Ultimate Guide to Vendor Compliance Auditing
Post Summary
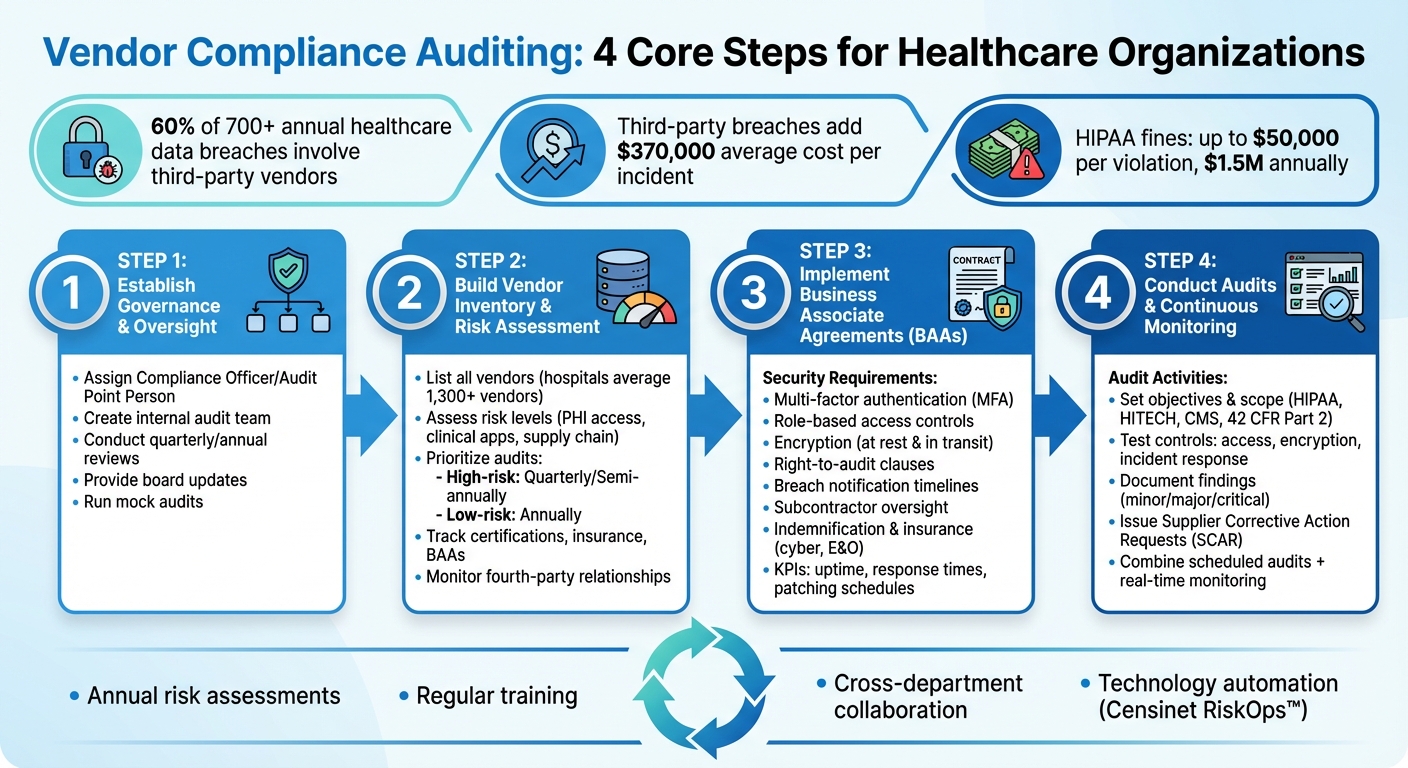
Vendor compliance auditing is critical for healthcare organizations to manage third-party risks, protect sensitive patient data, and meet regulatory requirements like HIPAA, HITECH, and CMS standards. This process ensures vendors follow agreed security practices, reducing risks of data breaches, fines, and reputational harm. Here’s what you need to know:
- Why it matters: Healthcare providers are accountable for vendor compliance, even if breaches occur due to vendor negligence.
- Challenges: Limited resources, evolving regulations, and large vendor networks make compliance management complex.
- Key steps:
- Establish governance with clear oversight roles.
- Build a vendor inventory and assess risks.
- Use Business Associate Agreements (BAAs) to set security requirements.
- Conduct audits, prioritize high-risk vendors, and test controls thoroughly.
- Tools: Technology like Censinet RiskOps™ simplifies audits by automating tasks and providing real-time insights.
Vendor compliance auditing isn’t a one-time task. Combining scheduled audits with continuous monitoring and using clear corrective actions ensures long-term compliance and better protection for patient data.
