Internal Audit Best Practices for CMMC in Healthcare
Post Summary
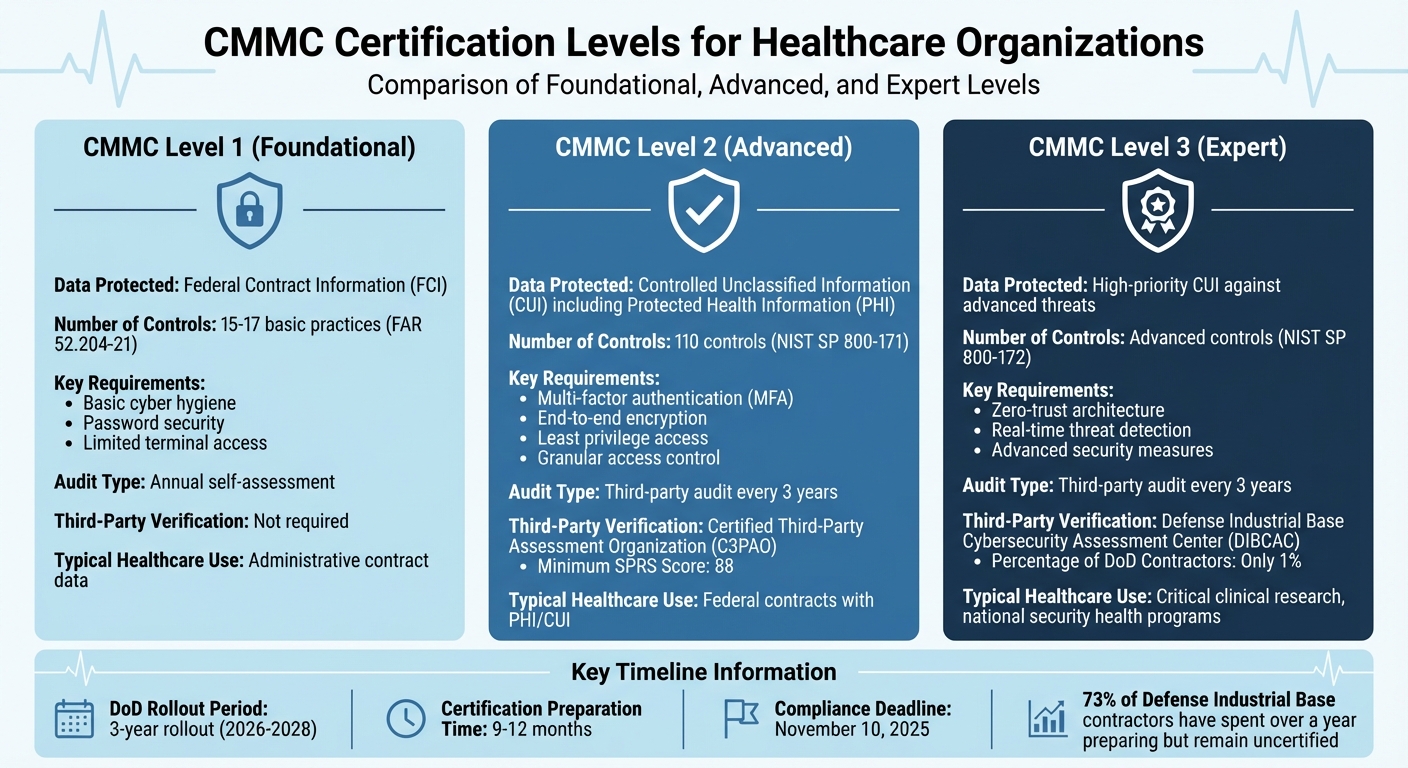
The Cybersecurity Maturity Model Certification is a DoD framework requiring all Department of Defense contractors to meet specific cybersecurity standards, with compliance required beginning November 10, 2025. Healthcare organizations with DoD contracts — including those involved in medical research, telehealth programs, clinical trials with federal funding, and health IT contracts with the DoD — must comply. Non-compliance results in losing eligibility for DoD contracts. CMMC has three levels: Level 1 for contractors handling Federal Contract Information, Level 2 for those handling Controlled Unclassified Information including PHI in federal contracts, and Level 3 for organizations working with high-priority CUI in national security contexts, affecting approximately 1% of all DoD contractors.
Level 1 requires 15 to 17 basic practices from FAR 52.204-21 covering basic cyber hygiene such as password security and terminal access limitation, with annual self-assessment and no third-party verification required. Level 2 requires 110 controls based on NIST SP 800-171, including MFA, end-to-end encryption, and least-privilege access, with a third-party audit conducted by a Certified Third-Party Assessment Organization every three years. Level 3 requires NIST SP 800-172 controls including zero-trust architecture and real-time threat detection, with audits conducted by the Defense Industrial Base Cybersecurity Assessment Center every three years — affecting only approximately 1% of all DoD contractors, primarily those in critical clinical research or national security health programs.
