5 Steps to Integrate Cloud Incident Response
Post Summary
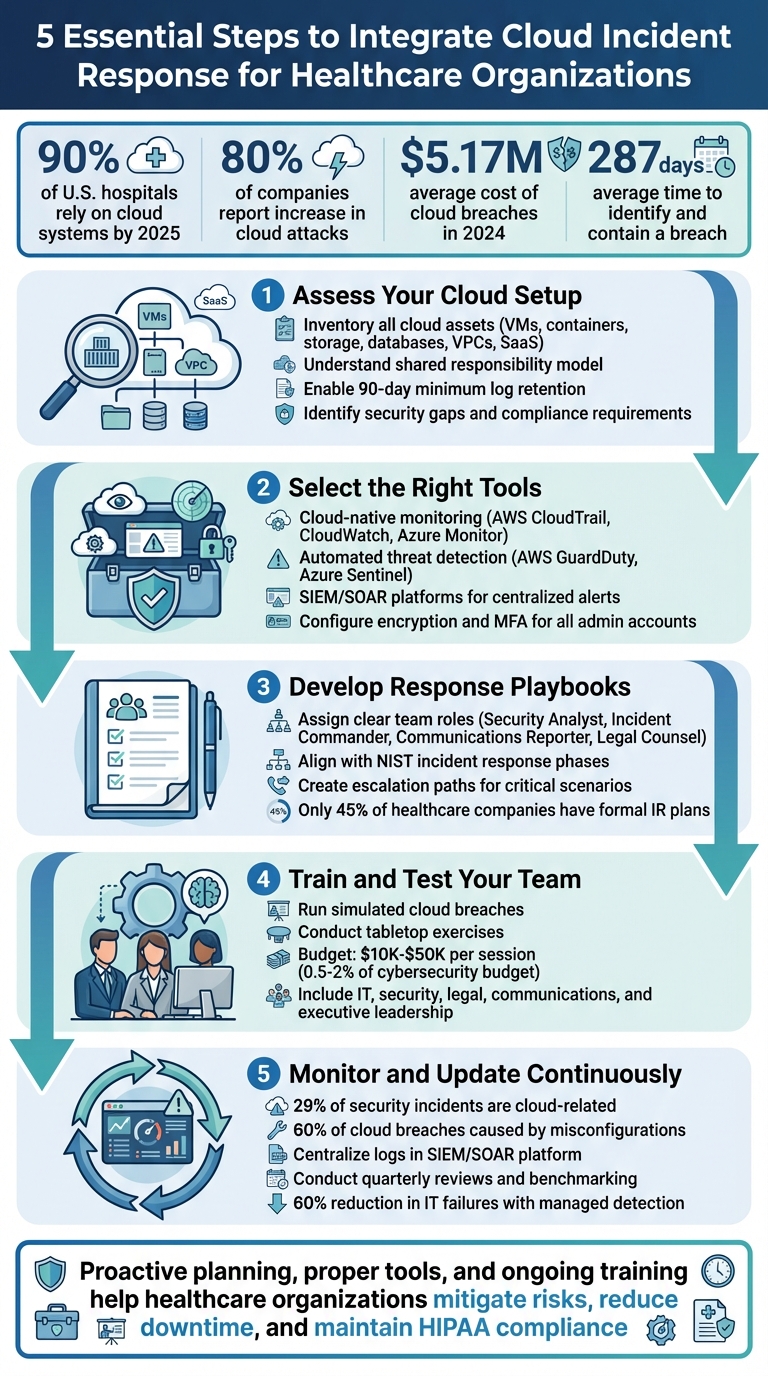
Cloud security is no longer optional for healthcare organizations. With over 90% of U.S. hospitals relying on cloud systems by 2025, safeguarding patient data and ensuring compliance with regulations like HIPAA has become critical. Cyber threats, especially in cloud environments, demand swift and effective responses to protect sensitive information and maintain operations.
Here’s a quick summary of the 5 essential steps to strengthen your cloud incident response plan:
- Assess Your Cloud vs. On-Premise Setup: Inventory all cloud assets, understand the shared responsibility model, and identify security gaps.
- Select the Right Tools: Use cloud-native tools for monitoring, logging, and automated threat detection.
- Develop Response Playbooks: Create detailed workflows, assign team roles, and align with NIST standards for compliance.
- Train and Test Your Team: Conduct breach simulations and tabletop exercises to identify weaknesses and improve readiness.
