NIST Framework Training for Healthcare Teams
Post Summary
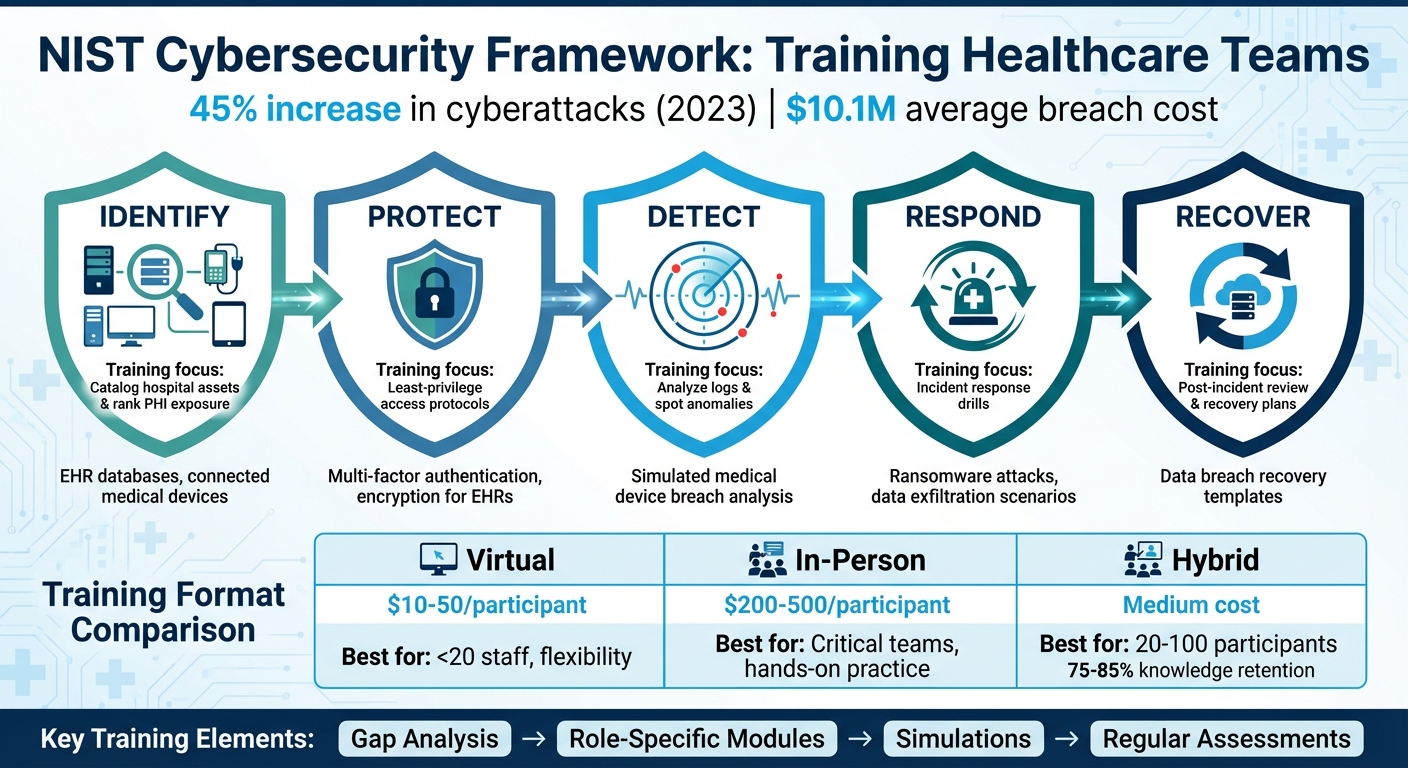
Healthcare organizations face mounting cybersecurity challenges, with cyberattacks increasing by 45% in 2023 and costing an average of $10.1 million per breach. These incidents disrupt patient care, expose sensitive data, and highlight the urgent need for cybersecurity training.
The NIST Cybersecurity Framework (CSF) provides a structured approach to managing risks through five core functions: Identify, Protect, Detect, Respond, and Recover. Tailoring training to these functions equips healthcare teams to handle threats effectively. Key steps include:
- Conducting gap analyses to assess vulnerabilities.
- Focusing on healthcare-specific risks like medical device security and third-party threats.
- Designing role-specific training modules aligned with NIST functions.
- Using tools like Censinet RiskOps™ to integrate training with real-world risk management.
