NIST CSF Incident Response Plan for Healthcare
Post Summary
Healthcare organizations face constant cybersecurity threats, with ransomware and data breaches causing significant disruptions to patient care and operations. A structured incident response plan, based on the NIST Cybersecurity Framework (CSF), helps mitigate these risks and ensures faster recovery. Here's what you need to know:
- Why NIST CSF? It provides a flexible, risk-based approach to managing cybersecurity, going beyond basic HIPAA compliance.
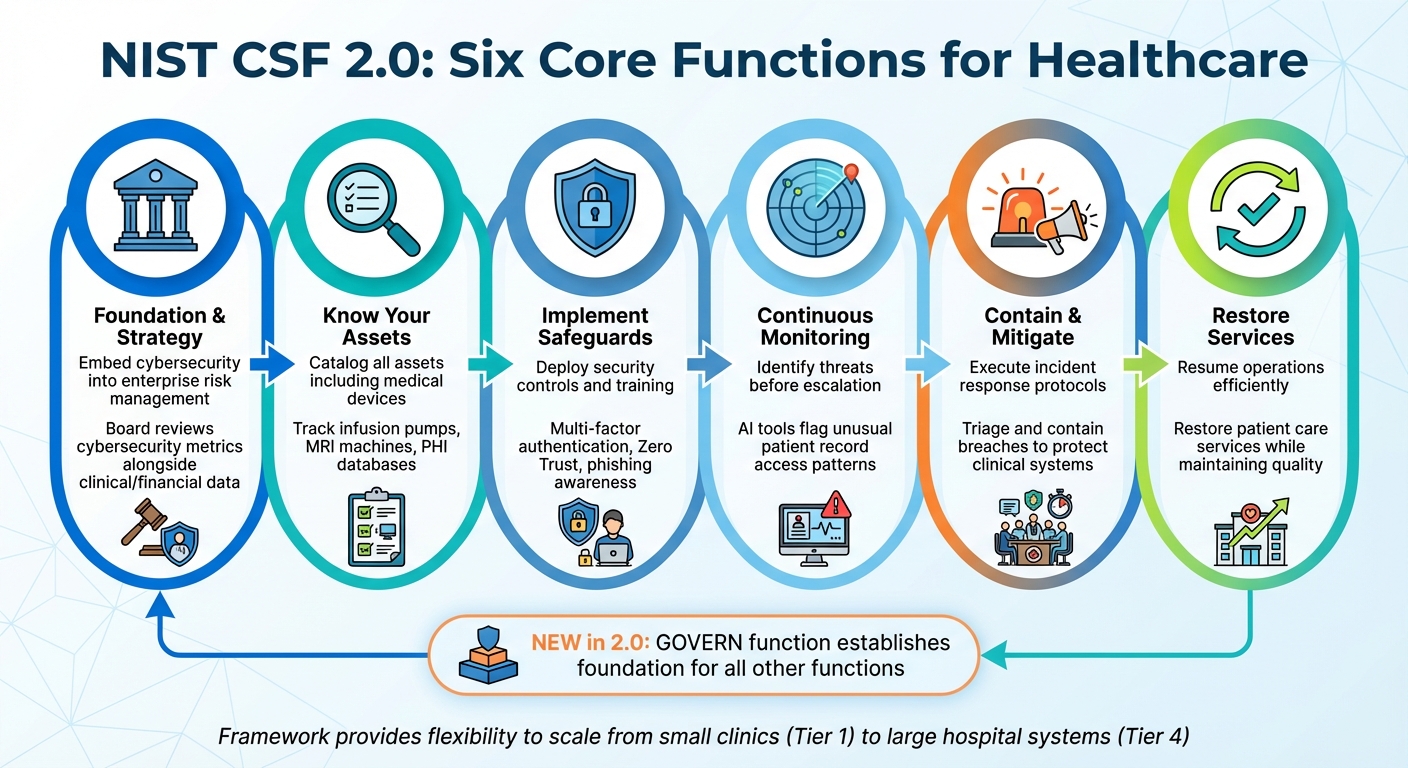
- Core Functions: The framework includes six functions - Govern, Identify, Protect, Detect, Respond, and Recover - each tailored to address healthcare-specific challenges like protecting patient data and securing medical devices.
