CMMC Compliance Challenges: Small vs. Large Healthcare Providers
Post Summary
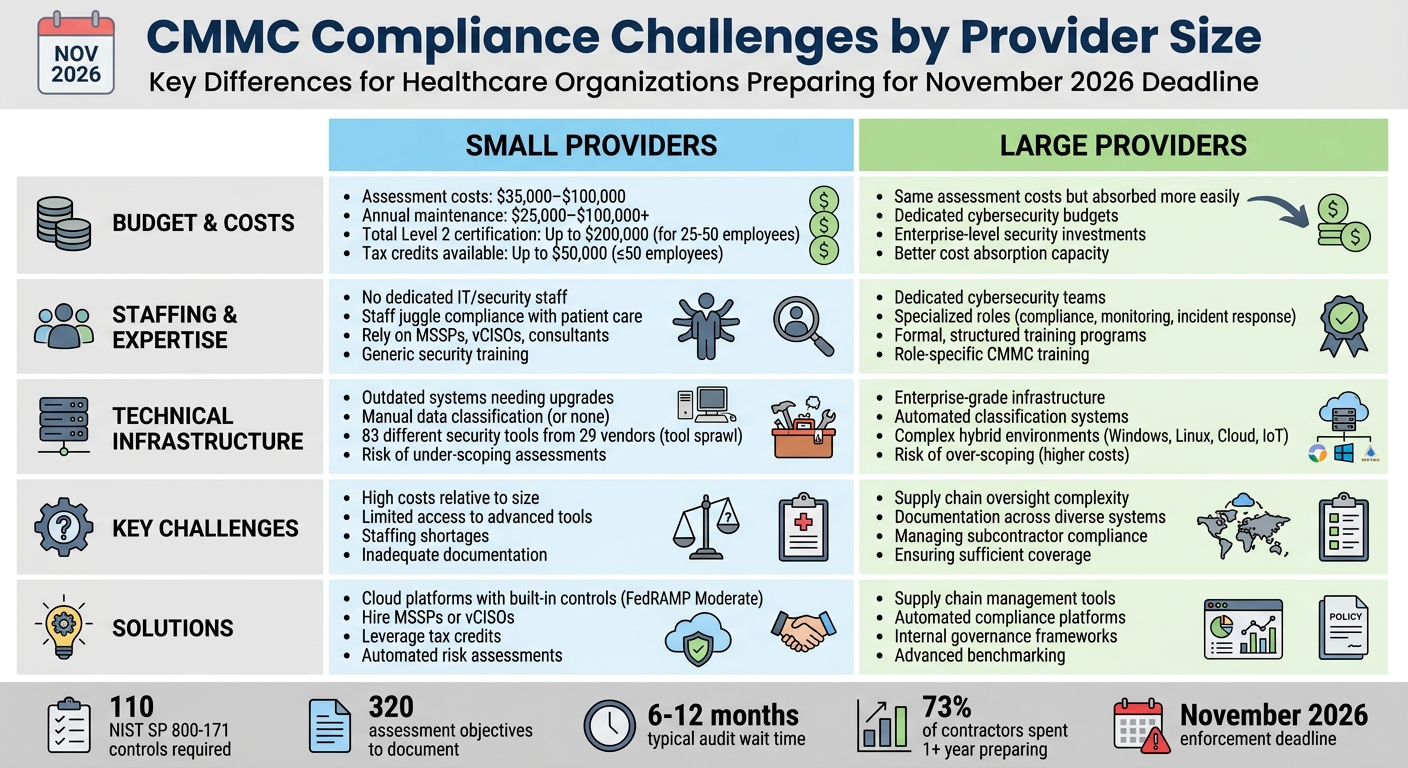
CMMC compliance is critical for healthcare providers working under DoD contracts, but the path to certification varies significantly between small and large organizations. Small providers often struggle with limited budgets, minimal IT staff, and outdated systems. Larger providers face challenges managing compliance across vast networks and subcontractors. Both must prepare for the November 2026 enforcement deadline while navigating complex requirements, including 110 NIST SP 800-171 controls and audits by C3PAOs.