Healthcare Vendor Compliance Audit Process: 4 Core Steps
Vendor Management In Healthcare: The High Cost of Failing to Triage Your Vendors
sbb-itb-535baee
Core Elements of a Vendor Compliance Audit Program
Creating a solid audit program is a key part of effectively manage third-party risk. To do this, organizations need a structured approach that combines governance, detailed tracking of vendors, and enforceable security requirements.
Setting Up Governance and Oversight
Every strong compliance program begins with leadership. Assigning a Compliance Officer or Audit Point Person ensures someone is responsible for coordinating audits, aligning internal practices with regulatory standards, and maintaining accountability across the organization. An internal audit team can conduct regular reviews, such as quarterly billing checks or annual HIPAA assessments, to catch potential issues early. Dividing responsibilities through internal controls also helps prevent errors or misconduct.
To strengthen oversight, organizations should provide regular updates to the board, reinforcing accountability and enabling timely corrective actions. Mock audits or internal spot checks can also test how well these measures work in practice [4]. Together, these governance practices lay the groundwork for the vendor inventory and risk assessment framework discussed next.
Building a Vendor Inventory and Risk Assessment Framework
A complete vendor inventory is essential for a successful audit program. Organizations should list all vendors, assess their risk levels, and prioritize audits based on factors like access to sensitive data, use of clinical applications, or involvement in supply chains. Vendors with higher risk - such as those handling protected health information (PHI) or critical systems - may need audits quarterly or semi-annually, while lower-risk vendors might only require annual reviews [6,7].
Automated systems can help by tracking vendor certifications, insurance policies, and Business Associate Agreements (BAAs), sending alerts as expiration dates approach. This prevents compliance lapses. Additionally, organizations must monitor fourth-party relationships to ensure compliance requirements extend to subcontractors as needed [5].
Business Associate Agreements and Security Requirements
Business Associate Agreements (BAAs) are the legal foundation of vendor relationships. These agreements should outline both administrative safeguards, like security management processes and workforce training, and physical safeguards, such as controlled facility access and protections for devices handling sensitive data [5]. Security measures like multi-factor authentication (MFA), role-based access, least-privilege access, and encryption (both at rest and in transit) are critical for protecting PHI. This is especially important given that third-party data breaches can add an average of $370,000 to the cost of an incident, with total costs often exceeding $4 million [5].
Key clauses in BAAs include the right-to-audit, which allows organizations to verify vendor compliance through on-site or remote assessments [6,7]. Breach notification clauses should define clear timelines and responsibilities for reporting incidents, while subcontractor oversight provisions ensure HIPAA requirements extend to fourth-party vendors [6,8]. Indemnification and insurance clauses can protect organizations from vendor negligence by specifying required coverage levels for cyber insurance and Errors & Omissions (E&O) [5].
Including a Plan of Action and Milestones (POA&M) helps address vulnerabilities within set deadlines. Measurable KPIs, such as system uptime, incident response times, and patching schedules, ensure clear expectations and accountability [6,8]. These well-structured BAAs set the stage for effective audit execution strategies.
How to Plan and Execute a Vendor Compliance Audit
Once you’ve established governance structures and vendor agreements, it’s time to bring your audit plan to life. A successful audit hinges on clear objectives, solid preparation, and methodical testing of vendor controls.
Setting Audit Objectives and Scope
Start by defining what the audit will cover: the processes, locations, time periods, systems, and regulations involved [1]. For instance, if you’re auditing an EHR vendor, decide whether the focus is on HIPAA Privacy Rule compliance, Security Rule technical safeguards, or both. Use a relevant historical timeframe to sample vendor activities effectively [3].
Not all vendors can be audited at once - especially since hospitals, on average, work with over 1,300 vendors. Prioritize audits based on the risk level identified in your HIPAA-compliant vendor risk management inventory. High-risk vendors, such as those handling PHI, managing clinical applications, or supporting critical supply chain functions, should take precedence. To ensure thorough coverage, assemble a cross-functional team that includes compliance, privacy, security, IT, legal, and clinical leadership [1]. These steps provide a clear roadmap for your audit efforts.
Creating an Audit Plan
Preparation is key. Gather essential documents like policies, BAAs, risk analyses, training records, incident logs, and past audit reports. Assign responsibilities to team members with clear deadlines for collecting and organizing these materials [1]. Use an evidence index to track ownership - assign specific individuals to collect each document, set due dates, and determine where files will be stored [1].
Develop a sampling methodology that’s either statistically or judgmentally valid to keep the audit manageable while ensuring meaningful results [1]. Establish objective pass/fail criteria for each control being tested to ensure results are defensible [1].