- Incident Response Focus: The "Respond" function is critical for managing incidents effectively, covering containment, mitigation, communication, and recovery.
- Implementation Steps: Build a Computer Security Incident Response Team (CSIRT), create incident playbooks, and conduct regular tabletop exercises to test your plan.
Adopting the NIST CSF can reduce recovery time, improve compliance, and safeguard patient care during cyberattacks. With 37% of healthcare organizations lacking a contingency plan, implementing this framework is a practical step toward resilience.
Improving Healthcare Incident Response in the Wake of Recent Healthcare Breaches
sbb-itb-535baee
Understanding the NIST Cybersecurity Framework
NIST CSF 2.0 Six Core Functions for Healthcare Cybersecurity
The NIST Cybersecurity Framework provides healthcare organizations with a structured, risk-based approach to managing cybersecurity threats. Instead of prescribing a rigid checklist, it focuses on achieving specific outcomes, allowing organizations to customize their methods based on unique needs [3]. This flexibility is especially useful in healthcare, where environments range from small clinics to massive hospital systems teeming with connected devices.
Beyond technical guidance, the framework creates a shared language that bridges the gap between IT security teams and executive leadership. This integration ensures cybersecurity becomes part of enterprise-wide risk management rather than being siloed as just an IT issue [3]. Let’s break down the six core functions that form the backbone of this approach.
The 6 Core Functions of the NIST CSF
The NIST Cybersecurity Framework 2.0 organizes activities into six interconnected functions: Govern, Identify, Protect, Detect, Respond, and Recover [3]. Each function plays a distinct role in managing cybersecurity risks, working together to create a comprehensive defense.
Govern is the newest addition in version 2.0 and serves as the foundation for all other functions. It focuses on embedding cybersecurity into overall risk management, defining roles, responsibilities, and policies for third-party oversight [3].
The 'Govern' function establishes a robust foundation for the organization to build a cohesive cybersecurity strategy with clearly defined roles and responsibilities [3].
For healthcare, this means ensuring that boards review cybersecurity metrics alongside clinical and financial data [4][5].
Identify emphasizes understanding your organization's attack surface by cataloging all assets, including hardware, software, and data repositories. In healthcare, this extends to often-overlooked medical devices like infusion pumps and MRI machines [4][5]. It helps prioritize critical assets, such as Protected Health Information (PHI) or life-saving systems, ensuring resources are allocated to protect what matters most [3].
Protect involves implementing safeguards to minimize the impact of threats. This includes measures like multi-factor authentication (MFA), identity management systems, and phishing awareness training for staff [3]. Many healthcare organizations use this to adopt Zero Trust principles, ensuring that every user - whether in billing or the ER - meets strict security standards [4].
Detect focuses on continuous monitoring to identify potential threats before they escalate.
This function supports successful incident response and recovery activities [3].
For example, healthcare providers might rely on AI tools to flag unusual activity, like a user accessing thousands of patient records at odd hours [4].
Respond outlines how to contain and mitigate malicious activity once detected. This includes analyzing incidents, enacting mitigation strategies, and establishing communication protocols to notify both internal and external stakeholders [3]. Healthcare organizations often use this function to execute triage and containment measures, preventing breaches from disrupting clinical systems.
Recover ensures that services disrupted by an incident are restored efficiently. This includes verifying backups, bringing systems back online, and documenting lessons learned to improve future resilience [3]. For healthcare, this means resuming patient care services while maintaining quality standards.
| NIST CSF 2.0 Core Function | Healthcare Application Focus |
|---|---|
| Govern | Integrating cyber risk into hospital board-level decision-making and third-party vendor oversight. |
| Identify | Cataloging medical devices, software, and PHI databases to understand the attack surface. |
| Protect | Implementing multi-factor authentication (MFA) and training clinical staff on phishing risks. |
| Detect | Using 24/7 monitoring to spot unauthorized access to patient records or network anomalies. |
| Respond | Executing triage and containment protocols to prevent a breach from spreading to clinical systems. |
| Recover | Restoring patient-facing services and analyzing the incident to prevent future occurrences. |
Adapting the NIST CSF for Healthcare
Healthcare organizations can tailor the NIST framework to address challenges specific to their industry. Its flexibility allows providers to tackle issues like PHI protection, medical device security, and regulatory compliance [3].
