Multi-Tenancy Risks in Healthcare Cloud Systems
Post Summary
Multi-tenancy is a cloud architecture where multiple organizations share the same underlying infrastructure, and in healthcare this creates risk because weak tenant isolation, misconfigured databases, or software flaws can expose protected health information across organizational boundaries.
The four primary risks are data breaches caused by tenant isolation failures, HIPAA and HITECH compliance challenges from fragmented audit trails in shared components, performance disruptions from the noisy neighbor problem, and confusion about shared security responsibilities between cloud providers and healthcare organizations.
Healthcare organizations typically choose between the database-per-tenant model for maximum isolation, the schema-per-tenant model for a balance of security and operational simplicity, or shared schema with row-level security for the most cost-efficient option, with each model offering different trade-offs between security strength and infrastructure overhead.
Multi-tenant environments complicate HIPAA compliance because shared components such as load balancers and storage systems create fragmented audit trails that make it difficult to verify data access controls and produce the detailed logs required during regulatory reviews.
Role-based access control validated at every decision point, multi-factor authentication required at all access points, and Zero Trust frameworks that continuously verify identity, device health, and permissions for every request are the essential layered access controls for multi-tenant healthcare cloud environments.
Automated platforms such as Censinet RiskOps continuously evaluate vendor security postures, identify gaps in tenant isolation and access controls, benchmark vendor practices against industry standards, and centralize oversight of patient data, clinical applications, and medical devices to reduce manual compliance burden.
Sharing cloud infrastructure saves healthcare providers money but introduces risks to sensitive patient data. Multi-tenancy, where multiple organizations share the same cloud resources, can lead to data breaches, compliance challenges, and performance issues. For instance, breaches in such environments cost an average of $4.5 million, and regulatory fines can exceed $2 million annually. Here's what you need to know:
To mitigate these risks, healthcare organizations should focus on data isolation (e.g., database-per-tenant models), strict access controls (e.g., MFA and RBAC), clear vendor agreements, and continuous monitoring. Tools like automated risk management platforms can simplify compliance and improve security. The stakes are high, as breaches can lead to massive financial losses, operational disruptions, and damaged trust.
Cloud Security: How to Defend Healthcare Data in the Cloud
sbb-itb-535baee
Main Risks of Multi-Tenancy in Healthcare Cloud Systems
Multi-tenant healthcare cloud systems come with several risks that can jeopardize patient data, disrupt clinical workflows, and complicate compliance efforts. Understanding these risks is essential to implementing effective security measures. These challenges span operational, legal, and performance-related concerns for healthcare organizations.
Data Breaches and Tenant Isolation Failures
In a shared infrastructure, weak tenant isolation is a major vulnerability. Misconfigured databases, incorrect permissions, or software flaws can lead to patient data being exposed across tenants. The financial fallout is significant: a 2024 IBM report found that the average cost of a breach tied to multi-tenancy reached $4.5 million [1]. Even more alarming, 33% of organizations reported experiencing three or more breaches within a single year [3].
HIPAA and HITECH Compliance Challenges
Meeting regulatory requirements like HIPAA becomes more difficult in shared cloud environments. HIPAA requires safeguards for protected health information (PHI), such as encryption, detailed audit logs, and strict access controls. Multi-tenant systems complicate these safeguards because data often flows through shared components, including load balancers and storage systems. This can result in fragmented audit trails, making compliance verification harder during regulatory reviews.
Operational challenges further compound these issues, particularly when it comes to resource allocation.
Performance Issues and Resource Conflicts
The "noisy neighbor" problem is a significant concern in multi-tenant setups. When one tenant uses resource-heavy workloads - such as running large-scale analytics or performing system backups - it can consume shared resources, causing performance issues for others [2].
"Resource-heavy tenants can monopolize the system, slowing down other tenants or leading to degraded performance." - Madhumitha Karthikeyan
These bottlenecks can delay access to electronic health records (EHRs), disrupt patient monitoring systems, and interrupt clinical workflows. As more tenants join the shared infrastructure, scalability problems can worsen, resulting in inconsistent application response times [2].
