HIPAA Encryption vs. Other Standards for Clinical Apps
Post Summary
Addressable under HIPAA means that organizations must evaluate whether encryption is feasible and appropriate for their environment, implement it if reasonable, or document a defensible alternative rationale — it does not mean optional and failure to implement or document can result in enforcement action.
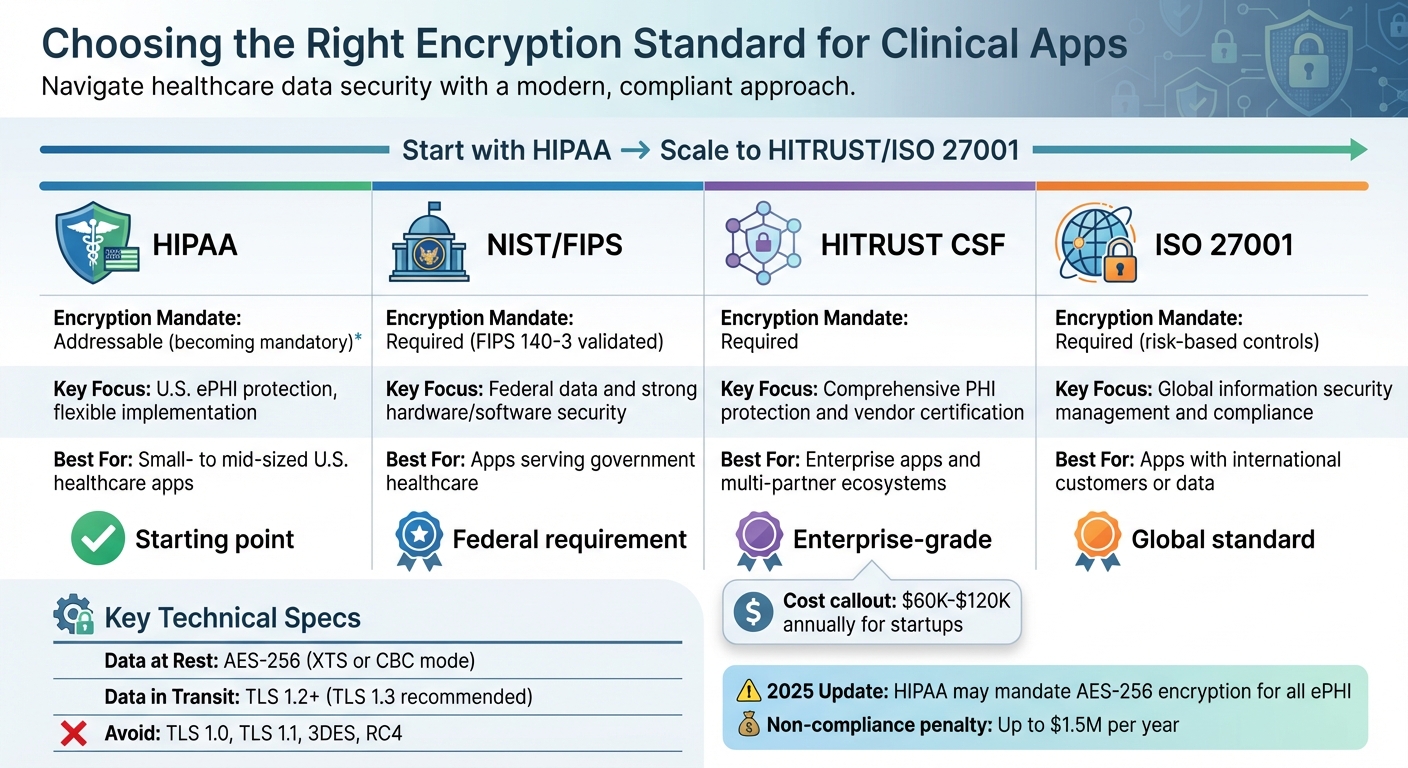
HIPAA relies on NIST to define encryption standards and recommends AES-256 for data at rest using NIST SP 800-111 and TLS 1.2 or higher for data in transit using NIST SP 800-52, while deprecated protocols including TLS 1.0, TLS 1.1, 3DES, and RC4 should be disabled.