Communicate openly with vendors about the audit. Provide advance notice that outlines the purpose, timeline, scope, and required documentation [6]. Similarly, brief internal stakeholders and vendor contacts on the audit’s objectives and timelines [3]. This transparency fosters trust and improves the chances of obtaining accurate and complete information [7]. With this groundwork, you can now focus on executing the audit itself.
Conducting the Audit: What to Test
With your plan in place, it’s time to dive into testing vendor controls. Examine both documentation and operational practices. Review vendor policies for compliance with regulations such as HIPAA Privacy, Security, and Breach Notification Rules; HITECH; CMS requirements; and 42 CFR Part 2 for substance use disorder records. Validate that data-sharing agreements clearly define PHI elements, usage purposes, and retention limits [1].
Go beyond paperwork by conducting walkthroughs and interviews with vendor staff to understand how processes work in practice compared to what’s documented [1]. For high-risk vendors, consider on-site visits to observe operations firsthand, assess physical security, and verify system implementations [6]. For lower-risk vendors, off-site audits with remote record reviews and virtual interviews are often sufficient [6].
Evaluate critical controls such as access management, encryption, multi-factor authentication, and incident response protocols. Look at segregation of duties, access controls, inventory management, and quality assurance processes to spot potential risks like fraud or errors [2]. Document all findings thoroughly, using screenshots, interview notes, and observation records to support your conclusions [3][6].
Analyzing Audit Results and Implementing Corrective Actions
Once testing is complete, the next step is to dive into the findings and tackle any issues head-on. This stage is where your audit work transforms into meaningful steps to reduce risk, rather than just creating another compliance report to file away.
Assessing Findings Against Standards
Start by categorizing your findings into three levels: minor (e.g., incomplete documentation), major (e.g., control failures), and critical (e.g., missing Business Associate Agreements or unreported breaches). Each observation should be carefully compared against the relevant regulatory or policy requirements. Be sure to document the key details: what happened, where it occurred, when it was identified, and which procedure was violated [8].
Once categorized, prioritize the issues not just by their severity but also by the potential financial or operational impact they could have. This prioritization is essential for shaping the corrective actions you’ll take next.
Developing Corrective and Preventive Actions
For every significant finding, create a Supplier Corrective Action Request (SCAR). This document should directly connect the issue to its observation and include:
- A clear description of the required changes
- The individual or team responsible for addressing the issue
- A deadline for completion
- A plan to verify whether the solution is effective
"The party that is ultimately responsible remains the manufacturer... even if it outsources some or all of its manufacturing or other operations." - Ave Love, Staff Writer, MasterControl [8]
This principle is especially critical in healthcare settings. Even if certain operations are outsourced, organizations remain accountable for protecting PHI (Protected Health Information). Work closely with vendors to establish realistic timelines for remediation and, for high-risk findings, implement interim controls. Automated tools can help streamline this process by routing corrective action requests, sending reminders, and escalating overdue tasks. Manual tracking often causes delays, so automation can keep things moving efficiently [8].
Documenting Results for Compliance Records
Once corrective actions are defined, it’s crucial to document every step. This includes the findings, the actions taken, verification of those actions, and closure of the issue. Thorough documentation serves two purposes: it shows regulators that you’ve taken appropriate steps, and it builds a knowledge base for future audits.
Make sure to store all audit-related materials - reports, evidence, vendor communications, and remediation verifications - in one secure, centralized location. Use retention policies that align with regulatory requirements to ensure everything is properly maintained. Your documentation should tell a full story, from the initial observation to the final resolution. This comprehensive approach can provide valuable insights during regulatory reviews or when evaluating the effectiveness of your compliance program.
Using technology can make this process even smoother. Platforms like Censinet RiskOps™ can simplify audit documentation and automate workflows, ensuring your records are well-organized, secure, and easily accessible for any compliance review.
Maintaining Ongoing Compliance and Monitoring
Once vendor audits are completed and analyzed, the next step is keeping compliance and monitoring efforts active. Vendor compliance isn’t a one-and-done task - it’s an ongoing process that demands constant vigilance. Risks associated with vendors can evolve rapidly due to new threats, operational changes, or shifts in regulations. To stay ahead, healthcare organizations must pair regular reviews with real-time monitoring.
Scheduled Audits vs. Continuous Monitoring
Scheduled audits are thorough evaluations conducted annually or on a predetermined timeline. These are particularly useful for meeting regulatory requirements or evaluating high-risk vendors. For instance, a six-month retrospective audit can uncover patterns and gaps by analyzing historical data [3]. However, the drawback of scheduled audits is that they only reflect past events, not real-time developments.
Continuous monitoring fills this gap by offering real-time insights through dashboards, automated alerts, and periodic check-ins. This approach is especially effective for identifying immediate risks, such as cybersecurity breaches or sudden changes in vendor operations [1]. The most effective strategy combines both methods: scheduled audits for in-depth reviews and continuous monitoring to address issues as they arise. Together, they create a proactive and responsive compliance framework.
