SOC 2 Incident Response: Vendor Supply Chain Risks
Post Summary
Managing vendor supply chain risks is critical for protecting sensitive healthcare data. SOC 2 compliance helps organizations evaluate vendors based on key principles like Security, Availability, and Confidentiality. However, supply chain vulnerabilities - like misconfigured databases or unpatched systems - can still pose significant threats, especially in healthcare, where vendor ecosystems are vast.
Key Takeaways:
- SOC 2 Compliance: Focuses on monitoring vendor access, ensuring system uptime, and safeguarding sensitive data.
- Supply Chain Risks: Weak links in vendor networks can lead to breaches, legal issues, and reputational damage.
- Incident Response: Requires documented, tested plans tailored to supply chain risks, including clear roles, communication protocols, and remediation steps.
- Monitoring Vendors: Continuous oversight, real-time anomaly detection, and automated tools like Censinet RiskOps™ improve risk management.
- Post-Incident Reviews: Evaluate vendor performance, update contracts, and refine response plans based on actual incidents.
By integrating continuous monitoring, robust incident response protocols, and regular vendor assessments, healthcare organizations can better manage supply chain risks and maintain compliance with SOC 2 standards.
SOC 2 Academy: Managing Vendor Risk
sbb-itb-535baee
SOC 2 Requirements for Incident Response
SOC 2 Trust Services Criteria for Supply Chain Incident Response
Trust Services Criteria for Incident Management
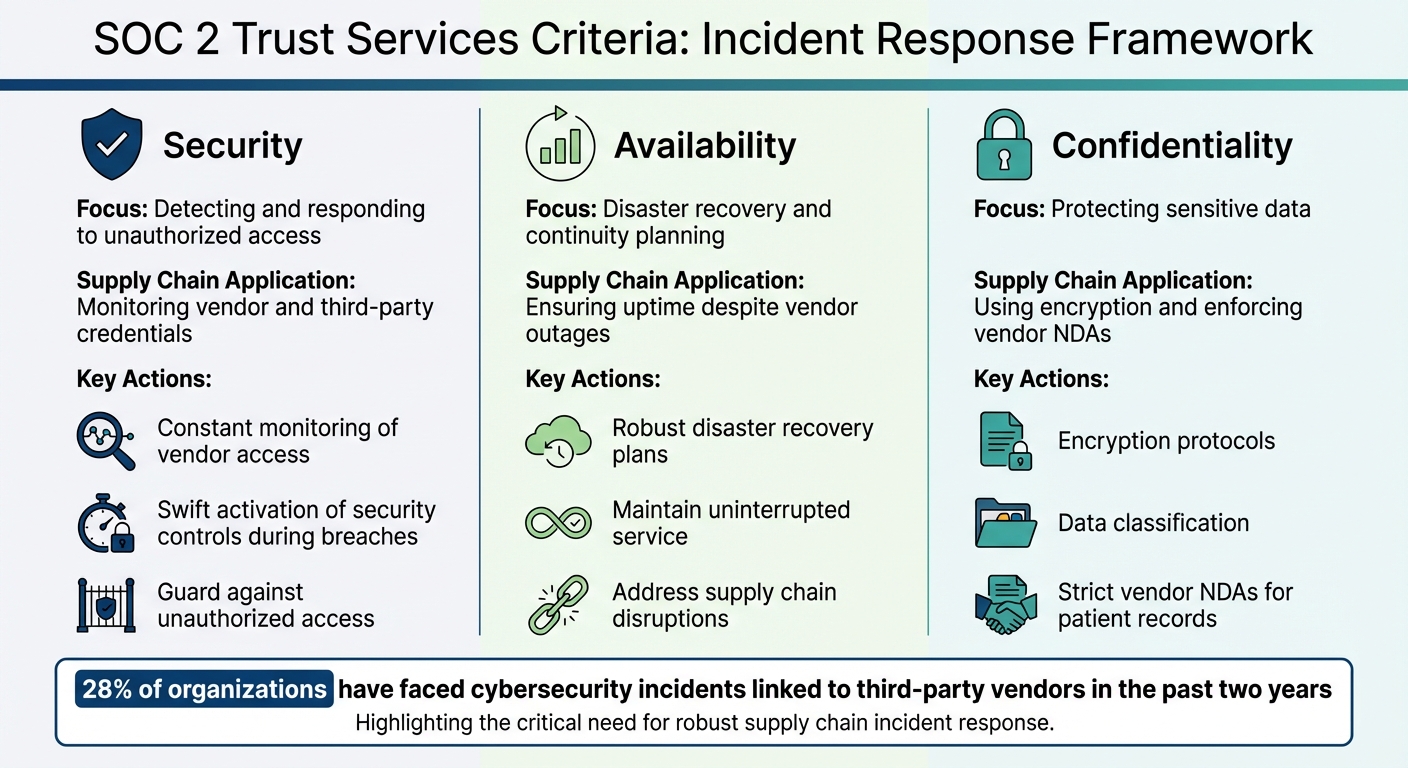
SOC 2 evaluates service providers using five Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy. For incident response, the focus often falls on Security, Availability, and Confidentiality.
