Clinical Continuity Planning: Ensuring Patient Care During Vendor Disruptions
Post Summary
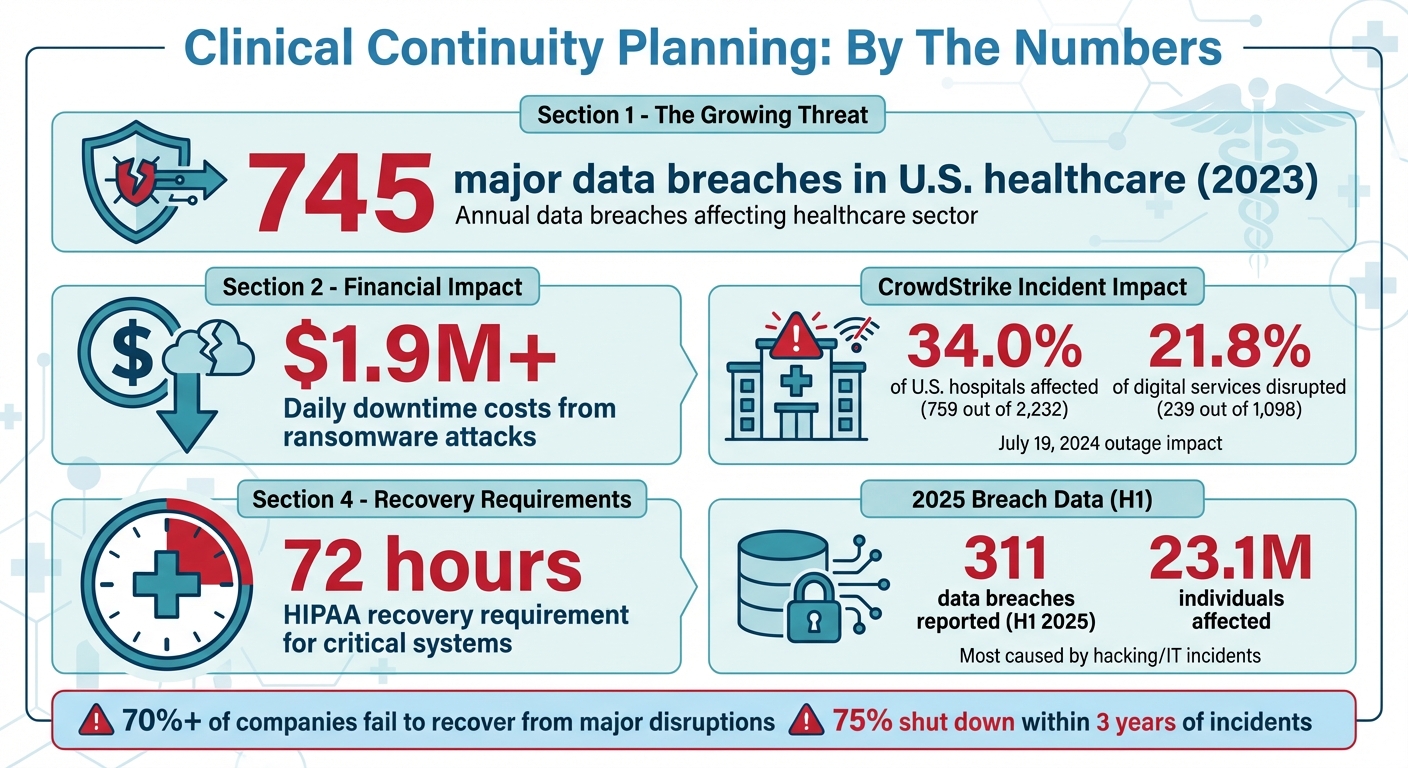
Without preparation, vendor disruptions can delay treatments, violate regulations like HIPAA, and harm both patient trust and organizational stability — as demonstrated by the 2024 CrowdStrike outage that disrupted 759 out of 2,232 U.S. hospitals, with 239 patient-facing systems affected including EHR access, imaging platforms, and fetal monitoring systems, and some services taking over 48 hours to recover.
Organizations should evaluate every vendor connected to their operations using frameworks like HITRUST and NIST SP 800-53, conduct vendor questionnaires covering security protocols, financial stability, and business continuity plans, perform on-site audits for critical vendors managing EHRs and medical devices, and rank vendors based on the clinical impact of potential downtime — assessing which functions would be disrupted, how patients would be affected, and how quickly backup systems could activate.