One key adaptation involves mapping data flows beyond basic hardware inventories. For example, healthcare providers must identify potential vulnerabilities, such as HVAC systems or guest Wi-Fi networks, that could serve as entry points to clinical systems [4].
The framework also addresses the growing threat posed by connected medical devices and Shadow IT. The "Identify" function ensures organizations maintain a complete inventory of assets, including IoT devices that traditional IT systems might overlook [4][5]. This visibility is crucial for securing the increasingly complex attack surface in healthcare.
While HIPAA sets the baseline for patient data protection, the NIST framework provides the operational roadmap for achieving cyber resilience.
You need HIPAA to remain legal. You need NIST to remain operational [4].
Healthcare providers can use HHS "crosswalk" documents to align NIST controls with HIPAA Security Rule requirements, as seen in industry benchmarking studies, ensuring compliance and a strong operational foundation [4].
The framework's Implementation Tiers (ranging from Tier 1 to Tier 4) allow organizations to scale their cybersecurity efforts based on size and resources [4][5]. For example, a small clinic might start with basic practices at Tier 1, while a large hospital system could aim for Tier 4 with adaptive, continuously evolving security measures. This scalability ensures even resource-limited providers can implement effective cybersecurity protections.
The Respond Function: Building Your Incident Response Plan
In NIST CSF 2.0, the Respond function kicks into action the moment an incident is detected. Its primary aim? To limit the damage, investigate the situation, and coordinate the response to keep disruptions at a minimum. For healthcare organizations, this means safeguarding patient care while tackling threats like ransomware, data breaches, or compromised medical devices. The stakes are high - 88% of organizations reported at least one cybersecurity incident last year, with nearly half facing multiple events [7]. The Respond function provides a structured approach to turn potential chaos into a well-coordinated response. Below, we’ll break down the key areas healthcare organizations should focus on.
Respond Function Subcategories
NIST CSF 2.0 organizes the Respond function into four main categories, each critical for handling incidents effectively:
- Incident Management (RS.MA): This involves executing the response plan and triaging reports. In healthcare, incidents are prioritized based on their impact on patient care. For example, a ransomware attack on surgery scheduling would demand immediate attention, unlike an isolated laptop issue. It also includes defined escalation procedures, such as notifying the Chief Medical Information Officer (CMIO) or involving external cybersecurity experts.
- Incident Analysis (RS.AN): This step focuses on understanding the root cause and scope of the incident. Healthcare providers need to ask key questions: Was Protected Health Information (PHI) accessed? Was sensitive patient data exfiltrated? By analyzing logs and security alerts, teams can piece together the timeline of an attack.
- Incident Response Reporting and Communication (RS.CO): Timely communication with stakeholders is critical. Healthcare organizations must comply with regulations like the HIPAA Breach Notification Rule, which requires notifying regulatory bodies (e.g., the Office for Civil Rights) and affected patients. Pre-established channels with vendors and cloud providers help streamline coordination during an incident.
- Incident Mitigation (RS.MI): This phase focuses on containment and remediation. Isolating affected devices or networks prevents further spread, followed by steps like patching vulnerabilities or removing malware to eliminate the threat.
| NIST CSF 2.0 Respond Category | Healthcare Application Example |
|---|---|
| Incident Management (RS.MA) | Prioritizing a ransomware attack on surgery scheduling over a minor laptop issue |
| Incident Analysis (RS.AN) | Investigating if a database with patient Social Security numbers was compromised |
| Reporting & Communication (RS.CO) | Informing the Office for Civil Rights (OCR) and patients after a data breach |
| Incident Mitigation (RS.MI) | Isolating hospital Wi-Fi used by IoT medical devices during an exploit |
Mapping Respond to Incident Response Phases
The Respond function integrates seamlessly into the broader incident response cycle, making it easier to translate NIST CSF principles into actionable steps for healthcare.
- Preparation (RS.MA): Develop protocols and coordination mechanisms ahead of time, ensuring the response plan can be activated quickly and key personnel are notified.
- Detection & Analysis (RS.AN): When an alert is triggered, teams dig into the root cause. Was it a phishing email or a compromised patient portal? Immediate triage helps classify the incident’s severity.