Key Differences:
- Small Providers: Face high costs relative to size, limited access to advanced tools, and staffing shortages.
- Large Providers: Struggle with healthcare supply chain security challenges, documentation across diverse systems, and managing subcontractor compliance.
Key Challenges:
- High assessment costs: $35,000–$100,000, plus ongoing expenses.
- Long preparation and audit wait times: 6–12 months.
- Heavy documentation requirements: 320 assessment objectives.
Solutions:
- Small Providers: Use cloud platforms with built-in controls, hire MSSPs or vCISOs, and leverage tax credits.
- Large Providers: Focus on supply chain management, automated tools, and internal governance frameworks.
Censinet RiskOps™ offers tailored tools to streamline compliance, from automated risk assessments to centralized documentation, helping both small and large providers meet requirements efficiently.
CMMC Compliance Challenges: Small vs Large Healthcare Providers Comparison
Resource Differences: Small vs. Large Providers
The financial divide between small and large healthcare providers significantly shapes their approach to CMMC compliance. Budget limitations not only dictate the tools an organization can afford but also influence its ability to stay competitive within the defense contracting industry.
Budget Differences
Small healthcare providers face steep fixed costs, regardless of their size. For instance, a clinic with just 20 employees often incurs third-party assessment fees similar to those of mid-sized organizations. CMMC Level 2 or 3 assessments typically cost between $35,000 and $100,000, with ongoing maintenance and compliance management adding another $25,000 to over $100,000 annually [6].
"CMMC compliance is especially challenging for many small defense contractors. Smaller companies mean smaller budgets. Expenses include hiring consultants, implementing necessary technologies, and training staff", says Danielle Barbour, a CMMC Compliance Expert [5].
Larger providers, on the other hand, can absorb these costs more easily within their operational budgets. They often have dedicated cybersecurity teams and can invest in advanced security measures without jeopardizing their core functions. For small providers, however, these expenses often require reallocating already stretched resources [5].
While the Small Business Cybersecurity Act of 2024 offers tax credits of up to $50,000 for companies with 50 or fewer employees, this assistance barely scratches the surface of broader compliance costs. These include initial gap analyses (which can cost thousands), employee training (ranging from hundreds to thousands annually), and the recurring expenses of maintaining certification [5][6]. Budget constraints also limit small providers' ability to adopt cutting-edge compliance tools.
Access to Compliance Tools
Limited budgets also restrict small providers' access to advanced compliance technologies. While large organizations can afford comprehensive security suites, small providers often have to prioritize only essential tools or rely on Managed Security Service Providers (MSSPs) for expertise they can't afford to maintain in-house [2].
"The process of implementing necessary controls can be costly, often requiring new systems, software, or cybersecurity experts. For numerous small enterprises, these expenses overwhelm", notes Kiteworks [5].
To cut costs, many small providers are turning to FIPS 140-2 validated cloud platforms. These platforms meet a significant portion of CMMC Level 2 requirements "out of the box", allowing providers to inherit pre-built security controls instead of creating custom infrastructure. While this strategy reduces initial expenses, it demands careful vendor selection and constant monitoring. In contrast, large providers can afford both cloud-based solutions and on-premise systems, enabling them to build hybrid architectures tailored to their needs [2].
Another challenge for small providers is the 9- to 15-month wait time for Level 2 and Level 3 audits. Even if they are ready for certification, delays in securing assessment dates can put contracts at risk. Larger organizations, with more diversified revenue streams, are better positioned to weather such delays [6].
sbb-itb-535baee
Staffing and Expertise: Small vs. Large Providers
The difference in staffing between small and large healthcare providers creates a major hurdle when it comes to achieving CMMC compliance. Large hospital systems usually have dedicated IT and information security teams, while smaller practices - like those run by one or two physicians - often operate without any dedicated compliance or cybersecurity personnel at all [7].