Training formats, such as virtual, in-person, or hybrid, should accommodate healthcare workers' demanding schedules. Simulations, phishing exercises, and incident response training drills help translate knowledge into practical skills. Regular assessments and refresher courses ensure teams stay prepared for evolving threats.
Outcome: A well-trained workforce minimizes human error, strengthens system defenses, and protects patient care.
NIST Cybersecurity Framework 5 Core Functions for Healthcare Training
NIST Adoption for Healthcare
sbb-itb-535baee
Assessing Training Needs and Gaps
To build an effective training program, start by conducting a baseline gap analysis. This helps pinpoint areas where staff knowledge is lacking and identifies high-risk vulnerabilities. By focusing on these gaps, you can avoid wasting time on topics employees already understand, creating a more focused and impactful curriculum tailored to your organization’s needs.
Conducting a NIST-Based Gap Analysis
The NIST Cybersecurity Framework (CSF) is a great tool for assessing your current practices. It breaks down cybersecurity into six core functions: Govern, Identify, Protect, Detect, Respond, and Recover. By comparing your organization’s efforts to these functions, you can uncover gaps in staff knowledge and operational risks.
Tools like the RISC 2.0 Toolkit Cybersecurity Module and the ONC/OCR Security Risk Assessment (SRA) Tool are especially useful for evaluating how well your organization aligns with NIST CSF 2.0 standards and HHS performance goals [5].
"The framework helps identify and prioritize vulnerabilities based on potential impact, enabling better resource allocation to prevent negative cybersecurity events." - Compliancy Group [4]
Your evaluation should determine whether staff can effectively identify critical assets, manage access controls, and detect unusual network activity. Healthcare-specific resources like the HHS 405(d) Program offer tailored guidance for improving cybersecurity in the sector. For clinical staff, the "Cybersecurity for the Clinician" video series is a valuable tool for assessing non-technical cybersecurity knowledge among physicians, nurses, and medical students [5]. These insights will form the foundation for targeted training modules aligned with NIST’s core functions.
Identifying Healthcare-Specific Risks
Healthcare organizations face unique challenges that require a specialized approach. Beyond general cybersecurity gaps, focus on risks specific to healthcare environments.
One major area is medical device vulnerabilities. Devices like infusion pumps and imaging equipment often run on outdated software or lack robust security features, making them easy targets for cyberattacks. Training should ensure staff understand these risks and the steps needed to secure such devices.
Another critical area is third-party vendor and supply chain threats. Healthcare organizations often work with numerous vendors who access sensitive systems, yet staff may not fully grasp how to verify vendor security practices or enforce proper access protocols. The Health Sector Cybersecurity Coordination Center (HC3) provides threat intelligence tailored to healthcare, helping organizations stay ahead of emerging risks [5].
Additionally, the HITECH Act requires that HHS publicly disclose cybersecurity breaches affecting 500 or more individuals. Reviewing this data can help your team identify common attack methods and vulnerabilities faced by similar organizations [4]. By addressing these healthcare-specific risks, your training program can better prepare staff for the unique challenges of the industry.
Designing a Training Curriculum
Once you've completed your gap analysis, the next step is to create a training program that turns those findings into actionable skills. The goal is to address the training gaps and healthcare risks you've identified while aligning your program with the NIST Framework. This means focusing on practical, role-specific training that mirrors the scenarios your staff encounters daily. By doing so, your curriculum will directly tackle vulnerabilities and strengthen your overall cyber risk strategy. Every team member should leave the training with a clear understanding of their role in protecting patient data and clinical systems within the framework's core functions.
Building Training Modules for Each NIST Core Function
To make the training effective, structure your program around the five core NIST functions: Identify, Protect, Detect, Respond, and Recover. Each module should connect technical concepts to real-life healthcare scenarios, ensuring the material feels relevant and applicable.
- For the Identify function, design exercises where teams catalog hospital assets and rank them based on their exposure to PHI (Protected Health Information). This helps staff recognize which systems - like EHR databases or connected medical devices - demand the highest level of protection.
- In the Protect module, have nurses and clinicians practice least-privilege access protocols for EHRs. Simulations involving multi-factor authentication and encryption can reinforce these critical security measures.
- The Detect module should include hands-on training where staff analyze logs from a simulated breach of a medical device. This teaches them how to spot anomalies in clinical networks.
- For Respond, run incident response drills that simulate scenarios like ransomware attacks or data exfiltration. These exercises help reinforce your response plan and ensure staff can act quickly and effectively.
- The Recover module should guide participants through creating post-incident review templates and recovery plans tailored to situations like data breaches that impact patient care.