An effective clinical continuity plan combines a Business Impact Analysis to assess financial, patient satisfaction, legal, and reputational consequences of disruptions; recovery time objectives defining the maximum acceptable system downtime; proactive measures to maintain operations; reactive strategies to restore IT systems and data; and alignment with standards including ISO 22301:2019 and NIST SP 800-34.
Vendor incident response protocols require documented procedures for detecting, reporting, and resolving issues; defined shutdown criteria that trigger manual workflows when systems are compromised; vendor notification strategies compliant with BAAs that typically require 24-hour notification when contingency measures are activated; and communication tools supporting secure breach notifications, system lockdowns, audit logging, and backup channels aligned with HIPAA Security Rule and NIST Cybersecurity Framework guidance.
Testing requires quarterly tabletop exercises to identify weak spots in planned responses, annual full-scale simulations that stress-test production processes, networks, personnel, and facilities at 100% capacity, vendor disruption drills that simulate downtime and communication breakdowns, multi-layered failure scenarios combining EHR outages with simultaneous imaging or laboratory system disruptions, and post-exercise reports documenting outcomes and action points for improvement.
Censinet RiskOps™ centralizes vendor risk assessments, Business Impact Analyses, and incident response plans in a unified platform; automates workflows that track recovery time objectives and compliance with continuity requirements; provides a real-time command center identifying which vendors support key clinical functions; keeps vendor contact details, escalation procedures, and recovery plans instantly accessible during disruptions; and uses Censinet AI™ to automatically summarize vendor documentation and identify fourth-party risks that could affect continuity strategies.
Healthcare providers depend on third-party systems like electronic health records (EHRs) and scheduling tools to deliver care. But when these systems fail - due to cyberattacks, outages, or technical issues - patient safety, clinical workflows, and operations are at risk. To counter this, clinical continuity planning is critical. It helps maintain patient care during disruptions by identifying key risks, setting up backup procedures, and ensuring quick recovery.
Key Points:
Why It Matters: Without preparation, vendor disruptions can delay treatments, violate regulations like HIPAA, and harm both patient trust and organizational stability. A strong continuity plan isn’t optional - it’s a necessity.
Healthcare Vendor Disruption Statistics and Impact Data 2023-2025
Identifying and Assessing Vendor Risks
To safeguard patient care from potential vendor disruptions, the first step is identifying your system's weak points. This requires a detailed evaluation of every vendor connected to your operations, data, or systems. According to BARR Advisory, vendor risk management often lacks sufficient processes to ensure data security [4]. Using structured frameworks and practical tools can help address these vulnerabilities effectively. Below are actionable steps to assess and minimize these risks.
How to Conduct Vendor Risk Assessments
Choosing the right assessment framework is key. For healthcare organizations, standards like HITRUST, along with broader frameworks such as NIST SP 800-53, PCI, SOC 1, and SOC 2, offer reliable methods to evaluate vendor security and compliance [4]. These frameworks allow you to systematically review vendor practices, including their data protection measures, operational stability, and security controls.
Vendor questionnaires are an essential tool for gathering insights into areas like internal controls, cybersecurity protocols, compliance status, financial stability, data encryption methods, incident response strategies, and business continuity plans [7]. For vendors deemed critical or high-risk - such as those managing electronic health records, medical devices, or patient scheduling systems - on-site audits provide deeper insights. These audits can uncover weaknesses in disaster recovery plans and other areas that may not be fully evident in written documentation [7].
The HHS Assistant Secretary for Technology Policy offers a Security Risk Assessment Tool that healthcare providers can adapt for evaluating vendors [5]. While NIST standards aren't mandatory for HIPAA compliance, they serve as a robust foundation for spotting vulnerabilities. Keep in mind that vendor risks are not static - they evolve as new threats arise and systems change. Continuous monitoring is therefore vital to stay ahead of potential risks and maintain compliance [4].
Ranking Risks by Impact on Patient Care
After completing assessments, it’s crucial to rank vendors based on their impact on clinical operations. Not all vendors carry the same level of risk to patient care. For example, a vendor managing your emergency department's electronic health records system poses a much higher risk than one handling non-urgent administrative scheduling. This categorization helps focus attention and resources where disruptions would most directly affect patient safety and treatment.
