Cyber Disruptions: Lessons from Healthcare Leaders
Post Summary
Healthcare organizations face increasing cyber threats that disrupt operations, compromise patient safety, and lead to significant financial losses. In 2023 alone, cyberattacks impacted 550 healthcare entities and exposed data of 118 million individuals. The cost of recovering from a single attack now averages $7 million, making healthcare the most expensive industry for data breaches. Organizations can measure their resilience against cybersecurity benchmarks to identify gaps. Key takeaways include:
- Ransomware Threats: Cyberattacks like the 2024 Change Healthcare breach disrupted billions of transactions and caused financial strain across hospitals.
- Vulnerabilities: Unpatched systems, shadow IT, and lack of visibility into digital assets leave healthcare providers exposed.
- Continuity Planning: Effective plans focus on maintaining critical operations during outages, with practices like "dark day" drills and isolated interim systems.
- Case Studies: Organizations like Ardent Health Services and OhioHealth showcase the importance of quick responses, asset management, and third-party vendor risk management.
- Technology and Training: Tools like immutable backups and AI-powered risk platforms help strengthen recovery efforts, while regular staff training ensures readiness.
Cyber resilience requires preparation, detailed planning, and advanced tools to protect patient care and minimize disruptions.
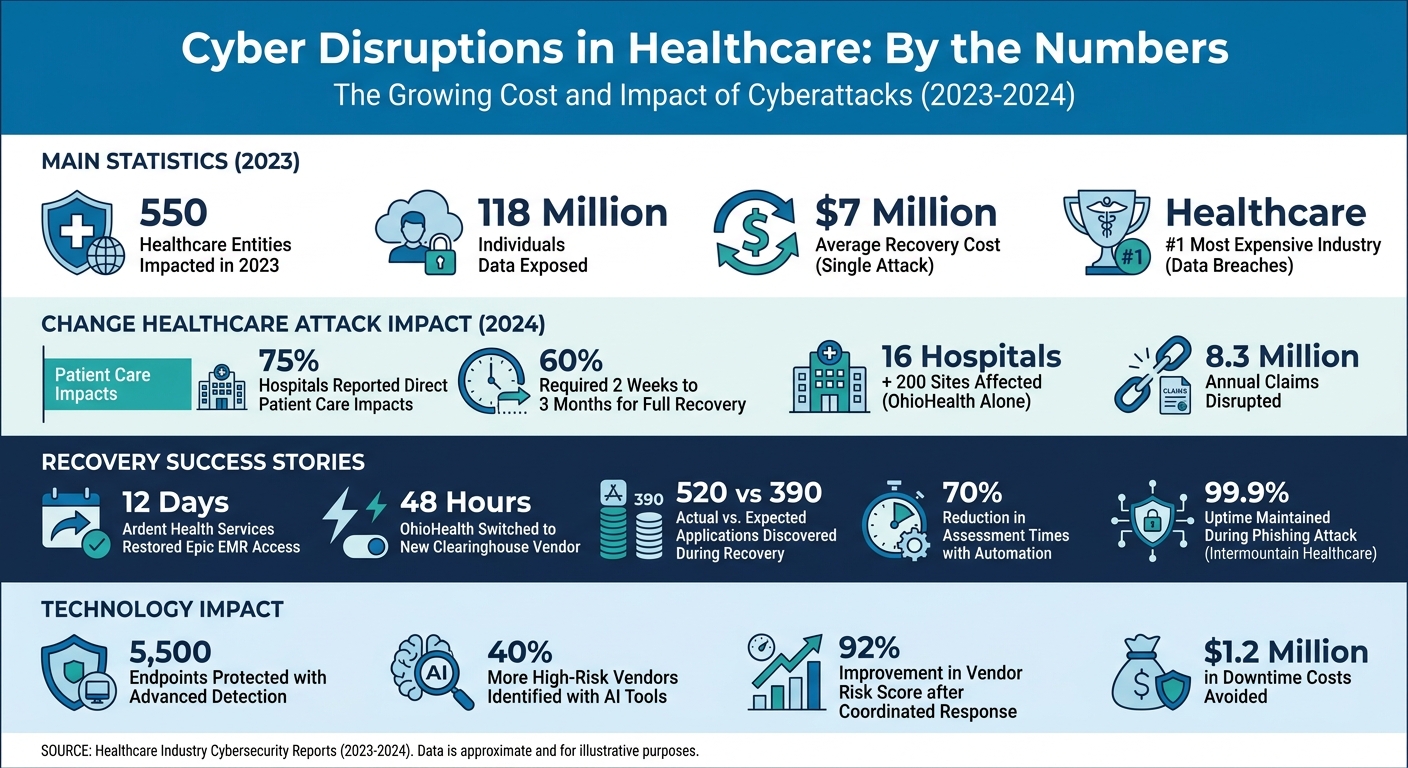
Healthcare Cybersecurity Statistics and Impact 2023-2024
After the Attack: The Critical Questions Every Hospital Must Answer
sbb-itb-535baee
Case Studies: Healthcare Organizations Responding to Cyber Incidents
These examples highlight how thorough business continuity planning can reduce the impact of cyber threats in healthcare.