By integrating real-world tools into these modules, staff can practice applying their knowledge in a way that mirrors their daily responsibilities.
Using Censinet RiskOps™ for Training Support

Censinet RiskOps™ offers tools that can elevate your training program by bridging classroom learning with practical risk management workflows. Its automated NIST CSF 2.0 assessments allow teams to perform self-assessments across all NIST functions, including the new Govern function, which emphasizes supply chain risk and cybersecurity strategy.
The platform's automated action plans are perfect for illustrating how to identify and address gaps. Trainees can use the task features to assign findings to stakeholders, gaining hands-on experience with accountability and remediation workflows. Additionally, the platform's dashboards are excellent for teaching cybersecurity leaders how to present complex compliance data to Boards and non-technical stakeholders using clear, visual reporting. To add more context, incorporate peer benchmarking data from the platform into your training. This helps teams see how their organization's maturity compares with others in the healthcare sector and understand why certain NIST controls are prioritized across the industry.
Delivering Training to Healthcare Teams
Once you've outlined a focused training curriculum, the next step is figuring out how to deliver it in a way that works for healthcare teams. These teams often face 12-hour shifts, on-call responsibilities, and unpredictable schedules. If the training format doesn’t align with these realities, even the best curriculum will fall short. The goal is to build practical cybersecurity skills without disrupting patient care.
Selecting the Right Training Format
The format you choose - whether virtual, in-person, or hybrid - should depend on factors like team size, budget, and engagement needs. Here’s how these options break down:
- Virtual training: Priced at $10-50 per participant, this is a cost-effective choice for small teams (fewer than 20 people) or dispersed staff who need flexibility. It’s great for delivering theoretical knowledge but may lack the hands-on engagement of other methods.
- In-person sessions: These cost more, around $200-500 per participant, but provide the highest levels of engagement. They're especially effective for critical teams, like ER staff, who benefit from hands-on practice with incident response protocols.
- Hybrid formats: Ideal for medium to large teams (20-100 participants), this approach combines virtual modules for theoretical learning with in-person workshops for practical exercises. Studies aligned with NIST training standards show hybrid formats can achieve 75-85% knowledge retention. For larger groups, hybrid delivery scales well while maintaining the hands-on elements necessary for skills like detecting anomalies in clinical networks or responding to ransomware threats.
To accommodate healthcare schedules, keep sessions under two hours and consider micro-learning modules that staff can complete on demand. These shorter, focused sessions are more likely to be completed and less likely to interfere with patient care.
Using Simulations and Practical Scenarios
Hands-on exercises are essential for turning abstract cybersecurity concepts into actionable skills. For example:
- Phishing simulations: Run these quarterly using realistic scenarios, such as fake emails from vendors requesting EHR credentials or spoofed messages from hospital leadership. These exercises help staff develop the ability to recognize social engineering tactics, reinforcing the NIST Detect function.
- Incident response drills: These bring the NIST Respond and Recover functions to life. Use tabletop exercises to walk teams through scenarios like ransomware attacks that lock medical devices or data breaches affecting patient scheduling systems. By using scenarios that mirror your organization’s actual infrastructure (with PHI-masked data), staff can see how NIST controls apply to their daily responsibilities.
To ensure all shifts get adequate practice, rotate drill participation and schedule these exercises during low-census periods or staff meetings. This way, you can integrate simulations into existing workflows without disrupting patient care. These drills not only enhance cybersecurity awareness but also tie directly into broader risk management efforts.
Incorporating Censinet RiskOps™ in Training
Practical simulations can be taken a step further by integrating tools like Censinet RiskOps™, which help bridge training with real-world risk management. During Detect and Respond modules, teams can use the platform to work through live risk assessment scenarios. For example, they might:
- Evaluate vendor security questionnaires.
- Score third-party risks and data breach impacts based on PHI exposure.
- Assign remediation tasks to stakeholders.
These activities align with the NIST Identify function, giving staff hands-on experience with the same tools they’ll use in their daily work. The platform’s dashboards and automated action plans also provide a clear way to present complex risk data to non-technical audiences, making it easier for teams to translate training into actionable steps.
Measuring Training Results and Maintaining Awareness
Training doesn’t stop once employees finish their last module. It’s crucial to assess whether the program has improved your organization’s cybersecurity readiness and to keep those skills sharp over time.
Measuring Training Effectiveness
Start by using pre- and post-training assessments to measure knowledge improvement. Before training begins, give a quiz focused on the NIST Core Functions. Once training is complete, follow up with scenario-based questions, like how to respond to a ransomware attack or review a vendor’s security questionnaire. According to NIST-aligned gap analysis processes, a 20% score increase indicates effective training results [3][2].
