5 Steps for HIPAA Data Labeling Compliance
Post Summary
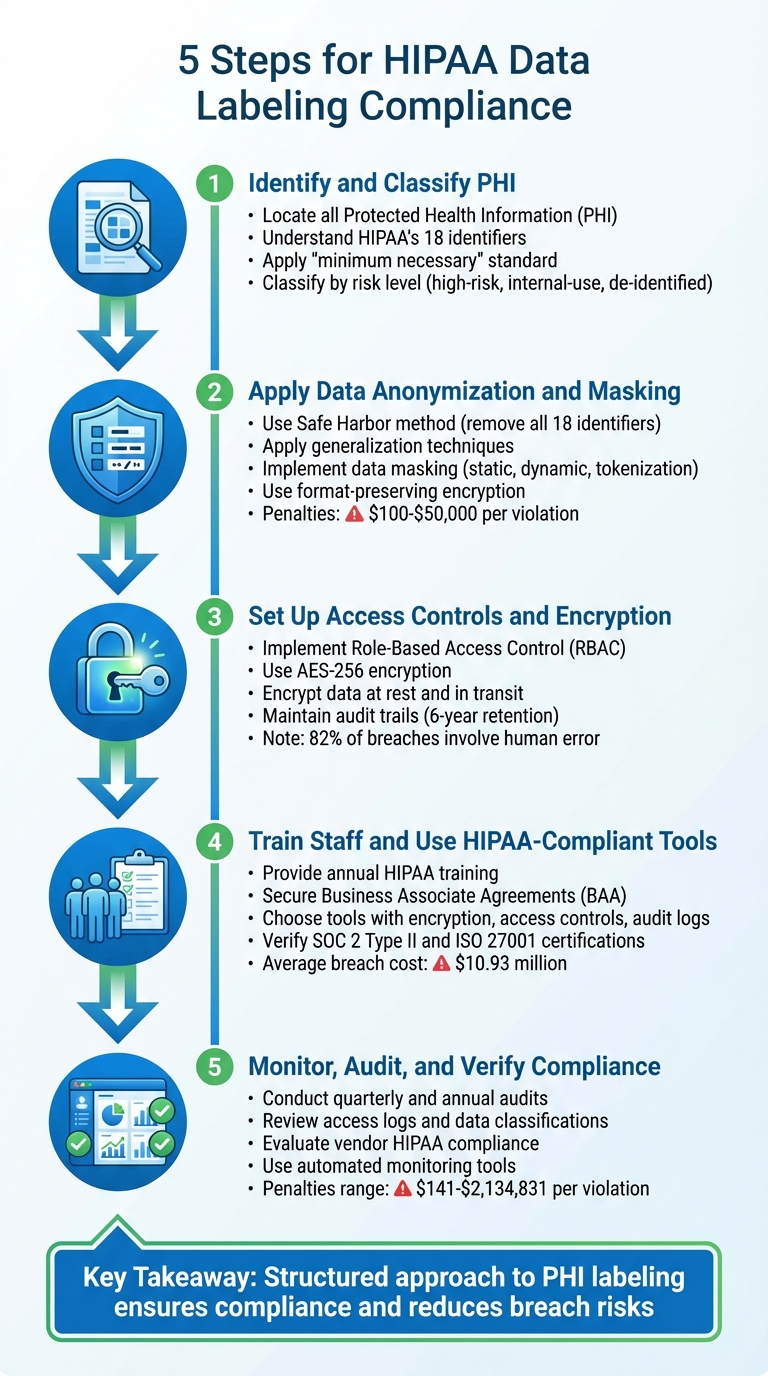
Managing healthcare data securely and aligning with HIPAA rules is no small task. Here's how you can streamline the process in five actionable steps:
- Identify and Classify PHI: Locate all Protected Health Information (PHI) in your systems and classify it based on risk levels. Understand HIPAA’s 18 identifiers and apply the "minimum necessary" standard to limit access.