- Monitor and Update Continuously: Centralize log management, use advanced tools for configuration checks, and review policies regularly.
Key takeaway: Proactive planning, proper tools, and ongoing training can help healthcare organizations mitigate risks, reduce downtime, and maintain compliance in the face of evolving threats.
5 Steps to Integrate Cloud Incident Response in Healthcare
Incident Response in the Cloud: The Modern CISO’s Plan
sbb-itb-535baee
Step 1: Review Your Cloud Infrastructure and Risk Profile
Before anything else, you need to understand what you're safeguarding. Healthcare organizations should start by creating a detailed inventory of all cloud resources. This includes everything from virtual machines and containers to object storage, databases, virtual private clouds (VPCs), load balancers, and SaaS applications like electronic health record (EHR) systems.
It's also essential to grasp the shared responsibility model. While your cloud service provider secures the underlying infrastructure, your organization is responsible for protecting data, applications, and access controls within that environment [2]. Knowing this helps clarify which systems fall under your control and which require collaboration with your provider. Engage your vendors early to identify potential compromise indicators and refine your response plans [1]. Once roles are clear, move on to cataloging your cloud assets and vendor relationships.
Create an Inventory of Cloud Assets and Vendors
Document every cloud resource across categories like compute, storage, networking, and SaaS. For each asset, note its ownership, dependencies, and any third-party vendors involved. Identify which vendors provide specific services, what data they have access to, and how they integrate with your clinical workflows. Asset management software can help you track these relationships and keep records up to date. This detailed inventory ensures quicker, more coordinated responses during incidents - an essential aspect of cloud security in healthcare.
Find Security Gaps and Compliance Requirements
Enable comprehensive logging across your cloud environment and retain log data for a minimum of 90 days. For resources handling protected health information (PHI), enable additional logging layers. Centralize these logs and use machine learning tools to analyze and correlate alerts, which will help you detect potential incidents more quickly [2]. These steps are critical for meeting HIPAA and other regulatory standards.
Additionally, review your IT Disaster Recovery Plans, Business Continuity Plans, and Business Impact Analysis reports. Make sure they address cloud-specific risks, such as compromised storage or SaaS breaches. Include input from IT teams, emergency managers, clinical staff, and other key stakeholders to ensure these plans are well-rounded and actionable [1].
Use Censinet RiskOps™ for Third-Party Risk Assessments

Censinet RiskOps™ simplifies the process of evaluating third-party vendors. It automatically compiles evidence and documentation, captures integration details, and identifies fourth-party risk exposures. The platform generates risk summary reports based on assessment data, while its AI capabilities allow vendors to complete security questionnaires in seconds. This not only speeds up the assessment process but also ensures thorough evaluations of risks tied to patient data, PHI, clinical applications, and medical devices. By centralizing these tasks, healthcare organizations can better manage vendor relationships and maintain compliance with regulatory frameworks like HIPAA and HITRUST.
Step 2: Choose and Configure Cloud Incident Response Tools
Once you've mapped out your cloud infrastructure and vendor relationships, the next step is selecting tools that can detect and respond to threats in real time. For healthcare organizations, this is especially critical - 80% of companies have reported an increase in cloud attacks, with breaches in cloud-hosted environments averaging $5.17 million in damages in 2024 [3]. The right tools can make all the difference, helping you contain incidents in minutes rather than discovering them months down the line. This step builds on your asset inventory by focusing on tools that prioritize immediate threat detection and response.
Review Incident Response Tools and Features
Start with cloud-native logging and monitoring services like AWS CloudTrail, CloudWatch, and Azure Monitor. These tools provide essential visibility into resource access - critical for both HIPAA compliance and forensic investigations. For automated threat detection, consider tools like AWS GuardDuty or Azure Sentinel, which analyze logs to flag suspicious activities, such as unauthorized logins or unusual data transfers. To streamline your response, centralize alerts using a SIEM (Security Information and Event Management) or SOAR (Security Orchestration, Automation, and Response) platform [3].
As Cyber Defense Group explains:
"Cloud providers (AWS, Azure, GCP) secure the infrastructure of the cloud; you secure everything in it. That includes data, access controls, configurations, and applications." [3]
With your tools selected, the next step is automating threat detection and ensuring alerts are streamlined.