Cybersecurity Team Size
Small healthcare providers often find themselves managing compliance without in-house IT security experts. This means staff members, already stretched thin with clinical responsibilities, take on the additional burden of handling security tasks. This shift results in what experts call "indirect costs" - the time and energy diverted from patient care to focus on mandatory security measures [5].
On the other hand, large organizations employ specialized cybersecurity teams. These teams are divided into specific roles, such as compliance management, threat monitoring, and incident response, which allows them to handle CMMC requirements more effectively.
"Many smaller organizations lack dedicated compliance or information security staff, and without the right tools, they struggle to conduct assessments that meet federal expectations", explains Keith A. Reynolds in Physicians Practice [7].
To address this expertise gap, small providers are increasingly turning to Managed Security Service Providers (MSSPs), CMMC consultants, and Certified Third-Party Assessor Organizations (C3PAOs). These external resources bring the necessary expertise but come with ongoing costs. This lack of internal staffing also makes it harder to train employees on critical compliance procedures.
Training and Knowledge
The staffing challenges are further compounded by a lack of training resources, which deepens the compliance gap. Small providers often have limited budgets and expertise, making it difficult to provide staff with the necessary training on CMMC standards. In contrast, larger organizations can afford formal, structured training programs that include regular updates on emerging cyber threats and best practices [5].
The disparity goes beyond how often training occurs - it also affects the quality of the content. Smaller organizations often rely on generic security training, which doesn’t cover the specific requirements of CMMC or the proper handling of Controlled Unclassified Information (CUI). Larger providers, however, offer tailored, role-specific training that ensures employees understand their responsibilities under CMMC standards [4]. This difference becomes especially important during audits, as staff knowledge of compliance obligations is a key evaluation point - something generic training programs often fail to address.
These gaps in staffing and training create additional challenges for small providers, making it even harder for them to meet CMMC requirements. This sets the stage for exploring technical readiness and customized solutions.
Technical Capabilities and Infrastructure: Small vs. Large Providers
The gap between small and large healthcare providers becomes even clearer when you look at their technical infrastructure and data security. Both types of organizations usually have basic security tools like firewalls, endpoint protection, and backup systems. However, the real challenge is in the governance layer - things like documented policies, clear ownership assignments, and evidence trails needed for CMMC compliance.
IT Infrastructure Readiness
When it comes to technical capabilities, the differences between small and large providers are stark. Small healthcare providers often rely on outdated systems that need major upgrades to meet CMMC standards. These organizations face tough decisions: spend heavily on new systems or risk failing compliance audits. For a small business with 25–50 employees, the cost of Level 2 certification can top $200,000, especially with major infrastructure upgrades [8].
Large healthcare providers, on the other hand, usually have enterprise-grade infrastructure that’s closer to meeting CMMC requirements. But their challenge lies in proving that security controls function across all their varied systems. For instance, a large hospital network might need to document compliance for Windows servers, Linux servers, cloud platforms, and multiple network devices - each requiring its own evidence [10].
The scoping process creates headaches for both groups, but in different ways. Smaller providers often under-scope their assessments, overlooking a single file share or laptop that handles sensitive data, which can lead to audit failures. Larger providers tend to over-scope, treating their entire network as in-scope. This approach significantly increases remediation costs [1]. Network segmentation - isolating systems that handle Controlled Unclassified Information (CUI) - offers a way to manage costs. However, implementing it requires technical expertise that smaller organizations often lack. Similarly, differences in how data is classified further widen the gap between small and large providers.
Data Classification and Security
Data classification is another area where small and large providers differ greatly. Large healthcare providers often use automated classification systems to identify and tag CUI, Federal Contract Information (FCI), and Protected Health Information (PHI) as it moves through their networks. Small providers, on the other hand, tend to rely on manual processes - or have no formal classification system at all - making scoping errors more likely [8].
