Top 7 Cybersecurity Metrics for FDA Compliance
Post Summary
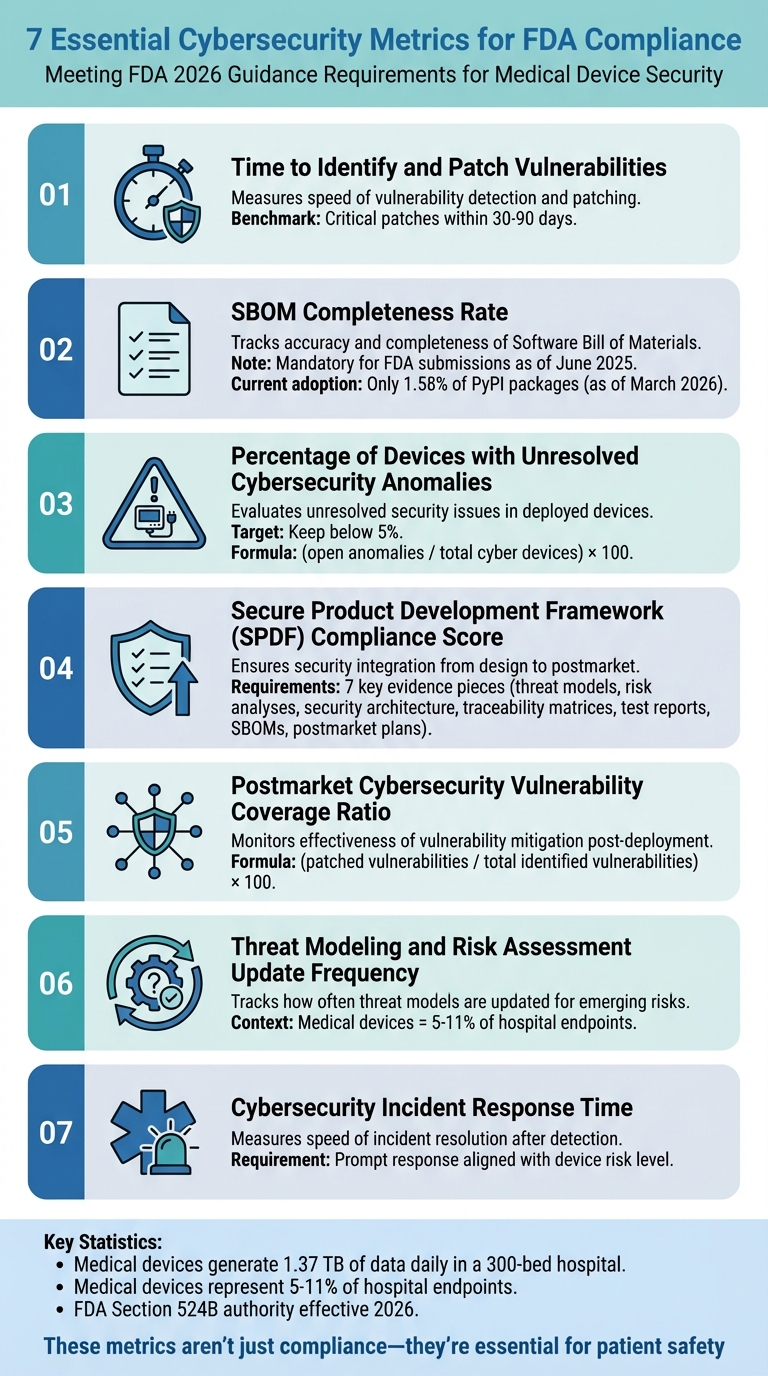
Cybersecurity is now a critical part of FDA compliance for medical devices. The FDA's 2026 guidance mandates measurable metrics to ensure device safety and security throughout their lifecycle. Medical device manufacturers and healthcare organizations must focus on seven key metrics to meet these requirements and protect patient safety:
- Time to Identify and Patch Vulnerabilities: Measures how quickly vulnerabilities are detected and patched.
- Software Bill of Materials (SBOM) Completeness Rate: Tracks the accuracy and completeness of SBOMs, now mandatory for FDA submissions.
- Percentage of Devices with Unresolved Cybersecurity Anomalies: Evaluates unresolved security issues in devices.
- Secure Product Development Framework (SPDF) Compliance Score: Ensures security is integrated from design to postmarket.