Shared Responsibility Model Confusion
Balancing cost efficiency with security in multi-tenant healthcare clouds often leads to confusion about shared responsibilities. While cloud providers handle the security of the underlying infrastructure - such as servers and networks - healthcare organizations are responsible for their own data, application security, and user access controls. This division becomes especially unclear in areas like encryption key management, backups, and incident response.
Universal updates in SaaS and PaaS platforms add another layer of complexity. When updates are applied across all tenants, a single bug or issue can introduce vulnerabilities or disrupt services for every organization using the platform. As Josys [1] highlights:
"Multitenancy failures in identity and access management systems can lead to widespread service disruptions, with potential downtime averaging several hours."
Such disruptions can have severe consequences, including delays in accessing critical patient information, which could directly impact clinical care.
How Multi-Tenancy Risks Affect Healthcare Organizations
The dangers tied to multi-tenancy vulnerabilities in shared environments aren't just hypothetical - they can severely disrupt healthcare operations and damage public trust.
Healthcare Data Breach Examples
In February 2024, Change Healthcare experienced a breach that highlighted the risks of multi-tenancy. Attackers exploited a legacy Citrix remote access portal that lacked multi-factor authentication. Using low-level credentials, they gained unauthorized access [4][5]. This portal wasn’t integrated into UnitedHealth's broader security systems, leaving it exposed [5].
Once inside, the ALPHV/BlackCat group navigated the system for nine days, extracting 4 TB of sensitive data before deploying ransomware on February 21 [4][5]. The breach affected 192.7 million individuals - nearly two-thirds of the U.S. population - marking it as the largest healthcare data breach in the country’s history [6].
"The attack became the largest healthcare breach in US history, affecting over half of Americans and disrupting pharmacies, hospitals, and providers nationwide."
The fallout worsened when UnitedHealth paid a $22 million ransom in Bitcoin. However, the ransomware group misappropriated the payment, performing an exit scam. This led to another extortion attempt by a separate group, which subsequently leaked the stolen data. The situation triggered a Department of Health and Human Services investigation and consolidated multidistrict litigation involving over 49 cases [5]. These incidents underscore how breaches extend beyond data loss, creating financial and operational chaos.
Financial and Operational Consequences
UnitedHealth Group faced a staggering $2.9 billion in response costs and system rebuilding efforts [5]. Since Change Healthcare processes 15 billion transactions annually, the breach caused widespread disruptions. Approximately 94% of hospitals reported financial strain, and 74% experienced direct impacts on patient care, such as issues with insurance verification and prescription processing [5]. Smaller practices were hit hard too - 55% of medical practice owners had to dip into personal funds to cover payroll during the disruption. UnitedHealth even advanced $9 billion to healthcare providers to stabilize the industry [5][7].
These financial pressures highlight the real-world consequences of inadequate third-party vendor risk management in multi-tenant setups. Beyond the immediate costs, organizations face years of regulatory oversight, litigation, and potential penalties. For example, the 2015 Anthem breach - which affected 78.8 million individuals - resulted in a $16 million HIPAA violation penalty, the largest ever imposed by the Department of Health and Human Services [4].
How to Reduce Multi-Tenancy Risks in Healthcare Cloud Systems
Reducing the risks of multi-tenancy in healthcare cloud systems calls for a multi-layered approach. While it's impossible to eliminate these risks entirely, healthcare organizations can significantly minimize their exposure by combining technical safeguards, governance policies, and ongoing monitoring. Here’s how to create a robust framework that protects patient data while retaining the cost advantages of shared infrastructure.
Data Isolation Methods
Effective data isolation is key to limiting breaches to a single tenant. Healthcare organizations typically choose from three main architectural models, each offering different trade-offs between security and efficiency.
"Data isolation refers to the mechanisms that prevent tenants from accessing each other's resources, even though they're sharing underlying infrastructure." - John Noonan, Redis
Beyond database architecture, additional layers of isolation are critical. Application-level middleware filters, tenant-specific context mechanisms like JWT claims, and encryption at rest (using tenant-specific keys) all add extra protection. For environments with high compliance requirements, unique Key Management Service (KMS) keys for each tenant can further safeguard sensitive patient data.
Isolation should also extend to caching systems, object storage, and messaging systems. For example, use tenant-specific prefixes for stored files or tenant-scoped naming in messaging topics. These measures ensure that isolation is maintained across all layers of the system.
