Ransomware Disrupts Clinical Workflows: Key Risks
Post Summary
Ransomware attacks lock healthcare organizations out of EHR systems, patient portals, diagnostic tools, imaging devices, and pharmacy platforms simultaneously — forcing facilities to halt elective procedures, close outpatient clinics, and revert to paper-based workflows. The University of Mississippi Medical Center attack in February 2026 closed 36 clinics statewide, suspended all elective procedures, and kept the Epic EHR system offline for over a week with full recovery estimated at six months to a year. Paper-based fallback workflows slow triage, medication orders, and interdepartmental coordination, and create particular challenges for providers accustomed to digital systems who lose instant access to lab results and patient histories.
Extended EHR downtime forces clinical decision-making without access to medical histories, recent lab results, or diagnostic imaging — slowing and degrading care quality at precisely the moment when speed and accuracy matter most. Emergency departments must divert ambulances when they can no longer safely admit patients. During the Ascension Health attack in May 2024, a patient died after waiting four hours for lab results that should have been available in under an hour, and a NICU nurse nearly administered a fatal narcotic overdose to an infant because paper workflows eliminated the automated safety checks that digital systems provide. Staff working extended manual shifts face exhaustion and elevated error rates that compound patient safety risk throughout the outage period.
Healthcare networks are deeply integrated — EHRs connect to imaging devices, pharmacy systems, billing platforms, lab ordering systems, and medical equipment. A single ransomware attack exploiting this integration can compromise an entire network within minutes. To contain the spread, IT teams often take entire networks offline simultaneously, halting all digital operations at once and forcing every connected department into manual workflows at the same time. The February 2024 Change Healthcare attack demonstrated the scale of interconnected failure: encrypted clearinghouse systems brought insurance claims and prescription processing to a standstill nationwide, affecting thousands of facilities that had no direct involvement in the breach.
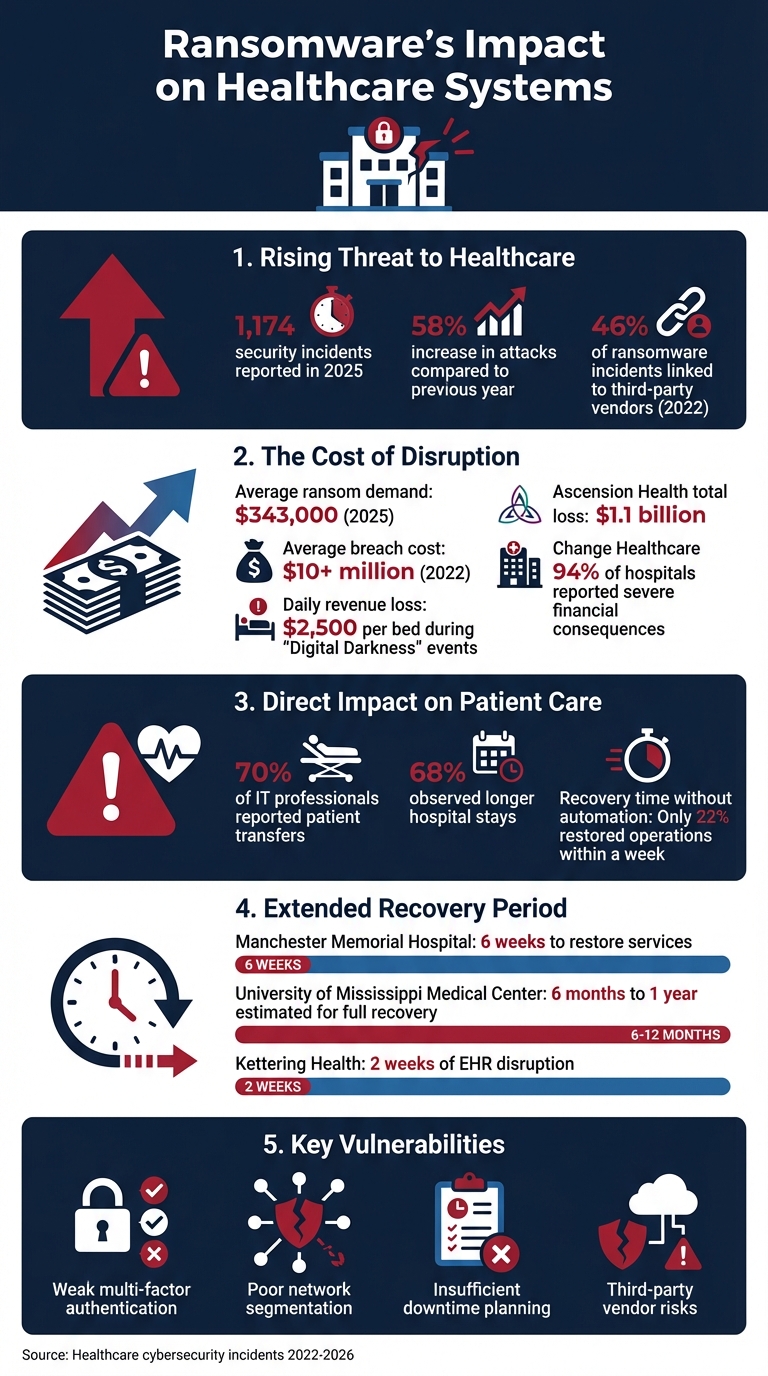
Recovery from healthcare ransomware attacks routinely stretches weeks to months. Manchester Memorial Hospital required nearly six weeks to fully restore services after the 2023 Rhysida attack. UMMC's February 2026 attack carried an estimated recovery timeline of six months to a year. Revenue losses during these "Digital Darkness" periods average $2,500 per bed per day. Following the Change Healthcare outage, 94% of affected hospitals reported severe financial consequences. In 2025, average ransomware demands in the healthcare sector reached $343,000, attacks increased 58% year-over-year, and the Ascension Health attack alone generated $1.1 billion in net losses alongside the exposure of 5.6 million patient records.
