercise, hold a debrief within 48 hours to review performance and track metrics like detection time (aiming for under four hours) and playbook adherence (targeting over 90%). This iterative process not only sharpens your team’s skills but also ensures they’re ready to respond swiftly when it matters most.
Response Phases: Detection Through Containment
When an incident hits, acting quickly and accurately is essential to keep your supply chain running smoothly. The detection-to-containment phase is where your playbook kicks into gear, pushing your team to swiftly identify, confirm, and stop threats. This rapid shift from detection to investigation lays the groundwork for everything that follows.
Detection and Investigation
With your systems already set up, constant monitoring takes center stage as your first line of defense against healthcare supply chain security challenges. Implement 24/7 dashboards that pull data from sources like electronic health records (EHR), enterprise resource planning (ERP) systems, and vendor APIs. These tools can catch irregularities in real time - like a sudden 20% drop in critical supply deliveries, which would immediately trigger an investigation [1].
When an alert goes off, your Cyber Incident Response Team (CIRT) must act fast to confirm the incident while preserving evidence according to HIPAA and FDA guidelines. Isolate the affected systems right away and create forensic images using write-blockers. For example, during a 2023 ransomware attack on a hospital vendor, investigators discovered that 15% of IV fluid supplies across five states were compromised. This information was crucial for planning containment measures [1][3]. The goal? Wrap up the initial investigation within 24 hours. Use tools like Wireshark for network traffic analysis and platforms like Censinet RiskOps™ to evaluate risks tied to third-party vendors efficiently.
Containment and Eradication
Containment is all about stopping the spread to protect patient care. Use firewalls to segment networks and isolate compromised vendor connections, and activate backup suppliers that were vetted during your preparation phase. For high-risk items like ventilators or connected medical devices, containment becomes a top priority. The aim is to reroute critical supplies within four hours to avoid delays in operating rooms [1][2].
During Ireland's HSE ransomware attack in 2021, air-gapping systems successfully contained the spread. However, the lack of automation forced manual workarounds for emergency care, leading to a staggering €100 million (around $110 million) in costs and an 11-month eradication period [1].
While containing the threat, evidence collection and vendor coordination must happen at the same time. Secure memory dumps and network traffic in tamper-proof repositories, and share only the necessary details of the compromise with vendors under non-disclosure agreements. Schedule daily secure video calls with designated escalation contacts. NIST SP 800-61 recommends joint "war rooms" for multi-party incidents, as real-time collaboration significantly improves outcomes [4]. Automation tools like Splunk Phantom can further speed things up by isolating endpoints, notifying vendors, and deploying patches. In fact, simulations show that automation can cut containment time from 12 hours to just 2 [1][3].
For safe eradication, follow a step-by-step process: confirm containment with vulnerability scans, patch or replace compromised software and firmware, wipe and rebuild affected systems from trusted images, and validate eradication through red-team testing. Document every action for the post-incident review. For instance, malware eradication from a drug infusion pump vendor's network restored full operations within 72 hours. Use metrics to measure success - such as containing threats within four hours, avoiding patient care diversions, and maintaining 100% evidence integrity. A 2024 study found that organizations using automated eradication recovered 30% faster [2]. Platforms like Censinet RiskOps™ can also help prioritize efforts by scoring vendor risks, focusing on suppliers critical to patient care [1][3].
Recovery and Continuous Improvement
After containment and eradication, the focus shifts to safely restoring systems. This step requires meticulous planning to prevent reintroducing vulnerabilities. Start by prioritizing critical systems like electronic health records (EHR) and inventory management, relying on pre-tested, verified backups. A phased approach often works best: begin with non-critical systems to test your processes, then move on to mission-critical ones. For example, during the 2022 Universal Health Services ransomware attack, phased EHR restoration - validated through HIPAA-compliant testing - helped reduce patient impact while ensuring no residual threats lingered [3][14]. This careful transition from containment to restoration is key to maintaining uninterrupted patient care.
System Restoration and Validation
Once systems are restored, validation ensures threats have been fully eliminated. This involves running thorough vulnerability scans, penetration tests, and functional checks on every restored system. To catch potential issues, monitor for unusual activity over a period of 30 to 90 days. The National Institute of Standards and Technology (NIST) also advises independent third-party audits to confirm no hidden threats remain in the network [4][2]. Organizations with strong incident response playbooks can significantly reduce recovery times, with top performers achieving a mean time to recover (MTTR) of under 48 hours for high-severity incidents [4][13]. Before resuming full operations, ensure sign-offs from your Cyber Incident Response Team (CIRT), legal, and compliance teams.
Post-Incident Review and Playbook Updates
Once recovery is complete, the next step is a post-incident review to understand what happened and how to improve. Convene your Cyber Incident Response Team within 72 hours to conduct a root cause analysis and document a detailed timeline of events. Use structured templates based on NIST SP 800-61 to identify detection gaps, response delays, and communication challenges [1][3]. For instance, after a 2023 supply chain cyberattack on a U.S. hospital network, the post-incident review led to the addition of vendor risk assessments in the response playbook, reducing future MTTR by 40% [2][15]. Organizations that conduct formal reviews often see repeat incidents drop by up to 50% within a year.
Continuous improvement is critical for staying ahead of emerging threats. Store all lessons learned in a centralized, version-controlled repository, and test updates through tabletop exercises within 30 days. These findings should directly inform updates to your incident response playbook. Despite 73% of healthcare organizations experiencing supply chain disruptions in 2024, only 42% have mature recovery processes [HHS Cybersecurity Report, 2024]. Tools like Censinet RiskOps™ can help streamline this process by providing rapid reassessments of third-party risks, offering data-driven insights into supply chain vulnerabilities [1][3]. Assigning a continuous improvement officer to oversee playbook updates ensures action items are fully implemented within 90 days, keeping your organization prepared for future challenges.