Access Control Implementation
Authentication alone isn’t enough to guarantee tenant isolation. Without proper safeguards, even authenticated users could inadvertently or maliciously access another tenant’s data [8]. This makes layered access controls essential.
Vendor Agreements and Monitoring Requirements
Strong vendor agreements and continuous monitoring are crucial for meeting HIPAA compliance standards. Business associate agreements (BAAs) with cloud vendors should clearly define security responsibilities, data handling protocols, and breach notification timelines. These agreements must specify the isolation methods used and how tenant separation is maintained.
Continuous monitoring is equally important. Automated systems should track access patterns, flag unusual activity, and alert security teams to potential cross-tenant access attempts. Immutable audit trails that log every data access event are vital for compliance audits and breach investigations. These logs should include details such as who accessed the data, when, and from where, with tenant context clearly identified.
Given that the average global cost of a data breach reached $4.88 million in 2024 - a 10% increase from the previous year [8] - investing in robust monitoring systems can help prevent costly incidents.
Using Automated Risk Management Platforms
Automated tools can simplify the process of assessing and managing security risks. These platforms continuously evaluate the security posture of vendors and detect vulnerabilities across the ecosystem.
For example, Censinet RiskOps™ allows healthcare organizations to conduct thorough risk assessments across their vendor network. The platform automates third-party risk evaluations, identifying vendors with strong tenant isolation, adequate access controls, and HIPAA compliance. Instead of manually reviewing questionnaires, organizations can rely on automated workflows to pinpoint risks quickly.
Censinet RiskOps™ also benchmarks vendor practices against industry standards, helping organizations identify gaps in their multi-tenancy protections. Powered by Censinet AI™, the platform accelerates risk assessments by summarizing evidence, capturing integration details, and uncovering fourth-party risk exposures.
Serving as a centralized hub, Censinet RiskOps™ provides real-time risk visualization and routes critical findings to the appropriate teams. This streamlined approach ensures that healthcare organizations maintain continuous oversight of patient data, clinical applications, medical devices, and more. By centralizing risk management, healthcare providers can address issues proactively and maintain strong governance over their cloud environments.
Comparing Data Isolation Approaches
Logical vs Physical Data Isolation in Healthcare Cloud Systems
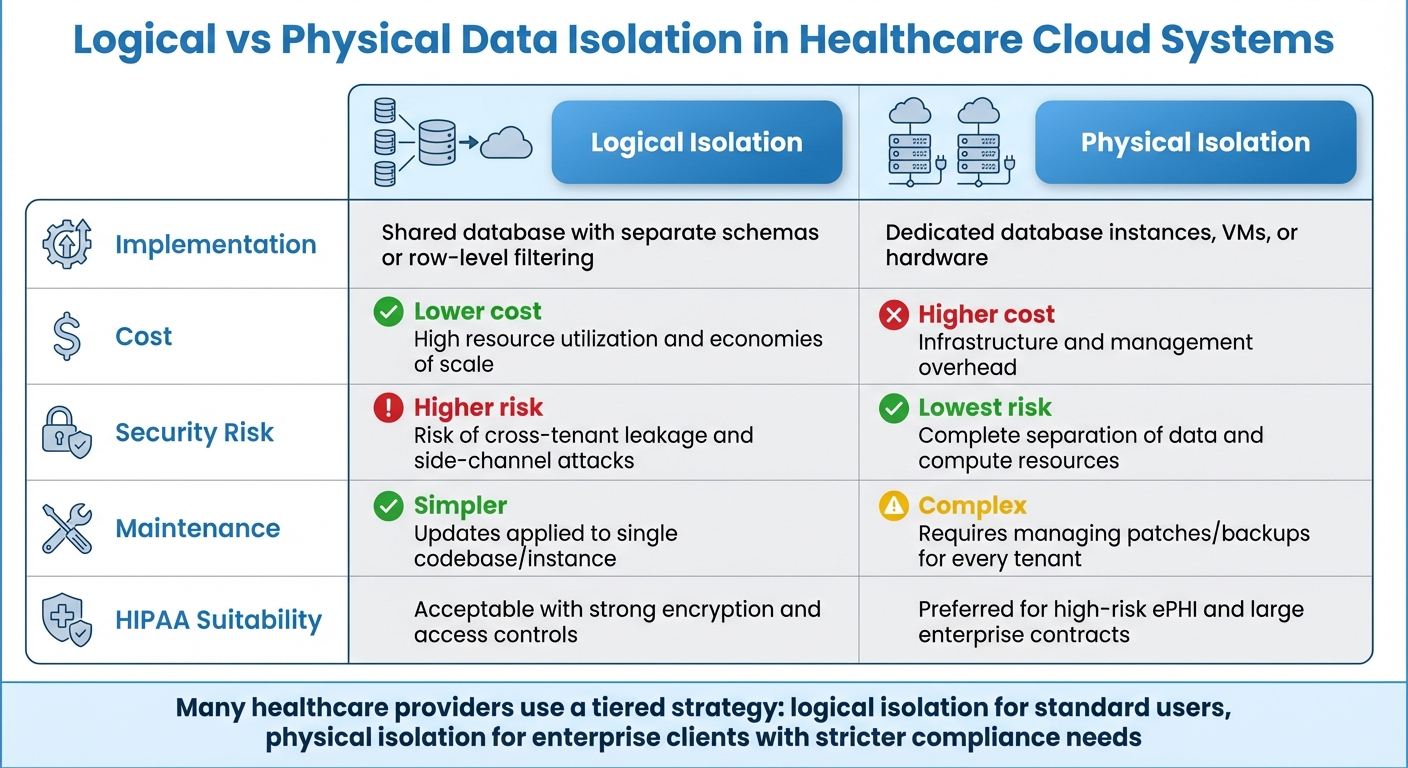
