NIST Framework and HIPAA: Aligning for Healthcare Compliance
Post Summary
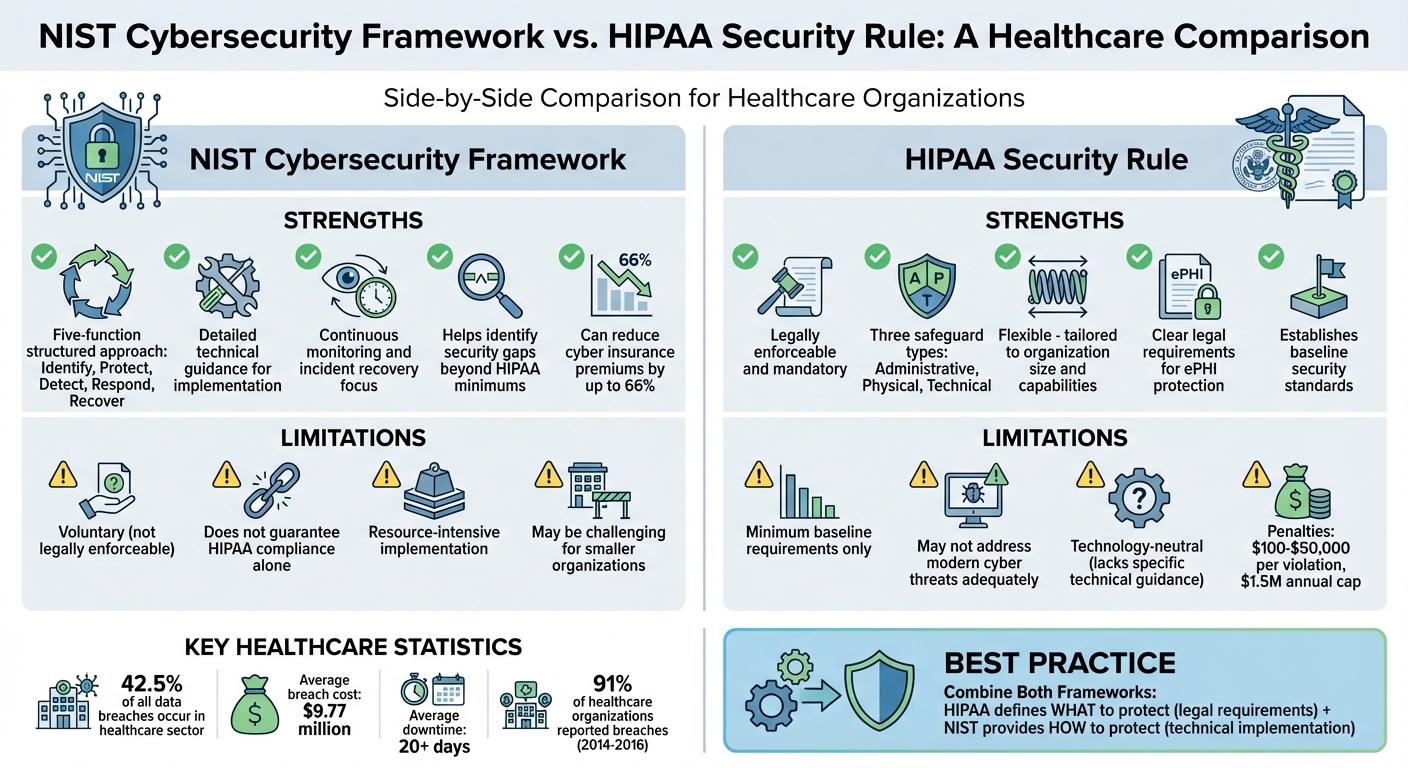
Healthcare organizations face increasing threats to patient data security, with over 40% of reported data breaches occurring in this sector over three years. Combining the NIST Cybersecurity Framework with HIPAA's Security Rule offers a structured way to protect sensitive electronic protected health information (ePHI) while meeting legal requirements.
Here’s what you need to know:
- HIPAA Security Rule: Sets mandatory safeguards for ePHI, including administrative, physical, and technical requirements.
- NIST Cybersecurity Framework: Provides a practical, five-step approach to security: Identify, Protect, Detect, Respond, and Recover.
- OCR Crosswalk Tool: Maps HIPAA requirements to NIST controls, simplifying alignment and identifying gaps.
- Penalties: HIPAA violations can cost $100 to $50,000 per incident, with annual caps of $1.5 million.
- Tools: Platforms like Censinet RiskOps™ streamline risk assessments and compliance efforts.
Aligning these frameworks strengthens security, reduces risks, and helps avoid penalties. Start by using the OCR crosswalk to map safeguards and appoint a security officer to oversee compliance. This approach not only keeps you compliant but also better protects patient data.