But it’s not just about test scores. Use NIST CSF maturity measurements to see the bigger picture. Compare your Current Profile (where you are now) with your Target Profile (where you aim to be). Tools like Censinet RiskOps™ simplify this process by automating NIST CSF 2.0 Enterprise Assessments. These tools evaluate cybersecurity across all six NIST functions and create action plans that assign tasks to stakeholders. Real-time progress tracking is made easy through activity logs and dashboards.
Also, keep an eye on incident response times, policy compliance rates, and how quickly staff report suspicious activity. Combine these measurable metrics with employee feedback for a well-rounded view of your program’s effectiveness [3][1]. Benchmarking tools can help you compare your maturity and coverage against industry peers, which not only justifies cybersecurity investments but also highlights where additional training may be needed. These insights lay the groundwork for ongoing training enhancements.
To sustain these improvements, it’s essential to implement continuous learning programs.
Creating Ongoing Learning Programs
Once you’ve achieved measurable progress, the next step is to ensure that training keeps pace with evolving cyber threats. Schedule regular refresher courses and update training materials every quarter to address new challenges.
The HPH CPG Dashboard in Censinet RiskOps™ can assist in tracking progress on the 10 "Essential" and 10 "Enhanced" cybersecurity performance goals recommended by HHS and the White House. This tool provides clear visibility into areas that may need more training. Regular trend analysis can show how your cybersecurity efforts are improving over time, and non-technical visuals can make complex metrics easier to present to Boards and regulators.
Conclusion
Protecting patient data and critical systems in healthcare starts with NIST-aligned training. This involves evaluating your current security gaps, creating training modules based on the NIST Core Functions, using practical, real-world scenarios to address healthcare-specific risks, and consistently measuring the program’s effectiveness. Keeping awareness programs active ensures that cybersecurity remains a priority at every level.
The HPH Sector Cybersecurity Framework Implementation Guide (v1.1, Mar 2023), developed by the HSCC Cybersecurity Working Group in collaboration with NIST and HHS, provides a tailored roadmap for strengthening healthcare cybersecurity. This guide serves as the foundation for the training strategy outlined here.
To support these efforts, Censinet RiskOps™ offers tools to simplify the process. It automates NIST CSF Enterprise Assessments, provides real-time dashboards for both technical teams and executives, and includes features for task assignments, compliance monitoring, and benchmarking against industry standards. This approach helps shift training from a one-time event to an ongoing cycle of improvement.
While adopting the NIST CSF is voluntary, it should be customized to address your organization’s unique risks, whether they involve PHI protection, medical device security, or vendor management [1][6]. Regularly updating training programs and leveraging tools for streamlined risk assessment and tracking can help build a cybersecurity program that adapts to evolving threats. Together, these steps ensure your training program grows stronger as new challenges arise.
FAQs
Where do we start with NIST CSF training in a hospital?
To kick off NIST CSF training in a hospital, begin with a thorough risk assessment. This step is essential for identifying the hospital's current cybersecurity risks and aligning them with the NIST framework’s core functions: Identify, Protect, Detect, Respond, and Recover. By doing this, you can create a clear snapshot of the hospital’s cybersecurity posture.
Once risks are mapped out, prioritize high-risk areas and craft a customized implementation plan that addresses these vulnerabilities. Tools like Censinet RiskOps™ can simplify the risk assessment process and provide a way to track progress over time, ensuring the hospital stays on course.
Which roles need what NIST training in healthcare?
Different roles in healthcare demand customized NIST cybersecurity training to address risks effectively and stay compliant. For instance, cybersecurity teams, risk managers, and IT staff require detailed training on areas like risk assessment, implementing technical controls, and managing incident responses. On the other hand, leadership and management should concentrate on aligning security strategies with the organization’s goals, meeting compliance requirements, and understanding NIST implementation tiers. Tailoring training to specific roles helps healthcare teams integrate NIST standards more efficiently into their operations.
How do we prove the training actually reduced risk?
Healthcare organizations can showcase the impact of training on reducing risk by monitoring specific cybersecurity metrics. These include incident response times, breach detection and reporting times, patch compliance rates, and multi-factor authentication (MFA) coverage.
Another way to gauge progress is by using the NIST Cybersecurity Framework Implementation Tiers (1–4) to evaluate maturity levels. Additionally, automating risk tracking and comparing results against industry benchmarks can provide clear evidence of a stronger security posture.


