How Vendor Access Impacts Healthcare Cybersecurity
Post Summary
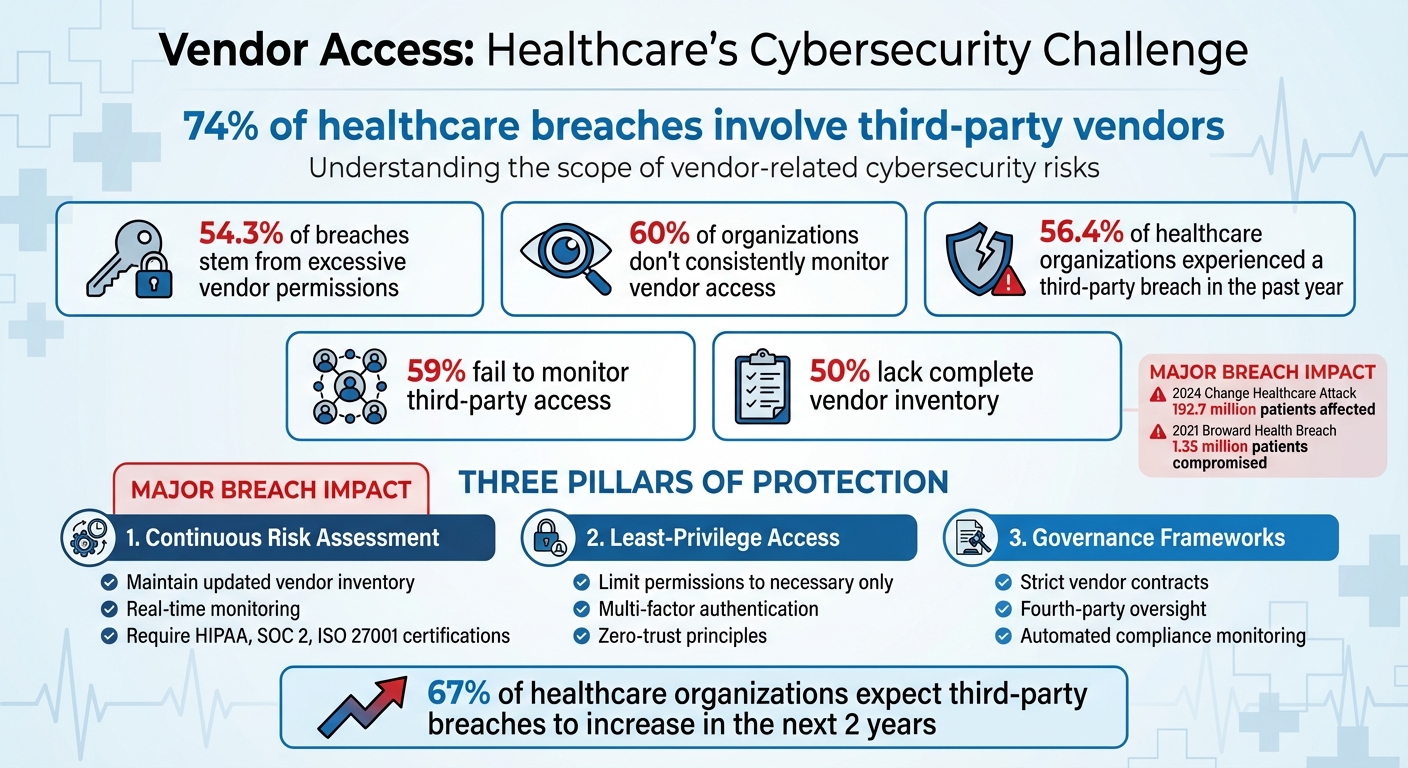
Healthcare cybersecurity is heavily influenced by third-party vendors, with 74% of incidents involving them. These vendors often require access to sensitive systems, making them prime targets for cyberattacks. Poorly managed access can lead to breaches, operational disruptions, and risks to patient care, as seen in high-profile cases like the 2024 Change Healthcare attack affecting 100 million individuals.
Key Takeaways:
- 74% of breaches involve vendors: Many vendors use outdated systems or lack strong security measures.
