Patient Safety and Vendor Risk: The Hidden Threats Healthcare Organizations Must Address
Post Summary
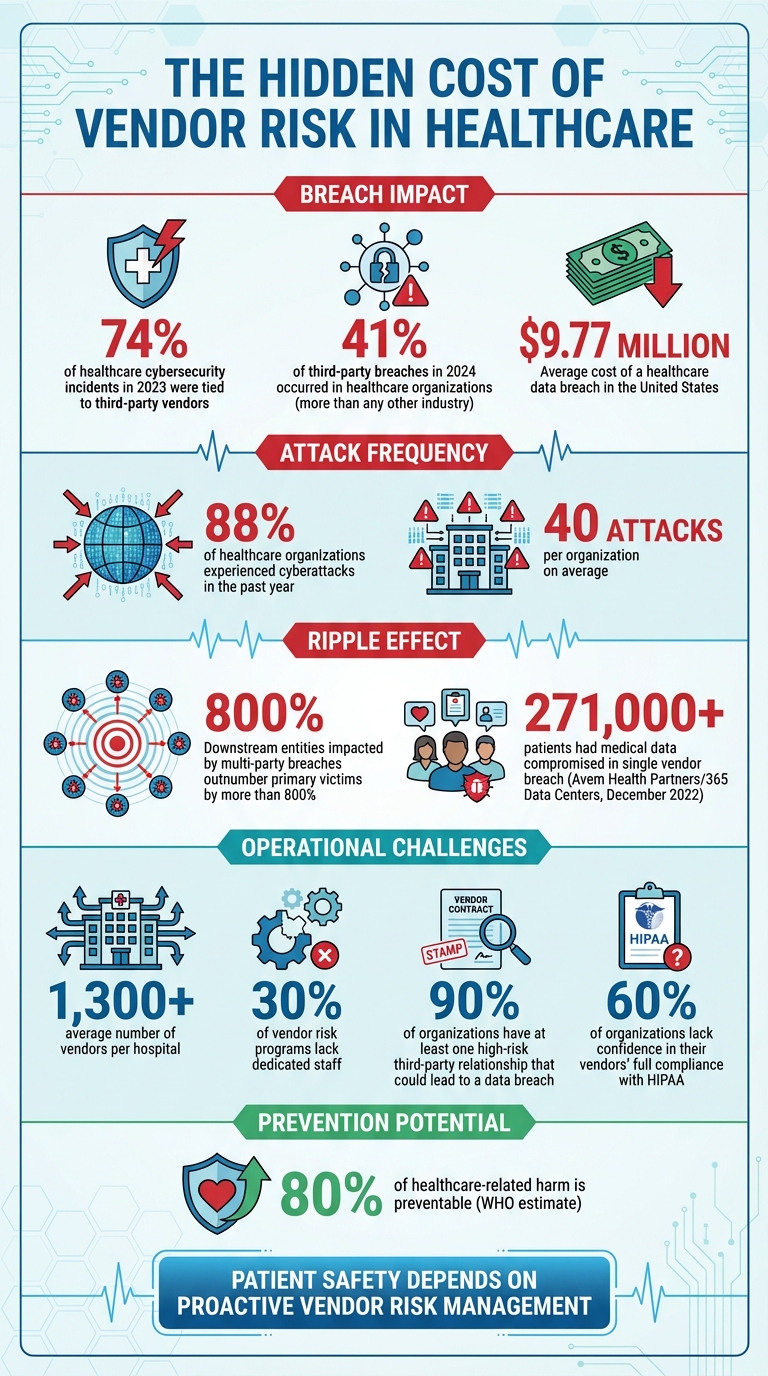
When vendor incidents occur, the consequences for patient care are immediate and severe — EHR breaches can delay critical treatments, poor EHR usability can cause clinical errors, and data compromises can cause patients to withhold medical information during future visits, with the downstream impact of multi-party breaches outnumbering primary victims by more than 800% and the average cost of a U.S. healthcare breach reaching $9.77 million.
Current programs rely on static one-time assessments, self-reported vendor questionnaires that offer minimal assurance, and fragmented risk ownership across IT, procurement, compliance, and clinical teams — with nearly 80% of organizations having vendor risk programs but 30% lacking dedicated staff to manage them, leaving vulnerabilities unnoticed until incidents occur that directly jeopardize patient safety.