- Postmarket Cybersecurity Vulnerability Coverage Ratio: Monitors how effectively identified vulnerabilities are mitigated post-deployment.
- Threat Modeling and Risk Assessment Update Frequency: Tracks how often threat models are updated to address emerging risks.
- Cybersecurity Incident Response Time: Measures how quickly incidents are resolved after detection.
Failing to meet these metrics risks regulatory delays, device recalls, and patient safety issues. Automation tools, like Censinet RiskOps™, simplify tracking and reporting for organizations managing complex device ecosystems.
Key takeaway: These metrics aren't just about compliance - they are essential for maintaining secure, functional medical devices in a rapidly evolving threat landscape.
7 Essential FDA Cybersecurity Compliance Metrics for Medical Devices
1. Time to Identify and Patch Vulnerabilities
Relevance to FDA Compliance Requirements
The FDA's 2026 guidance brings cybersecurity into focus by integrating it into the Quality Management System Regulation (QMSR) and ISO 13485 standards. Specifically, Section 524B requires organizations to have a clear vulnerability monitoring and response plan, complete with documented timelines for identifying, assessing, and patching vulnerabilities. These timelines are critical for avoiding delays in regulatory submissions. This metric evaluates how swiftly an organization can move from detecting a vulnerability to resolving it, aligning with the FDA's Total Product Lifecycle (TPLC) approach. The TPLC framework weaves vulnerability management into risk management, design validation, and postmarket surveillance. Beyond meeting compliance requirements, this process is vital for ensuring patient safety, as detailed below.
Impact on Patient Safety and Data Security
Timely patching is essential for protecting both patient care and sensitive data. Medical devices represent 5–11% of hospital endpoints [2], and delays in addressing vulnerabilities can leave systems exposed. Unpatched devices can become targets for unauthorized access, potentially compromising their functionality and the accuracy of treatments. FDA recalls of insulin pumps and pacemakers have shown how unpatched vulnerabilities can lead to remote hacks that disrupt dosing or heart rhythms. In a 300-bed hospital generating 1.37 terabytes of daily data from connected devices [2], these vulnerabilities pose a significant risk to clinical operations and the security of protected health information (PHI). Quick resolution of vulnerabilities is key to preventing exploits, safeguarding data, and maintaining system reliability.
Ease of Tracking and Reporting for Healthcare Organizations
Tracking this metric is straightforward with the help of automated QMSR tools. Automated scanners and integrated quality management software can calculate the mean time to patch (MTTP). While the FDA doesn't specify exact benchmarks, industry experts suggest applying critical patches within 30–90 days. Additionally, strategies like network segmentation and configuration controls can help contain vulnerabilities during the patching process, reducing the risk of widespread security incidents. These tools and practices make it easier for healthcare organizations to stay compliant while enhancing their overall security posture.
sbb-itb-535baee
2. Software Bill of Materials (SBOM) Completeness Rate
Relevance to FDA Compliance Requirements
The FDA, under Section 524B of the FD&C Act, now has the authority to reject premarket submissions - like 510(k) and PMA applications - if they don't include an adequate SBOM [6]. On June 27, 2025, the FDA issued updated guidance titled "Cybersecurity in Medical Devices: Quality System Considerations and Content of Premarket Submissions," which made SBOMs a required part of these submissions [6].
"The FDA's June 2025 cybersecurity guidance makes it clear: SBOMs are no longer optional for medical device manufacturers. They're a critical component of premarket submissions and ongoing compliance." – Viktor Petersson, CEO, sbomify [6]
The FDA's emphasis on real-time risk management highlights the importance of maintaining an updated SBOM throughout a product’s lifecycle. A complete SBOM must account for all software components within a device, regardless of type. It should adhere to the NTIA Minimum Elements, which include details like supplier name, component name, version, unique identifier (e.g., purl or CPE), dependency relationships, author, and timestamps. These records should be dynamic, reflecting any software changes or patches over the product's lifespan [6]. This approach not only simplifies the submission process but also strengthens the foundation for better risk management.
Impact on Patient Safety and Data Security
SBOM completeness plays a critical role in postmarket cybersecurity, especially since medical devices often remain in use for 10 to 15 years [6]. A well-maintained SBOM allows manufacturers and healthcare providers to track vulnerabilities (CVEs) discovered long after a device has been deployed. This capability is essential for conducting rapid impact assessments during security incidents. Without a thorough SBOM, organizations may struggle to identify and address risks tied to third-party or transitive dependencies, which could jeopardize both patient safety and data security.