Align your vendor risk management strategy with broader organizational goals, such as patient safety, quality assurance, regulatory compliance, and enterprise risk management [6]. Pay particular attention to vendors involved in IT risk management, third-party risks, compliance, and AI governance [6]. For each vendor, consider the potential consequences of system downtime - whether it lasts an hour, a day, or a week. Assess which clinical functions would be disrupted, how patients would be affected, and how quickly backup systems could take over. These evaluations guide investments in redundancy, alternative workflows, and better monitoring systems. A thorough risk assessment ensures that your continuity plans are tailored to address the most critical threats to patient care.
Building a Clinical Continuity Plan
After identifying and prioritizing vendor risks, the next critical step is crafting a clinical continuity plan. This plan ensures that your organization can maintain essential operations and patient care, even during disruptions. Essentially, it’s a roadmap to minimize downtime, protect your reputation, and - most importantly - keep patients and staff safe during crises [8][1].
Start by using your risk assessments to pinpoint the clinical services that must stay operational no matter what. Conduct a Business Impact Analysis (BIA) to gauge potential financial losses, patient satisfaction issues, legal risks, and damage to your organization’s reputation. From there, establish recovery time objectives (RTOs) - the maximum acceptable time a system or service can be offline without causing severe harm [8][1][9].
An effective continuity plan combines both proactive measures to maintain operations and reactive strategies to recover after disruptions. Business continuity ensures essential functions keep running, while disaster recovery focuses on restoring IT systems and data. Together, they create a safety net for uninterrupted patient care. Industry standards like ISO 22301:2019 and frameworks such as NIST SP 800-34 provide helpful guidelines for structuring your plan [8].
What to Include in Your Continuity Plan
For a continuity plan to work effectively, it needs to cover several key areas:
Using Technology to Support Continuity Planning
Technology can simplify and strengthen your continuity planning efforts, especially as vendor networks grow and risks evolve. Managing these complexities manually can quickly become overwhelming, but technology platforms can centralize information, automate workflows, and improve the speed and accuracy of responses.
Censinet RiskOps™ is one such platform designed to centralize vendor risk assessments, BIAs, and incident response plans [8]. Its automated workflows help track recovery time objectives, monitor compliance with continuity requirements, and assign tasks to the right team members. Think of it as a control tower, ensuring critical issues are routed to the appropriate stakeholders without delay.
The platform also provides a real-time command center, offering visibility into vendor risks and continuity statuses. Risk teams can quickly identify which vendors support key clinical functions, assess the potential impact of disruptions, and prioritize recovery efforts based on patient care needs. Additionally, Censinet AITM™ enhances planning by automatically summarizing vendor documentation, capturing integration details, and identifying fourth-party risks that could affect your strategies.
When disruptions occur, having instant access to continuity information can make all the difference. Censinet RiskOps™ keeps vendor contact details, escalation procedures, and recovery plans readily available, enabling response teams to act quickly. Its collaborative tools allow real-time coordination between internal teams, vendors, and external partners, reducing response times and ensuring the plan is executed effectively - when every second matters.
Responding to and Recovering from Vendor Incidents
When vendor disruptions strike, having a solid continuity plan is just the beginning. A quick and well-coordinated response is what truly determines whether patient care proceeds smoothly or grinds to a halt. Take the CrowdStrike outage on July 19, 2024, as an example. This incident, caused by a faulty software update, disrupted Windows systems globally. In the U.S. healthcare sector alone, 759 out of 2,232 hospitals (34.0%) faced service interruptions. Of the 1,098 digital services affected, 239 (21.8%) were patient-facing systems, including critical tools like EHR access, imaging platforms, and fetal monitoring systems. While most services were restored within hours, some took over 48 hours to recover [10].
Acting immediately is non-negotiable. As soon as systems fail, activate downtime procedures and assess which patient care systems are impacted. Recovery efforts should align with your pre-established recovery time objectives (RTOs), while keeping HIPAA’s 72-hour recovery requirement for critical health systems in mind [10][12]. Your response plan should focus on identifying the root cause, preventing further risks, and restoring operations as quickly as possible [15]. This highlights the importance of having strong, well-defined incident response protocols in place.
Creating Incident Response Protocols
Strong incident response protocols hinge on clear documentation and tested procedures for detecting, reporting, and resolving issues. One key element is defining shutdown criteria to trigger manual workflows in case systems are compromised. For vendor-specific incidents, your notification strategy must comply with business associate agreements, which typically require vendors to notify you within 24 hours of activating contingency measures [12].