Compliance-focused strategies aim to avoid fines and penalties through periodic audits and self-reported questionnaires, while patient-safety-focused strategies require real-time insight into vendor security and operational risks, rapid identification and mitigation of threats before patient harm occurs, and direct assessment of how vendor risks affect patient outcomes including care delays, complications, and mortality rates.
A patient-safety-focused framework requires a detailed vendor inventory outlining each vendor's role in patient care, standardized assessments throughout the vendor lifecycle including pre-contract, periodic, and offboarding evaluations, strong BAAs with security requirements and breach notification protocols, continuous monitoring for high-risk vendors using certifications like HITRUST and SOC 2 Type 2, network segmentation to limit vendor access, and regular testing of incident response and recovery plans.
Key metrics include system downtime caused by vendor issues (minutes or hours of clinical system unavailability), remediation time for identified security gaps after vendor assessments, financial consequences tied to downtime and remediation delays, vendor tier distribution, fourth-party vendor risk exposure, SLA breach trends, and compliance scorecards tracking vendor adherence to HIPAA — with continuous monitoring essential given that nearly 90% of organizations report at least one high-risk third-party relationship that could lead to a data breach.
Censinet RiskOps™ enables vendors to complete security questionnaires in seconds rather than weeks, uses Censinet AI to summarize vendor evidence and identify fourth-party risks, routes critical findings to the right stakeholders through advanced routing that functions like air traffic control, and provides a centralized real-time dashboard that enables healthcare organizations to embed vendor risk management seamlessly into daily clinical operations with patient care and safety at the forefront.
Healthcare organizations rely on third-party vendors for critical services like EHR systems and medical devices. But when vendors face cybersecurity breaches or failures, patient safety is directly at risk. These issues can delay care, disrupt emergency operations, and lead to poor clinical decisions. Current vendor risk management approaches often fall short, focusing on compliance rather than protecting patients.
Key Insights:
Healthcare providers must shift from compliance-focused strategies to patient-centered approaches to safeguard care and reduce risks.
Healthcare Vendor Risk Statistics: Impact on Patient Safety and Cybersecurity
Threats from Vendor Ecosystems
What Drives Risk in Vendor Ecosystems
Relying on static, one-time assessments isn't enough to manage vendor risks effectively. Limited visibility into vendor security practices leaves critical threats unchecked. Many organizations depend on self-reported questionnaires, where vendors essentially evaluate their own security measures. This method offers minimal assurance that vendors are actually implementing the practices they claim to follow.
Adding to this challenge, risk ownership is often fragmented across IT, procurement, compliance, and clinical teams. This lack of coordination makes it difficult to get a clear picture of vendor risks. While nearly 80% of organizations have vendor risk programs, 30% of them lack dedicated staff to manage these risks, allowing vulnerabilities to go unnoticed until an incident occurs [2]. These hidden risks can lead to vendor-related incidents that directly jeopardize patient safety.
Patient Safety Impacts from Vendor Incidents
When vendor incidents occur, the consequences for patient care can be immediate and severe. For example, in December 2022, over 271,000 patients of Avem Health Partners had their medical data compromised after a breach at Avem's vendor, 365 Data Centers [2]. The ripple effects of such incidents are staggering - downstream entities impacted by multi-party breaches outnumber primary victims by more than 800% [2]. A single vendor breach can affect hundreds of healthcare organizations and millions of patients.
Beyond cyberattacks, vendor-related issues with Electronic Health Records (EHRs) can also harm patients. According to The Pew Charitable Trusts, "EHR usability - their layout, design, customizations, and how they fit into different workflows - can impact patient safety" [1]. Poor usability in EHR systems can lead to errors that directly affect patient outcomes.
Compliance-Focused vs. Patient-Safety-Focused Vendor Risk
The difference between a compliance-driven approach and one centered on patient safety is stark. Compliance programs primarily aim to avoid fines and penalties, while patient-safety-focused strategies assess how vendor risks affect patient outcomes. The financial stakes are immense - the average cost of a healthcare breach in the United States is $9.77 million [4]. But the human cost is even higher: 88% of healthcare organizations experienced cyberattacks in the past year, averaging 40 attacks per organization [4]. These breaches result in care delays, longer hospital stays, more complications, and even higher mortality rates [4].
Feature
Regulatory-Driven
Patient-Centric
Limited to regulatory requirements; relies on self-reported questionnaires and periodic audits.