- Containment (RS.MI-01): Prevent the threat from spreading by isolating affected systems, such as medical imaging devices or pharmacy networks.
- Eradication (RS.MI-02): Eliminate the root of the problem by removing malware or patching vulnerabilities.
- Recovery (RS.MA-05): Once it’s safe, restore services and bring patient-facing systems back online without putting safety at risk.
- Lessons Learned (RS.MA-01 / Identify Function - ID.IM): Use insights from the incident to improve future response capabilities.
| Incident Response Phase | NIST CSF 2.0 Respond Mapping |
|---|---|
| Preparation | RS.MA (Planning and coordination protocols) |
| Detection & Analysis | RS.AN (Investigating magnitude and root cause) |
| Containment | RS.MI-01 (Isolating affected systems) |
| Eradication | RS.MI-02 (Removing malware or closing vulnerabilities) |
| Recovery | RS.MA-05 (Criteria for restoring services) |
| Lessons Learned | RS.MA-01 / Identify Function (ID.IM) |
NIST SP 800-61 Revision 3, finalized in April 2025, serves as the official CSF 2.0 Community Profile for incident response, offering tactical guidance to complement these strategic categories [6][2].
To streamline the process, consider using Security Orchestration, Automation, and Response (SOAR) tools. These tools automate workflows, sending real-time notifications and isolating threats automatically. This not only speeds up response times but also allows security teams to focus on deeper analysis and decision-making.
How to Implement a NIST CSF Incident Response Plan
An effective incident response plan brings together people, processes, and technology into a cohesive system. For healthcare organizations, NIST SP 800-61r3 provides a detailed guide to setting up incident response capabilities, aligning with the six core functions of NIST CSF 2.0: Identify, Protect, Detect, Respond, Recover, and Govern [10][11]. This section focuses on translating these frameworks into practical steps to operationalize your incident response plan.
Building a CSIRT Structure
The first step is to establish your Computer Security Incident Response Team (CSIRT). Healthcare organizations typically choose one of three models:
- Centralized: A single team handles incidents across the organization.
- Distributed: Local teams manage incidents independently in their respective facilities.
- Coordinated: A central body oversees and supports independent teams.
For smaller healthcare providers, a virtual CSIRT can be an effective option. This team is formed by pulling together staff from existing IT, clinical, legal, and compliance departments as needed. As the National Cyber Security Centre (UK) notes:
It is more cost-effective to have a 'virtual' CSIRT, pulled together when needed, from people who have other day jobs [11].
This flexible approach ensures that even smaller organizations can respond effectively while balancing resource constraints.
Phased Implementation of the Plan
Implementing the incident response plan works best in structured phases:
- Preparation Phase: Lay the groundwork by developing incident response plans, acquiring forensic tools, setting up monitoring systems, and providing targeted training [9][11].
- Detection and Analysis Phase: Focus on identifying precursors (early signs of an attack) and indicators (evidence that an attack is underway) [9][11].
- Containment and Recovery Phase: Isolate affected systems, eliminate the cause of the threat, and restore operations using clean backups. Follow up with "Lessons Learned" reviews to refine policies and improve systems [9][11].
Each phase builds on the previous one, creating a cycle of continuous improvement that strengthens your organization’s cybersecurity posture.
Creating Policies and Procedures
Clear, well-documented policies and procedures form the foundation of an effective incident response plan. These should align with NIST CSF and HIPAA/HITECH requirements [9][10].
- Incident Playbooks: Develop playbooks for common threats like phishing, ransomware, or unauthorized access. Each playbook should detail steps such as who to notify, how to contain the threat, and what evidence to preserve.
- Asset Inventory: Maintain an up-to-date list of IT systems, medical devices, applications, and data repositories. This inventory is critical for assessing which systems are affected and prioritizing recovery efforts based on patient care impact [9].
- Legal and Regulatory Compliance: Engage legal counsel early to ensure your procedures meet data breach notification requirements. Under the HITECH Act, breaches affecting 500 or more individuals must be reported to the U.S. Department of Health and Human Services (HHS) [10].