- Apply Data Anonymization and Masking: De-identify or mask sensitive data to protect patient privacy. Use techniques like Safe Harbor, generalization, and format-preserving encryption for compliance.
- Set Up Access Controls and Encryption: Implement role-based access controls (RBAC) and encrypt data at rest and in transit using robust methods like AES-256. Maintain detailed audit trails to monitor access and actions.
- Train Staff and Use HIPAA-Compliant Tools: Regularly train employees on HIPAA standards and data handling. Choose labeling tools that offer encryption, access controls, and thorough audit logs.
- Monitor, Audit, and Verify Compliance: Conduct regular audits of your processes and vendors. Use tools to track PHI, ensure data security, and maintain compliance with HIPAA's technical safeguards.
Key takeaway: A structured approach to labeling and securing PHI not only ensures compliance but also reduces risks of breaches and penalties. By combining effective tools, staff training, and regular audits, you can safeguard patient data and meet HIPAA requirements confidently.
5 Steps for HIPAA Data Labeling Compliance
HIPAA Compliance in Nutshell | HIPAA Rules | PHI Data | HIPAA Compliance to whom does it applicable?
sbb-itb-535baee
Step 1: Identify and Classify PHI
The first step to ensuring HIPAA-compliant data labeling is understanding what qualifies as PHI (Protected Health Information) and identifying where it resides within your systems. According to HIPAA, PHI includes any individually identifiable health information related to a person’s health status, care, or payment, created or received by a covered entity or business associate. This includes 18 specific identifiers, ranging from names and Social Security numbers (SSNs) to IP addresses and device serial numbers.
A key part of this process is distinguishing between direct and indirect identifiers. Direct identifiers, like SSNs, can immediately pinpoint an individual, while indirect identifiers - such as a combination of a birth date and ZIP code - require additional context to reveal someone’s identity. The 18th identifier acts as a “catchall,” covering any unique identifying number, code, or characteristic not explicitly listed, ensuring the framework remains adaptable to technological changes.
Conduct a PHI Risk Assessment
Start by creating a detailed inventory that maps out where PHI exists and how it moves through your systems. This should include every system, database, and workflow that stores or processes PHI. Common examples include electronic health records (EHRs), billing systems, patient portals, email servers, and even backup storage. Don’t overlook unstructured data, like clinician notes, where identifiers might be hidden.
Regular audits of data pipelines are essential to uncover hidden risks. For example, metadata in image files or URLs embedded in clinical documentation may inadvertently expose patient information. By mapping out the locations of PHI, identifying access points, and tracking data flows, you’ll gain a clear picture of where vulnerabilities might exist. This groundwork sets the stage for assessing and categorizing PHI based on its risk level.
Categorize PHI by Risk Level
Once PHI is located, the next step is to classify it based on its sensitivity and regulatory requirements. This classification helps determine the security measures needed to protect the data. High-risk data includes direct identifiers like SSNs, medical record numbers, or full-face photos, which demand the strictest safeguards. On the other hand, internal-use data might include broader details, such as dates (excluding the year) or general geographic information, which are allowed in limited data sets. De-identified or public data, where all 18 identifiers are removed, carries minimal risk of re-identification.
It’s important to adhere to HIPAA’s minimum necessary standard, which means limiting access to only the information required for a specific task. For example, a billing clerk processing claims doesn’t need to see clinical notes with diagnostic details, just as a researcher studying treatment outcomes shouldn’t have access to patient names or contact information. Proper classification ensures that security measures like encryption, access controls, and retention policies can be applied effectively, as outlined in later steps.
Step 2: Apply Data Anonymization and Masking
Once you've classified PHI, the next step is to protect it by anonymizing patient identities. Data anonymization, often referred to as de-identification under HIPAA, involves altering personally identifiable information to ensure individuals cannot be identified. Within this broader category, data masking is a specific technique that replaces sensitive values with realistic, fictitious data while preserving the structure of the original dataset.