Certain security measures, like Multi-Factor Authentication (MFA), end-to-end encryption for CUI, and continuous system monitoring, are non-negotiable for CMMC Level 2 compliance [9]. While large organizations typically have these controls in place, they must demonstrate "sufficiency" - proving the controls cover all in-scope assets. Small providers often struggle with "adequacy" - they may have basic security practices but lack the formal documentation and version-controlled procedures needed for audits [10].
"Adequacy means you're showing the right thing... Sufficiency means you're showing enough", explains FutureFeed [10].
The documentation burden is particularly heavy. NIST SP 800-171, which forms the foundation for CMMC Level 2, includes 110 requirements and 320 assessment objectives, all of which require evidence [1]. Small providers often juggle an average of 83 different security tools from 29 vendors, leading to "tool sprawl" that complicates evidence collection [8]. Large providers, with their greater resources, can deploy unified platforms that automate gap analysis and evidence gathering. In contrast, small providers often scramble to gather logs and screenshots manually just before audits.
| Feature | Small Healthcare Providers | Large Healthcare Providers |
|---|---|---|
| IT Infrastructure | Outdated; needs significant upgrades for compliance | Modern, enterprise-grade systems |
| Data Classification | Manual or absent; prone to scoping errors | Automated systems with clear segmentation |
| Infrastructure Complexity | Simple (e.g., mostly Windows) | Complex (Windows, Linux, Cloud, IoT) |
| Evidence Burden | Struggles with inadequate documentation | Challenges with ensuring sufficient coverage |
| Technical Tools | Disconnected point solutions | Integrated platforms with automation |
| Scoping Challenge | Under-scoping due to limited visibility | Over-scoping, leading to higher costs |
Comparison Table: Technical Challenges
Small and large providers face distinct technical challenges when working toward CMMC compliance. These challenges are influenced by the size and resources of each provider.
For small providers, data classification often relies on manual processes - or worse, no processes at all - leading to the risk of improperly identifying Controlled Unclassified Information (CUI) [4]. On the other hand, large providers might overcompensate by treating their entire network as in-scope, which can push remediation costs into six figures [1].
Small providers frequently turn to FedRAMP Moderate-certified cloud services to meet compliance needs without building infrastructure from scratch [2]. In contrast, large providers must navigate the complexities of hybrid environments, juggling legacy systems, multiple clouds, and on-premises setups to ensure consistent enforcement of policies [11].
Staffing constraints also play a role. For small providers, every hour spent on compliance documentation is an hour taken from patient care or other essential operations [9]. Larger providers, however, often have dedicated compliance teams, allowing them to handle these responsibilities without disrupting clinical or business workflows [9].
Below is a summary of these technical challenges by provider size:
| Technical Challenge | Small Healthcare Providers | Large Healthcare Providers |
|---|---|---|
| Data Classification | Manual or non-existent; risk of insufficiently scoping CUI [4] | Complex; risk of over-scoping, leading to high remediation costs [1] |
| Asset Management | Lack of automated discovery tools; incomplete inventories [4] | Struggle with "shadow IT" and maintaining baselines across diverse departments [4] |
| Access Control | Often lack Multi-Factor Authentication (MFA) on all systems [9] | Difficulty managing identity and access across legacy and hybrid cloud environments [11] |
| Audit Logging | Logs rarely standardized or reviewed [1] | Centralized log management exists but plagued by "noise" and alert fatigue [4] |
| Cloud Compliance | Heavy reliance on MSPs; must ensure providers meet FedRAMP Moderate [1] | Managing multiple cloud instances while enforcing consistent policies [11] |
| Operational Impact | High impact; limited staff to handle new protocols [9] | Formal change management processes, but slower implementation [9] |
These differences highlight the unique hurdles each provider size must overcome when addressing compliance requirements.