When ePHI is encrypted using NIST-approved methods and the encryption keys remain secure, a covered entity may be exempt from breach notification requirements under 45 CFR 164.402 even if the encrypted data is lost or stolen, because the data is rendered unusable to unauthorized parties.
HITRUST CSF combines HIPAA, NIST, ISO 27001, and other standards into a single prescriptive risk-based framework that includes specific required encryption controls across 19 control categories, making it more demanding than HIPAA alone while providing a single certifiable path to multi-standard compliance.
ISO 27001 is appropriate when a clinical app operates in international markets, processes data beyond US ePHI such as credit card information or data from non-US patients, or needs a globally recognized information security management certification that HIPAA compliance alone cannot provide.
HIPAA violations can result in fines of up to $1.5 million per year per violation category, and enforcement cases such as the University of Rochester Medical Center's $3 million penalty and Children's Medical Center of Dallas's $3.2 million penalty demonstrate that unencrypted device losses are among the most consistently penalized compliance failures.
HIPAA encryption rules are evolving, and understanding them is crucial for clinical app and medical device developers. Here's what you need to know:
Quick takeaway: Start with HIPAA compliance for U.S. apps handling ePHI. For global or multi-partner apps, consider HITRUST or ISO 27001 for added security and flexibility.
HIPAA Encryption Requirements Explained
HIPAA Security Rule and Encryption
The HIPAA Security Rule takes a somewhat flexible stance on encryption. According to 45 CFR 164.312, encryption is classified as "addressable" for ensuring access control and securing data during transmission. This means healthcare organizations and clinical app developers need to assess whether encryption is feasible or document a solid alternative. Tools like Censinet Connect™ Copilot can help automate these assessments using standardized questionnaires. The process for making these decisions is outlined under 45 CFR 164.306(d).
Kevin Henry, a HIPAA Specialist at AccountableHQ, explains: "Addressable does not mean optional; it requires you to evaluate feasibility and risk, implement encryption when reasonable and appropriate, or implement an equivalent alternative and document a defensible rationale."
One of the biggest reasons to implement encryption is the breach notification safe harbor. When ePHI (electronic protected health information) is encrypted using NIST-approved methods, it becomes unusable to unauthorized users. Under 45 CFR 164.402, if encrypted data is lost or stolen but the encryption keys remain secure, the entity may be exempt from breach notification requirements. This applies to ePHI both at rest (stored on devices, servers, or databases) and in transit (transmitted via email, APIs, or networks). These guidelines lay the groundwork for understanding the technical details discussed in the next section.
Technical Specifications
HIPAA relies on NIST to define encryption standards, recommending AES-256 for data at rest and TLS 1.2 or higher for data in transit. For data at rest, AES-256 (using XTS or CBC mode) is outlined in NIST SP 800-111 and is applicable to full-disk encryption on devices like laptops and mobile phones, as well as Transparent Data Encryption (TDE) for databases. For data in transit, NIST SP 800-52 provides the framework, emphasizing that outdated protocols like TLS 1.0, TLS 1.1, and weak ciphers such as 3DES and RC4 should be disabled.
The regulatory environment is evolving. Starting in early 2025, the Department of Health and Human Services (HHS) proposed a significant update to the Security Rule, aiming to make encryption a mandatory requirement for all ePHI at rest and in transit. The comment period for this proposal ended on March 7, 2025. If finalized, organizations will likely have a 180-day window to comply. This shift highlights an effort to make encryption a standard practice rather than a situational choice.
Organizations are also moving toward newer encryption standards, like transitioning from FIPS 140-2 to FIPS 140-3 validated cryptographic modules for handling ePHI. Additionally, there’s growing attention to post-quantum encryption readiness, with developers monitoring NIST’s post-quantum standards and experimenting with hybrid key exchanges to prepare for potential future threats.