Healthcare is a prime ransomware target because of the high value of patient data, operational dependencies on digital systems that create maximum leverage for attackers, and the complexity of vendor ecosystems that create multiple entry points. Third-party vendors represented 46% of ransomware incidents in 2022, up from 36% in 2021 — making supply chain exposure the fastest-growing attack vector. Attackers increasingly target backup systems and administrative credentials to make recovery impossible without paying ransom, and human-operated ransomware attacks involve skilled adversaries who may spend months inside networks gathering intelligence before executing. Annual vendor assessments leave gaps that continuous monitoring must close.
Censinet RiskOps™ automates continuous third-party and enterprise risk management, enabling real-time monitoring of vendor security posture rather than point-in-time annual assessments that leave gaps attackers exploit. Censinet AI™ completes security questionnaires in seconds, summarizes documentation, and produces risk reports based on collected data — replacing manual assessment processes that cannot keep pace with the vendor portfolio size modern healthcare organizations manage. Among healthcare systems lacking automation, only 22% restored operations within a week following a 2025 security incident. Integrated cybersecurity benchmarking enables organizations to compare their security posture against peer institutions, while the platform's AHA Preferred Cybersecurity Provider status reflects its design specifically for healthcare operational and patient safety requirements.
Ransomware attacks are paralyzing healthcare systems, disrupting patient care, and creating safety risks. These attacks lock providers out of critical systems like electronic health records (EHRs), diagnostic tools, and patient portals, forcing facilities to halt operations or switch to inefficient manual workflows. The impact includes delayed treatments, canceled procedures, and increased risks for patients. Recent incidents, such as the University of Mississippi Medical Center attack in 2026, highlight how these disruptions can take months to resolve, costing millions in revenue and jeopardizing lives.
Key Points:
To mitigate these risks, healthcare organizations must strengthen cybersecurity measures, monitor third-party vendor security risks, and prepare for system outages with detailed incident response plans.
Ransomware Impact on Healthcare: Key Statistics and Recovery Costs
Cyberattacks on Hospitals Are Attacks on Communities: Why Ransomware Is a Patient Safety Crisis
sbb-itb-535baee
Key Risks of Ransomware in Clinical Workflows
When ransomware strikes a healthcare organization, it causes widespread operational breakdowns that jeopardize patient safety, disrupt essential services, and can take months to fully resolve.
Disruption to Patient Care and Clinical Operations
Ransomware doesn’t just lock up data - it cripples the digital systems that healthcare facilities depend on. Electronic Health Records (EHRs) become inaccessible, patient portals like MyChart shut down, and diagnostic tools stop functioning. The result? Elective procedures are canceled, and outpatient clinics are forced to close.
Take the University of Mississippi Medical Center in February 2026. A ransomware attack led to the closure of 36 clinics statewide and the suspension of all elective procedures. While emergency departments stayed open, staff had to switch to manual, paper-based workflows for several days. Their EPIC EHR system remained offline for over a week, with recovery efforts stretching into months [2][5].