Changing Standards and Regulatory Requirements
The CMMC framework is constantly evolving, and organizations need to keep pace. With Phase 2 enforcement set to roll out in November 2026, companies face a tight timeline to meet Level 2 C3PAO assessment requirements for contracts involving Controlled Unclassified Information (CUI). This means staying agile as standards shift.
For small providers, the challenge lies in a lack of expertise. Without dedicated security teams, they often struggle to interpret the 110 NIST SP 800-171 requirements, which break down into 320 detailed assessment objectives requiring supporting evidence. When regulatory updates or new guidance are issued, these smaller organizations frequently lack the internal resources to figure out what’s needed. Many end up relying on external consultants or virtual CISOs (vCISOs), which can drive up costs and cause delays. This is a widespread issue - 73% of Defense Industrial Base contractors have spent over a year preparing for CMMC but still haven’t completed the process [9].
On the other hand, large providers face a different hurdle: managing their supply chains. While they typically have in-house security teams to track regulatory changes, their certification timelines can be derailed by subcontractors who aren’t prepared. Even one unready subcontractor could jeopardize an entire program’s certification schedule. As standards continue to evolve, large providers must not only update their own controls but also ensure that dozens - or even hundreds - of subcontractors do the same. This creates a ripple effect, slowing the entire certification process.
The assessment bottleneck is another major issue impacting everyone. There are roughly 80,000 contractors needing Level 2 certification, but the number of Certified Third-Party Assessment Organizations (C3PAOs) is limited, leading to wait times of 6 to 12 months [1]. When standards change, organizations often have to redo parts of their preparation, further clogging an already overwhelmed system. For smaller providers, these delays can mean missing out on contracts. For larger providers managing numerous programs, the delays can cascade, affecting multiple projects and threatening overall timelines.
Adding to the complexity is the growing emphasis on governance-focused assessments. Regulatory bodies now demand more than just technical controls like firewalls or backups - they expect documented policies and evidence that show these controls are consistently followed. Small providers often take a reactive approach, scrambling to gather evidence only when an audit is imminent, instead of embedding evidence collection into their daily operations [4]. Meanwhile, larger providers, despite having established processes, can still face challenges maintaining consistent evidence across multiple departments and hybrid environments. This shift toward governance makes compliance a more intricate and time-consuming process for everyone involved.
Cross-Department Implementation Barriers: Small vs. Large Providers
When it comes to CMMC compliance, healthcare providers - whether small or large - face distinct challenges rooted in coordination and resource allocation. For smaller providers, the main hurdle is often bandwidth. Without dedicated IT or security personnel, existing staff are tasked with juggling compliance responsibilities alongside their primary focus: patient care. This dual role stretches resources thin and inevitably shifts attention away from security.
Eric Kong, CEO of Consilien, highlights this struggle: "CMMC compliance involves conducting assessments, implementing controls, and documenting procedures. All of these tasks are time-consuming and can divert the focus from the core business operations" [12].
Without specialized training or adequate resources, smaller providers often operate in silos, which weakens their ability to maintain consistent compliance practices.
On the other hand, large healthcare organizations face a different kind of challenge: the complexity of coordination. Even with dedicated teams in place, aligning IT, legal, HR, clinical staff, and third-party vendors under unified security protocols can feel like an uphill battle. Mapping the flow of Controlled Unclassified Information (CUI) across multiple systems and departments adds to the complexity. Misjudging the scope - whether by overestimating or underestimating - can lead to wasted resources or, worse, security gaps [4].
Documentation requirements further strain both small and large providers, though the impact varies. Small practices often lack centralized systems for managing records, which can lead to fragmented policies, incomplete training logs, and disorganized vendor agreements [12]. Meanwhile, large organizations, though better equipped with systematic record-keeping, must manage an overwhelming volume of documentation to meet HIPAA requirements, which mandate retaining compliance records for at least six years [3]. This creates a massive administrative burden across multiple departments.