Application to Clinical Apps
In clinical applications, encryption needs to be integrated at every level, from data storage to patient-facing interfaces. For platforms like electronic health records (EHRs), telehealth services, and imaging systems, developers should implement "default-on" encryption for object storage and block volumes, ensuring that snapshots and replicas automatically inherit these protections. Telehealth video streams can benefit from using TLS 1.3 with forward secrecy across web portals, APIs, and other patient-facing systems.
Mobile clinical apps require strict Mobile Device Management (MDM) policies. These policies should block local backups of ePHI and enable remote-wipe capabilities. Additionally, service-to-service communication within clinical systems should use mutual TLS (mTLS) to provide both enhanced encryption and authentication.
The risks of non-compliance are significant. For example, in 2019, the University of Rochester Medical Center faced a $3 million fine after losing a single unencrypted flash drive and laptop. Similarly, Children's Medical Center of Dallas paid a $3.2 million penalty in 2017 following the theft of an unencrypted Blackberry and laptop. These cases highlight why encryption is increasingly seen as a critical practice, even when regulations currently classify it as "addressable."
sbb-itb-535baee
HIPAA Encryption vs. Other Standards
HIPAA vs. NIST Standards
HIPAA and NIST serve different purposes. HIPAA is a legal requirement enforced by the Office for Civil Rights (OCR), while NIST provides detailed technical guidelines. Although HIPAA references NIST, it doesn’t mandate its use directly.
The key distinction lies in their approach: HIPAA offers broad directives, like "implement a mechanism" to secure electronic Protected Health Information (ePHI), leaving room for interpretation. NIST, on the other hand, provides specific technical protocols, such as AES-256 for data at rest, TLS 1.3 for data in transit, and SHA-256 for hashing. HIPAA focuses solely on PHI, while NIST applies to all federal and sensitive data environments [4].
A 2021 amendment to the HITECH Act introduced an incentive for using NIST standards. If a covered entity demonstrates 12 months of compliance with a recognized security framework like NIST, the OCR may reduce enforcement actions [3]. This makes NIST an attractive option for clinical app developers who want clear technical guidance while meeting HIPAA requirements.
Feature
HIPAA Encryption Requirements
NIST Standards (SP 800-66/111/52)
Legal/Regulatory Requirement
Technical Framework/Guideline
High ("Addressable" specifications)
Low (Specific technical protocols)
Vague ("Implement a mechanism")
Precise (AES-256, TLS 1.3, SHA-256)
OCR (Fines and Corrective Action Plans)
Voluntary (unless mandated by law/contract)
Patient Privacy and Data Confidentiality
Information Security and System Integrity
Must be rendered "unusable" to unauthorized users
Recommends full disk encryption or equivalent
Applied "whenever deemed appropriate"
Mandates TLS 1.3 or IPSec VPNs
Margaret Hales, J.D., CEO of ET&C Group LLC, notes, "These days, encrypting PHI in transit and at rest is essential for any healthcare organization"
.
NIST SP 800-57 also provides comprehensive guidelines for encryption key management, covering everything from creation to destruction. This ensures that encryption keys are as secure as the data they protect [5].
HIPAA vs. HITRUST CSF
HITRUST CSF goes beyond NIST by combining HIPAA and NIST controls into a unified, risk-based framework. While HIPAA establishes baseline requirements and NIST offers detailed technical guidelines, HITRUST provides a prescriptive set of controls tailored to healthcare enterprise risks. For clinical app developers, HITRUST certification demonstrates compliance with HIPAA while also aligning with NIST, ISO 27001, and other standards.
HIPAA vs. ISO 27001
For clinical apps operating globally, ISO 27001 offers added value. Unlike HIPAA, which is specific to U.S. healthcare, ISO 27001 is an international standard for information security management. It takes a broader approach through an Information Security Management System (ISMS) that covers all types of data, not just PHI.
ISO 27001’s cryptographic controls, outlined in Annex A 10.1, require organizations to establish clear policies for using encryption. It emphasizes risk assessment and management processes rather than prescribing specific technical measures. Certification involves third-party audits by accredited bodies and detailed key management processes, including policies for key generation, storage, retrieval, and destruction.
For clinical app developers targeting international markets, ISO 27001 certification can provide a competitive edge and access to opportunities that HIPAA compliance alone may not. Organizations can further strengthen their security posture by utilizing automated vendor risk assessment solutions to streamline compliance across these various standards.