Requires real-time insight into vendor security, operational risks, and impact on clinical workflows.
Reactive to regulatory changes; audit cycles are slow and infrequent.
Focuses on rapid identification, assessment, and mitigation of risks to prevent patient harm.
Aims to avoid fines and legal penalties; patient outcomes are an indirect concern.
Prioritizes preventing adverse events, care delays, complications, and mortality.
The World Health Organization estimates that up to 80% of healthcare-related harm is preventable [3]. This highlights the urgent need for healthcare organizations to move beyond regulatory checklists and develop vendor risk programs that actively prevent harm. A patient-safety-focused approach is the only way to address these hidden and evolving threats effectively.
Gaps in Vendor Risk Management Programs
Program Gaps and Their Consequences
Healthcare organizations often struggle with significant weaknesses in how they track and monitor vendors. On average, a hospital works with over 1,300 vendors[6][7], yet many fail to maintain effective oversight of these relationships. Without proper tracking systems, organizations leave themselves vulnerable - not just to security threats but also to risks that directly impact patient safety.
Ongoing vendor monitoring is essential to catch and address emerging threats. In 2023, third-party vendors were linked to 74% of cybersecurity incidents or unauthorized access cases in healthcare[5]. These gaps in oversight lead to compliance issues and operational disruptions that can compromise the quality of care. For example, when systems go offline or supply chains are interrupted, patient safety is often at risk.
Another issue lies in the lack of enforceable cybersecurity standards within business associate agreements[6]. When breaches occur, this weak accountability leaves healthcare providers scrambling to respond. Additionally, many organizations fail to include vendors in their incident response plans or disaster recovery tests, making it difficult to coordinate during emergencies that affect patient care[6]. A culture that penalizes incident reporting further complicates the ability to address vulnerabilities, as it discourages timely and transparent communication about breaches[5].
Failure to Meet Regulatory Standards
These operational gaps also put organizations at odds with regulatory requirements. Many vendor risk management programs fail to meet the standards outlined by HIPAA, NIST, and HHS for managing third-party and supply chain risks. Alarmingly, healthcare organizations accounted for 41% of third-party breaches in 2024, more than any other industry[6]. This statistic highlights the failure of current practices to effectively mitigate vendor-related risks.
A common misconception is that HIPAA compliance alone is sufficient. However, patient safety risks extend beyond data privacy. Non-IT vendors - such as medical equipment suppliers, medication distributors, and health and safety system providers - play a critical role in care delivery[5][7]. When these vendors face disruptions, the ripple effect on patient care is immediate and severe. Yet, many risk management programs fail to address these operational dependencies, leaving patients exposed to preventable safety risks and organizations vulnerable to regulatory penalties.
Building a Patient-Safety-Focused Vendor Risk Framework
Steps for Managing Vendor Risk
For healthcare organizations, managing vendor risk isn't just about meeting compliance requirements - it’s about safeguarding patient safety. A robust framework starts with creating a detailed vendor inventory that outlines each vendor's specific role in supporting patient care.
It’s crucial to perform standardized assessments throughout the vendor lifecycle. This means evaluating vendors before signing contracts, periodically during their tenure, and when the partnership ends. These assessments should examine key areas like security credentials, history of breaches, data protection practices, and their potential impact on patient safety. Additionally, strong Business Associate Agreements (BAAs) are essential. These agreements should clearly spell out security requirements, breach notification protocols, and data-handling procedures for the end of the contract term [5][8].
Annual reviews are no longer enough. Continuous monitoring is now the gold standard, especially for high-risk vendors. Using certifications like HITRUST, SOC 2 Type 2, or ISO 27001 can provide real-time assurance of compliance [9]. Organizations should also adopt network segmentation to limit vendor access to only the necessary systems. To prepare for potential disruptions, regular testing of incident response and recovery plans - complete with simulations of vendor-related failures - ensures that clinical teams can continue delivering care without interruption.
Using Censinet RiskOps™ and Censinet AI
Managing thousands of vendor relationships can feel overwhelming, but Censinet RiskOps™ simplifies the process through automation. The platform allows vendors to complete security questionnaires in seconds instead of weeks. Meanwhile, Censinet AI steps in to summarize vendor evidence, document integration details, identify fourth-party risks, and generate risk summary reports from all relevant assessment data.