Choosing between logical and physical isolation often comes down to a balance between security needs and cost constraints. Logical isolation uses software-defined boundaries like row-level security or separate schemas within a shared infrastructure. On the other hand, physical isolation assigns dedicated resources, such as separate database instances or distinct hardware, for each tenant [10][11]. For healthcare cloud systems handling sensitive Protected Health Information (PHI), these decisions directly affect compliance and healthcare cyber risk management.
The security gap between the two approaches is notable. Logical isolation is more vulnerable to cross-tenant risks and side-channel attacks - like Meltdown and Spectre - that exploit shared memory or CPU caches [1][8]. Physical isolation mitigates these risks by ensuring complete separation of data and compute resources, offering a much stronger security posture [10][11]. This discussion builds on previous analyses of isolation methods, emphasizing the differences between shared versus dedicated hardware resources.
Cost is another key factor. Logical isolation significantly lowers expenses by enabling shared infrastructure, which maximizes resource utilization [1][8]. However, this cost-saving approach comes with higher security risks. A case in point is Microsoft Azure's "ChaosDB" vulnerability from August 2021. This breach allowed researchers to access other customers' databases in Azure Cosmos DB by exploiting a shared feature in Jupyter Notebook, highlighting the potential dangers of logical isolation [1].
Isolation Methods Comparison Table
Factor
Logical Isolation
Physical Isolation
Shared database with separate schemas or row-level filtering
Dedicated database instances, VMs, or hardware
Lower; high resource utilization and economies of scale
Higher; infrastructure and management overhead
Higher; risk of cross-tenant leakage and side-channel attacks
Lowest; complete separation of data and compute resources
Simpler; updates applied to a single codebase/instance
Complex; requires managing patches/backups for every tenant
Acceptable with strong encryption and access controls
Preferred for high-risk ePHI and large enterprise contracts
These differences are crucial for organizations navigating compliance and vendor risk management efficiency. Many healthcare providers adopt a tiered strategy: offering logical isolation for standard users while reserving physical isolation for enterprise clients with stricter compliance demands [8]. Since HIPAA §164.306(b) permits organizations to tailor security measures based on their size, complexity, and costs, documenting how the chosen model addresses specific risks is critical for regulatory justification.
Conclusion
Multi-tenant cloud systems offer a cost-efficient infrastructure for healthcare organizations, but they come with risks that require constant vigilance. Issues like tenant isolation failures, HIPAA compliance challenges, and resource conflicts can jeopardize Protected Health Information (PHI) and result in regulatory penalties. For instance, the February 2024 Change Healthcare breach [12] highlighted how insufficient security in shared environments can lead to significant data exposure and heightened scrutiny.