When designing these protocols, use frameworks like the HIPAA Security Rule and NIST Cybersecurity Framework as guides. Resources such as the HHS Cyber Security Checklist and Ransomware Guidance offer practical steps to structure your response [16]. To enhance your readiness, integrate incident response capabilities into your communication tools. These should support secure breach notifications, system lockdowns, audit logging, and backup channels [12]. With third-party involvement in data breaches nearly doubling, it’s crucial to set clear expectations for vendor incident responses and establish dedicated workflows for supply chain disruptions [13].
Working with External Partners During Incidents
Recovery is rarely a solo effort. Transparent, two-way communication between healthcare providers, manufacturers, and distributors is essential for documenting, monitoring, and forecasting product needs during disruptions. Aligning external communication with your continuity procedures strengthens your overall resilience.
"It is critical to forge new relationships with onshore and near-shore suppliers or invest in dependable companies that can fill their needs during peak surges."
This advice from the American Hospital Association underscores the importance of diversifying your supply chain and leveraging community resources, such as healthcare coalitions and regional partners, to support recovery efforts [14].
When working with affected vendors, rely on data-driven approaches to avoid overreacting to supply chain disruptions [11]. If necessary, collaborate with external cybersecurity experts to bolster your incident response capabilities [15]. During the recovery phase, document lessons learned and refine your protocols based on how they performed in practice. In the first half of 2025, U.S. healthcare organizations reported 311 data breaches affecting approximately 23.1 million individuals, with most caused by hacking and IT-related incidents. This underscores the ongoing need to improve incident response strategies [12]. By combining internal efforts with external partnerships, you can create a cohesive and effective recovery plan.
sbb-itb-535baee
Testing and Updating Your Continuity Plans
A continuity plan is only as good as its testing. Without regular evaluation, it’s just a document gathering dust. Consider this: more than 70% of companies fail to recover from major disruptions, and 75% shut down within three years of such incidents [19]. These numbers underscore why testing your continuity plan is absolutely critical.
To start, schedule quarterly tabletop exercises. These discussion-based reviews help you examine potential scenarios and identify weak spots in your plan [18][19]. However, keep in mind that while these exercises are useful, they often lack the depth to uncover all vulnerabilities, especially if the focus is limited to IT systems.
For a more thorough evaluation, conduct annual full-scale simulations. These stress tests go beyond discussions, putting your production processes, networks, personnel, and facilities to the test [18]. Make sure your disaster recovery systems are designed to handle 100% capacity, not just partial loads, since real-world demands often exceed expectations [18].
Running Vendor Disruption Drills
Vendor disruptions can have ripple effects on your operations, so it’s essential to test how your organization handles these situations. Run drills that simulate downtime, vendor communication breakdowns, and their impact on critical services like patient care. Align these exercises with your overall business continuity goals, starting with a gap analysis to define the drill's purpose [19].
Don’t stop at testing a single failure point. For example, simulate a scenario where your EHR system goes down while access to imaging platforms or laboratory systems is also interrupted. This multi-layered approach ensures your team is prepared for complex challenges. Verify that all communication channels, including backup tools for breach notifications and system lockdowns, are functioning before starting the drill [19].
Budgeting is another key element. Allocate sufficient resources, define the roles of participants, and provide any necessary training to ensure the drill runs smoothly [19]. Afterward, document everything in post-exercise reports. These reports should include outcomes, recommendations, and specific action points for improvement [19][2]. Regularly engaging your recovery team in these simulations helps identify gaps and improve your overall readiness [20]. Use the results to update your continuity plan and strengthen weak areas.
Learning from Incidents to Improve Plans
Every disruption is an opportunity to refine your continuity plan. Review and update your plan annually - or sooner if significant operational, technological, or facility changes occur, or after learning key lessons from an incident [2][17][19]. This ongoing process ensures your plan stays effective and ready for future challenges [3].
When analyzing incidents, focus on four critical areas: people, processes, premises, and providers [3]. Use these insights to revise training programs, improve communication strategies, and update your Business Impact Analysis [3]. Evaluate vendor performance during disruptions, and if necessary, diversify your supplier base or renegotiate contracts with critical vendors [3].
Take concrete steps to address vulnerabilities. Update supporting documentation, including contact lists, critical functions, supplies, vendors, equipment, and alternate site details. Regular practice runs are essential - they reveal weaknesses and give you the chance to make quick adjustments, ultimately strengthening your organization’s resilience [20].