Ease of Tracking and Reporting for Healthcare Organizations
Despite its importance, SBOM adoption remains low. As of March 12, 2026, only 1.58% of PyPI packages included an SBOM [6]. However, automation is making it easier to track SBOM completeness. Many organizations now integrate SBOM generation directly into CI/CD pipelines, ensuring that documentation is accurate, reproducible, and tied to specific software builds [6].
"Manual SBOM generation is not sustainable for medical device compliance. Every software build should automatically generate an SBOM." – Viktor Petersson, CEO, sbomify [6]
Creating a dedicated Trust Center can further streamline compliance by providing controlled access to both current and historical SBOMs for FDA reviewers and internal stakeholders. Additionally, going beyond the NTIA minimum standards by including lifecycle metadata - such as support levels and end-of-life dates for each component - can further enhance compliance efforts [6]. This metric lays the groundwork for broader compliance strategies, setting the stage for metrics that refine cybersecurity oversight even further.
3. Percentage of Devices with Unresolved Cybersecurity Anomalies
Relevance to FDA Compliance Requirements
The FDA's 2026 guidance emphasizes the need for manufacturers to document assessments of unresolved cybersecurity anomalies in premarket submissions for cyber devices, as outlined in Section 524B of the FD&C Act [3][4]. Cyber devices - those equipped with validated software, internet connectivity, or other features that make them susceptible to cybersecurity threats - must undergo thorough evaluations of any detected anomalies to determine potential risks to patients [4]. This metric plays a critical role in aligning with FDA compliance by linking premarket documentation of anomalies to essential postmarket security practices. If manufacturers fail to justify why certain residual risks remain unresolved, high percentages of anomalies could trigger FDA scrutiny [1]. The FDA now treats cybersecurity as a core software quality issue, directly tied to patient safety. This shift moves the focus away from purely functional performance to addressing unauthorized or unintended device behaviors [2]. By connecting premarket assessments with ongoing postmarket vigilance, this metric underscores the importance of proactive and transparent reporting.
Impact on Patient Safety and Data Security
Research shows that even a small number of unresolved anomalies in environments with significant data flow can pose serious risks to patient safety. These unresolved issues can open the door to vulnerabilities such as unauthorized access, data manipulation, or interruptions in monitoring - each of which can compromise patient care. For instance, anomalies might prevent access to critical data during life-saving treatments or pave the way for ransomware attacks, like the one experienced by Change Healthcare in 2023 [2][5].
Ease of Tracking and Reporting for Healthcare Organizations
To calculate this metric, use the formula: (open anomalies / total cyber devices) x 100. Data sources may include network monitoring tools, vulnerability scans, and patch logs [1][4]. The target benchmark is to keep this percentage below 5%. Tools like automated dashboards, combined with device classification and network segmentation, can help organizations stay well under this threshold [1][2]. For older devices that cannot receive updates, additional segmentation strategies may be necessary [1]. Accurately tracking unresolved anomalies is not just about meeting FDA requirements - it also strengthens continuous risk management efforts.
4. Secure Product Development Framework (SPDF) Compliance Score
Relevance to FDA Compliance Requirements
The SPDF ensures cybersecurity is embedded throughout the entire lifecycle of a medical device. The FDA no longer accepts security measures slapped on at the last minute. Instead, they require security to be integrated from the very beginning - starting with the initial concept and continuing through postmarket maintenance [7]. The FDA's 2023 and 2025 Premarket Cybersecurity Guidance highlights the SPDF as a core requirement for all "cyber devices", which includes any product featuring software with network connectivity [7].
To meet these guidelines, manufacturers must provide seven key pieces of evidence: threat models, risk analyses, security architecture documentation, traceability matrices, test reports, SBOMs (Software Bill of Materials) with vulnerability management, and post-market plans [8]. These requirements ensure that security isn't just an afterthought but a deliberate and well-documented process.
"SPDF embeds secure practices throughout the product lifecycle." - Elton Cyber [7]
This structured approach doesn't just meet compliance standards - it also lays the groundwork for improving patient safety, as explored below.