Implementation Guidance for Clinical App Developers
Determining Compliance Requirements
Before diving into development, it's crucial to identify the encryption standards your clinical app must meet. In the United States, HIPAA compliance is mandatory for organizations handling electronic protected health information (ePHI). Meanwhile, frameworks like HITRUST and ISO 27001 are optional but provide a certifiable path to meeting compliance standards [6].
To figure out your app's compliance scope, tools like the HITRUST MyCSF portal can be incredibly useful. These tools help pinpoint the necessary controls based on your organization's size, industry, and systems [9]. For instance, if your app is intended for federal government use, you'll need to meet NIST compliance standards [6]. Similarly, if your app processes data beyond ePHI - like credit card information or international customer data - opting for HITRUST or ISO 27001 can simplify compliance across multiple regulatory frameworks [10].
In some cases, your partners may specifically require HITRUST certification. As Ryan Winkler, a HITRUST Advisory Council Member at 360 Advanced, points out:
"Because the framework [HITRUST] covers all HIPAA standards, it can help companies focus in on what they need for compliance. This means that as long as a company implements the applicable HITRUST CSR control requirements, they're also meeting HIPAA specifications"
.
Budget is another key factor to consider. HITRUST certification for startups typically costs between $60,000 and $120,000 annually, while failing to comply with HIPAA can result in fines of up to $1.5 million per year [7][8][9].
Once you've outlined your compliance requirements, the next step is integrating these standards into your app's risk management strategy.
Encryption in Risk Management Platforms
After determining compliance needs, incorporating encryption standards into a risk management platform can save time and reduce errors. For example, Censinet RiskOps™ provides healthcare organizations with a centralized system to manage encryption requirements across third-party and internal risk assessments. This platform automates critical safeguards like audit logging, role-based access control (RBAC), and session management - all essential for HIPAA compliance [11].
Automation helps shift security efforts from manual tracking to structured management. Instead of juggling vendor BAAs (Business Associate Agreements) and encryption protocols manually, Censinet RiskOps™ consolidates all this information into a single dashboard. This is especially helpful when dealing with the shared responsibility model, where compliance depends not only on the platform provider's measures but also on additional safeguards like multi-factor authentication (MFA) and RBAC implemented by developers [11].
For organizations pursuing HITRUST certification - covering 19 control categories with varying implementation levels - a risk management platform is almost indispensable [10]. Censinet RiskOps™ simplifies risk assessments and cybersecurity benchmarking, helping healthcare organizations and vendors continuously enforce HIPAA and HITRUST encryption standards. It ensures encryption controls are consistently applied across the vendor ecosystem, minimizing the chance of PHI ending up in non-compliant areas like server logs, third-party analytics, or customer support systems [12].
HIPAA Requirements: Encryption at Rest and in Transit #HIPAA #cybersecurity #breach #data #it #phi
Conclusion: Selecting the Right Encryption Standard
HIPAA vs NIST vs HITRUST vs ISO 27001 Encryption Standards Comparison
Choosing the right encryption standard means matching your clinical app's needs with the appropriate framework, considering both the sensitivity of the data and the operational environment. For handling U.S. ePHI, HIPAA’s addressable encryption provides a reliable starting point. However, more complex environments - such as federal, international, or multi-partner settings - might require adherence to NIST, HITRUST, or ISO 27001 standards.
Change is on the horizon. By 2025, HIPAA updates may require AES-256 encryption. Margaret Hales, J.D., suggests using a hybrid approach that combines HIPAA with NIST or HITRUST controls to counter emerging threats like phishing [13][2]. This highlights the growing importance of staying ahead with strong encryption practices.
The Office for Civil Rights (OCR) monitoring reveals a troubling trend: most healthcare breaches happen because encryption is either missing or insufficient. Annual OCR investigations often trace major breaches back to outdated encryption protocols, weak passwords, or inadequate logging practices [14]. Addressing these vulnerabilities can reduce the risk of breaches and the financial penalties that follow [1].