What sets this system apart is its human-in-the-loop approach. While automation handles the heavy lifting, experienced risk teams make the critical decisions. Advanced routing features act like "air traffic control", ensuring that important findings reach the right stakeholders, including members of the AI governance committee. A centralized dashboard ties it all together, offering a real-time, unified view of risks across all vendor relationships. This streamlined approach enables healthcare organizations to embed vendor risk management seamlessly into their daily clinical operations, keeping patient care and safety at the forefront.
sbb-itb-535baee
Integrating Vendor Risk into Healthcare Operations
Making Risk Management Part of Daily Operations
In healthcare, managing vendor risk shouldn't be an afterthought - it needs to be woven into everyday operations. One effective way to do this is by embedding vendor risk assessments directly into procurement workflows. This ensures that risk and security teams evaluate potential impacts on patient safety - like vendor access to clinical systems or risks of service delays - before contracts are signed.
Another key step is creating clear, collaborative incident response plans with vendors. These plans should outline protocols, escalation procedures, and recovery timelines. Regular simulations, such as ransomware attack drills or system outage scenarios, can help clinical teams practice maintaining care continuity under pressure. Aligning these efforts with broader disaster recovery strategies ensures that vendor-related risks are seamlessly incorporated into overall business continuity planning. This way, patient care can continue uninterrupted, even if a critical vendor faces disruption.
This integrated, proactive approach lays the groundwork for accurately measuring how vendor risks affect operations and, ultimately, patient safety.
Measuring Vendor Risk Impact on Patient Safety
To understand how vendor risks impact patient safety, healthcare organizations need to track the right metrics. A key indicator is system downtime - how many minutes or hours were clinical systems unavailable due to vendor issues? Another critical metric is remediation time, which measures how quickly identified security gaps are resolved after vendor assessments. Financial consequences tied to system downtime and remediation delays should also be monitored.
Other valuable metrics include vendor tier distribution, exposure to risks from fourth-party vendors, and trends in SLA breaches. Continuous monitoring and detailed recordkeeping are essential here. For example, nearly 90% of organizations report having at least one high-risk third-party relationship that could lead to a data breach, illustrating why ongoing visibility is so crucial [10][11]. Additionally, a survey revealed that 60% of organizations lack confidence in their vendors' full compliance with HIPAA. This highlights the need for compliance scorecards as a measurable way to track vendor performance [11].
By focusing on these metrics, healthcare organizations can better connect vendor risk to operational tools, enabling continuous risk management.
How Censinet Supports Daily Risk Management
Censinet RiskOps™ offers a centralized solution for managing vendor risks, keeping patient safety at the forefront. Its dashboard aggregates real-time data, acting like a command center for risk management. With advanced routing capabilities, critical findings and tasks are automatically sent to the right teams - whether it's procurement, clinical leadership, or even an AI governance committee. It’s like having air traffic control for vendor risk.
The platform also ensures continuous oversight by automating workflows that track remediation efforts and trigger reassessments when needed. Expert validation adds an extra layer of assurance to automated processes. By bringing together vendor risk data, task management, and stakeholder collaboration into one streamlined system, Censinet enables healthcare organizations to respond more quickly to threats while keeping patient safety at the heart of every decision.
Conclusion
Healthcare organizations must view vendor risk management as a responsibility tied directly to patient safety. In this industry, the stakes are far too high - lives depend on it. Protecting patients should always take precedence over simply satisfying regulatory requirements like HIPAA [12]. Cybersecurity and third-party risks are not just about compliance; they are integral to safeguarding care [5]. When vendors face breaches or disruptions, the consequences ripple directly to patient well-being.
This reality calls for a shift in mindset - from focusing solely on compliance to adopting proactive, patient-centered risk strategies. Traditional risk management approaches often fall short, leaving critical gaps unaddressed. A framework that prioritizes patient safety is the natural next step in healthcare cybersecurity. This approach demands real-time monitoring, automated processes, and scalable solutions to manage thousands of vendor relationships effectively. Enter Censinet. With its RiskOps™ platform powered by integrated AI, Censinet redefines the process, slashing assessment times and centralizing vendor data on a large scale [13][14].
Ed Gaudet, CEO and founder of Censinet, emphasizes this shift:
"Our collaboration with AWS enables us to deliver Censinet AI to streamline risk management while ensuring responsible, secure AI deployment and use. With
.
By combining automation with human oversight, healthcare organizations can expand their operational capabilities without sacrificing control.