To address these risks, healthcare organizations should focus on strong data isolation, Role-Based Access Control (RBAC) with Multi-Factor Authentication (MFA), strict Business Associate Agreements (BAAs), and continuous monitoring [12][13]. Additionally, documenting how the chosen isolation model - whether logical, physical, or hybrid - meets HIPAA §164.306(b) compliance standards is critical. Together, these measures create a robust foundation for securing multi-tenant cloud environments.
The financial implications of non-compliance are steep. HIPAA violations can lead to fines exceeding $2 million annually, alongside criminal penalties of up to $250,000 and 10 years of imprisonment [12]. Beyond these direct costs, operational disruptions and the erosion of patient trust can far outweigh the initial savings of adopting multi-tenancy.
To strengthen these controls, active risk management is crucial. Automated platforms like Censinet RiskOps™ simplify third-party risk assessments, cybersecurity benchmarking, and collaborative risk management. By centralizing the monitoring of patient data, clinical applications, and supply chain risks, such tools help close gaps in manual processes and ensure ongoing compliance in shared cloud settings.
FAQs
How do I choose between logical and physical isolation for PHI?
Choosing the right approach between logical isolation and physical isolation for Protected Health Information (PHI) boils down to your security priorities, compliance needs, and available budget.
Your decision should align with your organization's risk tolerance and compliance requirements. Tools like Censinet RiskOps™ can help simplify this process and provide valuable insights.
What are the most common multi-tenant misconfigurations that cause cross-tenant leaks?
In healthcare cloud systems, some of the most common missteps in multi-tenant configurations can lead to cross-tenant data leaks. These include insecure API settings, poor data governance practices, insufficient segmentation between tenant environments, and weak access controls. When these vulnerabilities exist, they open the door to unauthorized access and potential exposure of sensitive information - serious risks for any organization handling protected health data.
What should a HIPAA-ready cloud BAA require for multi-tenant security and monitoring?
A HIPAA-ready cloud Business Associate Agreement (BAA) must include strict security measures to safeguard patient data. Key requirements typically involve encryption, access controls, continuous monitoring, breach notification protocols, and clearly defined responsibilities. These measures are essential for protecting sensitive information, maintaining audit logs, and ensuring compliance with HIPAA standards, even within shared or multi-tenant environments.
Related Blog Posts
- HIPAA Cloud Violations: Penalties Explained
- Ultimate Guide to Zero Trust in Healthcare Cloud
- Ultimate Guide to Data Residency in Healthcare Cloud
- Shared Responsibility Model: Vendor vs. HDO Roles
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":[{"@type":"Question","name":"How do I choose between logical and physical isolation for PHI?","acceptedAnswer":{"@type":"Answer","text":"<p>Choosing the right approach between <strong>logical isolation</strong> and <strong>physical isolation</strong> for Protected Health Information (PHI) boils down to your security priorities, compliance needs, and available budget.</p> <ul> <li><strong>Logical isolation</strong> relies on techniques like encryption, access controls, and network segmentation within a shared infrastructure. This approach is more budget-friendly and allows for easier scalability.</li> <li><strong>Physical isolation</strong>, on the other hand, uses dedicated hardware systems. While it offers a higher level of security, it comes with a steeper price tag.</li> </ul> <p>Your decision should align with your organization's risk tolerance and compliance requirements. Tools like <em>Censinet RiskOps™</em> can help simplify this process and provide valuable insights.</p>"}},{"@type":"Question","name":"What are the most common multi-tenant misconfigurations that cause cross-tenant leaks?","acceptedAnswer":{"@type":"Answer","text":"<p>In healthcare cloud systems, some of the most common missteps in multi-tenant configurations can lead to cross-tenant data leaks. These include <strong>insecure API settings</strong>, <strong>poor data governance practices</strong>, <strong>insufficient segmentation between tenant environments</strong>, and <strong>weak access controls</strong>. When these vulnerabilities exist, they open the door to unauthorized access and potential exposure of sensitive information - serious risks for any organization handling protected health data.</p>"}},{"@type":"Question","name":"What should a HIPAA-ready cloud BAA require for multi-tenant security and monitoring?","acceptedAnswer":{"@type":"Answer","text":"<p>A HIPAA-ready cloud Business Associate Agreement (BAA) must include strict security measures to safeguard patient data. Key requirements typically involve <strong>encryption</strong>, <strong>access controls</strong>, <strong>continuous monitoring</strong>, <strong>breach notification protocols</strong>, and <strong>clearly defined responsibilities</strong>. These measures are essential for protecting sensitive information, maintaining audit logs, and ensuring compliance with HIPAA standards, even within shared or multi-tenant environments.</p>"}}]}
Key Points:
What are the primary security risks of multi-tenancy in healthcare cloud systems and why do they matter?