Set Up Automated Threat Detection and Alerts
Relying on manual investigation for cloud incidents can result in delays that cost valuable time. For example, in September 2025, AWS GuardDuty detected an "UnauthorizedAccess:IAMUser/ConsoleLogin" event. This triggered an automated response, disabling access keys and isolating affected EC2 instances. The response time dropped from hours to just minutes [4].
To maintain this level of efficiency, configure Simple Notification Service (SNS) to send instant alerts via email or SMS whenever automated actions are taken. This ensures your security operations center (SOC) stays informed [4]. Similarly, Microsoft Sentinel offers rule templates to automatically create incidents from high-severity alerts generated by Defender for Cloud, further streamlining your workflow [5].
Configure Encryption and Access Controls
Encryption and strict access controls are non-negotiable when handling patient data. Start by enforcing multi-factor authentication (MFA) for all administrative accounts. Cloud "root" accounts, in particular, should always be secured with MFA and not used for routine operations. Apply the principle of least privilege, granting users only the access they need to perform their tasks.
For databases, ensure they are accessible only from the application tier they serve, not from the broader network or internet. Centralized logs should be stored in encrypted S3 buckets with configurations that prevent accidental or malicious deletion [6]. Long-term log retention - at least one year - is crucial for forensic analysis and meeting HIPAA compliance requirements, especially since it takes organizations an average of 287 days to identify and contain a data breach [6].
Matthew Stephen from Mitiga emphasizes:
"Zero trust architecture assumes there is a breach and works to minimize the blast radius with micro-segmentation, end-to-end encryption, continuous monitoring, and automated threat detection and response." [6]
To further limit potential damage, implement micro-segmentation within your incident response tools. This approach restricts lateral movement, ensuring that even if an attacker gains access, their ability to cause harm is significantly reduced.
Step 3: Create Incident Response Playbooks and Workflows
Once you’ve set up threat detection and automated alerts, the next step is to craft detailed incident response playbooks. Surprisingly, only 45% of healthcare companies have formal incident response plans in place [7]. Without clear guidance, teams can easily become disorganized during a breach. Considering it takes an average of 277 days to identify and contain a breach [7], having clear, actionable protocols is essential. These playbooks should provide step-by-step instructions tailored to cloud-specific threats and HIPAA compliance needs, leaving no room for guesswork.
Assign Roles, Responsibilities, and Escalation Paths
Start by building a dedicated incident response team. Each member should have a clearly defined role, such as:
- Security Analyst: Investigates alerts and determines the scope of threats.
- Incident Commander: Oversees the overall response effort.
- Communications Reporter: Manages notifications and updates.
- Legal Counsel: Ensures all actions comply with HIPAA and HITECH regulations.
- Third-Party Coordinator: Handles vendor relationships and ensures external accountability [7].
Establish escalation paths for critical scenarios. For instance, if ransomware impacts systems essential to patient care, the incident commander should immediately notify the Chief Information Security Officer (CISO) and clinical leadership. Triggers for action might include automated alerts from tools like AWS GuardDuty, user-reported issues, or sudden disruptions in IT services. Differentiate between mandatory actions, like isolating compromised instances, and optional steps, such as enriching threat intelligence [7][8].
Align Playbooks with Industry Standards
HIPAA mandates that healthcare organizations maintain formal incident response policies [7]. To ensure compliance, structure your playbooks around the NIST incident response phases: preparation, detection and analysis, containment and eradication, and recovery. These should also account for the shared responsibility model - while your cloud provider secures the infrastructure, you’re in charge of data, access controls, and applications [8].
For the containment phase, include cloud-specific actions like revoking compromised API keys, isolating affected resources (e.g., auto-scaling EC2 instances), and analyzing logs from tools such as CloudTrail or Azure Monitor. Pre-approved templates for press releases, customer notifications, and regulatory reports can help you meet HIPAA/HITECH reporting deadlines [7][8]. Focus on addressing threats that could compromise patient care, expose Protected Health Information (PHI), or involve ransomware, as these are the most critical risks to mitigate.
Use Censinet Connect™ for Vendor Collaboration
Many cloud incidents involve third-party vendors responsible for parts of your infrastructure or applications. Censinet Connect™ simplifies vendor collaboration by providing predefined communication channels. This tool allows you to share playbooks, assign responsibilities, and track remediation efforts in real time. By integrating Censinet Connect™ with your third-party vendor risk management strategy from Step 1, you can ensure a coordinated response. For example, if a vendor’s security lapse triggers an incident, your third-party coordinator can immediately engage the vendor through Connect™, ensuring faster resolutions and clearer accountability.