The way forward is straightforward. Healthcare providers must adopt centralized platforms that integrate real-time data, direct critical findings to the appropriate teams, and maintain continuous vendor risk oversight. When vendor risk management is aligned with patient safety, healthcare leaders can ensure uninterrupted, high-quality care delivery.
FAQs
What steps can healthcare organizations take to manage vendor risks and protect patient safety?
Healthcare organizations can strengthen their approach to vendor risk management by conducting thorough risk assessments before bringing vendors on board and continuously monitoring their security measures. Setting specific security requirements in contracts and developing strong incident response plans are key steps in this process.
Focusing on vendors based on the sensitivity of the data they manage and their involvement in critical operations is equally important. Keeping a clear view of all third-party relationships and working closely with vendors to ensure compliance and implement timely security updates can go a long way in reducing risks and safeguarding patient safety.
What’s the difference between compliance-focused and patient-safety-focused vendor risk strategies?
When it comes to vendor risk management, compliance-focused strategies aim to ensure that vendors align with key regulatory standards such as HIPAA, HITRUST, and SOC 2. These strategies prioritize thorough due diligence during the onboarding process and ongoing compliance checks to maintain adherence to legal and industry-specific requirements.
On the other hand, strategies centered on patient safety go beyond compliance. They actively assess risks that could directly impact the quality of patient care. This includes identifying potential issues like operational disruptions or cybersecurity threats that might jeopardize care delivery or endanger patient safety.
Why is it important to continuously monitor vendors to prevent cybersecurity risks in healthcare?
Continuous vendor monitoring plays a crucial role in helping healthcare organizations stay ahead of cybersecurity risks. It allows them to spot vulnerabilities, implement strict access controls, and identify unusual activity at every stage of the vendor relationship - whether during onboarding, active collaboration, or offboarding.
With real-time monitoring in place, healthcare organizations can act swiftly to address potential threats. This not only reduces the chances of data breaches and operational interruptions but also safeguards patient safety. Ultimately, it strengthens the healthcare system’s defenses, protects sensitive information, and helps maintain the trust of patients and stakeholders.
Related Blog Posts
- Building Vendor Risk Frameworks for Healthcare IT
- Patient Safety and Vendor Risk: The Hidden Threats Healthcare Organizations Must Address
- Healthcare IT Infrastructure Vendor Risk: Network, Security, and System Reliability
- Insurance and Benefits Administration Vendor Risk for Healthcare Organizations
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":[{"@type":"Question","name":"What steps can healthcare organizations take to manage vendor risks and protect patient safety?","acceptedAnswer":{"@type":"Answer","text":"<p>Healthcare organizations can strengthen their approach to vendor risk management by conducting thorough risk assessments before bringing vendors on board and continuously monitoring their security measures. Setting <strong>specific security requirements in contracts</strong> and <a href=\"https://censinet.com/perspectives/5-steps-to-train-incident-response-teams-in-healthcare\">developing strong incident response plans</a> are key steps in this process.</p> <p>Focusing on vendors based on the sensitivity of the data they manage and their involvement in critical operations is equally important. Keeping a clear view of all third-party relationships and working closely with vendors to ensure compliance and implement timely security updates can go a long way in reducing risks and safeguarding patient safety.</p>"}},{"@type":"Question","name":"What’s the difference between compliance-focused and patient-safety-focused vendor risk strategies?","acceptedAnswer":{"@type":"Answer","text":"<p>When it comes to vendor risk management, compliance-focused strategies aim to ensure that vendors align with key regulatory standards such as <strong>HIPAA</strong>, <strong>HITRUST</strong>, and <strong>SOC 2</strong>. These strategies prioritize thorough due diligence during the onboarding process and ongoing compliance checks to maintain adherence to legal and industry-specific requirements.</p> <p>On the other hand, strategies centered on patient safety go beyond compliance. They actively assess risks that could directly impact the quality of patient care. This includes identifying potential issues like operational disruptions or cybersecurity threats that might jeopardize care delivery or endanger patient safety.</p>"}},{"@type":"Question","name":"Why is it important to continuously monitor vendors to prevent cybersecurity risks in healthcare?","acceptedAnswer":{"@type":"Answer","text":"<p>Continuous vendor monitoring plays a crucial role in helping healthcare organizations stay ahead of <a href=\"https://www.censinet.com/blog/5-ways-to-reduce-3rd-party-cybersecurity-risks-per-18-experts\">cybersecurity risks</a>. It allows them to spot vulnerabilities, implement strict access controls, and identify unusual activity at every stage of the vendor relationship - whether during onboarding, active collaboration, or offboarding.</p> <p>With real-time monitoring in place, healthcare organizations can act swiftly to address potential threats. This not only reduces the chances of data breaches and operational interruptions but also safeguards patient safety. Ultimately, it strengthens the <a href=\"https://www.censinet.com/blog/stronger-together-a-response-to-rising-systemic-risk-in-healthcare\">healthcare system’s defenses</a>, protects sensitive information, and helps maintain the trust of patients and stakeholders.</p>"}}]}
Key Points:
What hidden threats in vendor ecosystems create patient safety risks that compliance programs miss?