CMMC isn’t a one-and-done task - it’s a continuous process that requires organization-wide commitment. For smaller providers, limited staff makes sustained coordination a challenge, while larger providers must navigate the complexities of aligning sprawling teams and processes. These hurdles underscore the importance of integrated solutions, which will be explored in the next section.
Solutions for Overcoming Challenges Using Censinet RiskOps™

Censinet RiskOps™ provides healthcare providers with tools to address their unique challenges, whether they’re small practices with limited resources or large organizations managing complex operations. By focusing on automation, streamlined collaboration, and ongoing improvement, the platform reduces administrative burdens while meeting critical compliance requirements.
Automated Risk Assessments
Automation is a game-changer, especially for smaller healthcare providers. With Censinet AI™, tasks that once took weeks - like answering third-party risk assessment questions - can now be done in seconds. The system automatically processes vendor evidence, summarizes documentation, and generates risk reports based on relevant data. This efficiency allows small clinics to handle vendor assessments without pulling staff away from their primary duties.
For larger organizations managing hundreds or even thousands of vendor relationships, automation simplifies the process on a much larger scale. Censinet AI™ accelerates assessments while maintaining oversight through customizable rules and review mechanisms. This ensures faster evaluations without compromising critical decision-making, creating a streamlined approach to compliance management.
Collaborative Compliance Management
Coordinating across departments can be a significant hurdle, but Censinet RiskOps™ addresses this by centralizing communication and task management. The platform automatically routes assessment findings and assigns related tasks to the right personnel. If a compliance review uncovers gaps in communication, the system tracks progress on remediation tasks and stores all documentation in one place.
This method helps smaller providers avoid disjointed processes while giving larger organizations a clear, unified view of their operations. A real-time dashboard ensures accountability without the need for endless email threads or meetings, keeping everyone aligned and on track.
Benchmarking and Continuous Improvement
Maintaining compliance isn’t a one-and-done effort. Censinet RiskOps™ supports ongoing improvement with benchmarking tools that allow organizations to measure their cybersecurity posture against industry standards and peers. Smaller providers can identify areas for improvement without hiring external consultants, while larger organizations can focus on specific departments or facilities that need attention.
With a centralized risk visualization dashboard, tracking progress over time becomes simple. This makes it easier to adapt to evolving threats and changing standards, ensuring that compliance efforts remain effective and measurable in the long run.
Comparison Table: Solutions by Provider Size
Healthcare providers encounter different compliance challenges based on their size, making customized strategies essential for meeting CMMC requirements. Small and large providers require approaches tailored to their unique needs to reach certification.
The table below highlights how Censinet RiskOps™ adjusts its solutions to align with the specific demands of small and large healthcare providers:
| Feature Category | Small Provider Solutions | Large Provider Solutions |
|---|---|---|
| Staffing | Outsourced MSSP or vCISO support | Dedicated in-house security teams |
| Key Tools | Automated risk assessments and cloud platforms | Advanced benchmarking and supply chain oversight |
| Budgeting | Fractional expertise costs with available tax credits (up to $50,000) | Enterprise-level security budgets |
| Documentation | Automated evidence gathering integrated into daily operations | Continuous internal audits and governance frameworks |
| Supply Chain Management | Focus on meeting flow-down requirements from prime contractors | Verifying compliance across the entire supplier base to protect certification |
| Risk Assessment | Prioritizes allocation across 110 NIST SP 800-171 controls | Manages complexity across large, multi-site networks and diverse IT assets |
| Scope Definition | Avoids over-scoping to reduce unnecessary remediation costs | Prevents under-scoping in environments where CUI flows through multiple systems |
This breakdown demonstrates how Censinet RiskOps™ adapts its features to address the distinct compliance needs of providers, regardless of their size. By scaling its solutions effectively, Censinet ensures both small and large organizations can achieve certification with strategies that align with their operational realities.