Paper-based workflows bring their own challenges. Clinical teams must manually document everything, which slows down triage, medication orders, and interdepartmental coordination [2]. For younger providers who are accustomed to digital systems, working with paper records can be particularly difficult, as they lose quick access to lab results and patient histories [1].
The delays hit time-sensitive treatments hardest. Chemotherapy sessions are postponed, imaging appointments like CT scans and mammograms are canceled, and prescription refills stall. These aren’t just inconveniences - they’re serious disruptions to care plans that increase risks for patients [2][1].
"Healthcare downtime has a direct human cost. When outpatient clinics close, chemotherapy, imaging, follow-ups, and elective surgeries do not simply get delayed on a calendar. Care plans get disrupted, risk increases, and clinical teams lose the speed and coordination they rely on." - CyberFortress
These disruptions not only delay treatment but also place patients in increasingly vulnerable situations.
Increased Risk of Patient Harm
Prolonged system outages create conditions where patient safety is at serious risk. Without access to digital records or diagnostic tools, clinical decision-making slows down and becomes less precise. Emergency departments may even need to divert ambulances to other facilities, delaying critical care when every minute counts.
For example, in May 2024, Ascension Health System - a network of 140 hospitals - was hit by a cyberattack that forced ambulance diversions in multiple states, including Kansas and Florida. Patients missed vital imaging appointments, and clinicians had to make decisions without access to medical histories or recent test results [1].
Overworked staff further compound the problem. Nurses and physicians face longer shifts while trying to maintain care standards with manual processes, leading to exhaustion and higher chances of errors. Connie Smith, President of the Wisconsin Federation of Nurses and Health Professionals, described the toll:
"You're doing everything to the best of your ability but you leave feeling frustrated because you know you could have done things faster or gotten that patient home sooner if you just had some extra hands."
In August 2023, Manchester Memorial Hospital dealt with the fallout of a Rhysida ransomware attack, operating without X-rays or CT scans for nearly six weeks. Ambulances were diverted, elective surgeries canceled, and critical decisions were made with incomplete diagnostic information [3].
As patient care deteriorates, ransomware’s ability to spread across interconnected systems worsens the situation.
Network Propagation and System Failures
Ransomware thrives on interconnected healthcare systems, escalating disruptions by exploiting linked networks. EHRs are connected to imaging devices, pharmacy systems, billing platforms, and even medical equipment. While this integration boosts efficiency under normal circumstances, it also means a single ransomware attack can compromise the entire network in minutes [4].
To contain the spread, IT teams often take entire networks offline. While this may prevent further damage, it also halts all digital operations, forcing every connected system into downtime simultaneously [1].
The ripple effects are enormous. When EHRs go offline, it’s not just patient records that are affected - lab orders, medication dispensing, surgical scheduling, and even basic patient registration are disrupted. During the February 2024 Change Healthcare attack, encrypted clearinghouse systems brought insurance claims and prescription processing to a standstill nationwide, impacting thousands of facilities [4].
Extended Recovery Times
Restoring healthcare operations after a ransomware attack is a painstaking process that can stretch over weeks or even months. The complexity of medical IT systems - combined with the need to verify data integrity and investigate breaches - makes a quick recovery nearly impossible.
For instance, Manchester Memorial Hospital needed almost six weeks to fully restore services after the Rhysida attack in 2023 [3]. Following the University of Mississippi Medical Center attack in February 2026, experts estimated that full recovery could take six months to a year. During this time, facilities faced staggering losses, averaging $2,500 per bed, per day in revenue during these "Digital Darkness" events [5][4]. After the Change Healthcare outage, 94% of affected hospitals reported severe financial consequences [4].
"Resilience has to be measured by time to restore critical services, not only time to detect an incident." - CyberFortress
Ransomware attackers are well aware of these vulnerabilities. Increasingly, they target backup systems and administrative credentials, making recovery impossible without paying the ransom [2]. In 2025, the average ransomware demand in the healthcare sector rose to $343,000, with attacks increasing by 58% compared to the previous year [5].
How to Reduce Ransomware Risks
Ransomware's impact on healthcare systems can be devastating, but taking proactive steps can make a huge difference. By focusing on vendor oversight, leveraging automation, and preparing resilient operational plans, healthcare organizations can safeguard clinical workflows and reduce the risk of disruption.