- Limited visibility into vendor security practices is the foundational gap — many organizations depend on self-reported questionnaires where vendors essentially evaluate their own security measures, providing minimal assurance that the practices claimed are actually implemented and leaving critical threats unchecked between formal assessment cycles
- Fragmented risk ownership across IT, procurement, compliance, and clinical teams makes it structurally difficult to get a clear picture of vendor risks — no single team has the authority and information needed to act on cross-functional vendor threats, and the coordination gaps between teams create blind spots that incidents reliably exploit
- The 800% downstream impact multiplier of multi-party breaches illustrates the structural interconnection of healthcare vendor ecosystems — the December 2022 Avem Health Partners breach through vendor 365 Data Centers exposed over 271,000 patients' records, demonstrating that a single vendor breach can affect hundreds of healthcare organizations and millions of patients beyond the primary incident
- EHR usability failures from vendor design choices create patient harm that compliance programs do not measure — poor EHR layout, design, and workflow fit can lead to clinical errors that directly affect patient outcomes, a risk category that is entirely invisible to security-focused vendor assessments
- Non-IT vendors including medical equipment suppliers, medication distributors, and health and safety system providers play critical roles in care delivery that compliance programs focused on data privacy systematically miss — when these vendors face disruptions, the impact on patient care is immediate and severe regardless of whether any ePHI was compromised
What are the critical gaps in current healthcare vendor risk management programs?
- Static, one-time assessments cannot keep pace with evolving vendor threats — vendor risks change as new threats arise, systems are updated, and vendor operations evolve, making point-in-time assessments inadequate for maintaining the real-time visibility that patient safety requires
- 74% of healthcare cybersecurity incidents in 2023 were tied to third-party vendors — this statistic reflects the scale of the oversight failure in current programs, with healthcare accounting for 41% of third-party breaches in 2024 across all industries, more than any other sector
- Lack of enforceable cybersecurity standards in business associate agreements leaves healthcare providers without contractual accountability when breaches occur — weak BAA language means vendors face minimal consequence for security failures that directly harm patients and create significant organizational liability
- Failure to include vendors in incident response plans or disaster recovery tests means that when vendor-related emergencies occur, coordination is improvised rather than practiced — clinical teams cannot maintain care continuity without knowing in advance how they will operate when critical vendor systems are unavailable
- A culture that penalizes incident reporting discourages the timely, transparent communication about breaches that effective vendor risk management requires — organizations that treat reported incidents as failures rather than information consistently learn about vendor problems later and at greater patient safety cost than organizations that actively surface and address vulnerabilities
How should healthcare organizations differentiate compliance-focused from patient-safety-focused vendor risk strategies?
- The fundamental difference is what success looks like — compliance programs measure success by audit outcomes and regulatory adherence, while patient-safety-focused programs measure success by whether vendor risks are identified and mitigated before they affect patient outcomes, care quality, or clinical continuity
- Real-time visibility versus periodic audit cycles is the operational distinction — compliance programs that audit vendors annually cannot detect the security changes, new vulnerabilities, and operational failures that create patient safety risk between audit cycles, while continuous monitoring provides the ongoing visibility that patient-centered programs require
- WHO estimates that up to 80% of healthcare-related harm is preventable — this framing positions vendor risk management as a harm prevention function rather than a regulatory compliance function, with the preventability of vendor-related patient harm making the case for proactive patient-centered strategies over reactive compliance approaches
- 88% of healthcare organizations experienced cyberattacks in the past year averaging 40 attacks per organization — the frequency of vendor-related threats makes compliance-cycle risk management structurally inadequate, as the interval between assessments routinely exceeds the interval between threats in today's healthcare threat environment
- The financial case aligns with the patient safety case — the $9.77 million average cost of a U.S. healthcare breach represents a financial consequence that both exceeds compliance penalty exposure and reflects real patient harm costs including care delays, longer hospital stays, and increased complications, making patient-safety-focused strategies financially as well as ethically superior
What does a patient-safety-focused vendor risk framework include that compliance programs do not?
