How Penetration Testing Supports FDA Compliance
Post Summary
Penetration testing is key to ensuring medical devices meet FDA cybersecurity standards. With the rise of connected devices like insulin pumps and cardiac monitors, vulnerabilities pose risks to patient safety and data security. The FDA now mandates stricter cybersecurity measures for "cyber devices" under updated guidelines effective February 2, 2026.
Here’s why penetration testing matters:
- Identifies Risks: Simulates attack scenarios to expose flaws in hardware, software, and network connections.
- Protects Patients: Fixes security issues before they can impact device functionality or safety.
- Supports Compliance: Provides detailed reports required for FDA premarket and postmarket submissions.
To comply with FDA requirements, manufacturers must integrate cybersecurity into their design and post-launch processes. Penetration testing not only helps meet these requirements but also ensures devices remain secure throughout their lifecycle.
Medical Device Cybersecurity: FDA Compliance & Threat Protection | DeviceTalks West 2024
This session explores how manufacturers can address medical device security risks to maintain patient safety and regulatory compliance.
sbb-itb-535baee
FDA Cybersecurity Requirements for Medical Devices
FDA Two-Phase Cybersecurity Compliance Approach for Medical Devices
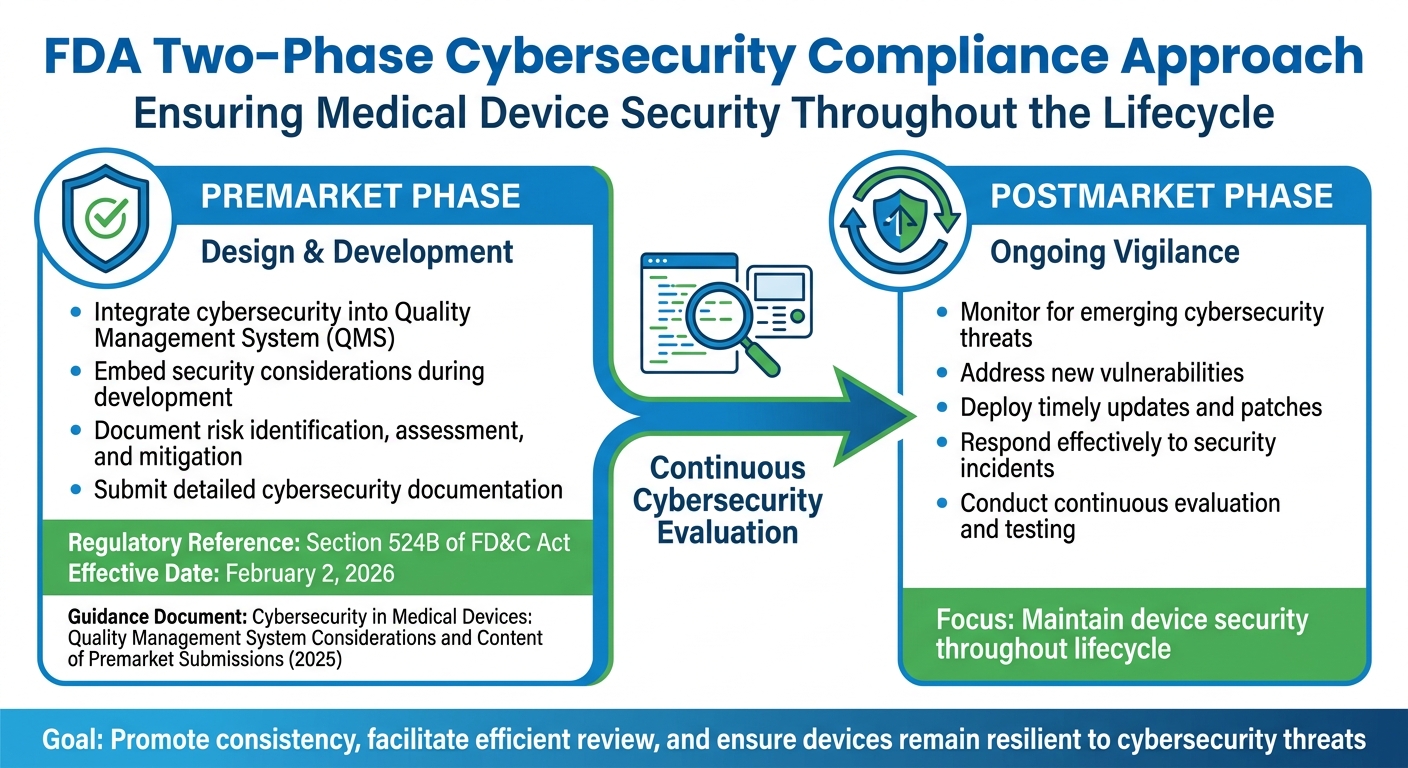
The FDA has established a two-phase approach - premarket and postmarket - to ensure medical devices remain secure and protect patient data. This is critical as cyberattacks increasingly threaten patient care through clinical application downtime.