Here’s a quick comparison of the key standards:
Addressable (becoming mandatory)
U.S. ePHI protection, flexible implementation
Small- to mid-sized U.S. healthcare apps
Required (FIPS 140-3 validated)
Federal data and strong hardware/software security
Apps serving government healthcare
Required
Comprehensive PHI protection and vendor certification
Enterprise apps and multi-partner ecosystems
Required (risk-based controls)
Global information security management and compliance
Apps with international customers or data
For most healthcare organizations, starting with HIPAA compliance is a practical first step. As your app or organization scales, transitioning to HITRUST or ISO 27001 can provide broader security coverage and meet more demanding requirements. Tools like Censinet RiskOps™ can simplify this process by centralizing encryption management, automating audit logs, and handling third-party risk assessments. These solutions help ensure your clinical applications remain compliant and secure as standards and threats evolve.
FAQs
Does HIPAA require encryption today?
Yes, HIPAA mandates the encryption of all electronic Protected Health Information (ePHI) when it is stored, transmitted, or accessed remotely. This encryption requirement has been reinforced under the 2025 guidelines to provide stronger safeguards for sensitive patient information.
What qualifies as 'NIST-approved encryption' for safe harbor?
When we talk about NIST-approved encryption for safe harbor, we're referring to algorithms validated under FIPS 140-2. This includes encryption methods such as AES-256, Triple DES, and RSA, all of which align with NIST guidelines like SP 800-52 for encryption protocols. These standards are essential for meeting HIPAA requirements and ensuring the protection of sensitive data, such as Protected Health Information (PHI).
When should a clinical app pursue HITRUST or ISO 27001?
When developing a clinical app, pursuing HITRUST certification can showcase a strong security framework tailored to healthcare. This certification combines HIPAA requirements with well-known standards like NIST and ISO, making it particularly suited for managing healthcare-specific risks. It's especially valuable for cloud-based services that handle Protected Health Information (PHI).
On the other hand, ISO 27001 is a great choice for organizations aiming for a globally recognized, risk-focused approach to information security. It’s ideal for businesses with international operations or those needing to address a broader range of compliance requirements beyond healthcare-specific concerns.
Related Blog Posts
- How PHI Encryption Impacts System Performance
- Best Practices for End-to-End Encryption in Healthcare
- HIPAA Encryption Rules for Data in Transit
- Encryption in Transit: Compliance for Healthcare IT
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":[{"@type":"Question","name":"Does HIPAA require encryption today?","acceptedAnswer":{"@type":"Answer","text":"<p>Yes, HIPAA mandates the encryption of all electronic Protected Health Information (ePHI) when it is stored, transmitted, or accessed remotely. This encryption requirement has been reinforced under the 2025 guidelines to provide stronger safeguards for sensitive patient information.</p>"}},{"@type":"Question","name":"What qualifies as 'NIST-approved encryption' for safe harbor?","acceptedAnswer":{"@type":"Answer","text":"<p>When we talk about <strong>NIST-approved encryption</strong> for safe harbor, we're referring to algorithms validated under <strong>FIPS 140-2</strong>. This includes encryption methods such as <strong>AES-256</strong>, <strong>Triple DES</strong>, and <strong>RSA</strong>, all of which align with NIST guidelines like <strong>SP 800-52</strong> for encryption protocols. These standards are essential for meeting <strong>HIPAA requirements</strong> and ensuring the protection of sensitive data, such as <strong>Protected Health Information (PHI)</strong>.</p>"}},{"@type":"Question","name":"When should a clinical app pursue HITRUST or ISO 27001?","acceptedAnswer":{"@type":"Answer","text":"<p>When developing a clinical app, pursuing <strong>HITRUST certification</strong> can showcase a strong security framework tailored to healthcare. This certification combines HIPAA requirements with well-known standards like NIST and ISO, making it particularly suited for managing healthcare-specific risks. It's especially valuable for cloud-based services that handle Protected Health Information (PHI).</p> <p>On the other hand, <strong>ISO 27001</strong> is a great choice for organizations aiming for a globally recognized, risk-focused approach to information security. It’s ideal for businesses with international operations or those needing to address a broader range of compliance requirements beyond healthcare-specific concerns.</p>"}}]}
Key Points:
What does HIPAA's "addressable" encryption classification mean in practice for clinical app developers?