HIPAA focuses on PHI protection while CMMC enforces stricter and more formal standards for access control, auditing, encryption, and incident response. Healthcare organizations often assume that existing HIPAA policies satisfy CMMC requirements, only to discover that CMMC requires more granular access controls, more detailed audit logging, stronger encryption standards, and more formal incident response planning than HIPAA mandates. In 2023, the average healthcare data breach cost $10.93 million per incident while ransomware attacks on healthcare providers surged over 94% since 2021. Healthcare organizations must map CUI flows, implement network segmentation separating CUI-related systems from clinical and administrative networks, and ensure subcontractors handling CUI comply with flow-down clauses as prime contractors remain accountable for vendor compliance.
A gap analysis begins by defining the CUI boundary and documenting all data flows within that boundary, then evaluating current controls against all 110 NIST SP 800-171 Rev 2 requirements for Level 2. Identified gaps should be ranked high, medium, or low to prioritize remediation, with special attention to five-point controls that have the greatest influence on the SPRS score, which starts at 110 points. Level 2 certification requires a minimum SPRS score of 88 and resolution of all controls that cannot be deferred to a Plan of Action and Milestones. Small environments may complete a gap analysis in two to four weeks; multi-site healthcare organizations may require 12 weeks or more. The gap analysis must validate that systems controls are functioning — not merely check documentation boxes.
A SIEM system correlating security event logs provides auditors with evidence that controls are functioning as intended. A traceability matrix mapping logs and policies to each CMMC control ensures complete coverage that can be demonstrated during formal assessment. CloudTrail, GuardDuty, or Azure Activity Logs should be used to maintain log coverage across the asset inventory. Access control testing must verify MFA enforcement across all administrative groups through authenticator logs, review privileged access rights, and test offboarding workflows to confirm access is revoked promptly when roles change. Encryption testing should scan for misconfigured storage buckets and generate KMS audit logs demonstrating encryption at rest and in transit. Incident response plans must be validated through cybersecurity drills that simulate recovery scenarios and verify backup operability and key rotation.
Censinet RiskOps™ uses standards-based questionnaires aligned with NIST CSF and HICP that map directly to CMMC requirements, enabling internal audits that match the controls C3PAO assessors will evaluate during formal certification. Baptist Health in Jacksonville replaced manual processes across six acute care hospitals and 14,250 staff with Censinet RiskOps™, bringing consistency, time savings, and collaboration across the health system. Tower Health used Censinet RiskOps™ AI-driven capabilities to automate evidence validation and risk mapping, scaling audits while improving data accuracy. Automated evidence validation identifies gaps in NIST SP 800-171 controls before assessors do, and collaborative workflows route issues to appropriate stakeholders for remediation tracking.
Healthcare organizations working with the Department of Defense (DoD) must meet Cybersecurity Maturity Model Certification (CMMC) standards starting November 10, 2025. Non-compliance can result in losing eligibility for DoD contracts. Internal audits are critical for preparing healthcare contractors for these stringent requirements, especially as third-party assessments replace self-certification.
Key points to know:
Healthcare providers must prioritize internal audits to safeguard sensitive data, meet DoD standards, and avoid contract disruptions.
How to Complete Your CMMC Self-Assessment and Get Audit Ready
sbb-itb-535baee
CMMC Levels and What They Require for Audits
CMMC Levels 1-3 Requirements and Audit Processes for Healthcare Organizations
CMMC Levels 1, 2, and 3: What Each Level Requires
The Cybersecurity Maturity Model Certification (CMMC) framework organizes cybersecurity requirements into three levels, each with specific audit processes. Here's how they break down:
The DoD plans a three-year rollout (2026–2028) for CMMC compliance, with certifications typically taking 9–12 months to complete. Interestingly, 73% of Defense Industrial Base contractors have spent over a year preparing but remain uncertified [2]. These timelines and requirements significantly influence how healthcare organizations secure sensitive data.
Connecting CMMC Controls to Healthcare Data Protection
The connection between CMMC controls and healthcare data protection becomes clearer when considering the unique challenges healthcare organizations face. A common misconception is that HIPAA compliance alone meets CMMC standards. However, this assumption can leave critical gaps. As Coalfire Federal points out:
"HIPAA focuses on protected health information (PHI), which may also be classified as CUI in federal contracts. Organizations may assume that existing policies are sufficient, only to find that CMMC requires more granular access control, auditing, encryption, and incident response planning"
.