Using Technology Platforms to Improve Incident Response
Manual incident response methods can create delays that healthcare supply chains simply can't afford. When a vendor breach or supply disruption happens, teams need tools that provide real-time risk data, automated workflows, and collaboration features to avoid disruptions to patient care. Incorporating technology into your response plans enhances traditional detection and containment strategies by enabling faster, data-driven actions. According to the Ponemon Institute's 2024 research, healthcare-specific technology platforms can reduce the average response time (MTTR) during supply chain incidents by 40–60%. This efficiency is especially critical given that 82% of healthcare breaches in 2023 involved third-party vendors within supply chains[7].
Accelerating Risk Assessments with Censinet RiskOps™
Censinet RiskOps™ simplifies cybersecurity risk assessments by automating key tasks. Its recommendation engine evaluates risks across all types of supply chain vendors, from IT and medical supplies to facilities management and food services. Even vendors without automated oversight are included, ensuring no gaps in risk evaluation. The platform also generates corrective action plans automatically, helping teams move swiftly from detection to mitigation.
RiskOps™ assessments go beyond cybersecurity, addressing areas like operational resiliency, financial stability, subcontractor management, and international vendor oversight. These comprehensive evaluations help ensure uninterrupted delivery during disruptive events. Automated workflows further enhance efficiency by enabling faster communication and data collection during procurement or incident response. Gartner's 2025 analysis highlights that healthcare organizations using automated platforms like this complete vendor assessments three times faster than those relying on manual processes - a crucial advantage as supply chain disruptions grew by 25% year-over-year in 2024[8].
Improving Response Coordination Through Automation
Automation isn't just about risk assessment; it also transforms how teams coordinate their responses in real time. By delivering actionable insights and decision support, automation helps managers address challenges like inventory balancing, supplier redundancy, and safety. Automated alert routing ensures that the right team members are notified based on incident severity, while escalation procedures activate for high-priority events. This allows response teams to focus on strategic decisions instead of time-consuming tasks like log collection or status reporting.
Collaborative dashboards play a vital role during incidents, enabling dynamic task assignments while ensuring compliance with HIPAA for supply chain events involving PHI[5]. Risk teams maintain control through configurable rules and review processes, ensuring that automation supports rather than replaces critical decision-making. To maximize the benefits of these platforms, organizations should integrate them with existing CIRT tools for automated alerting on supply chain risks. Conducting quarterly simulations using platform features can also help validate workflows and prepare teams for real incidents[6]. By adopting these automated tools, healthcare organizations can better protect their supply chains and maintain continuity in patient care.
Conclusion
Healthcare supply chain incidents require a well-prepared and organized response. Developing an incident response playbook helps shift from chaotic, reactive management to a structured, proactive approach that safeguards patient care and keeps operations running smoothly. By combining clear protocols with defined team roles, the playbook ensures quick and coordinated action. Assigning responsibilities minimizes confusion during high-pressure situations, reducing the risk of missed steps. Effective communication plans keep everyone informed while protecting sensitive information. Regular reviews and updates to the playbook foster a culture of improvement, helping your organization stay ready for new challenges in healthcare supply chains.
This foundation paves the way for incorporating advanced tools and technologies. Platforms like Censinet RiskOps™ can speed up risk analysis, simplify vendor assessments, and improve real-time coordination. When paired with skilled personnel and well-established processes, these tools significantly enhance the effectiveness of your response plan. However, human expertise and strong organizational preparation remain the backbone of any successful incident response.
Start by forming your Cyber Incident Response Team (CIRT), documenting critical systems, and setting up basic communication frameworks. As your team grows more capable, move toward regular practice drills and automated workflows. Think of this as a step-by-step journey rather than a single, overwhelming task.
Organizations that follow this approach will be better equipped to handle supply chain disruptions, ensuring both patient safety and operational stability. This method not only strengthens supply chain resilience but also supports the ultimate goal of delivering quality healthcare. Investing in training, simulations, and refining your response playbook is crucial to avoiding severe consequences. Supply chain issues can directly affect patient outcomes, leading to delays in surgeries or medication shortages. By treating incident response as a critical aspect of patient safety, healthcare organizations can build the resilience needed to protect their mission and serve patients effectively during disruptions.
FAQs
What should trigger activating the supply chain incident playbook?
The supply chain incident playbook comes into action when situations such as vendor disruptions, cyberattacks, natural disasters, or operational failures threaten essential healthcare services or patient safety. These triggers are designed to ensure a swift and effective response, safeguarding healthcare operations and upholding the quality of patient care.
How do we choose the right severity level for a supply disruption?
To gauge how serious a supply disruption is, evaluate its effect on patient care, daily operations, and regulatory compliance. Look at key aspects like the scale of the disruption, which systems are impacted, and how urgent the situation is. For example, a shortage of life-saving medications would demand swift intervention. Frameworks like the NIST guidelines can help classify these incidents and guide you in prioritizing responses based on the risks and possible outcomes.
What vendor info should we document before an incident happens?
Before any incident occurs, it’s essential to have key vendor information documented. This includes their incident response policies, security controls, breach notification procedures, and adherence to standards like HIPAA and SOC 2. Having this information on hand ensures you're ready to handle disruptions and work efficiently with vendors during a crisis.