The feedback from these tests plays a vital role in refining your strategies. By continuously evolving your continuity plans to address emerging risks and challenges, you’ll be better prepared for whatever comes next [20].
Conclusion
Vendor disruptions are bound to happen, but with proper preparation, healthcare organizations can avoid severe consequences that jeopardize patient care. The difference between a minor inconvenience and a full-blown crisis often comes down to how well-prepared an organization is. By focusing on detailed risk assessments, strong continuity plans, and consistent testing, healthcare providers can ensure critical operations remain intact during disruptions. These efforts build on existing strategies, creating a seamless safety net for patient care.
Prolonged downtime puts both revenue and patient safety at risk, making swift recovery a top priority. In healthcare, the stakes are exceptionally high since disruptions impact not only business operations but also the ability to provide safe and timely care. This is why continuity planning should be seen as a continuous commitment, not a one-and-done task.
Leveraging technology like Censinet RiskOps™ can simplify vendor risk assessments and automate key workflows, ensuring uninterrupted oversight of essential operations. These tools, combined with proactive planning, help shield your organization from vendor-related challenges.
Key Takeaways
FAQs
What are the essential steps for healthcare providers to assess vendor risks effectively?
To carry out a thorough vendor risk assessment, begin by sorting your vendors into categories based on the level of risk they pose. Carefully examine their security and compliance documentation to confirm they align with your required standards. From there, create action plans to manage any risks you uncover, and set up continuous monitoring to catch potential problems early. Additionally, make sure you have a well-defined incident response plan in place and establish clear steps for vendor offboarding when the relationship ends.
How can healthcare organizations maintain clear communication during vendor disruptions?
Healthcare organizations can navigate vendor disruptions more effectively by adopting a few practical strategies. Conducting regular performance reviews helps pinpoint potential problems before they escalate. Leveraging digital communication tools promotes open and transparent dialogue, ensuring all parties stay on the same page. To address changes swiftly, real-time alerts can be used to notify vendors immediately about disruptions. Moreover, incorporating vendors into incident response plans creates a unified and streamlined approach to tackling challenges as they arise.
How does technology help maintain patient care during disruptions?
Technology is essential for keeping patient care on track during unexpected disruptions like cyberattacks or system outages. It ensures rapid response mechanisms, reliable data backup and recovery, and smooth communication across healthcare teams.
Some of the most important tools include well-structured incident response plans, tiered recovery systems to prioritize critical applications, and strong digital security protocols. These solutions work together to safeguard patient information, keep operations running, and support clinical workflows even in tough situations.
Related Blog Posts
- Top 7 Cloud Disaster Recovery Tools for Healthcare
- Clinical Continuity Planning: Ensuring Patient Care During Vendor Disruptions
- Patient Care Can't Wait for Cloud Recovery: Healthcare's Business Continuity Crisis Exposed
- The AWS Outage Exposed Cloud Vulnerabilities - What It Means for Healthcare Business Continuity
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":[{"@type":"Question","name":"What are the essential steps for healthcare providers to assess vendor risks effectively?","acceptedAnswer":{"@type":"Answer","text":"<p>To carry out a thorough <a href=\"https://censinet.com/vendor-solutions\">vendor risk assessment</a>, begin by sorting your vendors into categories based on the level of risk they pose. Carefully examine their <strong>security and compliance documentation</strong> to confirm they align with your required standards. From there, create action plans to manage any risks you uncover, and set up <strong>continuous monitoring</strong> to catch potential problems early. Additionally, make sure you have a well-defined <strong>incident response plan</strong> in place and establish clear steps for vendor offboarding when the relationship ends.</p>"}},{"@type":"Question","name":"How can healthcare organizations maintain clear communication during vendor disruptions?","acceptedAnswer":{"@type":"Answer","text":"<p>Healthcare organizations can navigate vendor disruptions more effectively by adopting a few practical strategies. Conducting <strong>regular performance reviews</strong> helps pinpoint potential problems before they escalate. Leveraging <strong>digital communication tools</strong> promotes open and transparent dialogue, ensuring all parties stay on the same page. To address changes swiftly, <strong>real-time alerts</strong> can be used to notify vendors immediately about disruptions. Moreover, incorporating vendors into <strong>incident response plans</strong> creates a unified and streamlined approach to tackling challenges as they arise.</p>"}},{"@type":"Question","name":"How does technology help maintain patient care during disruptions?","acceptedAnswer":{"@type":"Answer","text":"<p>Technology is essential for keeping patient care on track during unexpected disruptions like cyberattacks or system outages. It ensures <strong>rapid response mechanisms</strong>, reliable data backup and recovery, and smooth communication across healthcare teams.</p> <p>Some of the most important tools include well-structured <strong>incident response plans</strong>, <strong>tiered recovery systems</strong> to prioritize critical applications, and strong <strong>digital security protocols</strong>. These solutions work together to safeguard patient information, keep operations running, and support clinical workflows even in tough situations.</p>"}}]}
Key Points:
Why is clinical continuity planning a patient safety imperative rather than an operational preference?