Impact on Patient Safety and Data Security
By tying cybersecurity directly to patient safety, the SPDF emphasizes proactive measures like threat modeling and exploitability analysis. This helps prevent scenarios where a single compromised device could jeopardize an entire hospital network [8]. Using frameworks like STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege), manufacturers can identify where sensitive data crosses trust boundaries - such as when a device connects to hospital Wi-Fi - and address vulnerabilities before deployment.
The framework also promotes "secure by design" principles, requiring manufacturers to implement safeguards like network segmentation and device-level firewalls. These measures are carefully documented and rigorously tested. Additionally, tools like CVSS (Common Vulnerability Scoring System) and ISO 14971 guide exploitability analyses, helping to prioritize fixes for the most critical threats.
This proactive approach ensures that risks are managed effectively, with a clear focus on protecting both patients and their data through real-time portfolio risk management.
Ease of Tracking and Reporting for Healthcare Organizations
SPDF compliance hinges on maintaining a "traceability thread" that connects every identified security risk to its corresponding control, implementation code, and verification test [8]. Tools like Jira can be integrated into the development process to make documentation seamless and ongoing, rather than a last-minute burden.
"The goal isn't to add a mountain of extra tasks at the end of a project, but to make security an integral part of every development stage, just like unit testing or code reviews." - Henry Anfang, Firmware Developer, Punch Through [8]
Creating a centralized Security Control Catalog with unique, testable identifiers linked to source code enhances transparency and accountability. For SBOM management, tools like Syft can be integrated into CI/CD pipelines, turning static records into dynamic documents that alert teams to emerging vulnerabilities. Additionally, using VEX (Vulnerability Exploitability eXchange) documentation helps filter out irrelevant alerts, such as unused library functions, so teams can focus on real risks.
FDA Cybersecurity for Medical Devices
5. Postmarket Cybersecurity Vulnerability Coverage Ratio
Building on premarket and development security measures, keeping track of postmarket vulnerability remediation is key to staying compliant with FDA regulations.
Relevance to FDA Compliance Requirements
The Postmarket Cybersecurity Vulnerability Coverage Ratio measures how many identified cybersecurity vulnerabilities in deployed medical devices are addressed through patches, updates, or other mitigations. Similar to metrics like time-to-patch and unresolved anomalies, this ratio ensures cybersecurity efforts continue well beyond the premarket submission phase. It aligns with Section 524B of FDA requirements, which calls for manufacturers to manage risks in internet-connected devices by continuously monitoring vulnerabilities and documenting their remediation efforts [2].
The FDA’s February 2026 guidance emphasizes ongoing surveillance. This includes regular vulnerability assessments, timely patching, and thorough documentation of supply chain risks. Premarket submissions now need to include detailed plans for addressing vulnerabilities in deployed devices [2].
To calculate the coverage ratio, divide the number of patched or mitigated vulnerabilities by the total number of identified vulnerabilities, then multiply by 100. For instance, if a manufacturer identifies 100 vulnerabilities in a fleet of infusion pumps and remediates 80 of them within 30 days, the coverage ratio would be 80% [2]. This metric not only highlights remediation efficiency but also helps evaluate the broader impact on patient safety.
Impact on Patient Safety and Data Security
Unpatched vulnerabilities can lead to serious risks, including compromised patient care. A hacked device might have its operating settings altered or grant unauthorized access, potentially allowing attackers to move laterally or exposing sensitive patient health information (PHI). For example, in a 300-bed hospital generating roughly 1.37 terabytes of data daily - much of it from medical devices - a single exploited vulnerability could disrupt clinical workflows or lead to a data breach [2].
Isolation measures can add an extra layer of protection. Medical devices account for 5% to 11% of healthcare IT endpoints, and isolating vulnerable devices can prevent attackers from roaming freely within a hospital network [2].
Ease of Tracking and Reporting for Healthcare Organizations
Tracking this metric supports a continuous risk management approach. Automated tools for inventory management, vulnerability scanning, and Software Bill of Materials (SBOM) integration can provide real-time dashboards to monitor both patched and unresolved vulnerabilities. Reporting involves documenting unresolved anomalies and patch timelines as part of FDA submissions [2].
Phil Englert from Health-ISAC points out that many current systems need redesigning to meet FDA’s lifecycle security expectations. Medical devices are often overlooked amidst the rapid growth of IoT. However, hospitals that use segmentation to isolate vulnerabilities have successfully minimized clinical disruptions by reframing cyber risks as patient safety issues [2].