Step 4: Test and Train Your Incident Response Team
Testing your response plans with simulated scenarios ensures your team is prepared to handle real crises. Tabletop exercises and simulated breaches help uncover weaknesses in your processes before they result in serious consequences. Many organizations dedicate 0.5–2% of their annual cybersecurity budgets to these exercises, with mid-sized healthcare organizations spending between $10,000 and $50,000 per session [9]. These costs typically cover facilitator fees, scenario creation, and the materials needed for realistic practice sessions. Once your playbooks are ready, the next step is ensuring your team can execute them effectively under pressure.
Run Simulated Cloud Breaches and Tabletop Exercises
Simulations are a practical way to test your incident response strategies in a controlled setting. Design scenarios that mimic the specific cloud threats your organization might face. For example, you could simulate ransomware attacks targeting patient records stored in AWS S3 buckets or evaluate your team's response to a vendor's compromised API key exposing sensitive data through Azure services. Include participants from IT, security, legal, communications, and executive leadership to ensure all areas of response are thoroughly tested [9].
To make these exercises realistic, use actual organizational details. Add challenges like the unavailability of key personnel or intense media scrutiny to replicate real-world conditions [9]. These scenarios force teams to answer critical questions such as: How should this incident be classified? What immediate steps should be taken to contain the threat? What evidence needs to be preserved for compliance purposes?
Review and Improve Response Processes
Evaluate the success of your exercises by looking at how accurately incidents are identified, how quickly the team responds, the clarity of communication, and the quality of decision-making [9]. Document any issues, such as trouble accessing cloud logs, unclear escalation procedures, or delays in revoking compromised credentials.
After the exercise, hold a detailed debriefing session to discuss what went well and where improvements are needed. Turn these insights into actionable updates for your response processes. For remote teams, use collaboration tools to keep everyone engaged and ensure effective participation throughout the exercise [9].
Use Censinet RiskOps™ for Risk Visualization
Technology can take your training to the next level by offering clear visualizations of risks. During simulations, platforms like Censinet RiskOps™ act as a command center, highlighting vulnerabilities across your cloud infrastructure and third-party vendors. Its risk dashboard consolidates real-time data to show how a simulated breach might impact interconnected systems. For instance, if a vendor is compromised, the platform can reveal affected clinical applications, devices, and data repositories, helping your team make quicker, more informed decisions. This visualization capability is invaluable during both practice scenarios and real incidents, providing a clearer picture of potential cascading effects.
Step 5: Monitor, Update, and Expand Incident Response Efforts
Once your playbooks are tested and your team is well-trained, the next step is to continuously monitor and refine your incident response strategies. Cyber threats are always changing, and the numbers don't lie: nearly 29% of security incident response cases are cloud-related, with over 60% of cloud breaches caused by misconfigurations [11]. These stats underline the importance of staying vigilant and keeping your defenses up to date.
Set Up Continuous Monitoring and Policy Updates
The backbone of effective monitoring is centralized log management. Bring together logs from all your cloud providers - AWS CloudTrail, Azure Activity Logs, Google Cloud Audit Logs - into a unified SIEM or SOAR platform. This gives your team a complete view of your cloud environment, making it easier to detect anomalies early [11][12].
To stay ahead, monitor three critical layers:
- Application layer: Keep an eye on performance metrics and errors.
- Infrastructure layer: Track computing and storage resources.
- Network layer: Analyze firewall rules and traffic metadata.
This layered approach reduces the chances of threats slipping through undetected [10].
Leverage tools designed for cloud environments, like Cloud Security Posture Management (CSPM) for real-time configuration checks and Cloud Workload Protection Platforms (CWPP) to secure containers and VMs during runtime [11]. Automated runbooks can also help by immediately isolating compromised instances, revoking API keys, or blocking malicious IPs [10][11].
"Continuous monitoring isn't about 'set and forget.' Expect and plan for an ongoing, iterative adoption process extending through the entire product lifecycle." - Arfan Sharif, Product Marketing Lead, CrowdStrike [10]
Focus your efforts on critical systems instead of spreading resources too thin. Use historical logs to establish benchmarks for performance and user behavior. This makes it easier to spot unusual activities, like brute force attempts or unexpected data exfiltration [10].
Once your monitoring system is running, regular reviews are crucial to keep everything up to date.
