Top Tools for Medical Device Firmware Vulnerability Scanning
Post Summary
General IT scanners are not designed for the unique demands of medical device environments — they can cause device crashes in clinical settings, miss firmware-specific vulnerabilities that only appear in compiled binaries, and lack the regulatory compliance automation that FDA 524B and IEC 62304 require. Modern healthcare settings average over 10 connected devices per patient bed, and active scanning can disrupt clinical workflows or void manufacturer warranties. Medical device firmware includes proprietary code, third-party libraries, open-source components, and binary-compiled images that require different scanning approaches — static analysis for source code, binary analysis for compiled firmware, and passive network monitoring for deployed devices. Risk prioritization must account for clinical impact, not just CVSS scores.
Parasoft C/C++test uses static analysis specifically designed for medical device firmware, scanning with over 2,500 checkers aligned with CWE, CERT, and MISRA standards to detect buffer overflows, null pointer dereferences, and memory leaks before code is ever executed. The tool holds TÜV SÜD certification for IEC 62304 compliance and provides FDA 510(k) Qualification Kits that automate tool validation documentation. Its Process Intelligence Engine uses AI to prioritize vulnerabilities by technical impact score, remediation complexity, and exploitation likelihood, and it integrates seamlessly into CI/CD pipelines. Parasoft is the right choice for development teams creating proprietary medical device firmware who need early vulnerability detection with IEC 62304 compliance automation — but requires integration with a Software Composition Analysis tool to address third-party and open-source component risks.
The Finite State Platform uses a binary-first approach that automatically unpacks over 130 binary formats and works with more than 30 architectures — revealing file systems, libraries, and components even in encrypted or proprietary firmware without requiring source code access. Binary SCA extracts function names, control flow graphs, and symbols directly from compiled binaries. Binary SAST identifies zero-day vulnerabilities by analyzing decompiled code for unsafe function calls. Reachability analysis evaluates call graphs and entry points to determine whether vulnerable code paths can actually be executed at runtime — reducing false positives by up to 80% and cutting noise by up to 90%. The platform generates, imports, and enriches SBOMs in SPDX, CycloneDX, and VEX formats, automatically maps findings to FDA 524B and IEC 62304, and generates audit-ready VEX documents with defensible not-affected justifications for unreachable vulnerabilities.
Nessus provides broad vulnerability coverage through over 316,000 plugins covering more than 116,000 CVEs, with an Offline Mode for air-gapped healthcare environments and a 0.32 defects per million scan false positive rate. Its Vulnerability Priority Rating system uses machine learning to evaluate over 109,000 vulnerabilities nightly, identifying the critical 3% that pose the highest risk. However, Nessus is not tailored to medical device regulations or real-time operational needs, and active scanning can cause device crashes or miss firmware-specific issues in specialized clinical equipment. Qualys provides enterprise-scale scanning with over 99.99966% accuracy, passive sensors monitoring network traffic without disrupting clinical workflows, and a dynamic SBOM repository with over 15,000 signatures covering more than 12,000 CVEs. However, Qualys does not support medical device-specific protocols or real-time operational constraints, making it better suited for large IT infrastructure vulnerability management than specialized medical device firmware scanning.
Rapid7 InsightVM emphasizes asset discovery and fingerprinting — identifying open ports, running services, and operating systems including proprietary RTOS — to classify and inventory medical devices across the network without requiring deep binary firmware inspection. Its Active Risk scoring model uses a 1-to-1,000 scale with real-world threat intelligence from Rapid7 Labs, assigns a CVSS score of 10.0 to end-of-life software and operating systems, and allows tagging of medical devices by clinical function or ePHI capability for prioritized risk treatment. At $1.93 per asset per month for up to 500 assets, InsightVM is affordable for healthcare organizations managing complex device inventories. However, traditional scanning methods may not effectively secure connected medical devices — particularly in no-patch scenarios where vendor constraints prevent remediation — and the platform lacks deep firmware-specific analysis capabilities.
Censinet RiskOps™ brings together IT, Risk, Cybersecurity, and BioMed teams to manage medical device firmware risk across healthcare IoMT environments where over 10 connected devices per patient bed create portfolio-scale risk management challenges. The platform automates MDS2 form processing for both 2013 and 2019 versions — capturing device-specific security details without manual data entry — and uses the Digital Risk Catalog™ to compare vulnerabilities against industry benchmarks, generating prioritized reports that guide corrective action. Automated Corrective Action Plans allow teams to track remediation progress, delegate tasks to BioMed specialists, and maintain accountability across IT and clinical teams. Dashboards provide both device-level filtered views and enterprise-wide insights for leadership, ensuring critical firmware vulnerabilities are addressed from individual device to organizational scale.