- Security serves as the backbone of incident management. Organizations must guard against unauthorized access while detecting, responding to, and recovering from security incidents. For healthcare vendors, this means constant monitoring of vendor access and third-party credentials throughout the supply chain. Swift activation of security controls is essential during a breach.
- Availability ensures systems and services remain operational to meet commitments. This involves robust disaster recovery and continuity plans, especially for supply chain disruptions. For instance, if a cloud provider experiences downtime, availability controls should help maintain uninterrupted service.
- Confidentiality emphasizes protecting sensitive information. This includes encryption, data classification, and strict vendor non-disclosure agreements (NDAs) to safeguard shared data, such as patient records, during supply chain incidents. The stakes are high: 28% of organizations have faced cybersecurity incidents linked to third-party vendors in the past two years [4].
| Trust Services Criteria | Application to Incident Response | Supply Chain Context |
|---|---|---|
| Security | Detecting and responding to unauthorized access | Monitoring vendor and third-party credentials |
| Availability | Disaster recovery and continuity planning | Ensuring uptime despite vendor outages |
| Confidentiality | Protecting sensitive data | Using encryption and enforcing vendor NDAs |
These criteria form the foundation for a strong, supply chain-aware incident response strategy.
Documenting and Testing Incident Response Plans
Building on these criteria, organizations must create and rigorously test their incident response plans. SOC 2 compliance requires documented, tested, and repeatable procedures. Healthcare vendors, in particular, need to demonstrate that these plans effectively address supply chain incidents. This means having clear communication protocols and defined remediation steps for incidents involving third-party vendors.
Procurement processes reflect the importance of these measures - 61% of organizations require vendor incident response protocols during vendor selection [4]. Additionally, 83% of software and digital service providers report having formal incident response policies, including detailed communication plans and timelines for notifying customers [4].
To address supply chain vulnerabilities, vendors should:
- Include breach scenarios specific to third-party risks in testing.
- Regularly review SOC 2 reports from suppliers to identify gaps in controls.
- Require ongoing SOC 2 compliance in vendor contracts.
- Verify that vendors use multi-factor authentication and secure access protocols.
Healthcare vendors can strengthen their approach with tools like Censinet RiskOps™, which simplify third-party risk assessments and provide real-time monitoring of vendor compliance. These solutions help maintain continuous oversight and improve response readiness.
"This resource helps organizations communicate certain information about the supply chain risk management efforts and assess the effectiveness of system controls that mitigate those risks." [5]
The AICPA's SOC for Supply Chain framework offers a clear reporting structure tailored to addressing supply chain vulnerabilities. By using this framework, healthcare vendors can demonstrate the reliability of their controls, gaining an edge during vendor selection.
Identifying and Reducing Supply Chain Vulnerabilities
Mapping Vendor Risks in Healthcare
Healthcare supply chains come with challenges that go far beyond standard vendor relationships. These systems involve patient data, medical records, research platforms, and medical devices - each introducing its own set of risks [3]. Even small mistakes, like vendor misconfigurations, can snowball into major vulnerabilities.
"It takes only one vendor's vulnerability to compromise everyone. A single misconfigured database or unpatched cloud service can trigger supply chain risks across dozens of connected companies." [1]
- Mark Edgeworth, CEO, Hicomply
To tackle these risks, vendor mapping must be thorough and systematic. This means managing the entire vendor lifecycle - from initial selection and due diligence to contract oversight, ongoing monitoring, and incident response [2]. Healthcare organizations should keep a detailed risk register that tracks third-party relationships, their SOC 2 compliance status, access controls, and the types of data they handle. This approach not only creates a clear audit trail but also helps prioritize vendors that pose the highest risks to PHI security. With this foundation, healthcare providers can better address the specific threats outlined below.