Conduct Quarterly Reviews and Benchmarking
Set aside time each quarter to review key metrics like Mean Time to Respond (MTTR) and dwell time. Update your detection rules and policies based on the latest threat intelligence and lessons learned from recent incidents [11][12]. Companies using managed detection and response have reported up to a 60% drop in IT failures within just four months [13].
Speed is critical, especially since about 20% of cloud incidents involve data exfiltration in under an hour [11]. Your policies need to reflect this reality. Comparing your performance to industry standards can also help identify where you're excelling and where there's room for improvement.
As your cloud infrastructure grows, managing risks becomes more complex. That’s where advanced tools can make a difference.
Use Censinet AI for Scalable Risk Management
When manual risk management becomes overwhelming, tools like Censinet AI can help. Designed with healthcare-specific challenges in mind - such as managing patient data, PHI, clinical applications, and medical devices - Censinet AI uses human-in-the-loop automation to scale risk management without sacrificing oversight.
The platform simplifies risk assessments by automatically summarizing vendor evidence, capturing integration details, and generating risk reports. Risk teams remain in control with customizable rules and review processes, ensuring automation supports decision-making rather than replacing it.
The AI-powered risk dashboard aggregates real-time data and directs key findings to the right stakeholders. This ensures that risks are addressed quickly while maintaining accountability and visibility across the organization.
Conclusion
Integrating cloud incident response into healthcare operations is essential for protecting patient data and maintaining operational stability. With cyber threats constantly evolving in cloud environments, having a solid incident response plan is more important than ever. The five-step process - evaluating your cloud infrastructure, setting up effective tools, creating actionable playbooks, training your team, and committing to continuous monitoring - offers a structured approach to tackling these challenges.
Preparation is the key to avoiding chaos during an incident. A well-organized response strategy ensures that logs are retained for 90 days, centralized with AI tools for compliance, and ready for efficient post-incident analysis. This setup aligns with HIPAA, NIST, and CISA standards, allowing for faster triage and timely notifications [1][2].
Platforms like Censinet RiskOps™ simplify third-party risk assessments and provide clear visualizations of potential threats while keeping your team in control. Its human-in-the-loop design ensures that automation supports decision-making without removing the critical oversight needed in healthcare. This balance is vital for organizations managing a mix of vendors, medical devices, and protected health information (PHI) within cloud systems.
Following the core phases of incident response - Preparation, Identification, Containment, Eradication, Recovery, and Lessons Learned - highlights the importance of post-incident reviews for continuous improvement [14]. As threats evolve and infrastructure changes, regular reviews, updated playbooks, and ongoing training help keep defenses strong and teams ready to respond. These practices ensure that your cloud incident response strategy remains effective and adaptable.
FAQs
What’s the fastest way to inventory all cloud assets that touch PHI?
The fastest way to inventory cloud assets managing PHI is to start by defining the scope. This means identifying the cloud platforms, services, and data types in use, and then mapping them to compliance requirements such as HIPAA or HITRUST. Bringing together a cross-functional team - including IT, compliance, and legal experts - ensures no detail is overlooked. Tools like Censinet RiskOps™ can make this process easier by offering real-time monitoring, centralized assessments, and ongoing oversight of cloud assets and any associated vulnerabilities.
How do we decide what to automate vs. handle manually in cloud incident response?
Deciding between automation and manual handling in cloud incident response comes down to evaluating task complexity, frequency, and impact.
- Automate tasks that are repetitive, take up a lot of time, or are prone to human error. Examples include data collection, threat detection, and initial analysis.
- Handle manually tasks that rely on human judgment, require deeper analysis, or involve critical decision-making.
It's also important to factor in the shared responsibility model, your organization’s capabilities, and any relevant regulations. This ensures that automation supports the response process without taking away human oversight where it’s most needed.
What log retention is required for HIPAA and cloud forensics?
HIPAA requires that audit logs be retained for a minimum of six years. This retention period is crucial for maintaining compliance and assisting in any investigations related to Protected Health Information (PHI).
In the context of cloud forensics, these logs should capture essential details, including:
- User actions
- Timestamps
- IP addresses
- Configuration changes
It’s equally important that these logs are securely stored and designed to be tamper-proof, ensuring their integrity over time.
While HIPAA sets the six-year minimum, some state laws may demand longer retention periods. For instance, certain states require logs to be kept for up to 10 years or for specific durations when minors are involved. Always verify state-specific regulations to ensure full compliance.