- Tenant isolation failures are the most consequential multi-tenancy risk, occurring when misconfigured databases, incorrect permissions, or software flaws allow patient data from one organization to be accessed across tenant boundaries
- The financial exposure from multi-tenancy breaches is significant, with the average cost of a breach tied to multi-tenancy reaching $4.5 million according to IBM's 2024 research, and 33% of organizations reporting three or more breaches in a single year
- HIPAA and HITECH compliance becomes materially harder in shared environments because encryption requirements, audit log completeness, and access control verification all depend on data flowing through components that are not exclusively under a single organization's control
- The noisy neighbor problem creates clinical workflow disruption when resource-heavy tenants monopolize shared compute and storage, delaying access to electronic health records and interrupting patient monitoring systems in ways that have direct care implications
- Shared responsibility model confusion compounds all other risks because the boundary between what a cloud provider secures and what the healthcare organization must secure is unclear in areas like encryption key management, backup integrity, and incident response coordination
- The Change Healthcare breach of February 2024 illustrated the systemic consequences of multi-tenancy vulnerabilities at scale, affecting 192.7 million individuals, triggering $2.9 billion in response costs, and causing financial strain for 94% of hospitals that relied on the compromised infrastructure
What data isolation models are available for healthcare cloud environments and how should organizations choose between them?
- The database-per-tenant model provides the strongest isolation by assigning each tenant a separate database instance, ensuring that even if one tenant's data is compromised the others remain unaffected, making it particularly appropriate for large healthcare enterprises with strict compliance requirements
- The schema-per-tenant model offers a balance between security and operational simplicity, separating tenants into distinct schemas within a shared database instance and working well for mid-sized providers that need reasonable isolation without the overhead of managing numerous individual databases
- Shared schema with row-level security is the most cost-efficient option, potentially reducing infrastructure costs by up to 70%, but it provides the weakest isolation and demands flawless implementation of application logic and database policies to prevent cross-tenant data exposure
- Isolation must extend beyond the database layer to include application-level middleware filters, tenant-specific encryption at rest using tenant-specific keys, caching systems, object storage, and messaging systems to ensure protection is maintained across all infrastructure components
- HIPAA §164.306(b) permits organizations to tailor security measures based on size, complexity, and costs, which means the chosen isolation model must be documented with a clear rationale for how it addresses the organization's specific risk profile and compliance obligations
- Many healthcare providers adopt a tiered strategy, offering logical isolation for standard workloads while reserving physical isolation with dedicated hardware and database instances for enterprise clients or high-risk ePHI environments where the compliance and liability exposure justifies the additional cost
What access controls are required to prevent cross-tenant data exposure in healthcare cloud systems?
- Role-based access control must validate tenant context at every decision point', not only at login, ensuring that a clinician in one facility cannot access records belonging to a patient at another tenant organization even if both share the same application layer
bb Multi-factor authentication is non-negotiable at all access points', particularly remote access portals, because credential theft is a primary mechanism through which attackers gain initial access in multi-tenant environments and MFA materially reduces this exposure
bb Zero Trust frameworks address the specific complexity of healthcare cloud access' by continuously verifying identity, device health, and permissions for every request from every user type, whether clinicians, administrators, or third-party vendors, rather than assuming trust based on network location
bb Authentication alone is insufficient to guarantee tenant isolation', as even authenticated users can inadvertently or maliciously access another tenant's data without layered application-level controls that enforce tenant context independently of the authentication state
bb The Change Healthcare breach originated through a legacy remote access portal lacking MFA', demonstrating that a single access point without proper controls in a multi-tenant environment can serve as the entry vector for a breach affecting hundreds of millions of individuals
bb Encryption key management at the tenant level adds a critical additional layer', with unique Key Management Service keys for each tenant ensuring that even if shared infrastructure is compromised, data from individual tenants cannot be decrypted without the tenant-specific key
How does multi-tenancy complicate HIPAA compliance and what governance measures address the challenge?