Using Technology for Compliance Management
Relying on manual processes for tracking compliance is both inefficient and prone to errors. Technology simplifies this by automating repetitive tasks and providing a centralized view of vendor risks. Tools like Censinet RiskOps™ enable healthcare organizations to streamline critical tasks like evidence collection, risk tiering, distributing security questionnaires, and managing Business Associate Agreements (BAAs) - all within a single platform.
Advanced platforms go beyond basic tracking by supporting ongoing risk assessments and benchmarking vendors against industry standards. This not only eases the administrative workload but also enhances the precision and reliability of compliance efforts. By integrating technology, healthcare organizations can better manage vendor risks while freeing up resources for other priorities.
Creating a Culture of Continuous Improvement
Technology alone can’t sustain long-term compliance - human involvement remains essential. A culture of continuous improvement involves analyzing the root causes of issues and applying targeted corrective actions based on those insights [1][9]. Annual updates to enterprise risk assessments, informed by past audits and new threats, ensure the organization stays adaptable.
Regular training and collaboration across departments are equally important. These efforts ensure that everyone understands their role in vendor oversight and contributes to the broader compliance goals. Tracking progress against past audits helps identify strengths and areas for growth [9]. When compliance becomes ingrained in the organization’s practices rather than treated as a checklist, it strengthens the ability to safeguard patient data and maintain regulatory compliance over time.
Conclusion
Healthcare organizations face a critical need to focus on vendor compliance auditing. This process is key to protecting patient safety and meeting regulatory requirements. Alarmingly, third-party vendors are linked to 60% of the more than 700 major healthcare data breaches reported annually, making a well-organized auditing strategy essential [1]. This guide has outlined effective strategies to tackle this challenge.
The move from periodic reviews to continuous monitoring has redefined vendor risk management. By leveraging technology, organizations can automate time-consuming tasks like gathering evidence and completing security questionnaires. Tools such as Censinet RiskOps™ simplify the auditing process, offering real-time insights into vendor compliance and strengthening the protection of patient data, PHI, and supply chains.
Maintaining compliance goes beyond technology - it requires embedding it into the organization's culture. Regular training, collaboration across departments, and yearly risk assessments help ensure that vendor oversight evolves with new threats and regulatory updates. These cultural practices complement technical measures, making vendor compliance a seamless part of daily operations. This integration significantly enhances an organization’s ability to safeguard patient information.
The financial risks of non-compliance are steep. Violations of HIPAA regulations can lead to fines of up to $50,000 per incident, with annual penalties reaching $1.5 million [1][2]. Beyond avoiding fines, effective vendor compliance auditing reduces PHI exposure, prevents billing mistakes, and mitigates operational risks tied to vendors.
FAQs
How do I decide which vendors to audit first?
When deciding which vendors to audit, start by classifying them into risk levels - critical, high, medium, or low. This classification hinges on two main factors: their access to Protected Health Information (PHI) and the significance of the services they provide. Vendors with higher risk levels, especially those labeled as high-risk, should be your first priority. This ensures patient data remains secure and compliance with regulations is maintained.
To guide this process, frameworks like HIPAA, HITRUST, and NIST offer valuable structure. Additionally, platforms like Censinet RiskOps™ can simplify the monitoring and prioritization of these vendors, making the entire process more efficient.
What should a healthcare BAA require from a vendor?
A healthcare Business Associate Agreement (BAA) lays out a vendor’s obligations when it comes to safeguarding Protected Health Information (PHI). It should spell out how PHI can be used, include safeguards required by the HIPAA Security Rule, and specify breach reporting timelines - typically within 24 to 72 hours. Vendors are also responsible for ensuring that any subcontractors they work with comply with HIPAA regulations.
Beyond these basics, the BAA should address key areas like audits, risk assessments, and robust data security practices. This includes measures such as encryption, strict access controls, and workforce training programs, all aimed at keeping patient information secure.
How can we keep vendor compliance up to date between audits?
Healthcare organizations can stay on top of vendor compliance by adopting continuous monitoring strategies. This means keeping a close watch on vendor risks, compliance, and security controls - in real time. Tools like Censinet RiskOps™ make this easier by providing automated oversight, helping organizations respond quickly to potential issues.
Key practices include routinely reviewing security protocols, performing risk assessments, and using AI-powered tools for predictive analysis. These approaches help detect potential threats early. Automated tracking systems and dashboards also play a crucial role, streamlining compliance efforts and cutting down on manual work. This proactive approach ensures vendors align with regulations while reducing the burden on internal teams.