The stakes are high. In 2023, the average cost of a healthcare data breach hit $10.93 million per incident, while ransomware attacks on healthcare providers surged by over 94% since 2021 [2]. While HIPAA addresses PHI, CMMC enforces stricter and more formal standards for access, auditing, encryption, and incident response [1].
To prepare, healthcare organizations must map the flow of CUI to pinpoint where DoD-funded research data or other CUI is stored, processed, or transmitted. Many hospitals are adopting network segmentation to separate CUI-related systems from general administrative networks. This reduces the scope of CMMC audits by clearly defining the "assessment boundary" in environments where clinical, research, and administrative systems often overlap [1].
Third-party risk management further complicates compliance. Healthcare systems often rely on external providers for electronic health records (EHR), telehealth services, and medical devices. Organizations must ensure subcontractors handling CUI comply with flow-down clauses, as prime contractors remain accountable for vendor compliance [1].
How to Conduct Effective Internal CMMC Audits
Running Gap Analyses to Find Compliance Weaknesses
A gap analysis is your first step toward identifying how your current cybersecurity measures stack up against the 110 requirements outlined in NIST SP 800-171 Rev 2 for Level 2 compliance [6]. Start by clearly defining your Controlled Unclassified Information (CUI) boundary and documenting data flows. Once that's done, rank identified risks as high, medium, or low to prioritize remediation efforts. Pay special attention to "five-point" controls, as these have the greatest influence on your Supplier Performance Risk System (SPRS) score, which begins at 110 points [6]. This process ensures you're validating system controls, not just checking off documentation boxes. As Emily Bonnie, Senior Content Marketing Manager at Secureframe, puts it:
"The most expensive mistake in a CMMC gap analysis is treating it as a documentation exercise instead of a systems validation exercise."
For small environments, this analysis might take two to four weeks. Larger organizations, such as multi-site healthcare providers, may need 12 weeks or more [6]. Achieving a Level 2 certification requires a minimum SPRS score of 88 and the resolution of all controls that cannot be deferred to a Plan of Action and Milestones (POA&M) [6].
Once gaps are identified and risks are prioritized, the next step is to implement monitoring systems that validate your controls.
Setting Up Logging and Monitoring Systems
After pinpointing compliance gaps, the focus shifts to implementing effective logging and monitoring systems. A Managed Security Information and Event Management (SIEM) system can help correlate security event logs, providing auditors with clear evidence that your controls are functioning as intended [8]. To streamline this process, create a traceability matrix that maps logs and policies to each CMMC control. Regularly review the coverage of these logs against your asset inventory using tools like CloudTrail, GuardDuty, or Azure Activity Logs [4][9]. As IS Partners emphasizes:
"It's not enough to say you're secure - you need to show it through policies, logs, and proof of implementation."
Remember, while certification is only required every three years, maintaining compliance is a continuous effort. Conduct formal reviews annually or whenever there are significant system changes [6].
Testing Access Controls, Encryption, and Incident Response Plans
With your logging framework in place, it's time to rigorously test access controls, encryption measures, and incident response plans. These tests ensure that your controls remain effective over time. Use audit findings to guide targeted testing. For instance, verify that critical controls like Multi-Factor Authentication (MFA), access rights, encryption, and incident response are functioning as required. For MFA, check authenticator logs to confirm enforcement across all administrative groups [9]. Regularly review privileged access and test workflows to ensure access rights are updated promptly when roles change or employees leave [9].
Encryption testing should involve scanning for misconfigured storage buckets or open security groups. Generate Key Management Service (KMS) audit logs to demonstrate encryption both at rest and in transit [9][10]. For incident response, conduct cybersecurity drills to simulate recovery scenarios. These drills validate that backups are operational and that key rotation is happening as planned [9][10]. Additionally, running internal or third-party mock assessments before formal certification can help you practice responding to assessor questions and identify any documentation gaps [5].
The entire journey, from the initial gap analysis to achieving certification, generally takes nine to twelve months for most organizations. The formal CMMC Level 2 assessment itself typically lasts four to six weeks [5][6].
Using Censinet RiskOps to Simplify Internal Audits

Censinet RiskOps Features for Healthcare Compliance
Relying on spreadsheets to manage CMMC audits often leads to version control headaches and inconsistent data. Censinet RiskOps™ eliminates these issues by introducing automated workflows tailored for healthcare organizations aiming for CMMC compliance [7][11].
The platform uses standards-based questionnaires, such as NIST CSF and HICP, that align seamlessly with CMMC requirements [7]. This ensures your internal audits match the controls assessors will review during formal certification. For example, Baptist Health in Jacksonville, Florida, under the leadership of VP/CISO James Case, replaced manual processes with Censinet RiskOps across six acute care hospitals and a workforce of 14,250. This shift not only saved time on risk assessments but also brought consistency across the entire health system [7].