Common Supply Chain Threats
Once vulnerabilities are identified through vendor mapping, healthcare organizations must address threats like credential theft, unauthorized access to critical systems, and poor physical security at data centers [1]. Credential theft is particularly concerning when vendors fail to implement multi-factor authentication (MFA) across their supply chains.
Looking ahead to 2026, a new challenge is emerging: the "governance gap." This refers to the rapid adoption of AI technologies outpacing the ability to manage and govern associated risks [3].
"Healthcare is the most complex industry... You can't just take a tool and apply it to healthcare if it wasn't built specifically for healthcare" [3].
- Matt Christensen, Sr. Director GRC at Intermountain Health
This complexity increases systemic risk. A single weak link in a network of tens of thousands of vendors can jeopardize the entire ecosystem [3].
Risk Assessment Methods for Vendors
To address vulnerabilities and threats, healthcare organizations need robust risk assessment strategies. These assessments should go beyond SOC 2 certifications, diving into Trust Service Criteria and audit findings to uncover potential control weaknesses that could impact PHI [2]. When prioritizing risks, organizations should consider the services a vendor provides, the sensitivity of the data they handle, and their overall security measures [2].
The SOC for Supply Chain framework from AICPA offers a structured approach to pinpoint and evaluate risks at every stage of the supply chain [1]. Instead of relying solely on annual audits, many healthcare organizations are adopting continuous compliance monitoring. This involves using automated tools to track vendor controls in real time, making it easier to spot issues as they arise [1]. Platforms like Censinet RiskOps™ are paving the way for this shift, replacing manual spreadsheets with integrated risk management systems. These tools allow organizations to conduct more assessments with fewer resources [3].
For example, Tower Health implemented Censinet RiskOps in 2025-2026. According to CISO Terry Grogan, the platform freed up three full-time employees to return to their primary responsibilities while enabling the team to handle a much higher volume of risk assessments with just two staff members [3]. Similarly, Baptist Health’s VP & CISO James Case highlighted how joining a collaborative network of hospitals eliminated the need for spreadsheets:
"Not only did we get rid of spreadsheets, but we have that larger community [of hospitals] to partner and work with" [3].
- James Case, VP & CISO, Baptist Health
Building Supply Chain Risks into Incident Response Plans
Creating Vendor-Specific Response Protocols
To meet SOC 2 requirements, healthcare vendors need incident response protocols tailored to address supply chain risks. These protocols should outline clear roles and responsibilities for teams like security, privacy, legal, compliance, procurement, IT, and vendor management. They should also define severity tiers that determine when to notify leadership and impacted entities. Additionally, the protocols must include detailed playbooks for immediate actions, such as revoking tokens and keys, disabling SSO, blocking integrations, and initiating downtime procedures to protect clinical operations. Evidence handling is another crucial piece - vendors must secure logs, email headers, and system images to maintain a proper investigation chain [6].
Integrated tools like Censinet RiskOps™ can help automate risk assessments and ensure vendor-specific protocols are applied uniformly. Once these protocols are established, rigorous testing is necessary to confirm they work as intended.
Testing Response Plans for Supply Chain Scenarios
After defining protocols, healthcare vendors should validate their response readiness through simulated supply chain scenarios. Assigning specific roles for evidence preservation - separate from containment efforts - is key. Every action taken must be documented, including timestamps and the personnel involved, to maintain an unbroken chain of custody [6]. Regular tabletop exercises can also enhance coordination across departments, ensuring all teams understand their responsibilities when faced with supply chain incidents.
Monitoring Vendors and Maintaining Accountability
Real-Time Monitoring and Anomaly Detection
Keeping tabs on vendors in real time is crucial for spotting issues before they escalate. Instead of relying on one-off assessments, aim for continuous visibility into vendor security practices. This involves using tools and systems designed to detect unusual behaviors, like unexpected attempts to access data, dips in the performance of vendor systems, or strange authentication patterns. For protecting sensitive health information (PHI), strict access controls are a must. These include multi-factor authentication (MFA), IP allow-listing, and just-in-time access protocols - all aligned with SOC 2 Security and Availability Trust Services Criteria [7][6].