Regular tabletop exercises are essential for testing your response procedures in simulated scenarios. These exercises help identify weaknesses in your plan before a real incident occurs. As Monica McCormack, Compliance Copywriter at Compliancy Group, explains:
Adopting the NIST Cybersecurity Framework for healthcare is not just a measure of compliance; it's a strategic move toward ensuring the confidentiality, integrity, and availability of critical healthcare data [10].
With well-defined policies in place, technology can take your incident response capabilities to the next level.
Leveraging Technology for Incident Response
Technology plays a crucial role in every phase of incident response, from detection to post-incident analysis. Security Orchestration, Automation, and Response (SOAR) tools can automate initial containment steps - like isolating compromised devices or blocking malicious IP addresses - allowing your team to focus on investigation [9].
For healthcare-specific needs, platforms like Censinet RiskOps™ centralize risk data and streamline compliance workflows. This tool enables healthcare organizations to:
- Track incidents from detection to resolution.
- Document evidence for regulatory reporting.
- Conduct post-incident reviews to drive improvements.
Censinet RiskOps™ also integrates third-party risk assessments, which is especially important given the rising threat of supply chain attacks. Its real-time command center provides a clear view of incident scope and potential impacts on patient care. Automated workflows ensure that critical findings reach the right stakeholders, such as clinical leaders assessing the effect on medical devices.
NIST CSF Incident Response Plan Template for Healthcare
Incident Response Plan Components
The NIST Cybersecurity Framework (CSF) lays the foundation for a solid incident response strategy. This template translates that framework into actionable steps tailored for healthcare organizations. It follows the four-phase NIST SP 800-61 lifecycle: Preparation, Detection and Analysis, Containment, Eradication, and Recovery, and Post-Incident Activity [9][12]. Each phase includes specific documentation aligned with the Respond subcategories in NIST CSF 2.0.
Start by defining the roles and responsibilities of your Cybersecurity Incident Response Team (CSIRT). Key members should include IT specialists, legal advisors (such as the Chief Privacy Officer), public relations professionals, and senior leadership [9][12]. To ensure continuity, assign backup decision-makers who can step in if primary team members are unavailable.
Communication protocols are critical for effective response. Your template should outline both internal communication (among CSIRT members and management) and external communication (with patients, law enforcement, regulators like HHS/OCR, and the public) [9][12]. Under the HITECH Act, breaches affecting 500 or more individuals must be reported to the U.S. Department of Health and Human Services and listed publicly [10]. Align your communication workflows with the 60-day federal notification window and any stricter state-level requirements for reporting breaches of Protected Health Information (PHI) [8].
Develop playbooks to guide responses to healthcare-specific threats like ransomware attacks or unauthorized access to Electronic Health Records (EHR). These playbooks should include decision trees that clearly assign responsibilities, such as isolating compromised medical devices or disabling affected user accounts. Each playbook should also specify which evidence to preserve for forensic analysis, which is essential for assessing the scope of PHI exposure [8].
Incorporate a severity matrix that prioritizes clinical impact, data importance (e.g., Electronic Medical Record (EMR) access), and regulatory risks. This ensures that response efforts focus on maintaining clinical operations. As Emily Bonnie, Senior Content Marketing Manager at Secureframe, emphasizes:
What separates resilient organizations isn't whether an incident occurs, but how quickly it's detected, how effectively it's contained, and how well the organization recovers and learns from it [7].
Finally, tailor these components to align with your organization's specific needs and regulatory environment.
Adapting the Template to Your Organization
Healthcare organizations differ greatly in size, risk exposure, and operational setup. For example, a small rural clinic faces different challenges than a large hospital system. Start by conducting a risk assessment to identify critical assets such as patient records, medical devices, telemedicine platforms, and supply chain dependencies [10].
Customize your plan to meet regulatory requirements. While HIPAA applies to all U.S. healthcare entities, state laws may impose additional breach notification rules or data protection standards. Consult legal counsel during the planning phase to ensure compliance with these varying requirements [9]. Tools like Censinet RiskOps™ can help streamline third-party risk assessments, cybersecurity benchmarking, and collaborative risk management tailored to healthcare.
Your asset inventory should reflect the technologies your organization actually uses. For example, if you rely heavily on IoT medical devices, your containment strategies must balance isolating compromised systems with maintaining access to life-critical equipment [8].