With its centralized platform, teams can collaborate on assessments while maintaining a single, accurate source of truth. Additionally, the tool allows organizations to benchmark their security posture against other healthcare entities within the Censinet community, ensuring readiness for formal CMMC evaluations [7]. A Team Lead in Information Security at Baptist Health highlighted the platform's benefits:
"Censinet's customer service is great and responsive... the tool is centralized, collaborative, and reliable – it gives me the ability to share internally and the flexibility to pick up where I left off."
These collaborative advantages are further enhanced by advanced automation, which simplifies the audit process even more.
Using AI and Automation to Speed Up Audits
Automation plays a key role in maintaining continuous CMMC compliance. Tower Health previously relied on spreadsheets for third-party risk assessments, which limited their efficiency [11][12]. By adopting Censinet RiskOps, they leveraged AI-driven capabilities to automate evidence validation and risk mapping. This allowed them to scale their audits while improving the accuracy of their data.
A standout feature is automated evidence validation, which identifies gaps in NIST SP 800-171 controls before assessors do. This gives organizations the chance to address issues proactively, mapping findings to established security practices and clearly linking controls to CMMC requirements [4][5]. By automating repetitive tasks, the platform frees up your team to focus on strategic remediation efforts.
For healthcare organizations juggling risks across clinical applications, medical devices, and supply chains, automation ensures the continuous monitoring required by CMMC without the need for additional staff. When issues arise, the platform's collaborative workflows automatically route them to the appropriate stakeholders, keeping remediation efforts on track and aligned with organizational goals.
Documenting Audit Results and Fixing Issues
Ranking Risks and Setting Fix Priorities
When documenting audit findings, it's essential to create a formal report that outlines nonconformances and provides clear recommendations for remediation.
However, not all gaps are equally urgent. Healthcare organizations must have a structured system to rank risks and assign appropriate timelines for fixing them. The table below highlights how findings can be categorized and who is responsible for addressing them:
Risk Category
Description
Recommended Remediation Timeline
Responsibility
Missing critical controls like MFA or encryption, posing a direct threat to CUI/FCI.
Immediate to 30 Days
CISO / IT Director
Incomplete implementation of NIST 800-171 controls or documentation gaps.
30 to 90 Days
System Administrator
High-risk issues demand immediate attention because they directly jeopardize the security of Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). Medium-risk issues, while less urgent, often involve incomplete documentation or partially implemented controls that could fail a formal assessment.
To manage these deficiencies effectively, use a Plan of Action and Milestones (POA&M). This document should stay up-to-date and track all remediation efforts. Additionally, incorporate a traceability matrix that links each CMMC control to relevant evidence, such as logs, screenshots, or policy documents.
Once the risks are ranked and remediation priorities are set, the next step is to develop a detailed compliance plan to ensure long-term security and readiness.
Creating a Long-Term Compliance Plan
After addressing immediate risks, it's crucial to shift focus toward a proactive and sustainable compliance strategy. Using the audit findings and the risk rankings as a foundation, your System Security Plan (SSP) should detail how each NIST 800-171 control is implemented. This document should also be updated regularly to reflect any changes in systems or risks.
Conduct internal audits on a regular schedule - monthly or quarterly - using a checklist aligned with official CMMC assessment criteria. Follow up three to six months after corrective actions to verify that compliance is being maintained. This ongoing process not only avoids surprises during formal certification but also helps catch recurring issues before they grow into larger problems.
Automation can significantly ease the burden of maintaining compliance. Tools like GRC software can create time-stamped, unalterable audit trails of system activities. A continuous monitoring plan should also be established, specifying roles, automated tools (such as SIEM or EDR), and alert thresholds. This approach shifts the organization’s focus from periodic audit preparation to constant readiness, ensuring consistent oversight without overloading the team.
Healthcare organizations face unique challenges when it comes to documentation. Beyond CMMC requirements, they must also meet CMS regulations, which include proving "medical necessity" and maintaining patient consent records. Documentation failures are a common reason for audit issues in programs like Chronic Care Management (CCM). For example, claim denial rates can climb as high as 4.8%. On the flip side, well-documented care management programs can reduce hospital readmission rates by 21% [13].
Conclusion
Internal audits play a key role in achieving strong CMMC compliance within the healthcare sector. They replace unreliable manual processes with standardized, dependable methods for managing risk. For instance, organizations such as Baptist Health and Tower Health successfully transitioned from chaotic spreadsheets to efficient, automated risk assessments by adopting tools like Censinet RiskOps [7][11].