- Vendor disruptions are bound to happen — the question is not whether critical vendor systems will fail but whether the organization has prepared to maintain patient care when they do, and the difference between a minor inconvenience and a full-blown crisis depends entirely on preparation quality
- The 2024 CrowdStrike outage demonstrated the scale of vendor disruption risk at a single incident — a faulty software update disrupted Windows systems globally, with 759 of 2,232 U.S. hospitals facing service interruptions, 239 patient-facing systems affected including EHR access, imaging platforms, and fetal monitoring systems, and some services taking over 48 hours to recover
- HIPAA's 72-hour recovery requirement for critical health systems establishes a regulatory baseline for recovery time objectives — organizations without pre-planned recovery procedures cannot reliably meet this requirement under the operational stress of an active vendor disruption, making continuity planning a compliance obligation as well as a patient safety necessity
- Prolonged downtime puts both revenue and patient safety at risk simultaneously — healthcare disruptions affect not only business operations but also the ability to provide safe and timely care, with the financial and clinical consequences compounding in ways that well-prepared organizations consistently manage more effectively than unprepared ones
- More than 70% of companies fail to recover from major disruptions and 75% shut down within three years of such incidents — these statistics apply across industries, and in healthcare the patient safety consequences of recovery failure make this organizational survival data a patient safety metric as much as a business continuity one
How should healthcare organizations conduct vendor risk assessments specifically for continuity planning?
- Framework selection must match the organization's regulatory and operational priorities — HITRUST provides healthcare-specific rigor, NIST SP 800-53 offers a broader federal standard baseline, and SOC 1 and SOC 2 provide financial and security control attestations that together create a comprehensive vendor security evaluation foundation
- Vendor questionnaires must cover internal controls, cybersecurity protocols, compliance status, financial stability, data encryption methods, incident response strategies, and business continuity plans — the breadth of this information requirement reflects the operational dependency that continuity planning must account for, extending well beyond the security-focused assessments that compliance programs typically conduct
- On-site audits for critical vendors managing EHRs, medical devices, and patient scheduling systems provide deeper insights than written documentation can — uncovering weaknesses in disaster recovery plans and other areas that vendor questionnaires may not fully surface, and providing the ground-truth verification that life-critical vendor dependencies require
- Vendor risks are not static and continuous monitoring is therefore vital — new threats arise, systems change, and vendor operational stability evolves in ways that point-in-time assessments cannot track, making continuous monitoring the operational standard for vendors whose disruption would directly affect patient care
- Risk ranking by clinical impact of potential downtime distinguishes the vendor whose failure disrupts emergency department EHR access from the vendor whose failure disrupts non-urgent administrative scheduling — focusing assessment depth and monitoring intensity on the vendors whose disruption most directly threatens patient safety
What does a complete clinical continuity plan require and how is it structured?
- A Business Impact Analysis is the planning foundation — assessing potential financial losses, patient satisfaction consequences, legal risks, and reputational damage enables the organization to understand the full scope of disruption consequences and prioritize recovery investments accordingly
- Recovery time objectives define the operational boundaries of the continuity plan — establishing the maximum acceptable time a system or service can be offline without causing severe harm creates the measurable targets that recovery planning, testing, and vendor SLA negotiations must satisfy
- Business continuity and disaster recovery serve distinct but complementary functions — business continuity ensures essential functions keep running during disruptions, while disaster recovery focuses on restoring IT systems and data after disruptions, with both required to create the complete safety net for uninterrupted patient care
- ISO 22301:2019 and NIST SP 800-34 provide the structural frameworks for planning that align with international standards and federal guidance — using established frameworks ensures that the continuity plan is defensible to regulators, credible to insurers, and systematically comprehensive rather than ad hoc
- The plan must explicitly address vendor-specific scenarios including which clinical services must stay operational regardless of vendor disruption, which backup procedures activate when specific vendor systems become unavailable, and how quickly each backup procedure can be operational — with the gap between vendor failure and backup activation representing the highest-risk window for patient safety
What incident response protocols address vendor-specific disruption scenarios?