The distinction between these approaches lies in their purpose. Data masking ensures the data remains functional for tasks like software testing or training machine learning models. In contrast, full anonymization permanently removes any links to the individual. Your choice will depend on whether the data needs to be reversible for authorized users or not.
Remove Identifiable Data from PHI
To de-identify data, you can use the Safe Harbor method, which involves removing all 18 HIPAA identifiers. This method is straightforward and doesn't require statistical analysis.
However, in scenarios where complete removal isn't feasible - such as when data is needed for research or analytics - generalizing data can help. For instance, you could convert exact ages into 5-year ranges or reduce ZIP codes to their first three digits. Studies show that combining year of birth, sex, and a 3-digit ZIP code results in a unique identifier for only about 0.04% of U.S. residents, making it a low-risk combination. On the other hand, using a full date of birth, sex, and a 5-digit ZIP code creates a unique identifier for over 50% of U.S. residents, significantly increasing the risk of re-identification [1].
Before implementing any strategy, map all data touchpoints, such as logs, business intelligence extracts, and cloud storage, to ensure no PHI remains in its original form in secondary locations. This step is critical to avoid data leakage.
With identifiable data minimized, you can then apply masking techniques to maintain data usability while ensuring security.
Use Data Masking Techniques
Data masking allows you to create a version of your dataset that retains the structure and behavior of the original data without exposing actual patient information. Depending on your needs, you can use:
- Static masking: Provides irreversible protection for data stored at rest.
- Dynamic masking: Offers real-time, user-specific views of data.
Tokenization is another effective method, where sensitive data - like a Social Security number - is replaced with a random alphanumeric string that maintains the same length and format. To ensure accurate analysis, consistent masking across related tables (referential integrity) is essential. Deterministic masking functions can help maintain these relationships.
"Data masking techniques are essential for organizations that need access to realistic data that offers a high degree of fidelity to real-world data while safeguarding sensitive information." – Tonic.ai
Format-preserving encryption is particularly useful for applications that require data usability without altering schemas. For example, phone numbers can remain as 10-digit strings, and dates can stay in MM/DD/YYYY format, though their values are altered. This method is especially valuable when workflows require the ability to restore data using a decryption key. For more advanced needs, synthetic data generation can create artificial datasets that mimic real PHI properties without containing any actual sensitive information.
These masking techniques lay the groundwork for subsequent steps, such as implementing access controls and encryption.
It’s essential to regularly test reports, alerts, and clinical models to ensure they function correctly after masking. This step ensures the data remains useful while complying with HIPAA regulations. Non-compliance can result in penalties ranging from $100 to $50,000 per violation, with annual caps of $1.5 million [2]. Properly applying these techniques is not just a regulatory requirement but also a critical financial safeguard.
Step 3: Set Up Access Controls and Encryption
After masking and labeling data, the next step is to implement controls that align with HIPAA's technical safeguard requirements. This involves restricting access, encrypting data, and maintaining detailed monitoring systems to track every interaction with sensitive information.
Enforce Role-Based Access Control (RBAC)
Role-Based Access Control (RBAC) ensures that only those who need access to PHI for their specific job roles can retrieve it. Assign permissions based on roles so that users can access only the data necessary for their responsibilities.
The 2022 Verizon Data Breach Investigations Report revealed that human error contributed to 82% of data breaches [4]. A common issue? Sharing login credentials, which disrupts audit trails and makes it unclear who accessed sensitive data. To mitigate this, ensure each user has unique login credentials and avoid credential sharing.
Map out job functions and assign the minimum access required. For instance, a receptionist may need access to appointment schedules and contact details but shouldn’t see clinical notes or lab results. Regularly review and update access levels to reflect any changes in roles or responsibilities.
Once access controls are in place, encryption is the next layer of protection.