- Over-privileged access is a major risk: 54.3% of breaches stem from excessive vendor permissions.
- Lack of monitoring: 60% of healthcare organizations don’t consistently track vendor access.
- Fourth-party risks: Subcontractors often add hidden vulnerabilities.
Solutions:
- Continuous Risk Assessments: Maintain an updated inventory of vendors and monitor access in real-time.
- Least-Privilege Access Controls: Limit vendor permissions to only what’s necessary.
- Governance Frameworks: Use strict contracts and enforce compliance with security standards like HIPAA.
By addressing these vulnerabilities with better monitoring, access controls, and governance, healthcare organizations can protect sensitive data and ensure uninterrupted patient care.
Healthcare Vendor Cybersecurity Statistics and Risk Factors
HIMSS24 | Creating Cyber Resilience: Your Guide to Vendor Risk Management
sbb-itb-535baee
Challenges of Managing Vendor Access in Healthcare
Managing vendor access in healthcare is no small task. With the growing number of vendors and the intricate web of modern healthcare IT systems, organizations face mounting challenges in addressing vulnerabilities.
Security Gaps from Excessive Vendor Access
One of the biggest hurdles is the risk created by granting vendors too much access. When vendors receive permissions beyond what they actually need, every extra privilege becomes a potential gateway for cyberattacks. Alarmingly, 59% of organizations fail to monitor third-party access, leaving critical blind spots for IT teams to address[3]. These teams often spend countless hours trying to identify and mitigate vulnerabilities caused by such gaps. Shared credentials, instead of individual user authentication, further muddy the waters. This practice makes it nearly impossible to track who accessed systems and when. Adding to the challenge, healthcare organizations must also navigate the risks posed by subcontractors - commonly referred to as fourth-party access.
Managing Fourth-Party Risks
Fourth-party risks amplify the complexities of vendor management. When a primary vendor outsources tasks to subcontractors, these third parties may gain access to sensitive systems and data without adequate oversight. As Maria Phillips, Senior Counsel for Privacy & Compliance at Imprivata, explains:
"Third-party involvement in data breaches has nearly doubled this year from 15 percent to nearly 30 percent... A critical gap remains that many organisations overlook: fourth-party risk."[3]
Without a thorough inventory of vendors and their subcontractors, organizations struggle to monitor and control downstream access, leaving them exposed to hidden vulnerabilities.
Effects on Patient Care and Operations
The consequences of vendor access breaches go far beyond stolen data - they can disrupt patient care and essential operations. Ransomware attacks, for instance, can cripple Electronic Health Records and decision support tools, cutting off providers from critical patient information. This interruption increases the likelihood of medication errors, misdiagnoses, and delayed treatments. In some cases, system outages force hospitals to halt email communications or even divert emergency patients due to lost access to vital health records. Because healthcare systems are so interconnected, a single vendor breach can cascade across departments, causing life-threatening delays in treatment.
How to Reduce Vendor-Related Cybersecurity Risks
Healthcare organizations face critical challenges in protecting sensitive data from vendor-related breaches. With 56.4% of healthcare delivery organizations experiencing third-party access breaches in the past year and 54.3% of these incidents linked to excessive privileged access, it’s clear that stronger defenses are urgently needed[6].
Conducting Continuous Vendor Risk Assessments
Proactive risk assessment is essential for addressing these vulnerabilities. Unfortunately, many healthcare organizations fall short - half lack a complete inventory of third-party vendors and don’t consistently monitor vendor access to sensitive data. This lack of visibility creates opportunities for undetected threats to take hold[1].
To close these gaps, organizations should maintain up-to-date records of vendors, detailing their system access, permissions, and involvement with critical applications like EHRs or medical devices. Before onboarding, vendors should meet baseline security standards by providing certifications such as HIPAA, SOC 2, or ISO 27001. Once approved, continuous monitoring is necessary to detect vulnerabilities, unusual behavior, or potential breaches in real time[8][5].
A key strategy is risk prioritization based on clinical impact. Not all vendor relationships carry the same level of risk. For example, vendors with access to infusion pumps or clinical decision support tools pose a greater threat to patient safety than those managing administrative systems. Security teams can focus their efforts on high-risk areas by linking vulnerabilities to assets critical to patient care[5].