Medical device firmware vulnerabilities can lead to severe risks, from compromising patient safety to exposing sensitive data. To tackle these challenges, specialized tools help identify and mitigate firmware flaws, ensuring compliance with stringent regulations like FDA 524B and IEC 62304. Here's a quick summary of the top tools covered:
Each tool addresses different aspects of firmware security, from development to compliance and real-time risk management. Below is a comparison for quick reference.
Quick Comparison
Early detection of code issues during development
Limited to proprietary code
Developers creating secure medical device firmware
Binary analysis for third-party software risks
Active scans may disrupt critical devices
Managing software supply chain risks
Broad vulnerability coverage with plugins
Lacks medical-specific focus
General IT environments
Scalable scanning and SBOM tracking
Not tailored for medical devices
Large IT infrastructures
Asset discovery and risk scoring
Limited firmware-specific capabilities
Enterprise security
Healthcare-focused risk management and workflows
Requires collaboration across teams
Healthcare IoMT environments
Choosing the right tool depends on whether your focus is on development, supply chain risks, or compliance. For medical devices, tools with specialized features for firmware and regulatory needs offer the best results.

Medical Device Firmware Vulnerability Scanning Tools Comparison Chart
Top 10 Medical Device Vulnerabilities with Myles Kellerman | Ep. 38
1. Parasoft C/C++test
Parasoft C/C++test offers static analysis specifically designed for medical device firmware, aiming to catch vulnerabilities before the code is ever executed. By using a parsing engine to build an abstract representation of the code, the tool employs dataflow analysis to simulate execution paths. This allows it to detect issues like buffer overflows, null pointer dereferences, and memory leaks [2]. Here's a closer look at what sets Parasoft apart when it comes to firmware analysis.
Firmware Analysis Capabilities
Parasoft scans code with over 2,500 checkers that align with security and safety standards, including CWE, CERT, and MISRA [2]. It goes beyond surface-level checks by analyzing execution paths to identify deeply embedded runtime issues. Additionally, Parasoft has received TÜV SÜD certification for IEC 62304 compliance, a crucial standard for medical device software development [2]. This certification ensures the tool meets the rigorous requirements for safety-critical projects.
Streamlined Compliance
Parasoft simplifies compliance with industry-specific Compliance Packs that feature dynamic tracking dashboards. For FDA 510(k) certification, its Qualification Kits automate the creation of necessary tool validation documentation [2]. Inovytec, a company behind the Ventway Sparrow ventilator, relies on Parasoft for compliance, stating:
"Every time we are going to release a new software version of the Ventway Sparrow ventilator, we make sure that the static analysis from Parasoft is configured to run according to the FDA regulation definitions"
.
Smarter Risk Management
The tool’s Process Intelligence Engine uses AI to assess vulnerabilities and prioritize them based on technical impact scores. This includes evaluating the likelihood of exploitation, the complexity of remediation, and potential costs [2][3]. Solero Technologies, which develops automotive systems, highlighted the benefits:
"Parasoft integrates seamlessly into our CI/CD pipeline. We've embedded test automation and static code analysis early in the development cycle – a huge win for quality assurance in safety-critical automotive projects"
.
2. Finite State Platform
The Finite State Platform uses a binary-first approach to tackle firmware security. It can automatically unpack over 130 binary formats and works with more than 30 architectures, revealing file systems and libraries - even in encrypted or proprietary firmware [5][6]. Instead of relying solely on source code, it employs Binary Software Composition Analysis (SCA) to extract critical details like function names, control flow graphs, and symbols directly from compiled binaries. Its Binary Static Application Security Testing (SAST) goes further, identifying zero-day vulnerabilities by analyzing decompiled code for unsafe function calls [5]. This approach uncovers issues that traditional source code analysis might miss.
Firmware Analysis Depth
What sets Finite State apart is its reachability analysis. This process evaluates call graphs and entry points to determine if vulnerable code paths can actually be executed during runtime [5][7]. By focusing on exploitable vulnerabilities, it separates realistic threats from hypothetical ones. A Product Security Lead from a connected devices company highlighted its value:
"Reachability analysis cut our false positives by 80%. Our developers now trust the alerts because they know they're real, exploitable vulnerabilities."
Beyond runtime evaluations, the platform enhances visibility into the supply chain, providing a deeper understanding of potential risks.