This shift leads to more proactive cybersecurity practices, allowing organizations to address vulnerabilities before they escalate into serious breaches. Regular audits not only close cybersecurity gaps but also prepare healthcare providers for formal CMMC certification. This ensures the protection of critical care operations against cyberattacks while safeguarding sensitive patient data [12]. Moreover, automation enables more comprehensive risk management, evaluating a broader range of vendors and systems without increasing workload.
Centralized tools, like Censinet RiskOps, further enhance audit processes by streamlining workflows and improving tracking. As noted by a Team Lead for Information Security at Baptist Health:
"Censinet's customer service is great and highly responsive, which is uncommon; moreover, the tool is centralized, collaborative, and reliable – it gives me the ability to share internally and the flexibility to pick up where I left off"
.
FAQs
How do I determine our CUI boundary for a CMMC audit?
To figure out your Controlled Unclassified Information (CUI) boundary for a CMMC audit, start by conducting a scope analysis. This involves identifying all the systems, data, and processes that handle CUI. Pay close attention to areas where CUI is created, stored, transmitted, or processed.
Next, map your organization’s assets to the specific CMMC requirements. This step ensures you know exactly how and where CUI interacts with your systems. Dive into your data flows and system architecture to get a clear picture of how information moves through your organization.
It’s also a good idea to bring in cross-functional teams during this process. Their input can help you document your boundaries in detail and ensure nothing is overlooked. Make sure everything aligns with frameworks like NIST SP 800-171 to avoid any compliance gaps. Clear documentation is key to staying on track.
What evidence will auditors expect for Level 2 controls?
Auditors need to see clear and tangible proof that Level 2 controls are not just in place but are actively monitored and reviewed on a regular basis. This means having documentation like:
Make sure all these materials clearly show a pattern of consistent compliance and continuous oversight.
How can we maintain CMMC compliance between three-year assessments?
To maintain compliance with CMMC between assessments, it's essential to focus on proactive risk management and continuous monitoring. Start by performing regular gap analyses to identify areas that need improvement. Keeping detailed documentation is equally important, as it helps track compliance efforts and demonstrates adherence to standards.
Leverage tools like Censinet RiskOps™ to simplify the process of managing security controls and tracking compliance. Regularly train your staff to stay updated on the latest requirements and best practices. Forming cross-functional oversight teams can also enhance accountability and ensure a more comprehensive approach to compliance.
Using standardized questionnaires, such as those based on NIST CSF, can help you assess and confirm adherence to required standards. Additionally, automation can play a big role - streamlining audits, monitoring third-party risks, and addressing vulnerabilities as they arise in real-time.
Related Blog Posts
- Best Practices for DevSecOps in Healthcare IT
- 5 Steps for Post-Audit Cloud PHI Remediation
- SOC 2 Risk Plans: Monitoring Best Practices
- CMMC Maintenance Requirements: 2025 Updates for Healthcare
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":[{"@type":"Question","name":"How do I determine our CUI boundary for a CMMC audit?","acceptedAnswer":{"@type":"Answer","text":"<p>To figure out your Controlled Unclassified Information (CUI) boundary for a CMMC audit, start by conducting a <strong>scope analysis</strong>. This involves identifying all the systems, data, and processes that handle CUI. Pay close attention to areas where CUI is created, stored, transmitted, or processed.</p> <p>Next, map your organization’s assets to the specific CMMC requirements. This step ensures you know exactly how and where CUI interacts with your systems. Dive into your data flows and system architecture to get a clear picture of how information moves through your organization.</p> <p>It’s also a good idea to bring in cross-functional teams during this process. Their input can help you document your boundaries in detail and ensure nothing is overlooked. Make sure everything aligns with frameworks like <strong>NIST SP 800-171</strong> to avoid any compliance gaps. Clear documentation is key to staying on track.</p>"}},{"@type":"Question","name":"What evidence will auditors expect for Level 2 controls?","acceptedAnswer":{"@type":"Answer","text":"<p>Auditors need to see <strong>clear and tangible proof</strong> that Level 2 controls are not just in place but are actively monitored and reviewed on a regular basis. This means having documentation like:</p> <ul> <li><strong>Policies and procedures</strong> that outline the controls.</li> <li><strong>System logs</strong> showing activity and compliance.</li> <li><strong>Screenshots</strong> as visual evidence of implementations.</li> <li><strong>Training records</strong> to confirm employee awareness and involvement.</li> <li><strong>Periodic review reports</strong> that highlight ongoing evaluations.</li> </ul> <p>Make sure all these materials clearly show a pattern of consistent compliance and continuous oversight.</p>"}},{"@type":"Question","name":"How can we maintain CMMC compliance between three-year assessments?","acceptedAnswer":{"@type":"Answer","text":"<p>To maintain compliance with CMMC between assessments, it's essential to focus on <strong>proactive risk management</strong> and <strong>continuous monitoring</strong>. Start by performing regular gap analyses to identify areas that need improvement. Keeping detailed documentation is equally important, as it helps track compliance efforts and demonstrates adherence to standards.</p> <p>Leverage tools like <strong>Censinet RiskOps™</strong> to simplify the process of managing security controls and tracking compliance. Regularly train your staff to stay updated on the latest requirements and best practices. Forming cross-functional oversight teams can also enhance accountability and ensure a more comprehensive approach to compliance.</p> <p>Using standardized questionnaires, such as those based on <strong>NIST CSF</strong>, can help you assess and confirm adherence to required standards. Additionally, automation can play a big role - streamlining audits, monitoring third-party risks, and addressing vulnerabilities as they arise in real-time.</p>"}}]}
Key Points:
What is CMMC, when does it apply to healthcare organizations, and what are the consequences of noncompliance?