1. NIST Cybersecurity Framework
Core Functions and Safeguards
The NIST Cybersecurity Framework breaks down security into five core functions, offering healthcare organizations a clear path to protect electronic protected health information (ePHI). Here's how it works:
- Identify: Healthcare organizations regularly assess assets and risks to understand vulnerabilities.
- Protect: Safeguards like access controls, encryption, and workforce training ensure only authorized individuals can access PHI.
- Detect: Systems are monitored and audited to catch unauthorized access attempts quickly.
- Respond: A security incident response plan helps organizations minimize damage during a breach.
- Recover: Contingency plans, backups, and disaster recovery efforts restore services after an incident.
This structured framework helps organizations align their cybersecurity efforts with compliance goals through crosswalk mapping.
Alignment and Crosswalk Mapping
To bridge the gap between HIPAA requirements and NIST controls, the Office for Civil Rights (OCR), NIST, and the Office of the National Coordinator for Health IT created a crosswalk tool. This tool maps HIPAA Security Rule requirements to NIST CSF controls, making it easier for healthcare providers to spot vulnerabilities in their security programs.
While using the NIST CSF is not mandatory for HIPAA compliance, it offers detailed technical guidance that HIPAA's broader, technology-neutral regulations lack. In essence, it provides a "how-to" for implementing specific security measures.
Benefits for Healthcare Compliance
By following the NIST framework, healthcare organizations can strengthen both their compliance efforts and their overall security strategies. The framework's systematic approach ensures that entities address all key areas, from risk analysis to disaster recovery, while remaining adaptable to different organizational sizes and complexities.
Using the OCR crosswalk, organizations can identify specific weaknesses in their current practices. This is critical, considering that 42.5% of all reported data breaches in a recent three-year period occurred within the healthcare sector [2]. Adopting NIST's five core functions not only helps meet HIPAA's administrative, physical, and technical safeguard requirements but also builds a stronger defense against emerging threats.
Additionally, tools like Censinet RiskOps™ can simplify this process by streamlining risk assessments and enhancing collaborative risk management. These platforms support healthcare organizations in achieving HIPAA compliance while improving their overall security posture.
sbb-itb-535baee
Road to HIPAA Compliance: Using the NIST Cybersecurity Framework to Protecting PHI
2. HIPAA Security Rule
The HIPAA Security Rule builds on the structured NIST Cybersecurity Framework by setting mandatory safeguards specifically designed for healthcare organizations.
Core Functions and Safeguards
Under the HIPAA Security Rule, covered entities must protect electronic protected health information (ePHI) using three types of safeguards:
- Administrative safeguards: These include appointing a security officer to oversee compliance and conducting regular risk assessments.
- Physical safeguards: These focus on controlling access to facilities and securing workstations.
- Technical safeguards: These involve implementing access controls, encryption, and audit mechanisms to track and monitor data access.
The rule's flexibility allows organizations to tailor these measures based on their size and specific risks.
Alignment and Crosswalk Mapping
To simplify compliance, the crosswalk tool maps HIPAA requirements to NIST controls. This tool helps organizations already using one framework identify gaps in the other. For instance, NIST's detection processes (DE.DP) align with HIPAA's mandate to appoint a security officer, while its response planning (RS.RP) corresponds to HIPAA's requirements for handling security incidents.
"The crosswalk provides a helpful roadmap for HIPAA covered entities and their business associates to understand the overlap between the NIST Cybersecurity Framework, the HIPAA Security Rule, and other security frameworks that can help entities safeguard health data." - U.S. Department of Health and Human Services [1]
This alignment not only helps meet legal obligations but also simplifies and strengthens cybersecurity efforts.
Benefits for Healthcare Compliance
Integrating HIPAA standards with NIST controls offers clear advantages. Organizations can systematically pinpoint security gaps and take targeted actions to better protect ePHI. This is critical, considering that 91% of healthcare organizations reported data breaches between 2014 and 2016 [1].
The financial risks are steep, with penalties ranging from $100 to $50,000 per violation and annual caps of $1.5 million. Beyond avoiding fines, aligning these frameworks enhances patient trust and boosts an organization's reputation.
"Taking specific action to address these gaps can bolster compliance with the Security Rule and improve an entity's ability to secure ePHI from a broad range of threats." - Office for Civil Rights (OCR) [1]
Healthcare providers should prioritize appointing a dedicated security officer, routinely auditing monitoring systems, and testing detection and recovery processes. Leveraging tools like the OCR crosswalk ensures that security investments meet both regulatory and cybersecurity needs.
Platforms like Censinet RiskOps™ (https://censinet.com) can further simplify compliance by streamlining risk assessments and aligning with both HIPAA and NIST requirements.