- Addressable does not mean optional, as the term requires organizations to evaluate the feasibility and appropriateness of encryption for their environment, implement it when reasonable and appropriate, or implement an equivalent alternative control with documented justification
- The breach notification safe harbor provides a powerful incentive for implementation, because ePHI encrypted using NIST-approved methods and with encryption keys remaining secure may qualify for an exemption from breach notification requirements under 45 CFR 164.402 even if the data is lost or stolen
- The 2025 proposed HIPAA Security Rule update would eliminate the addressable classification for encryption entirely, making AES-256 for data at rest and TLS 1.2 or higher for data in transit mandatory requirements with a likely 180-day compliance window following finalization
- Enforcement patterns already treat unencrypted ePHI losses as serious violations, with the University of Rochester Medical Center paying a $3 million fine for a single unencrypted flash drive and laptop loss and Children's Medical Center of Dallas paying $3.2 million following theft of unencrypted devices
- The OCR monitoring record shows that most major healthcare breaches trace back to encryption that was missing or insufficient, making the addressable classification a source of false assurance for organizations that interpret it as permission to defer implementation
- Clinical app developers should implement encryption as a default design requirement rather than a post-development compliance addition, applying AES-256 to object storage, block volumes, database snapshots, and replicas with automatic inheritance of encryption protections
How do NIST encryption standards relate to HIPAA and why should clinical app developers follow them?
- NIST provides the technical specificity that HIPAA lacks, with HIPAA offering broad directives such as "implement a mechanism" to secure ePHI while NIST specifies precise protocols including AES-256 for data at rest, TLS 1.3 for data in transit, and SHA-256 for hashing
- HIPAA directly references NIST standards without mandating their use, which means following NIST provides a documented, defensible technical implementation path for HIPAA's addressable encryption requirement without requiring separate justification
- A 2021 amendment to the HITECH Act introduced an enforcement incentive for NIST adoption, providing that covered entities demonstrating 12 months of compliance with a recognized security framework like NIST may receive reduced OCR enforcement actions, making NIST alignment a risk management investment as well as a technical one
- NIST SP 800-111 governs encryption for data at rest and recommends full-disk encryption using AES-256 in XTS or CBC mode for laptops, mobile devices, and Transparent Data Encryption for databases
- NIST SP 800-52 governs encryption for data in transit and emphasizes disabling outdated protocols including TLS 1.0, TLS 1.1, 3DES, and RC4 while requiring TLS 1.2 at minimum and TLS 1.3 for new implementations
- NIST SP 800-57 provides comprehensive key management guidance covering encryption key creation, rotation, storage, and destruction, ensuring that the keys protecting ePHI are managed with the same rigor as the encrypted data itself
How does HITRUST CSF compare to HIPAA for clinical app encryption compliance?
- HITRUST CSF combines HIPAA, NIST, ISO 27001, and other standards into a single unified risk-based framework, providing clinical app developers with a single certifiable path to multi-standard compliance rather than maintaining separate compliance programs for each framework
- HITRUST certification requires implementing controls across 19 control categories at varying levels of stringency, making it more prescriptive and demanding than HIPAA alone but providing a higher level of assurance to healthcare partners and enterprise customers
- Partners at the enterprise level increasingly require HITRUST certification rather than HIPAA compliance attestations alone, because HITRUST certification provides independent third-party verification that controls meeting HIPAA specifications are in place and functioning
- HITRUST certification for startups typically costs between $60,000 and $120,000 annually, which must be weighed against HIPAA non-compliance penalties of up to $1.5 million per year per violation category and the reputational and operational costs of a breach
- HITRUST certification demonstrates compliance with HIPAA while simultaneously aligning with NIST and ISO 27001, which simplifies the compliance burden for organizations operating in complex multi-partner ecosystems where different partners may require different framework attestations
- Automated risk management platforms such as Censinet RiskOps help organizations pursuing HITRUST certification by centralizing encryption compliance management, automating audit logging, and ensuring encryption controls are consistently applied across the vendor ecosystem
How does ISO 27001 differ from HIPAA for international clinical app deployments?