- November 10, 2025 compliance deadline with DoD contract eligibility at stake — The Cybersecurity Maturity Model Certification framework requires all DoD contractors to meet specific cybersecurity standards beginning November 10, 2025. Healthcare organizations that lose CMMC certification or fail to achieve it lose eligibility for DoD contracts — a consequence that directly threatens the revenue and research partnerships that federal healthcare contracts represent.
- Three-year DoD rollout covering 2026 through 2028 — The DoD plans a three-year rollout for CMMC compliance requirements, phased across contract types and contractor categories. Healthcare organizations cannot delay preparation on the assumption that enforcement is distant — the 9 to 12 month certification preparation timeline means organizations that begin preparation in 2025 will be completing certification in 2026 at the earliest.
- 73% of DIB contractors spending over a year preparing but still uncertified — The documented experience of Defense Industrial Base contractors — with nearly three-quarters spending over a year preparing but remaining uncertified — establishes that CMMC compliance is materially more demanding than many organizations anticipated at the outset and that internal audit readiness is a genuine operational challenge requiring structured methodology.
- Healthcare-specific CMMC applicability extends beyond military medicine — CMMC applies to healthcare organizations that handle DoD-funded research data, participate in federal clinical trial programs, provide health IT services under DoD contracts, operate telehealth programs for military populations, or serve as subcontractors to prime DoD contractors in any of these capacities. The scope is broader than organizations focused on direct clinical care typically recognize.
- CUI identification as the compliance scope-defining activity — Before any level determination, healthcare organizations must identify whether they handle Controlled Unclassified Information — which may include PHI in federal contracts, DoD-funded research data, or other sensitive information categories. The presence or absence of CUI determines whether Level 1 or Level 2 requirements apply and defines the assessment boundary.
- Subcontractor flow-down accountability extending to the full vendor chain — Prime contractors remain accountable for ensuring that subcontractors handling CUI comply with CMMC requirements through flow-down clauses in their contracts. Healthcare organizations with complex vendor ecosystems — relying on EHR providers, telehealth platforms, and medical device manufacturers — must verify subcontractor compliance, not merely contractual commitment.
How do the three CMMC levels differ in their requirements, audit processes, and healthcare applicability?
- Level 1: 15 to 17 basic practices with annual self-assessment — Level 1 covers FAR 52.204-21 Federal Contract Information practices including basic cyber hygiene such as password security and terminal access limitation. Healthcare organizations at this level handle administrative contract data and can perform annual self-assessments without third-party verification — the lowest compliance overhead of the three levels.
- Level 2: 110 NIST SP 800-171 controls with C3PAO third-party assessment every three years — Level 2 is the level most relevant to healthcare organizations handling CUI including PHI in federal contracts. It requires 110 controls covering access control, audit logging, encryption, incident response, system integrity, and supply chain risk management — and mandates formal assessment by a Certified Third-Party Assessment Organization every three years rather than self-certification.
- Level 3: NIST SP 800-172 advanced controls with DIBCAC assessment for 1% of DoD contractors — Level 3 is designed for organizations protecting high-priority CUI against advanced persistent threats, requiring zero-trust architecture, real-time threat detection, and advanced supply chain risk management. DIBCAC-conducted assessments apply to approximately 1% of all DoD contractors — in healthcare, organizations involved in critical national security clinical research or high-priority defense health programs.
- MFA, end-to-end encryption, and least-privilege access as Level 2 technical requirements — Level 2's key technical requirements directly exceed what HIPAA mandates: multi-factor authentication for all system access, end-to-end encryption for CUI at rest and in transit, and least-privilege access controls ensuring only authorized personnel can access CUI-holding systems. Healthcare organizations with robust HIPAA programs frequently discover gaps in each of these areas when evaluating CMMC Level 2 readiness.