Ransomware Response: A Hospital's Recovery Process
In November 2023, Ardent Health Services faced a ransomware attack that affected 30 hospitals, putting their continuity planning to the test. CTO Lonnie Garrison and CDIO Anika Gardenhire acted quickly, shutting down internet access to contain the breach [1]. This decisive step stabilized their systems and allowed the team to focus on recovery efforts.
"It allowed us to get our teams less focused on 'Are they still attacking us?' and then pivot to other containment activities." - Lonnie Garrison, CTO, Ardent Health Services [1]
During recovery, they uncovered a major issue: their asset management system was incomplete. While they expected to manage 390 applications, they found 520 active ones, making the restoration process more complex as each needed assessment and patching [1]. This highlighted how a lack of visibility into digital assets can slow recovery during a cyberattack. To address these challenges, Ardent formed clinical advisory committees to align IT and care teams, assigned IT project managers to oversee specific workgroups, and held ongoing coordination calls. These actions helped them restore access to their Epic EMR system within 12 days, ensuring clinicians could resume patient care quickly [1].
While Ardent's approach focused on responding to an attack, some organizations have shifted their focus to prevention.
Prevention First: MedSecure's Cybersecurity Overhaul
MedSecure Health Systems took a proactive stance, implementing robust security measures across their 20 hospitals to prevent incidents before they could occur. Their efforts included forming a dedicated Cybersecurity Incident Response Team (CIRT) and deploying machine learning tools to detect network anomalies in real time [4]. Additionally, they introduced biometric authentication for system access and conducted quarterly cybersecurity drills to test their readiness. Since completing these upgrades, MedSecure has reported zero successful breaches [4]. This preventive strategy contrasts with reactive approaches like those seen in OhioHealth's response to a national cyberattack.
Maintaining Operations: OhioHealth's Cyber Defense Strategy
In February 2024, the Change Healthcare cyberattack caused widespread disruptions across the healthcare industry. OhioHealth demonstrated how pre-planning and quick decision-making could minimize financial losses. VP of Revenue Cycle Girish Dighe activated their enterprise cyber risk management playbook [3]. When billing operations for 16 hospitals and 200 sites came to a halt, OhioHealth swiftly transitioned to a new clearinghouse vendor.
Within 48 hours, they shifted their entire billing process to Availity's Lifeline program, restoring automation for 8.3 million annual claims. This rapid response prevented significant cash flow issues and kept operations running smoothly [3]. OhioHealth's case shows how having a well-developed continuity plan can help healthcare organizations maintain essential functions, even during large-scale cyber disruptions.
Lessons and Best Practices for Healthcare IT Leaders
Drawing insights from real-world scenarios, healthcare IT leaders can implement practical strategies to strengthen business continuity during cyber crises. The examples provided highlight key practices that serve as effective frameworks for preparing and responding to cyber incidents.
Incident Planning and Response Preparation
Recovering from a cyber incident requires a specialized approach, distinct from traditional disaster recovery. Lee Kim, Senior Principal for Cybersecurity and Privacy at HIMSS, explains the difference:
"Traditional disaster recovery means getting back to normal from physical and environmental incidents. Cyber incident recovery means getting back to normal from cybersecurity incidents. These are intangible things that normally are not within our line of sight unless we look for them." [2]
Healthcare organizations must plan for extended downtimes, potentially lasting over 30 days, rather than just a few hours. Memorial Hermann Health System, under the leadership of CISO Randy Yates and Director Adam Lee, spent two years mapping out the resources each department would need to operate for a month without IT systems. This involved asking critical questions:
"We asked what would happen if we experienced an attack and they couldn't use certain IT systems: 'What would happen if this went away, if you couldn't print, if you couldn't scan?'" [2]
To prepare for such scenarios, organizations can schedule "Dark Days" exercises, which simulate manual workflows during peak patient care times, typically mid-week.