SBOM Support
The platform offers robust support for Software Bill of Materials (SBOMs), working with formats like SPDX, CycloneDX, and VEX [5]. It can generate, import, and enrich SBOMs, aligning binary analysis with source code documentation to uncover "shadow components" - such as legacy code or supplier drivers that only appear in the final product. These dynamic SBOMs notify teams when new CVEs impact components in previously scanned builds [9].
Compliance Automation
Finite State simplifies regulatory compliance by mapping security findings to frameworks like FDA 524B, EU Cyber Resilience Act (CRA), ISO, and IEC 62304 [6][8]. It can automatically generate audit-ready evidence and VEX documents, offering defensible "not affected" justifications for unreachable vulnerabilities - essential for FDA submissions [6][7]. A Head of Compliance from the energy and utilities sector shared their experience:
"Compliance reporting that used to take weeks now takes hours. The platform automatically maps our security posture to regulatory requirements."
Risk Prioritization
The platform doesn’t stop at compliance; it prioritizes risks using reachability data combined with exploit intelligence from over 200 sources. Instead of relying solely on severity scores, it focuses on vulnerabilities that pose real-world risks [6][7]. This targeted approach reduces noise by up to 90%, enabling security teams to concentrate on the most pressing threats for their firmware [6][7].
3. Nessus
Nessus uses a plugin-based approach for firmware vulnerability scanning, boasting an impressive library of over 316,000 plugins, with more than 100 new ones added every week. These plugins help identify vulnerabilities, missing patches, and misconfigurations, covering over 116,000 CVEs [10]. The platform supports both credentialed (authenticated) and non-credentialed scanning methods [11], providing a detailed look into device internals while maintaining an impressively low false positive rate of just 0.32 defects per 1 million scans [10].
Firmware Analysis Depth
For environments like healthcare, where devices often operate in air-gapped or isolated settings, Nessus offers an Offline Mode. This mode allows thorough assessments without requiring internet access [11]. This feature is especially valuable for medical devices that must remain disconnected from external networks, enabling security teams to rely on accurate results without being bogged down by false positives [10].
Compliance Automation
Nessus simplifies regulatory compliance with over 450 pre-built templates tailored for frameworks like HIPAA, NIST 800-53, CIS, and DISA STIG. It also offers flexible deployment options, including the use of devices like Raspberry Pi [10]. These templates significantly reduce the manual workload during audits and extend scanning capabilities to distributed or embedded medical device systems.
Risk Prioritization
Instead of treating every vulnerability equally, Nessus uses a Vulnerability Priority Rating (VPR) system with scores ranging from 0.1 to 10.0 [12][13]. This machine-learning-driven feature evaluates over 109,000 vulnerabilities each night to identify the "critical 3%" that pose the highest risk [12][13]. By combining VPR with Exploit Prediction Scoring System (EPSS) scores [10], Nessus ensures remediation efforts target the vulnerabilities most likely to be exploited.
Pricing for Nessus Professional starts at about $4,790 for a 1-year license. For personal projects, Nessus Essentials is available for free, though it's limited to scanning up to 16 IP addresses [10][11]. This robust prioritization framework makes Nessus a cost-effective tool for managing vulnerabilities and sets the stage for exploring the unique capabilities of the next tool.