Strengthening Vendor and Third-Party Risk Management
A significant number of ransomware attacks infiltrate healthcare systems through third-party vendors or supply chain partners. Relying on manual reviews or annual assessments leaves gaps that attackers can exploit. By the time an annual review is conducted, a vendor's security may have already weakened, creating vulnerabilities.
Continuous monitoring of vendors helps close these gaps by tracking security changes in real time. Tools like Censinet RiskOps™ simplify pre-engagement assessments, allowing security teams to identify weaknesses by asking the right third-party risk assessment questions before a vendor connects to critical systems. Automation ensures all vendors, even smaller ones, are thoroughly vetted - not just those flagged as high-risk.
Leveraging AI and Automation to Minimize Risks
AI tools significantly speed up risk assessment processes, replacing manual, time-consuming tasks. For example, Censinet AI™ can complete security questionnaires in seconds, summarize documentation, and produce risk reports based on collected data. This blend of automation and human oversight ensures the process remains efficient while maintaining control.
In 2025, healthcare systems reported 1,174 security incidents. Among organizations lacking automation, only 22% restored operations within a week. AI-driven platforms provide actionable insights, enabling teams to detect and address vulnerabilities before attackers exploit them [6][8].
Additionally, Censinet AI ensures critical findings are routed to the right stakeholders for prompt action. With configurable rules in place, teams can maintain oversight and make informed decisions. This balance between automation and human input strengthens clinical workflow resilience.
Building Resilient Clinical Workflows
Even with strong preventive measures, healthcare organizations must be prepared for attacks. Offline backups are crucial - they should be isolated from networks and tested regularly to ensure reliability during emergencies.
Incident response plans serve as a blueprint during attacks, detailing steps like isolating affected systems, notifying stakeholders, and shifting to manual operations. These plans can reduce delays in patient care, even during widespread disruptions [6][7].
Another important tool is the software bill of materials (SBOM), which gives IT teams visibility into all software components on clinical systems. This visibility allows rapid identification and patching of vulnerabilities, minimizing disruptions to essential services like claims processing and prescription management [6][7]. Network segmentation, designed with workflow dependencies in mind, further limits the spread of ransomware while ensuring critical systems - such as EHRs, imaging devices, and pharmacy platforms - can still communicate [8].
Case Study: Ransomware's Impact on Healthcare Delivery
Lessons from Past Incidents
These incidents highlight the serious risks to operations and patient care when healthcare systems are disrupted by ransomware. Past attacks have shown just how vulnerable clinical workflows can be when digital systems fail.
Take the case of Ascension Health in May 2024. This 140-hospital system, operating across 19 states, was hit by a ransomware attack that crippled its Epic EHR and MyChart systems. The fallout was immediate: ambulance services had to be diverted because staff could no longer safely admit new patients. The disruption didn’t stop there. A patient tragically died after waiting four hours for lab results that should’ve been processed in under an hour. In another instance, Marvin Ruckle, a NICU nurse, almost administered the wrong dose of a narcotic to an infant because the switch to paper records eliminated automated safety checks. Lisa Watson, an ICU nurse, narrowly prevented a fatal error, later reflecting:
"My patient probably would have passed away had I not caught it"
.
The attack also had a staggering financial toll, exposing 5.6 million patient records and costing the organization $1.1 billion in net losses [13].
A year later, in May 2025, Kettering Health in Ohio faced a similar crisis. The Interlock ransomware group targeted its 14-hospital network, disrupting EHR systems, lab operations, and ambulance routing for nearly two weeks. Staff had to rely on walkie-talkies and cellphones to coordinate care while neighboring hospitals absorbed the overflow of patients. By June, the attackers had begun leaking 941 GB of sensitive data - including patient records, blood-bank information, and employee passports - on the dark web [12]. The rapid collapse of systems and subsequent data leaks further compounded the crisis.
In February 2026, the University of Mississippi Medical Center (UMMC) became the latest victim. The attack shut down its Epic EHR platform, forcing the closure of all 35 outpatient clinics across the state. The chaos was palpable: chemotherapy appointments and elective surgeries were indefinitely postponed, and staff had to revert to manual processes, physically transporting lab results between departments. Dr. LouAnn Woodward, Vice Chancellor for Health Affairs, described the situation:
"To use a medical phrase - we have stopped the bleeding. And while we know much more now than we did 24 hours ago, the extent and the scope of the intrusion is still not fully understood"
.