Maintaining an accurate asset inventory and managing third-party risk are equally critical. CTO Lonnie Garrison highlighted how delayed visibility can complicate recovery efforts. For instance, during a ransomware response, Ardent Health Services discovered they had 520 active applications instead of the 390 they had initially anticipated [1].
Using Technology to Strengthen Cybersecurity
Strategic use of advanced technology can significantly enhance recovery efforts, ensuring they are faster and more reliable.
- Immutable backups: These provide a dependable recovery option. Following a 2020 ransomware attack, the University of Vermont Health Network transitioned to Rubrik immutable backups and deployed CrowdStrike Falcon for endpoint detection and response across 5,500 endpoints. This move improved both visibility and protection [2].
- Isolated interim environments: These can ensure continuity of critical services during recovery. When the University of Vermont Health Network's Epic EHR system was offline for four weeks, the IT team created a separate, validated environment specifically for radiation oncology, allowing uninterrupted cancer care [2].
- Vendor diversification: This approach can safeguard revenue cycle operations. For example, OhioHealth quickly pivoted to Availity's Lifeline program within 48 hours during the Change Healthcare attack. This rapid shift prevented major cash flow disruptions across 16 hospitals and 200 ambulatory sites [3].
Staff Training and Organizational Preparedness
Beyond planning and technology, effective staff training plays a pivotal role in ensuring overall readiness.
Regular cross-functional simulations can uncover weaknesses that documentation alone may overlook. Memorial Hermann Health System conducts ransomware simulations involving both executive and clinical teams to test manual workflows. These exercises often reveal unexpected gaps, such as the need for sufficient paper and ink supplies during EHR outages [1][2]. Organizations can also streamline their preparedness by using AI-powered security tools to automate risk assessments and documentation.
Clear roles and consistent communication between technical and operational teams can speed up recovery efforts. For example, Ardent Health Services restored Epic access within 12 days by leveraging clinical advisory committees to coordinate 24/7 communication [1].
The stakes are high. A March 2024 survey of 1,000 hospitals found that nearly 75% experienced direct patient care impacts from the Change Healthcare attack, with 60% requiring two weeks to three months to fully recover [3]. As CISO Nate Couture aptly put it:
"Your job is to try to not get hit, to be able to take a punch if you do get hit and to stand yourself back up off the mat when you get knocked down." [2]
How Censinet RiskOps™ Supports Business Continuity in Healthcare

Censinet RiskOps™ is purpose-built to strengthen business continuity in healthcare, supporting over 200 healthcare organizations and more than 1,500 vendors within a specialized risk network [5]. This platform bolsters continuity strategies by automating risk assessments and improving incident response capabilities.
Simplifying Third-Party and Enterprise Risk Assessments
Managing vendor risks manually can slow down critical security decisions. Censinet RiskOps™ eliminates these delays by automating tasks like third-party risk assessment questions, evidence collection, and real-time risk scoring. This automation has helped healthcare organizations cut assessment times by 70%, reducing what used to take weeks to just a few days. For instance, in Q1 2024, Intermountain Healthcare completed over 500 vendor assessments in only two weeks - a process that previously required three months. Under the leadership of CISO Mark Lewis, the team identified 15 high-risk vendors and acted quickly to mitigate risks. Even during a sector-wide phishing attack, Intermountain maintained 99.9% uptime, avoided any PHI breaches, and cut compliance reporting time by 60% [5].
Censinet RiskOps™ also streamlines compliance by integrating with frameworks like NIST, HITRUST, and HIPAA. It automatically maps compliance requirements to safeguard patient data, with 85% of users reporting improved visibility into supply chain risks [5]. These time-saving and compliance tools enable faster responses to incidents, particularly when paired with advanced AI capabilities.
AI-Powered Tools for Faster Incident Response
Quick action is essential during cyber incidents, and Censinet RiskOps™ uses AI-driven tools to stay ahead of potential threats. AI-powered risk scoring and predictive analytics help detect vulnerabilities before they become major issues. Dynamic dashboards monitor risks across supply chains, medical devices, and clinical applications, allowing teams to prioritize critical areas like EHR systems.
For example, in September 2023, Cleveland Clinic identified a supply chain vulnerability in a medical device vendor using RiskOps™ AI tools. Automated alerts enabled 10 teams to coordinate fixes, cutting response time from 48 hours to just four. This swift action avoided $1.2 million in potential downtime costs and improved the vendor's risk score by 92% [5]. Additionally, Censinet AI™ speeds up risk assessments, letting vendors complete security questionnaires in seconds while summarizing evidence and generating reports. These features helped the network identify 40% more high-risk vendors in 2023 compared to traditional methods [5].