Encrypt Data at Rest and In Transit
Encryption is key to safeguarding PHI. Use encryption methods like AES-256 to make data unreadable without the appropriate decryption key. While HIPAA doesn’t specify particular encryption standards, AES-256 is widely recognized as a robust option for securing data both at rest (stored on servers, databases, or devices) and in transit (transferred across networks or systems). Following NIST guidelines ensures encryption is strong enough to render data useless to unauthorized individuals in the event of a breach.
If you used format-preserving encryption during the masking phase, it maintains the usability of data without requiring changes to database schemas. However, if re-identification codes are used, their disclosure must be tracked, as it would count as a disclosure of PHI.
Encryption alone isn’t enough - ongoing monitoring is critical to maintaining compliance and accountability.
Set Up Audit Trails for Monitoring
Audit trails document every interaction with ePHI, creating both a compliance record and a tool for identifying unauthorized access. They are essential for accountability and for detecting issues before they escalate.
"Audit Controls: This measures any attempted access to PHI and what actions were taken on the records." – Beth Osborne, Freelance Writer, Infosec Institute [5]
The numbers are sobering: in just the first quarter of 2018, 1.12 million records were exposed across 110 healthcare data breaches [5]. During an OCR investigation, organizations must provide proof of regular system activity reviews. Simply collecting logs isn’t enough - procedures must be in place to actively analyze them. Typically, the HHS Office for Civil Rights requires documentation within 30 days to address complaints [3].
"If a HIPAA-regulated entity is unable to prove they have a HIPAA compliance program in place, then a financial penalty is all but guaranteed." – Steve Alder, Editor-in-Chief, HIPAA Journal [4]
Real-time monitoring systems can flag unauthorized access to PHI, helping catch and address non-compliant practices - like shared login credentials - before they become systemic issues.
HIPAA mandates that audit records and system reviews be retained for at least six years [3][4]. These records can be stored physically or through HIPAA-compliant software, which simplifies the process while maintaining compliance. Automated logging tools with end-to-end encryption can further streamline data tracking and ensure every change or movement of data is recorded accurately.
Step 4: Train Staff and Select Compliant Labeling Tools
After implementing strict access controls and encryption, the next step is addressing the human element. Even the best security measures can fall short if staff aren't properly trained or if the tools they rely on fail to meet HIPAA standards.
Provide Regular HIPAA Training
Labelers don’t just handle data - they’re entrusted with federally protected PHI. The stakes are enormous: in 2023, healthcare data breaches averaged a staggering $10.93 million in costs, the highest across industries[6]. On top of that, fines for willful neglect can exceed $2 million per violation category annually[6].
"Your labelers aren't just data entry clerks - they are data guardians." – Acciyo[6]
Ensure all staff undergo annual HIPAA training, as well as additional training triggered by policy updates. New hires should complete this training before they ever handle PHI. The sessions should cover:
- Privacy and Security Rules relevant to data labeling.
- The two approved de-identification methods: Safe Harbor and Expert Determination.
- The "Minimum Necessary" standard, which limits access to only the data points required for a specific task. For example, a labeler identifying tumor locations doesn’t need access to a patient’s full name or billing details.
Maintain thorough documentation of every training session, including attendance records, to create an audit trail that demonstrates compliance through advanced third-party risk management.
Once your staff is well-trained, the next step is equipping them with the right tools.
Choose HIPAA-Compliant Labeling Tools
When selecting a labeling tool, start by securing a signed Business Associate Agreement (BAA) from the vendor. This agreement clearly outlines their responsibilities for protecting PHI. If a vendor refuses to provide a BAA, it’s a red flag - move on to another provider.
The tool itself should meet several key criteria:
- Encryption: Use AES-256 encryption to secure data.
- Access Controls: Ensure role-based access and multi-factor authentication.
- Audit Logs: Continuous logging to track all activities.
- Secure Hosting: Options like Virtual Private Cloud or on-premises hosting.
- De-identification Features: Automated tools that mask or remove the 18 identifiers defined under HIPAA’s Safe Harbor method before data reaches human annotators.