Premarket Cybersecurity Requirements
Medical device manufacturers are required to integrate cybersecurity measures right from the design stage. According to Section 524B of the Food, Drug, and Cosmetic (FD&C) Act, manufacturers must embed cybersecurity considerations into their Quality Management System (QMS) during the development process. They must also include detailed documentation in their premarket submissions, outlining how risks are identified, assessed, and mitigated [3].
The FDA emphasizes that these guidelines aim to "promote consistency, facilitate efficient premarket review, and help ensure that marketed medical devices are sufficiently resilient to cybersecurity threats" [3]. The regulatory framework is detailed in the guidance document Cybersecurity in Medical Devices: Quality Management System Considerations and Content of Premarket Submissions, which replaced earlier versions in late 2025 [3]. Building strong cybersecurity into the design phase is essential for maintaining device security throughout its lifecycle.
Postmarket Cybersecurity Requirements
Even after meeting premarket standards, manufacturers must stay vigilant against new cybersecurity threats. Once a device is on the market, ongoing efforts are needed to monitor for emerging risks, address vulnerabilities, and respond effectively to incidents. This includes deploying timely updates and patches to safeguard both the device’s functionality and patient safety.
The FDA’s dual-phase approach highlights the importance of continuous evaluation, including penetration testing, to ensure that cybersecurity measures remain effective against evolving threats throughout a device’s lifecycle.
How Penetration Testing Supports FDA Compliance
Penetration testing plays a critical role in ensuring that medical devices meet the cybersecurity standards set by the FDA. Rather than relying on claims of security, it provides solid proof that security measures actually work when faced with realistic attack scenarios. This process helps uncover vulnerabilities, reduces risks to patients, and generates the necessary documentation for regulatory compliance.
Finding Security Vulnerabilities in Medical Devices
Penetration testing goes beyond automated scans by simulating real-world attacks across the entire device ecosystem. This includes hardware, firmware, mobile apps, APIs, and cloud interfaces. Unlike standalone component testing, this approach aligns with the FDA's expectation of addressing the full "cyber device" environment, which often requires effective third-party risk assessments. Through this method, testers can uncover weaknesses in areas like authentication systems, encryption protocols, and update integrity mechanisms - issues that might otherwise go unnoticed until they cause problems in clinical settings.
Reducing Risks to Patient Safety
By identifying vulnerabilities early, penetration testing helps manufacturers address security flaws before they can affect patient safety. For instance, if a vulnerability allows unauthorized access, manufacturers can fix the issue and confirm the effectiveness of their solution through retesting. This proactive approach minimizes the likelihood of technical weaknesses leading to harmful incidents in clinical environments, ultimately protecting patients.
Creating Documentation for Regulatory Submissions
Penetration testing also generates the detailed reports required for FDA evaluations. These reports not only confirm that vulnerabilities have been resolved but also provide transparency into the testing process. As StealthNet AI explains:
"The practical expectation: saying 'we did a pentest' isn't enough. You want a report that clearly shows what was tested, how it was tested, what was found, and what changed after remediation" [1].
Regulatory documentation should include the scope of testing, methodologies used, detailed findings with reproduction steps, and raw evidence like screenshots or logs. It should also document retest results to verify that vulnerabilities have been addressed, along with tester qualifications and justifications for any unresolved issues. This level of detail supports FDA premarket and postmarket requirements, including submissions under Section 524B of the FD&C Act.
Best Practices for FDA-Aligned Penetration Testing
To meet FDA expectations, penetration testing needs to be thorough, expertly executed, and seamlessly integrated into your risk management strategy. Below are key practices to ensure your testing aligns with FDA requirements and supports broader cybersecurity efforts.
Defining Scope and Identifying Assets
Start by mapping every component in your device's ecosystem that connects to a network or handles data. This includes hardware, firmware, mobile apps, cloud interfaces, and APIs. The FDA requires testing to cover the entire "cyber device" environment, not just select parts. Pay special attention to assets that process patient data or perform critical functions, as these will face heightened regulatory scrutiny. Clearly defining the scope ensures no gaps in coverage and aligns your testing with what regulators will examine during reviews.
Working with Third-Party Testing Experts
Choose testing partners with a strong background in medical device cybersecurity and experience navigating FDA pathways like 510(k), PMA, and De Novo. Teams led by former FDA reviewers can provide precise documentation that strengthens your regulatory submissions. As Medcrypt highlights:
"Getting your medical device through FDA approval requires more than just great technology - it demands cybersecurity expertise that regulators trust" [4].
Medcrypt, for example, has maintained a 100% FDA approval rate since 2023 for clients using their cybersecurity services. Their expertise can significantly reduce response times to FDA "Additional Information" requests, cutting them from 180 days to around 45–60 days [4]. Partnering with experts who handle the entire process - from testing to documentation and regulatory responses - can save time and avoid complications that arise with fragmented vendor solutions.