Coordinating Risk Management Across Teams
A successful response to cyber incidents requires seamless teamwork across IT, compliance, clinical, and executive departments. Censinet RiskOps™ enhances coordination with shared risk profiles, audit trails, and integrated communication tools that centralize risk management. Important findings and tasks are automatically assigned to the right stakeholders for immediate action [5].
The platform also supports preparation through tabletop exercises and scenario modeling, helping organizations simulate cyber incidents and regularly test their business continuity plans. Real-time alerts and centralized dashboards ensure all teams are aligned and ready to address emerging threats as they arise [5].
Conclusion
The experiences of Ardent Health Services, University of Vermont Health Network, and OhioHealth highlight a clear takeaway: cyber resilience in healthcare is built on preparation, not chance. Ardent's unexpected discovery of 520 applications, instead of the estimated 390, emphasized the critical importance of maintaining accurate asset inventories. As CTO Lonnie Garrison wisely remarked:
"You don't have an application inventory? No better time to start than now" [1].
By keeping up-to-date inventories, running regular "dark day" drills, and establishing clear lines of authority, organizations can recover faster and ensure patient care remains a priority.
These lessons also showcase how technology plays a central role in continuity planning. For example, during the University of Vermont Health Network’s 2020 cyberattack, the team created an isolated interim environment for radiation oncology services while 1,300 servers were offline. This demonstrated how some clinical operations rely entirely on digital systems [2]. As CISO Nate Couture aptly explained:
"Your job is to try to not get hit, to be able to take a punch if you do get hit and to stand yourself back up off the mat when you get knocked down" [2].
This required more than just technical tools - it demanded operational strategies capable of supporting 30-day continuity, far beyond the typical 24-hour downtime plans.
Proactive risk management ties these insights together into a practical framework for protecting patient care. Tools like Censinet RiskOps™ streamline risk assessments, leverage AI for threat detection, and coordinate response efforts across teams. The urgency of such measures is clear: after the Change Healthcare attack, 75% of hospitals reported impacts to patient care, with recovery times ranging from two weeks to three months [3]. Hospitals equipped with well-defined playbooks managed to maintain financial stability and operational continuity, while others faced significant challenges.
The healthcare industry operates in a constantly shifting threat environment where cyber incidents directly affect patient safety. Effective business continuity plans must prepare for long-term outages, third-party vendor risks, and the reality that manual workarounds only succeed with proper rehearsal. By combining detailed planning, advanced tools, and consistent training, healthcare leaders can turn cyber threats into manageable problems - ensuring the safety and care of the patients who rely on them.
FAQs
What should a 30-day cyber downtime plan include?
A well-structured 30-day cyber downtime plan is essential for managing system outages effectively. It should focus on immediate response, ongoing management, and recovery to minimize disruptions. Here’s what it needs to cover:
- Incident Detection and Containment: Establish clear steps for identifying and isolating cyber incidents to prevent further damage.
- Communication Protocols: Define how internal teams and stakeholders will be informed and updated throughout the downtime.
- Critical System Prioritization: Ensure patient care and other essential systems are given top priority during the recovery process.
Additionally, the plan should outline specific roles for team members, set up reliable backup procedures, and include regular testing routines to maintain preparedness. Steps for restoring systems and verifying data integrity are also crucial to ensure operations resume smoothly.
How can hospitals find and fix unknown apps and devices fast?
Hospitals can tackle the challenge of unknown apps and devices by adopting proactive monitoring and response strategies. By building a cybersecurity framework that includes continuous asset discovery, they can quickly spot unauthorized applications and devices before they become a problem.
Effective response requires having a solid incident response plan in place. This means focusing on key actions like containment and remediation, involving cross-functional teams for a coordinated approach, and leveraging centralized platforms for real-time monitoring. These steps help reduce disruptions to patient care and keep hospital operations running smoothly.
What’s the quickest way to keep billing running during a vendor outage?
When a vendor outage disrupts electronic systems, the quickest way to keep billing operations running is to switch to manual processes. This might involve using paper forms or alternative communication methods to handle tasks until the digital systems are back online. These temporary workflows can help maintain operations while reducing interruptions to essential billing activities.
Related Blog Posts
- Building Battle-Tested Resilience: ERM Lessons from Organizations That Weathered Recent Crises
- Hospitals are under siege: cyber risk now outranks every other operational threat.
- How Healthcare Organizations Lost Access to Patient Records for 15 Hours - And What Happens Next
- Disaster Recovery for Patient Data: Best Practices