- A detailed vendor inventory that maps each vendor's specific role in supporting patient care rather than simply cataloging vendors by data access type — this clinical lens ensures that the risk framework addresses operational dependencies that affect patient safety, not only data security risks that affect regulatory compliance
- Standardized assessments throughout the vendor lifecycle including pre-contract, periodic review, and offboarding evaluations — compliance programs that assess vendors only at onboarding miss the risk evolution that occurs during the vendor relationship and the data security obligations that continue through and after offboarding
- Strong BAAs with specific security requirements, breach notification protocols, and data-handling procedures for contract end terms — these provisions create the contractual accountability that compliance-focused BAAs often lack, ensuring vendors bear defined responsibility for security failures rather than leaving remediation obligations ambiguous until incidents test the agreements
- Continuous monitoring for high-risk vendors using HITRUST, SOC 2 Type 2, or ISO 27001 certifications that provide real-time compliance assurance rather than point-in-time assessment snapshots — annual reviews are no longer adequate for vendors whose security posture can change significantly between assessment cycles
- Regular testing of incident response and recovery plans through simulations of vendor-related failures ensures that clinical teams have practiced maintaining care continuity under disruption conditions rather than discovering procedural gaps for the first time during actual incidents that are affecting patient care
How should healthcare organizations measure the patient safety impact of vendor risk management?
- System downtime caused by vendor issues is the most direct patient safety metric — clinical system unavailability measured in minutes or hours quantifies the care delay impact of vendor failures in terms that connect directly to patient safety outcomes and are immediately meaningful to clinical and executive leadership
- Remediation time for security gaps identified after vendor assessments measures the program's effectiveness at converting vendor risk findings into actual risk reduction — the interval between identification and resolution is the window of patient safety exposure that fast remediation closes and slow remediation leaves open
- Financial consequences tied to downtime and remediation delays provide the executive reporting context that technical metrics cannot — hourly downtime cost calculations and remediation expense tracking translate vendor risk management effectiveness into the financial terms that justify program investment and resource allocation
- Fourth-party vendor risk exposure tracks the risk that originates in vendors' own supply chains and technology providers — a risk category that compliance programs focused on direct vendor relationships systematically miss but that the 800% downstream breach multiplier demonstrates is consequential
- Compliance scorecards tracking vendor adherence to HIPAA with 60% of organizations lacking confidence in their vendors' full compliance underscore why scorecards must measure actual compliance behavior rather than contractual representations — tracking vendor compliance performance over time reveals the gap between what vendors commit to and what they actually implement
How does Censinet RiskOps™ operationalize patient-safety-focused vendor risk management at scale?
- Vendor questionnaire completion in seconds rather than weeks addresses the speed-of-threat problem that manual assessment processes cannot solve — when vendor security posture can change between assessment cycles, the ability to conduct rapid assessments enables continuous risk visibility rather than periodic snapshots
- Censinet AI automatically summarizes vendor evidence, captures integration details, and identifies fourth-party risks — generating risk summary reports from all relevant assessment data while maintaining the human-in-the-loop approach that keeps experienced risk teams in control of the critical decisions that automation accelerates but cannot replace
- Advanced routing that functions like air traffic control ensures that important findings reach the right stakeholders including AI governance committee members — preventing the organizational coordination failures that allow critical vendor risk findings to sit unaddressed because no one with the authority to act was aware of them
- A centralized real-time dashboard provides the unified view of risks across all vendor relationships that fragmented manual processes cannot — replacing the incomplete picture that results from risk data scattered across IT, procurement, compliance, and clinical teams with a single authoritative source of vendor risk visibility
- Embedding vendor risk management into daily clinical operations rather than treating it as a separate compliance function is the organizational outcome that Censinet RiskOps™ enables — when vendor risk oversight is integrated into procurement workflows, clinical governance, and operational decision-making, patient safety protection becomes continuous rather than episodic