- HIPAA's safeguard requirements for PHI become difficult to satisfy in shared environments because data frequently flows through shared components including load balancers, caching layers, and storage systems that span tenant boundaries and complicate the completeness of audit trails
- Business Associate Agreements with cloud vendors must specify isolation methods explicitly, including how tenant separation is maintained, what security responsibilities belong to each party, and what breach notification timelines and protocols apply to the multi-tenant environment
- Immutable audit trails that log every data access event with tenant context clearly identified are required for both HIPAA compliance verification and breach investigation, and these trails must capture who accessed what data, when, and from where in a format that cannot be altered after the fact
- Continuous monitoring systems should track access patterns, flag unusual activity, and alert security teams to potential cross-tenant access attempts in real time rather than relying on periodic manual review, which is too slow to catch active intrusions in clinical environments
- HIPAA violations in multi-tenant environments can result in fines exceeding $2 million annually alongside criminal penalties of up to $250,000 and ten years of imprisonment, making the compliance investment substantially less costly than the regulatory consequence of non-compliance
- Documenting how the chosen isolation model addresses HIPAA §164.306(b) requirements is a compliance obligation, not just a best practice, and healthcare organizations should maintain this documentation as part of their ongoing risk management program
What is the shared responsibility model in healthcare cloud environments and where does confusion most commonly arise?
- Cloud providers are responsible for securing the underlying infrastructure, including physical servers, network hardware, and the hypervisor layer, while healthcare organizations are responsible for their own data, application security, user access controls, and configuration of cloud services
- The boundary becomes especially unclear in areas like encryption key management, where both parties have capabilities and obligations but the division of responsibility is not always explicitly defined in vendor agreements, leaving gaps that attackers can exploit
- Universal SaaS and PaaS platform updates introduce risk that spans all tenants simultaneously, because a bug or vulnerability introduced through a platform update affects every organization using the shared service, meaning a single flaw can create exposure across an entire customer base
- Incident response coordination is a specific area where shared responsibility confusion creates delays, because each party may assume the other is taking the lead on detection, containment, or notification, resulting in slower response times that extend the window of exposure
- Business Associate Agreements must clearly define security responsibilities, data handling protocols, and breach notification timelines to eliminate ambiguity in the shared responsibility model and ensure that both the cloud provider and the healthcare organization know exactly what each party owns
- Healthcare organizations cannot outsource accountability for PHI security to cloud vendors, regardless of what the vendor handles at the infrastructure level, making it essential to maintain internal expertise in cloud security governance even when significant infrastructure management is delegated
How should healthcare organizations use automated risk management platforms to manage multi-tenancy risk?
- Automated risk management platforms continuously evaluate vendor security postures rather than relying on point-in-time assessments, providing ongoing visibility into whether cloud vendors maintain the tenant isolation controls and HIPAA compliance posture that healthcare organizations require
- Censinet RiskOps automates third-party risk evaluations across the vendor network, identifying vendors with strong tenant isolation, adequate access controls, and demonstrated HIPAA compliance and surfacing gaps that manual questionnaire review processes routinely miss
- Benchmarking vendor practices against industry standards allows healthcare organizations to identify where their multi-tenancy protections fall short relative to peer organizations and regulatory expectations, providing a prioritized view of remediation needs
- Censinet AI accelerates risk assessments by summarizing evidence, capturing integration details, and uncovering fourth-party risk exposures that arise when cloud vendors themselves rely on subprocessors with their own multi-tenancy configurations that could affect PHI security
- Centralized risk visualization routes critical findings to the appropriate teams in real time, eliminating the manual coordination overhead that delays remediation in organizations relying on spreadsheets or disconnected point tools to manage cloud vendor risk
- Continuous oversight through a unified platform reduces the gap between vendor risk assessment cycles, ensuring that changes in a vendor's security posture are detected and addressed before they create exploitable exposure in the healthcare organization's multi-tenant cloud environment