Applying Least-Privilege Access Controls
Excessive access remains one of the most significant risks in vendor security. A glaring example is the 2021 Broward Health breach, where a third-party provider with broad access compromised the data of 1.35 million patients[7].
Implementing least-privilege access controls ensures vendors are granted only the permissions they need to perform their tasks - nothing more. This approach incorporates multi-factor authentication, network segmentation, and zero-trust principles, dynamically adjusting access based on identity, device security, and real-time risk levels[5].
The importance of limiting access is underscored by the Change Healthcare breach in 2024, which affected 192.7 million patients due to vendor vulnerabilities. By restricting access, organizations can significantly reduce the potential damage from breaches[4][7].
However, enforcement remains a challenge. Many healthcare organizations still rely on shared credentials instead of individual authentication, making it difficult to track access activity. Mapping vendor access to critical systems and monitoring for unusual patterns can help contain threats before they spread. Additionally, automation can simplify risk management across complex vendor networks[7].
Using Automation for Risk Management
Effective risk management in today’s healthcare environment requires speed and scale, something manual processes simply can’t provide. Despite this, 53% of organizations still rely on manual monitoring for third-party access, leaving them ill-equipped to detect and respond to threats quickly[6].
Automation offers a solution. Platforms like Censinet RiskOps™ enable healthcare organizations to conduct automated risk assessments, maintain real-time visibility into vendor connections, and streamline risk management processes. These tools are specifically designed for healthcare, addressing risks tied to patient data, PHI, clinical applications, medical devices, and supply chains - all while easing the workload on security teams[5][6].
| Feature | Manual Monitoring | Automated RiskOps™ Platforms |
|---|---|---|
| Assessment Frequency | Periodic snapshots | Continuous, real-time monitoring |
| Scalability | Difficult to manage 1,000+ vendors | Repeatable workflows for all vendors |
| Data Accuracy | Prone to manual errors and outdated info | Real-time data and automated updates |
| Visibility | Siloed; lack of transparency | Centralized; transparent for all stakeholders |
Automation doesn’t just save time - it enables faster threat detection and containment while boosting compliance confidence. With two-thirds of healthcare organizations expecting a rise in third-party breaches over the next two years[6], automated platforms provide the efficiency and scalability needed to stay ahead of evolving risks, all without compromising patient care.
Building Governance Frameworks for Vendor Risk Management
Governance frameworks transform vendor management from a reactive process into a proactive shield. With over 80% of stolen protected health information tracing back to third-party vendors [7], healthcare organizations must implement structured policies that establish accountability right from vendor onboarding. John Riggi of the American Hospital Association highlights that a hospital's security is only as strong as its weakest vendor, emphasizing the need for comprehensive third-party oversight. This includes strict access controls and leveraging threat intelligence to combat ransomware risks that could jeopardize patient safety [1][2]. A structured framework ties earlier risk evaluations to actionable measures in contracts and vendor collaboration.
Setting Vendor Selection and Contract Requirements
Vendor contracts act as a critical frontline defense against cybersecurity threats. To ensure this, organizations should define clear security standards during vendor selection. This involves using standardized questionnaires to evaluate a vendor’s security protocols, incident response strategies, and audit capabilities. Only vendors with a demonstrated cybersecurity track record - such as adherence to HIPAA, NIST guidelines, or continuous monitoring practices - should be considered [1][6].
Contracts play a pivotal role in enforcing security measures. These agreements should include:
- Service Level Agreements (SLAs) mandating data encryption, timely breach reporting, audit rights, and penalties for non-compliance.
- Clauses addressing fourth-party risks, requiring vendors to enforce equivalent security protocols with their subcontractors. This includes shared risk assessments and breach notification chains, as highlighted in the Broward Health breach [7][1].
- Detailed access control provisions, such as just-in-time provisioning and role-based restrictions that limit vendors to specific systems. For example, billing vendors should not have unrestricted access to electronic health records (EHRs). Automatic de-provisioning after project completion is also essential.