- Defined shutdown criteria that trigger manual workflows when systems are compromised prevent the operational paralysis that occurs when clinical teams face vendor system failures without pre-established procedures — knowing in advance exactly when to activate manual workflows and what those workflows are enables clinical staff to maintain care continuity without waiting for guidance from incident commanders who may themselves be managing the response
- Vendor notification strategies compliant with BAAs that typically require 24-hour notification of contingency measure activation create the contractual information flow that enables coordinated response — organizations whose BAAs do not include vendor notification requirements consistently face delayed information during incidents that extends the disruption impact beyond what prompt vendor communication would produce
- HIPAA Security Rule and NIST Cybersecurity Framework provide the structural guidance for incident response protocol design — using these frameworks ensures that protocols address the regulatory obligations that activate during vendor incidents as well as the technical and operational response steps
- Communication tools supporting secure breach notifications, system lockdowns, audit logging, and backup channels must be verified as operational before drills begin — discovering during an actual incident that communication backup systems are non-functional compounds the disruption rather than containing it
- Third-party involvement in data breaches has nearly doubled — setting clear expectations for vendor incident responses and establishing dedicated workflows for supply chain disruptions addresses the increasing frequency of vendor-originating incidents that require coordinated rather than unilateral organizational response
How should healthcare organizations conduct vendor disruption drills and use results to improve continuity plans?
- Quarterly tabletop exercises identify weak spots in planned responses' through discussion-based review of potential scenarios — these exercises are valuable for surfacing procedural gaps and communication breakdowns without the operational disruption of full simulations, though their depth is limited when focused only on IT systems
- Annual full-scale simulations stress-test production processes, networks, personnel, and facilities at 100% capacity — real-world demands often exceed the partial-load scenarios that tabletop exercises explore, and recovery systems that function at 50% capacity will fail at the actual volumes that vendor disruptions generate during peak clinical operations
- Multi-layered failure scenarios combining simultaneous disruptions — EHR system failure concurrent with imaging platform or laboratory system interruption — prepare clinical teams for the compound failures that actual incidents frequently present rather than the single-system failures that simpler drills address
- Post-exercise reports documenting outcomes, recommendations, and specific action points convert drill experience into institutional learning — without structured documentation, the insights gained through simulation are absorbed by individuals rather than embedded in updated procedures, meaning the next drill or incident starts from the same baseline rather than building on previous learning
- Annual plan reviews triggered by significant operational, technological, or facility changes or following key incident lessons ensure the continuity plan remains current — the four critical analysis areas of people, processes, premises, and providers provide the structural framework for post-incident review that produces systematic improvement rather than symptom-specific fixes
How does Censinet RiskOps™ function as the operational backbone of clinical continuity planning?
- Centralizing vendor risk assessments, Business Impact Analyses, and incident response plans in a unified platform eliminates the fragmented documentation that slows response during actual incidents — having all continuity information in one accessible system means response teams are not searching for procedures across multiple systems while patient care is simultaneously at risk
- Automated workflows that track recovery time objectives and compliance with continuity requirements convert the continuity plan from a document into an operational system — automatically assigning tasks, monitoring completion against RTO targets, and escalating overdue items ensures that continuity plan execution is tracked in real time rather than verified after the fact
- A real-time command center identifying which vendors support key clinical functions provides the situational awareness that incident commanders need to make rapid prioritization decisions during disruptions — knowing immediately which vendor failures are affecting which clinical capabilities enables focused response rather than undifferentiated crisis management
- Instant access to vendor contact details, escalation procedures, and recovery plans during disruptions eliminates the information retrieval delays that compound response time — when every second matters, having recovery procedures immediately accessible rather than requiring manual document retrieval measurably improves response effectiveness
- Collaborative tools enabling real-time coordination between internal teams, vendors, and external partners reduce response times by enabling simultaneous rather than sequential communication — the multi-party coordination that effective vendor disruption response requires cannot be achieved through email and phone trees during active incidents, making real-time collaborative platforms a clinical continuity necessity rather than a convenience