These cases share alarming similarities: weak multi-factor authentication on critical systems, poor network segmentation that allowed malware to spread quickly, and a lack of robust downtime planning for extended outages. However, organizations that had invested in immutable backups, conducted regular paper-drill exercises, and implemented aggressive network isolation measures recovered faster and faced fewer patient safety issues [11][12][13]. These lessons underline the importance of stronger authentication protocols, better network design, and proactive planning to mitigate the impact of ransomware attacks.
Conclusion
Key Takeaways
Ransomware attacks pose serious risks to patient safety and hospital operations. Surveys reveal that 70% of IT professionals reported patient transfers, and 68% observed longer hospital stays as a direct result of such attacks[14]. These delays can lead to higher rates of medical complications and even increased mortality.
In 2022, healthcare breaches cost an average of over $10 million, with ransom payments climbing from $282,675 to $352,541 within just two years[14]. Human-operated ransomware attacks are particularly dangerous, as they involve skilled attackers who may spend months gathering intelligence and moving through networks before striking. Another alarming trend is the rise in third-party vendor vulnerabilities - 46% of ransomware incidents in 2022 were linked to third-party vendors, up from 36% in 2021[14].
Past incidents highlight how weaknesses such as poor multi-factor authentication, inadequate network segmentation, and insufficient downtime planning can leave healthcare organizations vulnerable. Those that invested in strong cybersecurity measures and well-thought-out incident response plans recovered faster and faced fewer disruptions to their clinical operations.
Strengthening cybersecurity is not just a technical necessity - it’s a critical step in protecting patient safety and ensuring uninterrupted care.
How Censinet Supports Healthcare Cybersecurity
Censinet RiskOps™ offers a proactive solution to these challenges by automating third-party and enterprise risk management, specifically designed to safeguard healthcare systems. As a Preferred Cybersecurity Provider of the American Hospital Association (AHA), Censinet provides a cloud-based risk exchange tailored to mitigate threats to patient safety and care delivery.
The platform simplifies risk assessments across all technology vendors and internal systems, identifying vulnerabilities - like those from software updates or new remote access tools - in real time. With Censinet AI™, healthcare organizations can manage the risks tied to the rapid adoption of AI in clinical environments. Additionally, integrated cybersecurity benchmarking allows organizations to compare their security posture with industry peers. This collaborative approach helps unify IT, procurement, and compliance teams, ensuring that risk management efforts are aligned to protect patient care and maintain operational stability.
Effective risk management is key to keeping clinical workflows reliable and resilient. By addressing these challenges head-on, healthcare organizations can better protect their patients and their systems.
FAQs
What should clinicians do first when the EHR goes down?
When an EHR system goes offline - whether from a ransomware attack or another disruption - clinicians need to rely on downtime procedures. This usually means shifting to manual processes, like using paper documentation, to keep patient care on track and ensure safety. These measures are critical for maintaining clinical operations while IT teams focus on getting the system back online.
How can hospitals keep ransomware from spreading across connected systems?
Hospitals can take steps to contain ransomware threats by using network segmentation, which helps stop infections from spreading across systems. Conducting regular risk assessments, providing staff with phishing awareness training, and keeping backups current are other key measures to reduce risk. Testing recovery plans is crucial for ensuring systems can be restored quickly without resorting to ransom payments. Tools like centralized access controls, such as single sign-on (SSO), and monitoring remote access points also play a vital role in preventing unauthorized movement within hospital networks.
What makes backups ransomware-resistant in healthcare?
Backups play a crucial role in protecting healthcare organizations from ransomware. They securely store critical data, enabling systems to be restored without succumbing to ransom demands. This safeguard ensures that essential information remains accessible, allowing healthcare providers to maintain continuity of care - even in the face of a ransomware attack.