Pros and Cons
NIST Framework vs HIPAA Security Rule Comparison for Healthcare Compliance
When you look at healthcare cybersecurity through the lens of established frameworks, it's clear there are both strengths and limitations to consider.
The NIST Cybersecurity Framework stands out for its structured, five-function approach: Identify, Protect, Detect, Respond, and Recover. It provides detailed guidance for continuous monitoring and incident recovery, making it easier for organizations to spot security gaps and vendor risks that HIPAA's minimum requirements might miss. However, there's a catch - NIST is voluntary. It doesn't carry legal weight, meaning compliance with NIST alone won't guarantee you're meeting HIPAA standards. Plus, implementing NIST's full set of controls can demand significant resources, which might be a challenge for smaller organizations.
On the other hand, the HIPAA Security Rule is legally enforceable, with strict requirements designed to protect electronic protected health information (ePHI). Its mandatory nature means that non-compliance can lead to hefty fines - ranging from $100 to $50,000 per violation, with annual caps reaching $1.5 million. The flexibility within the rule allows organizations to tailor safeguards to their size and capabilities, but it’s still a baseline standard. And in a world where healthcare accounted for 42.5% of all reported data breaches over a recent three-year period [2], sticking to just the minimum requirements may leave organizations exposed to modern cyber threats.
"By aligning NIST CSF with HIPAA's Security Rule, you can strengthen your data security and protect PHI beyond HIPAA's minimum requirements." - RSI Security [3]
The best strategy? Combine both frameworks. HIPAA spells out the legal "what" you need to do, while NIST offers the technical "how" to do it. Mapping HIPAA compliance to NIST's functions can help uncover vulnerabilities and ensure patient data is better protected.
Conclusion
Healthcare organizations face a critical choice: stick to the basics of compliance or adopt a stronger cybersecurity approach that safeguards both operations and patient care. Aligning the NIST Cybersecurity Framework with HIPAA requirements offers a way to achieve both. With the average data breach costing $9.77 million and causing over 20 days of downtime [4], the risks are too big to ignore.
A good starting point is to use the OCR crosswalk tool to map HIPAA safeguards to NIST's core functions. This process strengthens compliance while addressing real-world risks. It also helps identify vulnerabilities that standard HIPAA audits might miss. Appointing a dedicated security officer to oversee this alignment can push your organization toward a more proactive approach to risk management.
"You need HIPAA to remain legal. You need NIST to remain operational." - CompassMSP [4]
Enhance your readiness by conducting regular tabletop exercises with IT, legal, and clinical teams. Strengthen your defenses with measures like multi-factor authentication, continuous monitoring, and recovery plans designed to keep patient care uninterrupted during cyber incidents.
The advantages go beyond compliance. Organizations using the NIST Cybersecurity Framework have seen cyber insurance premiums drop by as much as 66% [4]. While HIPAA outlines what needs protection, NIST provides the "how" for effective safeguarding.
For those looking to simplify this integration, tools like Censinet RiskOps™ offer a practical solution. Platforms like these help healthcare organizations move past basic compliance and embrace a comprehensive risk management strategy that aligns HIPAA with NIST.
FAQs
What’s the quickest way to map HIPAA Security Rule safeguards to NIST CSF?
The quickest way to align the HIPAA Security Rule safeguards with the NIST Cybersecurity Framework is by using a crosswalk tool. These tools offer a detailed, control-by-control mapping along with clear explanations. Trusted sources, like the Department of Health and Human Services (HHS), provide such resources to make the process easier. This approach helps healthcare organizations simplify compliance and better align their efforts with both frameworks.
How can I show that NIST-based controls support HIPAA compliance during an OCR audit?
To meet HIPAA Security Rule requirements, leverage official crosswalk documents that map NIST Cybersecurity Framework (CSF) controls to these standards. These crosswalks provide a structured way to ensure your organization's cybersecurity measures align with regulatory expectations.
Document how these controls are applied within your organization. This includes detailing your policies, procedures, and risk assessments. Each of these elements plays a critical role in demonstrating compliance and maintaining a robust security posture.
It's equally important to perform regular evaluations of your controls. This ensures they remain effective and adapt to evolving threats or regulatory updates. Keeping your documentation up to date will also help during audits or reviews.
To simplify this process, tools like Censinet RiskOps™ can be invaluable. They streamline evidence collection and compliance management, making it easier to demonstrate alignment with both NIST and HIPAA requirements - particularly during an OCR audit.
What should a HIPAA security officer prioritize first when aligning NIST and HIPAA?
To kick off, a HIPAA security officer needs to perform a thorough risk assessment. This process helps uncover weaknesses and gaps in the organization's cybersecurity framework. By addressing risks tied to patient data, PHI (Protected Health Information), and other sensitive areas, this step ensures the program aligns with both NIST standards and HIPAA requirements. It also sets the stage for building a strong compliance strategy.