Conclusion
CMMC compliance presents unique hurdles for healthcare providers, whether they're small practices or sprawling hospital systems, especially as the November 2026 deadline approaches. Smaller providers wrestle with tight budgets and a shortage of cybersecurity talent, making it hard to access the expertise they need. Larger organizations, on the other hand, face the daunting task of ensuring compliance across vast networks and numerous subcontractors. As Cynomi aptly put it, "One unprepared subcontractor can jeopardize an entire program" [1].
The situation is further complicated by some sobering statistics. About 68% of contractors need more than a year to prepare for CMMC, and assessor wait times can stretch from 6 to 12 months [1]. Providers who delay their efforts risk falling behind competitors. Financially, the stakes are enormous - HIPAA violations alone can lead to annual penalties reaching $2,190,294 for repeated offenses [3]. Moreover, mistakes in scoping during CMMC preparation remain one of the costliest missteps [1].
To overcome these challenges, smaller providers are increasingly turning to fractional vCISOs and managed security services to fill their expertise gaps. Meanwhile, larger systems focus on streamlining evidence collection and ensuring subcontractors adhere to secure contract language. Both groups must shift their mindset from treating compliance as a one-time task to embedding it into their daily processes.
Censinet RiskOps™ provides tailored solutions to tackle these challenges. For smaller providers, it offers automated tools for risk assessments and evidence collection. Larger organizations benefit from its advanced benchmarking capabilities and supply chain oversight. With its ability to navigate the 110 NIST SP 800-171 requirements and 320 assessment objectives, the platform makes it easier for providers without dedicated compliance teams to maintain the detailed documentation needed for C3PAO assessments.
Ultimately, success in CMMC compliance lies in understanding the distinct realities faced by different types of healthcare providers. A rural clinic managing Controlled Unclassified Information (CUI) has vastly different needs compared to a multi-hospital system overseeing a complex vendor network. Those who acknowledge these differences and adopt solutions scaled to their specific needs will be better equipped to achieve certification and remain competitive in an increasingly regulated healthcare industry.
FAQs
Which CMMC level applies to my healthcare organization’s DoD work?
Level 2 of the CMMC 2.0 framework is specifically relevant for healthcare organizations that manage Controlled Unclassified Information (CUI) while working with the Department of Defense (DoD). At this stage, organizations are expected to adopt advanced security controls designed to protect sensitive information effectively.
Additionally, compliance at this level involves undergoing formal assessments to verify that these security measures are properly implemented and maintained. This ensures the organization meets the DoD's stringent requirements for handling CUI.
How do we define and limit the CUI scope to avoid over- or under-scoping?
To clearly define and limit the scope of Controlled Unclassified Information (CUI), start by identifying all assets that store, process, or transmit CUI. Use the safeguarding and dissemination controls outlined by the government as your guide. Once identified, document each asset's inclusion in the assessment scope. This ensures alignment with CMMC requirements for protecting CUI while avoiding the risks of over- or under-scoping. Staying precise in this process helps meet regulatory expectations effectively.
What should we do now to meet the November 2026 CMMC deadline with long audit wait times?
With the November 2026 CMMC deadline approaching and audit wait times expected to be lengthy, it's crucial to start preparations as soon as possible. Here's how you can get ahead:
- Conduct a gap analysis: Identify where your current cybersecurity practices fall short of CMMC requirements.
- Document cybersecurity controls: Thorough, well-organized documentation is essential for a smooth audit process.
- Implement continuous monitoring: Regularly review and update your security measures to ensure ongoing compliance.
Tools like Censinet RiskOps™ can be a game-changer, helping automate evidence collection and streamline vendor risk management. Speaking of vendors, don't overlook third-party compliance. Non-compliant vendors can create bottlenecks and delay your certification process.
The key to navigating audit backlogs and meeting the deadline lies in early preparation and meticulous documentation. Start now to ensure you're ready when it's time for assessments.