- ISO 27001 is an international standard for information security management that applies to all types of organizational data, not only ePHI, making it the appropriate framework for clinical apps operating in markets outside the United States or processing data categories beyond US-regulated health information
- ISO 27001's cryptographic controls in Annex A 10.1 require organizations to establish clear policies for encryption use based on risk assessment, emphasizing management processes and governance rather than prescribing specific technical algorithms, which provides more flexibility than HIPAA's NIST-referenced technical requirements
- ISO 27001 certification involves third-party audits by accredited bodies and detailed key management policies covering key generation, storage, retrieval, and destruction, making it a more rigorous certification process than HIPAA compliance attestations that do not require independent third-party verification
- ISO 27001 certification provides a competitive advantage in international markets where HIPAA compliance is not recognized and where healthcare partners may require evidence of internationally accepted information security governance
- Organizations can implement HIPAA and ISO 27001 controls simultaneously because the frameworks are complementary rather than contradictory, with ISO 27001 providing the broader information security governance structure within which HIPAA-specific ePHI controls operate
- Clinical app developers targeting federal government use must also consider NIST compliance independently of ISO 27001 or HIPAA, as federal healthcare applications are subject to FIPS 140-3 validated cryptographic module requirements that exceed standard HIPAA or ISO 27001 specifications
What encryption implementation requirements apply specifically to clinical apps handling ePHI?
- Encryption must be integrated at every layer of a clinical application, from object storage and block volumes at the infrastructure level to telehealth video streams, APIs, and patient-facing interfaces at the application level
- Default-on encryption for cloud storage should ensure that snapshots and replicas automatically inherit encryption protections, eliminating the risk that backup or archive copies of ePHI are stored without the same encryption applied to primary data
- Mobile clinical apps require Mobile Device Management policies that block local backups of ePHI and enable remote-wipe capabilities, because mobile devices represent a high-risk vector for unencrypted ePHI exposure through loss or theft
- Service-to-service communication within clinical systems should use mutual TLS, which provides both encryption and mutual authentication, ensuring that internal API calls between components of a clinical application cannot be intercepted or spoofed
- Telehealth video streams should implement TLS 1.3 with forward secrecy across web portals, APIs, and all patient-facing systems, ensuring that session data cannot be decrypted retroactively even if encryption keys are later compromised
- Organizations are transitioning from FIPS 140-2 to FIPS 140-3 validated cryptographic modules and should monitor NIST's post-quantum encryption standards, with hybrid key exchange experimentation recommended for applications with long data retention requirements where quantum computing threats may become relevant within the data's useful life
How should clinical app developers determine which encryption framework applies to their compliance requirements?
- HIPAA compliance is the mandatory baseline for any US clinical app handling ePHI, and the first step is confirming whether the application's data and workflows are subject to HIPAA coverage before layering additional framework requirements
- HITRUST certification is the appropriate next layer for enterprise apps operating in multi-partner ecosystems where partners require third-party certified assurance of HIPAA compliance and where managing separate attestations for multiple frameworks is operationally impractical
- ISO 27001 certification is the appropriate framework for apps with international operations or non-ePHI data processing requirements that extend beyond the scope of HIPAA, particularly where European or Asia-Pacific partners or regulators require internationally recognized information security certification
- Federal government healthcare apps require NIST compliance and FIPS 140-3 validated cryptographic modules regardless of which other frameworks apply, making NIST alignment a separate and additional requirement for this deployment context
- Budget constraints are a legitimate factor in framework selection, with HITRUST certification typically costing $60,000 to $120,000 annually for startups, and organizations should assess this cost against the revenue risk of being excluded from enterprise healthcare partnerships that require HITRUST certification
- Automated risk management platforms such as Censinet RiskOps centralize encryption compliance management across multiple frameworks, automating audit logging, consolidating vendor BAA tracking, and providing real-time visibility into encryption control implementation across the vendor ecosystem