- Assessment boundary definition as the audit scope-controlling activity — Network segmentation separating CUI-related systems from general clinical and administrative networks reduces the scope of CMMC audits by clearly defining the assessment boundary. In healthcare environments where clinical, research, and administrative systems overlap, this segmentation is both a security control and an audit scope management strategy.
- Formal Level 2 assessment lasting four to six weeks following 9 to 12 months of preparation — The formal C3PAO Level 2 assessment typically takes four to six weeks, following the 9 to 12 month preparation cycle required for most organizations. Healthcare organizations beginning preparation in early 2025 are positioned for certification in 2026; those who have not started face significant timeline pressure relative to the DoD rollout schedule.
Why is HIPAA compliance insufficient for CMMC and what specific gaps do healthcare organizations need to close?
- HIPAA addresses PHI; CMMC addresses CUI with stricter technical requirements — While PHI in federal contracts may qualify as CUI, HIPAA's technical safeguard requirements are less prescriptive and less demanding than CMMC Level 2. HIPAA treats encryption as addressable; CMMC makes it mandatory. HIPAA requires access controls; CMMC requires granular least-privilege controls with MFA enforcement. The compliance assumption gap is one of the primary reasons for failed CMMC readiness assessments in healthcare organizations.
- $10.93 million average 2023 healthcare breach cost establishing the financial stakes — The average cost of a healthcare data breach reached $10.93 million per incident in 2023, while ransomware attacks on healthcare providers surged over 94% since 2021 — context that establishes CMMC's stricter requirements not as regulatory burden but as operationally justified protection against an accelerating and increasingly costly threat environment.
- More granular audit logging than HIPAA requires — CMMC Level 2 requires audit logging that traces CUI access at a granularity HIPAA does not mandate — specific user actions, timestamps, system resources accessed, and audit log integrity protection. Healthcare organizations with HIPAA-compliant logging frequently lack the coverage, granularity, and tamper protection that CMMC assessment will evaluate.
- More formal incident response planning including tabletop validation — CMMC requires documented incident response plans that have been tested through tabletop exercises and cybersecurity drills — a validation step that HIPAA recommends but does not require with the same formality. Healthcare organizations whose incident response plans exist on paper but have not been exercised will not satisfy CMMC assessor expectations.
- CUI flow mapping as a healthcare-specific discovery challenge — Healthcare organizations must specifically map where DoD-funded research data, CUI-classified PHI, and other CUI categories flow through their systems — an exercise that frequently reveals CUI handling in systems not previously identified as within the CMMC assessment boundary, expanding the compliance scope beyond initial estimates.
- Prime contractor accountability for subcontractor CUI compliance — Healthcare systems relying on external EHR providers, telehealth services, and medical device manufacturers for systems that touch CUI must ensure those vendors comply with CMMC requirements through flow-down clauses. The vendor ecosystem complexity of modern healthcare organizations makes subcontractor compliance verification one of the most demanding CMMC preparation challenges.
How should healthcare organizations conduct effective CMMC internal audits including gap analysis, logging, and control testing?
- Gap analysis as the systems validation exercise, not a documentation review — The most expensive mistake in a CMMC gap analysis is treating it as a documentation exercise rather than a systems validation exercise. Controls must be tested as operational realities — verified through log review, access control testing, and encryption configuration examination — not accepted on the basis of policy documentation alone.
- SPRS score management through five-point control prioritization — The SPRS score starts at 110 points with deductions applied for each non-compliant control. Five-point controls — those with the largest deduction value — must receive prioritized attention in gap analysis because their absence most significantly reduces the SPRS score. Level 2 certification requires a minimum score of 88, making high-value control gaps the most urgent remediation targets.
- SIEM with traceability matrix as the audit evidence infrastructure — A SIEM system correlating security event logs provides the continuous evidence of control operation that CMMC assessors require. A traceability matrix mapping logs and policies to specific CMMC control identifiers ensures that evidence can be presented by control number during assessment — the format that C3PAO assessors use to evaluate compliance.
- MFA enforcement verification through authenticator log review — Verifying MFA enforcement requires reviewing authenticator logs to confirm that MFA is active and enforced across all administrative groups, service accounts, and remote access paths — not merely configured in policy. Gaps in MFA enforcement for privileged accounts are among the most commonly identified Level 2 control failures.
- Encryption testing beyond policy review — Encryption testing must actively scan for misconfigured storage buckets, open security groups, and unencrypted data paths — and must generate KMS audit logs demonstrating that encryption is active at rest and in transit. Policy documentation of encryption requirements does not satisfy the CMMC evidence standard; operational evidence of encryption functioning as intended does.