6. Threat Modeling and Risk Assessment Update Frequency
Keeping tabs on how often your organization updates its threat models is essential. This ensures your security measures evolve alongside emerging threats - a key requirement under FDA regulations.
Relevance to FDA Compliance Requirements
The FDA's Total Product Lifecycle (TPLC) framework emphasizes ongoing risk evaluation and mitigation throughout a device's entire lifecycle, from conception to end-of-life. This isn't just a one-time premarket task. FDA Section 524B specifically requires continuous risk management, and the June 27, 2025 guidance mandates documented threat monitoring and coordinated vulnerability disclosure [3][5].
Phil Englert, Director of Medical Device Security at Health-ISAC, highlights the importance of adaptability: "New devices should have the ability to stay current with emerging threats and be patched and updated" [2]. Regular updates to threat models incorporate postmarket feedback, aligning with FDA expectations and ensuring devices remain safe as new risks emerge.
Impact on Patient Safety and Data Security
Frequent updates to threat models are critical because they keep pace with the constantly shifting threat landscape. This proactive approach prevents devices from performing unauthorized actions that could compromise patient safety. As Phil Englert explains, "Cybersecurity engineering is about preventing devices from doing tasks you don't want or expect" [2]. Without regular updates, vulnerabilities can be exploited, potentially allowing unauthorized access or control. This could result in serious consequences, such as insulin pump malfunctions or other errors in therapy delivery, leading to patient harm [5].
In a hospital setting, where high volumes of data are processed, healthcare third-party risk assessments are equally vital for maintaining data security and availability. Automated vulnerability management systems can address vulnerabilities in minutes, a significant improvement over manual processes that are time-consuming and prone to gaps [9]. This efficiency is crucial, especially when medical devices account for 5% to 11% of endpoints in healthcare environments [2].
Ease of Tracking and Reporting for Healthcare Organizations
In addition to meeting regulatory requirements, tracking update frequency ensures that threat models remain effective and up-to-date. Modern security tools simplify this process by offering real-time dashboards and automated workflows. These tools integrate SBOMs (Software Bill of Materials) and threat modeling, making it easier to monitor and receive alerts about risk assessment updates [9]. Organizations can measure update frequency by monitoring the time intervals between formal risk assessment revisions and comparing them to regulatory or internal benchmarks.
7. Cybersecurity Incident Response Time
Cybersecurity Incident Response Time measures how long it takes to resolve an issue after it’s been detected. For medical devices, this isn’t just about efficiency - it’s about protecting patients and ensuring devices work as they should.
Relevance to FDA Compliance Requirements
This metric plays a central role in meeting FDA compliance standards by driving swift corrective actions. According to Section 524B and the updated February 2026 guidance, manufacturers must integrate a strong vulnerability monitoring and response plan into their device lifecycle. This builds on earlier vulnerability management requirements, ensuring incidents are resolved without delay. These plans are part of quality systems like those outlined in 21 C.F.R. Part 820 and ISO 13485:2016, helping manufacturers identify vulnerabilities, communicate updates, and take corrective actions in a structured way.
The FDA emphasizes the importance of "prompt" postmarket updates, which include coordinated vulnerability disclosures and patch management plans. Response times should align with the risk level of the device. Failing to act quickly can not only compromise patient safety but also risk regulatory approval.
Impact on Patient Safety and Data Security
Taking too long to respond to an incident can leave devices vulnerable to attacks, potentially affecting their functionality and the security of sensitive data. In a hospital, such delays could disrupt operations and interfere with patient monitoring. Strategies like network segmentation and proper configuration controls can help contain the impact of security breaches, ensuring patient safety remains a priority.
Ease of Tracking and Reporting for Healthcare Organizations
Automated tools like vulnerability scanners and SIEM systems make it easier to detect and log incidents. By linking these tools to quality system corrective action processes and maintaining clear traceability matrices, healthcare organizations can ensure accurate reporting and stay prepared for audits. Automated monitoring combined with well-defined playbooks helps contain and resolve incidents efficiently, protecting patient care and meeting FDA standards. These efforts, along with earlier metrics, create a robust compliance framework.
How Censinet RiskOps™ Supports FDA Compliance Metrics

Managing the seven cybersecurity metrics detailed earlier demands a platform capable of handling complex data from countless devices, vendors, and regulatory requirements. Censinet RiskOps™ equips healthcare organizations with the tools to efficiently track these metrics while adhering to FDA compliance standards, including Section 524B and related guidance.