Automated de-identification not only reduces the risk of exposure but also speeds up the labeling process. Additionally, prioritize vendors with SOC 2 Type II and ISO 27001 certifications. These certifications indicate that the vendor follows advanced security practices that align with HIPAA’s technical safeguards.
Step 5: Monitor, Audit, and Verify Vendor Compliance
Ensuring compliance isn't a one-and-done task - it’s an ongoing effort. Once your team is trained and your tools are in place, you’ll need systems that continuously monitor how data is handled and confirm that every vendor in your supply chain meets HIPAA standards.
Conduct Regular Compliance Audits
Set up a schedule for audits, such as quarterly reviews and an annual deep dive. Additionally, be ready to conduct immediate audits when triggered by events like data breaches, staff turnover, system updates, or shifts in policy. The HITECH Act’s breach notification rules make it essential to have pre-classified PHI for quick containment and reporting to regulators [7][8].
Each audit should include:
- Reviewing access logs to ensure only authorized personnel have accessed PHI.
- Verifying that data classifications match sensitivity levels, such as Restricted PHI for patient records.
- Confirming that encryption and masking are properly applied.
Leverage real-time dashboards to track PHI locations and confirm that protections are in place. This reduces manual oversight errors and ensures compliance with the HIPAA Security Rule [7][9][12].
Here’s an example: During an audit, an organization discovered that billing data (classified as Confidential PII) had been shared via unsecured email. This violated the HIPAA Privacy Rule. To address the issue, they implemented automated tagging for retroactive fixes, retrained their staff, and deployed data loss prevention (DLP) tools. These steps helped them avoid potential fines of up to $50,000 per violation [7][8][13].
Just as you review internal processes, you need to keep a close eye on vendor practices to ensure they stay aligned with HIPAA requirements.
Evaluate Vendor HIPAA Compliance
Monitoring vendor practices is a critical part of maintaining compliance. Before outsourcing tasks like data labeling, thoroughly conduct third-party risk assessments to vet each vendor’s HIPAA compliance. Check their adherence to the Security Rule by confirming they use encryption, enforce access controls, and maintain audit trails. Request SOC 2 Type II reports and ensure their staff has completed HIPAA training [9][10][11].
It’s worth noting that 25% of publicly shared files from healthcare organizations contain Personally Identifiable Information (PII) [14]. With HIPAA penalties ranging from $141 to $2,134,831 per violation and annual caps hitting $2,067,813, vendors share liability for breaches [14]. Make sure they limit PHI access to the minimum necessary, as outlined in §164.502(b) [10].
To simplify vendor assessments, tools like Censinet RiskOps™ can automate third-party risk evaluations. These platforms help you benchmark vendors against HIPAA standards and keep tabs on their PHI handling, medical device risks, and supply chain vulnerabilities.
Using Censinet RiskOps for HIPAA Compliance Management

Managing HIPAA compliance is no small task, especially when dealing with Protected Health Information (PHI). That's where Censinet RiskOps™ steps in. Designed specifically for healthcare organizations, this platform simplifies the complexities of cybersecurity and risk management. By automating tasks like PHI protection, vendor assessments, and team coordination, it keeps your organization audit-ready while reducing the manual workload. Once you've secured and labeled PHI as outlined earlier, RiskOps™ takes your compliance efforts to the next level.
Automate Risk Assessments with Censinet RiskOps™
Censinet RiskOps™ uses advanced AI tools to automatically identify, tag, and prioritize PHI across all your systems. Whether it's electronic health records, billing databases, or cloud storage, the platform ensures timely encryption, access restrictions, and breach notifications.
The real-time dashboards provide a clear view of PHI locations and their protection status. In the event of a breach, this pre-classified data allows for quick isolation and reporting, cutting down response times and potentially reducing penalties that can run into millions under HIPAA. For instance, in a hospital, RiskOps™ can scan lab results and patient records, flag high-risk PHI for AES-256 encryption, and enforce role-based access controls - all without requiring manual input.