Related Blog Posts
- One in Three Hospitals Confirm Cyber Incidents Directly Impacted Patient Care in Benchmark Findings
- How Healthcare Organizations Lost Access to Patient Records for 15 Hours - And What Happens Next
- Cancer Center Vendor Risk: Oncology Equipment, Drugs, and Treatment Safety
- Top 7 Topics for Healthcare Cybersecurity Training
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":[{"@type":"Question","name":"What should clinicians do first when the EHR goes down?","acceptedAnswer":{"@type":"Answer","text":"<p>When an EHR system goes offline - whether from a ransomware attack or another disruption - clinicians need to rely on <strong>downtime procedures</strong>. This usually means shifting to manual processes, like using paper documentation, to keep patient care on track and ensure safety. These measures are critical for maintaining clinical operations while IT teams focus on getting the system back online.</p>"}},{"@type":"Question","name":"How can hospitals keep ransomware from spreading across connected systems?","acceptedAnswer":{"@type":"Answer","text":"<p>Hospitals can take steps to contain ransomware threats by using <strong>network segmentation</strong>, which helps stop infections from spreading across systems. Conducting regular <strong>risk assessments</strong>, providing staff with <strong>phishing awareness training</strong>, and keeping backups current are other key measures to reduce risk. Testing recovery plans is crucial for ensuring systems can be restored quickly without resorting to ransom payments. Tools like centralized access controls, such as <strong>single sign-on (SSO)</strong>, and monitoring remote access points also play a vital role in preventing unauthorized movement within hospital networks.</p>"}},{"@type":"Question","name":"What makes backups ransomware-resistant in healthcare?","acceptedAnswer":{"@type":"Answer","text":"<p>Backups play a crucial role in protecting healthcare organizations from ransomware. They securely store critical data, enabling systems to be restored without succumbing to ransom demands. This safeguard ensures that essential information remains accessible, allowing healthcare providers to maintain continuity of care - even in the face of a ransomware attack.</p>"}}]}
Key Points:
How does ransomware create immediate and cascading clinical workflow failures across healthcare organizations?
- EHR loss as the central failure cascade — When ransomware encrypts EHR systems, the failure is not limited to patient record access. Lab ordering, medication dispensing, surgical scheduling, imaging requests, and patient registration all flow through EHR infrastructure. Taking the EHR offline takes all of these functions offline simultaneously, creating an organization-wide operational collapse rather than an isolated data access problem.
- Paper-based fallbacks introduce their own clinical risks — Manual paper workflows slow triage processes, medication order verification, and interdepartmental coordination. Providers accustomed to digital systems lose instant access to lab results, allergy alerts, medication histories, and diagnostic images — the information most critical to safe, fast clinical decisions. The automated safety checks embedded in digital systems — including medication dosing alerts and contraindication warnings — disappear entirely.
- Time-sensitive treatments absorb the largest harm — Chemotherapy sessions, CT scans, mammograms, and elective surgeries do not simply shift on a calendar when systems go down — care plans are disrupted, follow-up dependencies are broken, and risk accumulates for every day treatment is delayed. These are not administrative inconveniences; they are direct patient safety failures with measurable consequences.
- UMMC 2026 as a documented system-scale failure — The University of Mississippi Medical Center's February 2026 attack closed 36 clinics statewide, suspended all elective procedures, kept the Epic EHR offline for over a week, and initiated a recovery process estimated at six months to a year — demonstrating that even large, well-resourced health systems cannot contain ransomware damage to a limited scope once network propagation begins.
- Staff experience compounds clinical risk — Nurses and physicians working extended manual shifts under ransomware conditions face exhaustion that directly elevates medication error rates, documentation errors, and clinical judgment failures. Connie Smith, President of the Wisconsin Federation of Nurses and Health Professionals, described staff leaving shifts frustrated knowing they could have delivered better, faster care with functioning systems.
- Younger providers face particular digital dependency risks — Providers trained primarily in digital-first environments have limited experience with paper-based workflows, creating a skill gap that becomes a patient safety gap during outages. The institutional knowledge of manual processes that older providers carry is not uniformly distributed across clinical teams, creating uneven downtime capability across departments.
What patient safety consequences have ransomware attacks directly caused in documented healthcare incidents?
- Ascension Health 2024 — patient death and near-fatal medication error — The May 2024 Ascension Health attack crippled Epic EHR and MyChart across 140 hospitals in 19 states. A patient died after waiting four hours for lab results that should have been available in under an hour. A NICU nurse nearly administered a fatal narcotic overdose to an infant because paper records eliminated automated dosing safety checks. An ICU nurse described catching a potentially fatal error, reflecting that her patient would likely have died without her intervention.
- Ambulance diversion as an emergency access failure — Ransomware-forced ambulance diversions in both the Ascension Health 2024 attack and the Manchester Memorial 2023 Rhysida attack delayed emergency care for patients who could not be safely admitted to the affected facilities. Every diversion adds transport time to a patient population that sought emergency care because time was already critical.
- Six weeks without imaging at Manchester Memorial — Manchester Memorial Hospital operated without X-rays or CT scans for nearly six weeks following the 2023 Rhysida attack, requiring clinical teams to make diagnostic decisions without the imaging evidence those decisions normally depend on. Elective surgeries were canceled and ambulances diverted throughout the outage period.