- Mock assessments before formal certification for assessor question practice — Running internal or third-party mock assessments before formal C3PAO certification enables organizations to practice responding to assessor questions, identify documentation gaps under simulated assessment conditions, and surface control failures that might not emerge from self-review but become apparent when controls are tested by an external party applying formal assessment methodology.
What documentation practices are required for CMMC audit findings and long-term compliance planning?
- POA&M as the remediation contract for identified control gaps — A Plan of Action and Milestones documents every identified nonconformance with the specific remediation action, responsible owner, and completion timeline. High-risk gaps such as missing MFA or encryption require remediation within 30 days under CISO or IT Director ownership. Medium-risk gaps such as incomplete control documentation require resolution within 30 to 90 days under System Administrator ownership.
- SSP as the living record of control implementation — The System Security Plan must document how each of the 110 NIST SP 800-171 controls is implemented in the specific system environment, updated regularly to reflect changes in systems or risks. The SSP is the primary document C3PAO assessors use to evaluate CMMC Level 2 compliance and must be current, accurate, and specific to the actual system configuration rather than a generic template.
- Traceability matrix linking controls to evidence artifacts — A traceability matrix connecting each CMMC control identifier to the specific log files, screenshots, policy documents, and configuration records that demonstrate compliance enables auditors to locate evidence for any control in seconds rather than searching across disconnected documentation stores — a capability that significantly reduces assessment duration and reduces the risk of assessor findings from undiscoverable evidence.
- Continuous monitoring plan specifying roles, tools, and alert thresholds — A continuous monitoring plan documenting which automated tools including SIEM and EDR systems monitor which systems, which roles are responsible for monitoring activities, and what alert thresholds trigger escalation converts the CMMC monitoring requirement from a periodic compliance activity into a permanently operational security function.
- Annual or quarterly internal audits rather than triennial preparation sprints — Conducting formal internal audits on a monthly or quarterly schedule using a checklist aligned with official CMMC assessment criteria maintains continuous readiness rather than requiring an intensive preparation sprint before each three-year formal assessment. Following up three to six months after corrective actions verifies that remediation has been sustained rather than implemented only to pass the immediate review.
- Healthcare-specific documentation complexity spanning CMMC and CMS requirements — Beyond CMMC requirements, healthcare organizations must simultaneously maintain documentation for CMS regulations including medical necessity records and patient consent documentation. Documentation failures across these overlapping frameworks — with claim denial rates reaching 4.8% in some programs — establish that documentation quality management is a shared operational challenge across regulatory programs, not only a CMMC-specific obligation.
How does Censinet RiskOps™ specifically support CMMC internal audit readiness and continuous compliance for healthcare organizations?
- NIST CSF and HICP-aligned questionnaires mapping to CMMC requirements — Censinet RiskOps™ uses standards-based questionnaires aligned with NIST CSF and HICP that map directly to CMMC requirements — ensuring that internal audit activities evaluate the same controls that C3PAO assessors will examine during formal certification rather than conducting assessments against a different control framework that may leave gaps.
- Baptist Health transformation across six acute care hospitals — Baptist Health in Jacksonville replaced manual spreadsheet-based processes across six acute care hospitals and 14,250 staff with Censinet RiskOps™ under VP/CISO James Case. The transformation brought consistency across the full health system, saved time on risk assessments, and enabled the collaborative audit workflows that multi-site healthcare organizations require.
- Tower Health AI-driven evidence validation and risk mapping — Tower Health used Censinet RiskOps™'s AI-driven capabilities to automate evidence validation and risk mapping, enabling audit scaling across their vendor and system portfolio while improving accuracy over the manual data collection it replaced. Automated evidence validation identifies gaps in NIST SP 800-171 controls before C3PAO assessors do — converting post-assessment findings into pre-assessment remediation opportunities.
- Centralized collaborative platform replacing spreadsheet version control failures — Spreadsheet-based CMMC audit management creates version control conflicts, inconsistent data across assessors, and documentation gaps that surface during formal assessment. Censinet RiskOps™ provides a single accurate source of truth accessible to all team members simultaneously, with collaborative workflow management that routes findings to appropriate stakeholders for remediation action.
- Benchmarking against peer healthcare organizations for relative readiness assessment — The benchmarking capability enabling comparison against other healthcare entities in the Censinet community provides relative readiness context that internal assessment alone cannot supply — identifying whether the organization's CMMC control implementation is strong, average, or inadequate compared to peer organizations facing the same assessment requirements.
- Automation enabling broader vendor and system coverage without staffing increases — For healthcare organizations managing CMMC compliance across clinical applications, medical devices, and supply chain vendors simultaneously, automation that handles evidence collection, control mapping, and finding routing enables comprehensive compliance management across the full system scope without proportional increases in compliance team headcount.