Using Testing Results in Risk Management Programs
FDA guidance now emphasizes the importance of directly linking penetration testing results to your risk management efforts. Integrate these findings into your Quality Management System (QMS) and Software Development Life Cycle (SDLC). Map identified vulnerabilities to your risk assessments and controls, ensuring a clear connection between testing data and mitigation strategies [5]. Pair routine vulnerability scans and Software Bill of Materials (SBOM) updates with continuous monitoring to support both premarket submissions and postmarket compliance. This approach helps demonstrate an ongoing commitment to cybersecurity throughout your device’s lifecycle.
How Censinet Helps Manage Cybersecurity Risks
Managing cybersecurity risks in healthcare, especially for medical devices, requires a streamlined approach. Censinet RiskOps™ steps in to simplify this process, providing healthcare organizations with a centralized platform tailored for cybersecurity and risk management. This tool helps ensure compliance with FDA requirements throughout a device's lifecycle while addressing the challenge of coordinating efforts across multiple teams.
Simplifying Third-Party Risk Assessments
Medical devices often rely on vendors and suppliers, which can introduce cybersecurity vulnerabilities. Censinet RiskOps™ tackles this issue by managing third-party risk by automating vendor evaluations and standardizing risk assessments with the help of templates and AI-powered insights. This reduces manual work by 70%, allowing healthcare organizations to complete assessments significantly faster. For example, organizations using the platform report 50-70% faster third-party risk assessments and a 40% boost in risk visibility. One healthcare provider assessed 200 IoT medical device vendors and flagged 15% as high-risk within just a few weeks.
Improving Team Collaboration and Governance
FDA compliance involves collaboration across IT, compliance, clinical staff, and quality management teams. Censinet RiskOps™ facilitates this with shared dashboards for real-time updates, role-based access controls aligned with RACI principles, and automated workflows for approvals. These tools ensure all teams stay on track with FDA guidelines, such as the 2023 cybersecurity guidance, while maintaining detailed audit trails for governance. Acting as a central hub, the platform routes critical findings and tasks to the appropriate stakeholders, ensuring that risk insights from testing are seamlessly integrated into compliance efforts.
Maintaining Ongoing Compliance
Meeting FDA postmarket requirements means continuously monitoring cybersecurity risks. Censinet RiskOps™ supports this by providing automated alerts and incorporating penetration testing results to keep risk profiles up to date. This ensures detailed reporting for FDA submissions and tracks key metrics like vulnerability remediation times and risk scores. With trend reporting and regulatory mapping to FDA's Quality System Regulation (21 CFR Part 820), the platform helps organizations stay ahead. Benchmarking data shows that 85% of users maintain compliance scores above industry averages, highlighting its effectiveness in supporting both premarket and postmarket requirements.
Conclusion
Rigorous penetration testing plays a key role in ensuring device security throughout its lifecycle. It’s not just about meeting FDA compliance - it’s about safeguarding patient safety, validating security measures, and simplifying regulatory submissions. As StealthNet AI puts it:
"FDA penetration testing isn't about checking a box - it's about producing credible, repeatable, evidence-rich validation that supports your medical device cybersecurity story and reduces surprises during FDA review" [1].
With the FDA’s updated requirements now in place, manufacturers face stricter compliance expectations. Inadequate documentation can lead to recalls or even legal complications [2]. Conducting detailed penetration testing before submitting to the FDA can help manufacturers avoid unexpected hurdles, which are often the reason for market entry delays.
Modern compliance demands go beyond isolated testing. It requires examining entire ecosystems - covering mobile apps, cloud APIs, and network integrations - to identify and address potential vulnerabilities [1].
To tackle these challenges, tools like Censinet RiskOps™ provide centralized risk management. By automating third-party vendor assessments and enabling continuous compliance monitoring, platforms like this help manufacturers stay ahead. Impressively, 85% of its users maintain compliance scores above industry averages. This demonstrates how integrated risk management not only supports FDA requirements but also enhances patient safety and improves care delivery.
FAQs
What does the FDA consider a “cyber device”?
The FDA describes a “cyber device” as any medical device that incorporates software, connects to the internet or other networks (like USB or Bluetooth), or relies on systems such as update servers. These devices come with cybersecurity risks that need to be addressed throughout their entire lifecycle.
When should we run penetration tests for FDA submissions?
Penetration tests play a crucial role in ensuring the security of medical devices. They should be conducted both premarket - to validate cybersecurity controls as part of FDA submissions - and postmarket, to continuously identify and address vulnerabilities throughout the device's lifecycle. This dual approach helps maintain compliance and, more importantly, safeguards patient safety.
What evidence should a pentest report include for the FDA?
A penetration testing report aimed at meeting FDA compliance needs to deliver a clear and comprehensive assessment of cybersecurity risks. It should include several critical components:
- Executive Summary: A high-level overview of the findings and their potential impact, tailored for stakeholders who may not have technical expertise.
- Detailed Vulnerability Findings: A breakdown of identified vulnerabilities, complete with technical details and their locations.
- Exploitability Analysis: An evaluation of how easily each vulnerability could be exploited, along with the potential consequences.
- Recommended Remediation Actions: Practical steps to address the vulnerabilities and strengthen the device’s security.
The report must be thorough and well-documented to align with FDA standards for medical device cybersecurity.