- Kettering Health 2025 — 14-hospital network collapse — The May 2025 Interlock ransomware attack on Kettering Health's 14-hospital Ohio network disrupted EHR systems, lab operations, and ambulance routing for nearly two weeks. Staff coordinated care using walkie-talkies and cellphones while neighboring hospitals absorbed patient overflow. By June, attackers began leaking 941 GB of sensitive data including patient records, blood-bank information, and employee passports on the dark web.
- Change Healthcare 2024 — nationwide pharmacy and claims disruption — The February 2024 Change Healthcare attack encrypted clearinghouse systems and brought insurance claims processing and prescription management to a standstill nationally, affecting thousands of facilities with no direct involvement in the attack and demonstrating that ransomware on a single vendor node can produce patient care consequences across an entire healthcare system.
- Documented population-level survey data confirms systemic harm — Surveys found that 70% of IT professionals reported patient transfers and 68% observed longer hospital stays as direct results of ransomware attacks — translating individual incident narratives into population-level evidence that ransomware-related clinical disruption produces measurable harm at scale across the healthcare system.
How does ransomware propagate across interconnected healthcare networks and what makes containment so operationally disruptive?
- Deep system integration creates simultaneous multi-system failure — EHR systems are integrated with imaging devices, pharmacy dispensing platforms, billing infrastructure, lab ordering systems, surgical scheduling, and medical equipment management. A ransomware payload that reaches the EHR network does not stay there — it traverses every connected system, potentially encrypting all of them within minutes of initial execution.
- Network takedown as a containment measure creates its own operational crisis — IT teams responding to active ransomware propagation often take entire network segments offline to prevent further spread. While this limits encryption damage, it simultaneously forces every connected system and department into manual workflows at once — creating an organization-wide downtime event rather than a contained incident.
- Backup systems and administrative credentials as secondary targets — Sophisticated ransomware operators have adapted to target backup systems and administrative credentials specifically, recognizing that destroying recovery options maximizes leverage and ransom payment likelihood. Organizations that have not isolated backups from network access have discovered during attacks that their recovery infrastructure was encrypted alongside operational systems.
- Third-party vendor entry points as the dominant attack vector — 46% of ransomware incidents in 2022 were linked to third-party vendors, up from 36% in 2021. Vendors with access to hospital networks — including software providers, managed service vendors, and medical device manufacturers — represent attack surface that extends far beyond the hospital's own security perimeter and cannot be managed through internal controls alone.
- Human-operated ransomware extends dwell time before detonation — Unlike automated ransomware that executes immediately, human-operated ransomware attacks involve skilled adversaries who may spend weeks or months inside a network gathering administrative credentials, mapping backup systems, and staging payloads before executing — maximizing both propagation scope and recovery difficulty when the attack finally detonates.
- Software bill of materials as a propagation visibility tool — Maintaining a software bill of materials for clinical systems gives IT teams visibility into all software components, enabling rapid identification of vulnerable components following a ransomware detonation and supporting faster patching and isolation decisions that limit propagation before the full network is compromised.
What are the financial and operational costs of healthcare ransomware recovery and how do they accumulate over extended downtime periods?
- $2,500 per bed per day in revenue losses during downtime — Healthcare organizations experiencing what the industry terms "Digital Darkness" — complete loss of digital operational capability — average $2,500 per bed per day in revenue losses, creating a financial accumulation that scales directly with both facility size and recovery duration.
- 94% of Change Healthcare-affected hospitals reported severe financial consequences — The February 2024 Change Healthcare attack's financial impact extended to the 94% of affected hospitals that reported severe consequences — including claims processing delays, cash flow disruption, and operational costs of manual workflow maintenance — despite most having no direct involvement in the breach itself.
- Ascension Health $1.1 billion net loss and 5.6 million record exposure — The Ascension Health 2024 attack generated $1.1 billion in net losses and exposed 5.6 million patient records, establishing the upper bound of financial consequence for a large health system ransomware event and demonstrating that the financial impact of a major attack exceeds ransom payment costs by orders of magnitude.
- 2025 average ransom demand of $343,000 with 58% attack volume increase — The healthcare sector's average ransom demand reached $343,000 in 2025 while attack volume increased 58% year-over-year, establishing an accelerating financial threat environment in which the cost of building preventive capability is increasingly favorable compared to the cost of responding to an attack.
- Recovery complexity scales with system integration depth — The complexity of medical IT systems — combined with data integrity verification requirements and breach investigation obligations — makes rapid recovery structurally impossible. Full restoration requires rebuilding trust in every integrated system, not just restoring files, extending recovery timelines regardless of whether ransom is paid.