The NIST CSF is designed to focus on outcomes rather than rigid rules, giving you the flexibility to adapt response practices to your organization's reality. As Secureframe explains:
The Cybersecurity Framework is most effective when it's used to align expectations across the organization, not when it's treated as a checklist [7].
Test your customized plan with tabletop exercises that simulate realistic scenarios, such as a ransomware attack during peak patient hours or a vendor breach affecting your supply chain. These exercises expose weaknesses in your procedures and prepare your team to make decisions under pressure [9]. After each exercise or incident, conduct a review to update your playbooks and refine your risk profile. This ongoing improvement process ensures your plan evolves with new threats and organizational changes.
Conclusion
Key Takeaways
Healthcare organizations are grappling with increasing cybersecurity threats. Data breaches now average a staggering $9.77 million in costs and can lead to over 20 days of downtime following ransomware attacks [4]. Despite these risks, only 44% of healthcare organizations currently meet NIST CSF standards, and 37% lack any form of cybersecurity contingency plan [1]. This gap highlights both a pressing risk and a chance for improvement. Clearly, the need for stronger incident response strategies is urgent.
Adopting the NIST CSF framework can make a significant difference. For instance, organizations using it have seen insurance premium increases drop by 66% and recovery times improve, which helps minimize disruptions to patient care [1]. By implementing this framework, healthcare providers can restore critical systems like Electronic Health Records more quickly after an attack. As Emily Zaczynski, vCISO at Compass MSP, aptly puts it:
You need HIPAA to remain legal. You need NIST to remain operational [4].
The NIST CSF’s Respond function is key to managing incidents effectively, focusing on continuous improvement throughout the incident lifecycle. The updated NIST CSF 2.0 also introduces a new core function - Govern - which prioritizes cybersecurity governance and ensures leadership stays actively involved in managing risks [1][10].
To further strengthen defenses, healthcare organizations should develop tailored incident response plans. These plans should be continuously refined through regular tabletop exercises and thorough asset reviews. Customizing the approach to match an organization’s unique risk profile, resources, and regulatory requirements ensures the plan remains effective against evolving threats. Tools like Censinet RiskOps™ can support this process by simplifying third-party risk assessments, benchmarking cybersecurity efforts, and fostering collaboration.
Ultimately, the NIST CSF framework provides the foundation for rapid detection, effective response, and efficient recovery - critical steps in protecting patients and maintaining operational stability.
FAQs
How do we map HIPAA requirements to NIST CSF 2.0?
Mapping HIPAA requirements to NIST CSF 2.0 involves connecting HIPAA's administrative, physical, and technical safeguards to the categories and subcategories outlined in the NIST Cybersecurity Framework. This alignment helps healthcare organizations pinpoint compliance gaps, strengthen cybersecurity measures, and safeguard electronic protected health information (ePHI). By leveraging resources like NIST crosswalks, organizations can evaluate their current practices against desired cybersecurity objectives. This ensures they not only meet compliance standards but also effectively manage risks while addressing regulatory demands and stakeholder needs.
What should our CSIRT include in a small clinic?
Creating a Computer Security Incident Response Team (CSIRT) for a small clinic requires a well-thought-out incident response plan and a team of trained individuals with clearly defined roles. At its core, the team should include IT and security professionals who understand the unique challenges of healthcare cybersecurity. If necessary, consider involving external experts to fill any gaps in expertise.
The focus should be on rapid detection, containment, and recovery from threats such as data breaches or ransomware attacks. Following established frameworks, like the NIST Cybersecurity Framework, can provide a solid foundation for your plan. Regular testing through methods like tabletop exercises is also important to ensure the team is prepared to handle healthcare-specific risks. These drills can help identify weaknesses in your plan and improve the clinic's overall readiness.
How do we handle medical devices during ransomware containment?
To manage medical devices during a ransomware attack, focus on network segmentation to isolate these devices and prevent the malware from spreading further. Implement strict access controls, like two-factor authentication, to limit who can access the devices. Keeping devices updated with regular patches is crucial to address potential vulnerabilities.
An incident response plan that aligns with the NIST Cybersecurity Framework (CSF) is also key. This plan should include clear steps for isolating affected devices, conducting forensic analysis to understand the breach, and notifying patients when necessary. These measures ensure both effective containment of the threat and the safety of patients.