One tool that simplifies this process is Censinet RiskOps™, which automates updates and eliminates the need for manual tracking. For example, Tower Health reported a major efficiency boost in 2025/2026 by implementing automated monitoring. They reduced their risk assessment staffing from five full-time employees to just two, freeing up three team members for other responsibilities while still handling a higher volume of assessments [3]. To measure the success of monitoring efforts, focus on metrics like mean time to detect (MTTD) and mean time to respond (MTTR). These indicators help evaluate system performance and highlight areas needing improvement [6]. Such measures also set the stage for thorough post-incident reviews, which we’ll explore next.
Post-Incident Reviews and Vendor Performance Evaluation
When a supply chain issue arises, a structured review process is essential. This involves bringing together teams from security, privacy, legal, compliance, procurement, IT, and vendor management [8][6]. The review should evaluate how the vendor performed against the agreed-upon service level agreements (SLAs), including critical metrics like recovery time objectives (RTO) and recovery point objectives (RPO) outlined in their contract [7]. Documenting what worked, what didn’t, and where gaps exist is key. This documentation helps determine if the vendor met their obligations and identifies areas for improvement.
SOC 2 compliance emphasizes ongoing risk assessments and adapting internal controls based on lessons learned from incidents [9]. Use these reviews to refine your severity tiers, notification protocols, and escalation paths. This ensures that future responses are informed by actual performance data rather than theoretical planning [6].
Auditing and Updating Vendor Agreements
Post-incident reviews should lead to actionable changes in vendor agreements, reinforcing accountability and fostering improvement. SOC 2 standards require continuous oversight of vendors, which means regularly auditing and updating contracts to ensure compliance with third-party risk management policies [8].
These audits shouldn’t just happen when there’s a problem - schedule them at regular intervals. With the healthcare industry facing increasing regulatory pressures, staying ahead of risks requires a proactive approach. Update contracts to incorporate modern controls like least privilege access, network segmentation, and quick credential revocation. These measures might not have been part of the original agreement but are essential for addressing emerging vulnerabilities [6]. Regularly revisiting and revising these agreements ensures that accountability stays front and center throughout the vendor relationship.
Conclusion
Key Takeaways for Healthcare Vendors
Managing vendor supply chain risks is a critical part of protecting patient data and maintaining trust in the healthcare sector. Assigning clear responsibilities - like appointing Security and Privacy Officers - and implementing strict access controls are essential steps. Additionally, ensure your Business Associate Agreements (BAAs) align with the SOC 2 Trust Services Criteria for Security and Availability [6].
To stay ahead, map vendor risks to SOC 2 requirements, create a structured roadmap to address vulnerabilities, and maintain a compliance evidence repository. This repository should document your controls and testing activities, making audits and reviews more efficient [10].
Next Steps for Strengthening SOC 2 Compliance
To build on these practices, take the following steps to refine your SOC 2 compliance approach:
- Evaluate your current processes: Move away from manual spreadsheets to automated risk management tools. Test your incident response plans to ensure they can handle real-world supply chain challenges.
- Leverage automation for sharing security evidence: Tools like Censinet Connect™ allow vendors to share security evidence early in the sales process. This not only builds trust but also helps meet SOC 2 transparency requirements and speeds up deal closures [3].
With SOC 2 Type II increasingly becoming a standard for securing contracts with large healthcare networks and Fortune 500 companies, falling short on compliance can mean losing valuable opportunities [10]. Regular audits and post-incident reviews are vital for strengthening vendor relationships and refining your controls. Schedule these reviews consistently, update contracts to reflect current security standards, and use actual performance data to drive ongoing improvements.
FAQs
Which vendors should we treat as highest risk for PHI exposure?
Vendors with access to sensitive PHI and weak security measures or known vulnerabilities present the greatest risk. This is especially true for third-party vendors connected to critical systems or handling essential data. It's crucial to focus on evaluating these vendors and addressing potential risks to safeguard PHI effectively.
What evidence should we collect during a vendor-caused incident for SOC 2?
During a SOC 2 incident caused by a vendor, it's crucial to gather specific evidence to understand and address the situation effectively. This includes vendor activity logs, system and network monitoring data, breach notifications, access control and authentication logs, and records of response actions and communications. Make sure all documentation is detailed and adheres to your incident response plan to ensure a structured and efficient approach.
How often should we test supply-chain incident response scenarios?
Supply chain incident response scenarios should be tested on a regular basis. Experts suggest running these tests at least once a year to keep response plans effective and ensure teams are prepared to handle potential risks.