- Resilience measured by time to restore, not time to detect — CyberFortress has noted that healthcare resilience must be measured by time to restore critical services, not only time to detect an incident. Organizations that invested in immutable backups, conducted regular paper-drill exercises, and implemented aggressive network isolation recovered faster and faced fewer patient safety complications — establishing preparedness investment as directly tied to recovery speed outcomes.
What proactive steps should healthcare organizations take to reduce ransomware risk and build clinical workflow resilience?
- Continuous vendor monitoring replacing annual assessments — Annual vendor risk assessments leave gaps of 364 days during which a vendor's security posture can deteriorate without detection. Continuous monitoring tracks vendor security changes in real time, closing the gap that attackers most commonly exploit in supply chain ransomware campaigns.
- Network segmentation designed around workflow dependencies — Network segmentation limits ransomware propagation by isolating segments of the healthcare network from each other, but segmentation must be designed with clinical workflow dependencies in mind. Segmentation that prevents ransomware spread while also isolating EHRs from imaging devices or pharmacy platforms from lab systems creates its own operational failure during an attack response.
- Isolated and tested offline backups as a non-negotiable resilience requirement — Backups that are connected to the network are routinely encrypted alongside operational systems in sophisticated ransomware attacks. Offline, network-isolated backups that are regularly tested for restoration reliability are the only backup architecture that provides reliable recovery capability when ransomware targets backup systems as part of its execution strategy.
- Incident response plans with manual workflow protocols — Incident response plans must include specific manual workflow protocols for extended EHR downtime — covering paper documentation procedures, medication order verification processes, lab result communication pathways, and interdepartmental coordination mechanisms. Plans that only address IT response without clinical workflow guidance leave clinical teams without direction at the moment of highest stress.
- Multi-factor authentication and credential hygiene as entry point defenses — The UMMC, Ascension, and Kettering case studies share a common vulnerability pattern: weak multi-factor authentication on critical systems and poor network segmentation that allowed malware to spread rapidly. Implementing strong MFA across all administrative and clinical system access points closes the credential-based entry vectors that human-operated ransomware campaigns most commonly exploit.
- Software bill of materials for clinical system component visibility — Maintaining an SBOM for clinical systems enables rapid identification and patching of vulnerable components following a ransomware event and supports faster isolation decisions that limit propagation scope — a visibility tool that has become a recognized best practice for healthcare organizations managing complex, integrated clinical IT environments.
How do Censinet RiskOps™ and Censinet AI™ specifically address the vendor risk, assessment automation, and governance requirements that healthcare ransomware prevention demands?
- AHA Preferred Cybersecurity Provider status reflects healthcare-specific design — Censinet's designation as a Preferred Cybersecurity Provider of the American Hospital Association reflects the platform's design specifically for healthcare operational requirements, clinical system complexity, and patient safety obligations — not general enterprise risk management adapted for healthcare use.
- Continuous vendor monitoring at portfolio scale — Censinet RiskOps™ enables continuous monitoring of third-party vendor security posture across the full vendor portfolio, providing real-time visibility into the security changes that point-in-time annual assessments cannot detect and that represented the entry vector for 46% of healthcare ransomware incidents in 2022.
- Censinet AI™ assessment speed and accuracy — Censinet AI™ completes security questionnaires in seconds, summarizes vendor documentation, and produces risk reports based on collected data — replacing manual assessment timelines that cannot scale to the vendor portfolio sizes modern healthcare organizations manage and that leave assessment gaps that attackers exploit.
- 22% vs. majority recovery rate differential for automated vs. manual organizations — Among healthcare systems lacking automation, only 22% restored operations within a week following a 2025 security incident — establishing the operational resilience gap between automated and manual risk management programs and quantifying the recovery speed advantage that automation-equipped organizations demonstrate.
- Cybersecurity benchmarking for peer comparison — Integrated cybersecurity benchmarking within Censinet RiskOps™ enables healthcare organizations to compare their security posture against industry peers, identifying relative strengths and gaps that internal assessment alone cannot surface and supporting the evidence-based investment decisions that ransomware prevention requires.
- Unified IT, procurement, and compliance team alignment — Censinet RiskOps™ unifies IT, procurement, and compliance teams within a shared risk management platform, ensuring that vendor security assessment findings inform procurement decisions, that compliance obligations are tracked against actual vendor controls, and that risk findings reach the right decision-makers before they become operational vulnerabilities.