Improve Team Collaboration and Governance
RiskOps™ doesn’t just handle automation; it also streamlines team collaboration. By centralizing compliance efforts on a shared governance dashboard, it ensures that IT, compliance, and clinical teams stay in sync. From tracking PHI labeling tasks to reviewing access logs and updating policies, everything can be managed from one cohesive platform, eliminating the inefficiencies of scattered communications.
The platform also sends automatic notifications to stakeholders when issues arise. For example, if billing data is improperly labeled, the system alerts the appropriate team members to resolve the issue quickly, keeping your compliance efforts on track.
Assess Vendor HIPAA Compliance
Healthcare organizations bear the responsibility of ensuring their vendors meet HIPAA standards, and RiskOps™ simplifies this process with automated vendor risk assessments. It flags vendors with insufficient safeguards - such as missing data masking or weak access controls - so you can address potential vulnerabilities before they lead to breaches.
With HIPAA penalties ranging from $141 to $2,134,831 per violation and annual caps up to $2,067,813 [14], staying ahead of non-compliance is critical. Regular scans and compliance checks through RiskOps™ ensure your vendor relationships remain secure and aligned with HIPAA requirements, all without the hassle of manual paperwork.
Conclusion
Protecting patient privacy under HIPAA requires an ongoing commitment. By adhering to the five key steps - identifying and classifying PHI, using anonymization techniques, enforcing access controls and encryption, training your staff, and monitoring compliance - you can create a strong safeguard against breaches. This is especially critical when penalties can reach up to $2,134,831 per violation[14].
The risks of non-compliance are steep. With 89% of audited entities failing HIPAA Right of Access compliance and 25% of publicly shared healthcare files containing PII[14], the stakes are high. These rules aren't just about avoiding fines - they represent a moral responsibility to protect the trust patients place in you with their sensitive information.
As data volumes continue to grow, managing compliance manually becomes increasingly unrealistic. This is where tools like Censinet RiskOps™ prove essential. By automating risk assessments, facilitating team collaboration, and continuously tracking vendor compliance, such platforms help your organization stay prepared for audits without adding unnecessary administrative work.
However, automation should complement - not replace - human oversight. A strong compliance strategy combines efficient tools with regular audits, continuous staff training, and partnerships with vendors who sign Business Associate Agreements (BAAs). By integrating these practices, you can ensure your HIPAA data labeling efforts remain effective and responsive to evolving challenges.
FAQs
What’s the fastest way to find PHI across all my systems?
The quickest way to find PHI (Protected Health Information) within your systems is by leveraging automated data classification tools, such as those integrated into Censinet RiskOps™. These tools rely on AI and machine learning to pinpoint and tag sensitive healthcare data - like patient names or medical records - in real time. With dynamic classification methods, safeguards are applied automatically as data is created or accessed, helping you maintain HIPAA compliance effortlessly.
When should I use de-identification vs data masking for labeling?
De-identification techniques like Safe Harbor or Expert Determination are essential for sharing data in a HIPAA-compliant way. These methods strip away identifiable information, ensuring privacy while maintaining the data's usefulness for research or analysis. The goal? Prevent re-identification while still allowing the data to serve its purpose.
On the other hand, data masking temporarily obscures specific data elements. This approach is perfect for scenarios like testing or development, where the data might need to be re-identified later. It’s a practical solution for internal use cases where full de-identification isn't necessary.
What should I require from a labeling vendor to stay HIPAA-compliant?
To ensure compliance with HIPAA when selecting a labeling vendor, make sure they meet these critical requirements:
- Business Associate Agreement (BAA): This contract should clearly define their obligations to protect Protected Health Information (PHI).
- Strong security protocols: Look for vendors that use encryption for both data at rest and data in transit.
- Continuous compliance checks: These can include maintaining access logs and conducting regular risk assessments.
- Clear data handling policies: Their policies should align with HIPAA's standards and be well-documented.
- Thorough vendor risk evaluations: Assess their security measures and track record to ensure they meet compliance requirements.