The platform's automated risk assessment tools simplify the evaluation of medical device vulnerabilities and controls. Instead of relying on manual processes to track patch timelines or verify SBOM completeness, healthcare delivery organizations can centralize this data using RiskOps™. The platform also generates compliance reports that align with FDA requirements, which is a game-changer when dealing with the immense data volumes produced daily - much of it coming from medical devices [2].
On top of automation, the platform offers cybersecurity benchmarking to help organizations measure their performance against industry standards. This feature highlights gaps in Secure Product Development Framework (SPDF) compliance scores. Given that the FDA requires specific metrics - like defect density and patch implementation timelines - in premarket submissions [10], having a centralized system to track and report these figures significantly reduces the workload for clinical engineering and IT security teams.
The platform also emphasizes collaborative risk management, addressing the shared responsibility between Medical Device Manufacturers (MDMs) and Healthcare Delivery Organizations (HDOs). With medical devices accounting for 5% to 11% of hospital endpoints and IoT and operational technology making up approximately 30% [2], effective coordination between manufacturers and healthcare organizations is critical. RiskOps™ supports this by enabling real-time communication about vulnerability disclosures, patching strategies, and shared threat intelligence.
Additionally, Censinet AITM™ speeds up the risk assessment process by allowing vendors to complete security questionnaires in seconds. It automatically compiles vendor evidence, summarizes relevant documentation, and produces risk summary reports based on all assessment data. This blend of automation and human oversight helps healthcare organizations scale their risk management efforts while ensuring patient safety and regulatory compliance. By integrating these functionalities, RiskOps™ ensures that every stage of risk management aligns seamlessly with FDA cybersecurity metrics, bolstering the overall security framework necessary for compliance.
Conclusion
The seven cybersecurity metrics discussed here go beyond fulfilling regulatory requirements - they are essential for ensuring patient safety in a world where hospitals generate an average of 1.37 TB of device data daily [2]. The FDA's 2026 guidance under Section 524B emphasizes that cybersecurity is integral to the safety and effectiveness of medical devices, requiring detailed, traceable documentation from threat modeling to postmarket readiness [1]. Failing to monitor key metrics like vulnerability patching time, SBOM completeness, and incident response speed could lead to FDA submission rejections, regulatory penalties, or, worse, cyberattacks that jeopardize clinical operations and patient care [1].
Managing these metrics is no small feat. With thousands of devices in use, manually tracking vulnerabilities, anomalies, and compliance gaps becomes nearly impossible. Medical devices are a crucial part of hospital infrastructure [2], and their interconnected nature adds layers of complexity, especially when factoring in supply chain vulnerabilities, interoperability challenges, and the FDA's demand for detailed documentation in premarket submissions [1].
Censinet RiskOps™ offers a practical solution by automating the tracking of cybersecurity metrics, streamlining risk assessments, and fostering collaboration between healthcare providers and device manufacturers. The platform's benchmarking tools help pinpoint SPDF compliance issues, while Censinet AI™ speeds up vendor evaluations and evidence collection - key for managing the risks associated with interconnected devices and supply chains.
FAQs
Which FDA cybersecurity metric should we prioritize first?
When it comes to FDA cybersecurity, one metric stands out above the rest: the percentage of vulnerabilities patched. Why? Because this directly impacts how well vulnerabilities are managed, reducing risks by closing security gaps in medical devices and systems. Addressing these gaps promptly ensures a safer environment for both patients and healthcare providers.
What counts as a “complete” SBOM for FDA submissions?
A "complete" SBOM for FDA submissions is a machine-readable list of every software component in a device. This includes proprietary software, off-the-shelf solutions, and open-source components. It needs to align with FDA and NTIA standards, ensuring it provides the necessary details and format for cybersecurity measures and vulnerability tracking in premarket submissions.
How can hospitals track these metrics across thousands of devices?
Hospitals can monitor cybersecurity metrics across thousands of devices with the help of automated, centralized platforms like Censinet RiskOps™. These platforms offer real-time monitoring, automated assessments, and dashboards that deliver actionable insights into areas like vulnerabilities, threat detection, and compliance.
By automating tasks such as vulnerability scans, patch management, and incident reporting, hospitals can consistently track key metrics, including threat detection rates, response times, and the overall security posture of devices, even on a large scale.