- Requirements for multi-factor authentication and behavioral monitoring to mitigate risks, particularly in patient-critical systems like infusion pumps, where persistent and poorly documented access can lead to vulnerabilities [5][6].
Working with Vendors on Risk Management
Beyond contracts, collaboration with vendors is a key element of robust risk management. Healthcare organizations should engage vendors through joint risk workshops, share threat intelligence, and co-create access policies that strike a balance between security and operational efficiency. Tools like Censinet RiskOps™ enhance this collaboration by providing real-time visibility and automating the enforcement of least-privilege access across vendor networks [1][5].
Centralized and cross-functional oversight ensures standardized policies and reduces reliance on manual monitoring. This approach addresses common challenges such as resource shortages (affecting 45% of organizations) and oversight gaps (impacting 53%). With two-thirds of healthcare delivery organizations expecting an increase in third-party breaches over the next two years [6], combining rigorous contract terms with collaborative vendor relationships is essential. When integrated with continuous risk assessment and least-privilege access controls, these governance frameworks strengthen cybersecurity across vendor ecosystems and reduce vulnerabilities in healthcare operations.
Conclusion: Improving Cybersecurity Through Better Vendor Access Management
Healthcare organizations are grappling with a stark challenge: more than 56% of healthcare delivery organizations reported a third-party breach in the past year, with 54% of those breaches tied to excessive privileged access [6]. Addressing this issue requires putting three key defenses into action - continuous monitoring, least-privilege access controls, and strong governance frameworks.
Real-time monitoring plays a crucial role in closing security gaps that can delay breach detection and increase risks to patients. Alarmingly, only 40% of organizations actively monitor third-party access to sensitive data [5]. This lack of oversight leaves systems vulnerable to unauthorized access. Automated tools can help by spotting threats early across IT systems, IoT devices, and clinical environments, minimizing disruptions to patient care.
On top of monitoring, robust access controls are vital. Implementing least-privilege access ensures vendors only have the permissions they need, preventing unnecessary overreach. Many vendors retain access they no longer require [5]. By dynamically adjusting permissions based on identity, device security, and real-time risk factors, healthcare organizations can minimize the impact of breaches while staying compliant with HIPAA’s access control standards [5].
These efforts are further strengthened by governance frameworks that prioritize accountability. Contracts should mandate certifications like HIPAA, SOC 2, and ISO 27001, and include breach notification protocols [8]. Tools such as Censinet RiskOps™ simplify ongoing risk assessments and promote collaboration between healthcare organizations and their vendors [6]. Together, these strategies align with industry standards to protect sensitive patient data and ensure care continuity.
The risks go far beyond financial penalties or revenue loss. As John Riggi from the American Hospital Association puts it, healthcare security is "only as secure as the weakest link" in vendor networks [1]. With two-thirds of healthcare organizations anticipating an increase in third-party breaches [6], implementing layered security measures - combining continuous monitoring, restricted access, and rigorous governance - is essential to safeguarding patient data and maintaining uninterrupted care delivery.
FAQs
What vendor access should be restricted first?
Restricting vendor access should start with high-risk vendors - those who hold extensive permissions, handle sensitive data, or have access to critical systems. By limiting these access points, you can lower the risk of security breaches and minimize potential disruptions to operations.
How can we discover and track fourth-party access?
Healthcare organizations can keep track of and evaluate fourth-party access by using tools designed for continuous monitoring and risk assessment. Automated solutions, such as Censinet RiskOps™, play a key role in spotting vulnerabilities, monitoring vendor activities, and ensuring compliance throughout the third-party network. These tools provide a streamlined way to handle risk effectively.
What should vendor contracts require for cybersecurity?
Vendor contracts in healthcare must prioritize security measures to protect sensitive data. These should include encryption protocols, multi-factor authentication, and rapid breach notification requirements. Additionally, contracts should clearly outline security responsibilities between parties.
Key elements to incorporate are audit rights to verify compliance, liability clauses to address accountability, and adherence to HIPAA regulations and other applicable laws. By addressing these areas, healthcare organizations can strengthen their cybersecurity posture and mitigate risks effectively.