4. Qualys
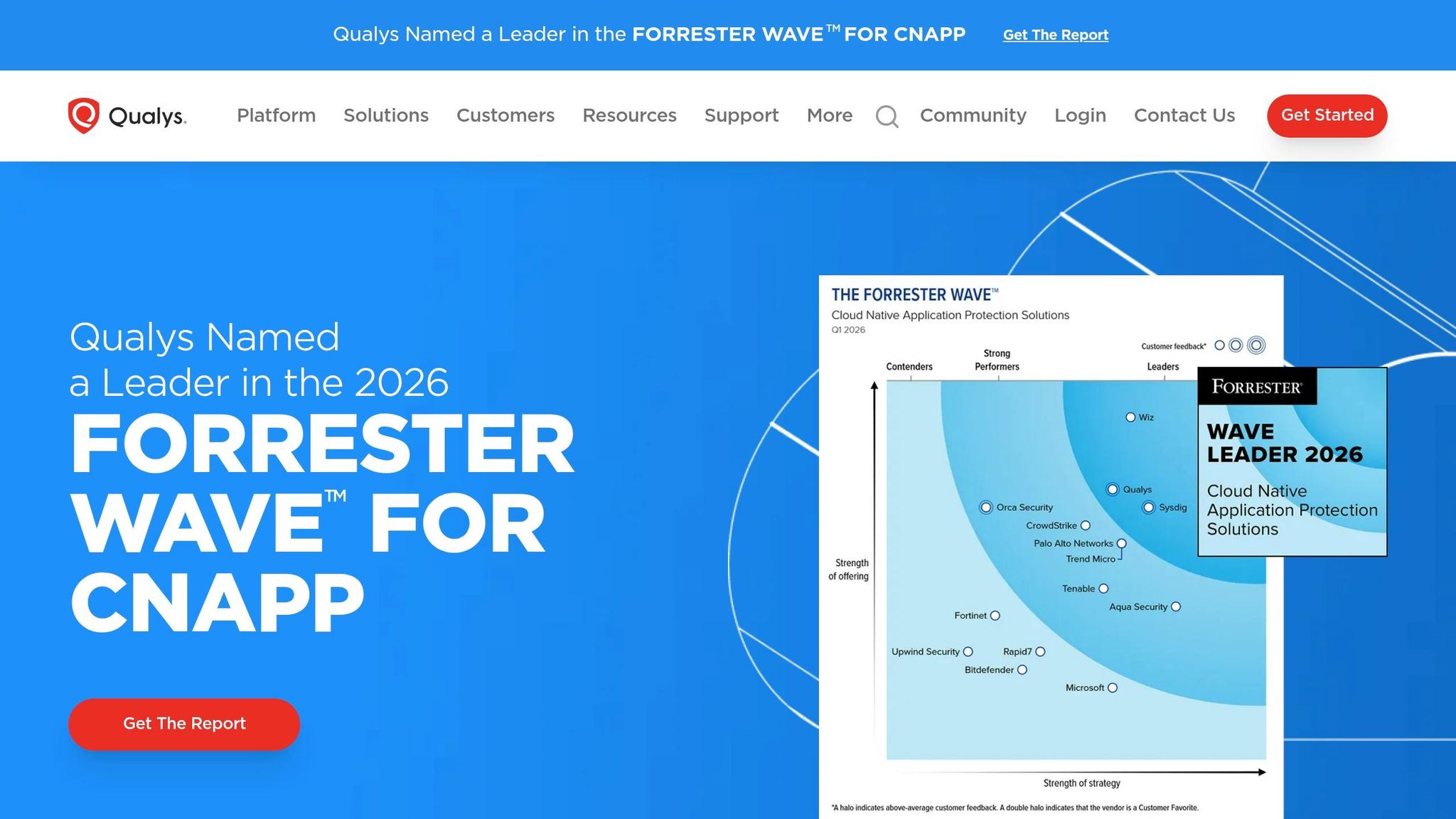
Qualys uses a combination of black-box scanners and passive sensors to provide comprehensive visibility into medical devices across both cloud and on-premise environments [16]. It performs Runtime Software Composition Analysis (SCA) to inventory software components within connected devices [14]. This capability is especially useful for healthcare organizations managing diverse fleets of medical devices, as its passive sensors monitor network traffic in real time without disrupting clinical workflows [16]. This creates a solid foundation for detailed analysis and proactive risk management.
Firmware Analysis Depth
Qualys goes beyond basic vulnerability detection, achieving accuracy levels of over 99.99966%, which virtually eliminates false positives [15]. It’s also capable of identifying vulnerabilities up to six times faster than many competitors [14]. With more than 60,000 active scanners and 55,000 virtual scanners deployed worldwide [16], Qualys provides the infrastructure necessary for large-scale medical device assessments. Additionally, its passive discovery feature detects Advanced Persistent Threat (APT) traffic without interrupting clinical operations [16].
SBOM Support
Qualys takes its scanning capabilities further by offering advanced Software Composition Analysis (SwCA) to manage embedded software components. It maintains a dynamic repository of Software Bills of Materials (SBOM) with over 15,000 signatures, covering more than 12,000 CVEs [17]. This repository provides visibility into both open-source and commercial software components, helping organizations identify vulnerabilities in software stacks and mitigate supply chain risks, such as those linked to Log4Shell. Cloud Agents and passive sensors work together to identify IoT and embedded devices across the network, ensuring real-time visibility [35, 33].
Risk Prioritization
To help organizations focus on the most pressing vulnerabilities, Qualys uses advanced threat intelligence for prioritization. Its TruRisk engine aggregates data from over 25 threat intelligence sources, going beyond standard CVSS scores to prioritize vulnerabilities based on exploitability and business context [14]. This approach has allowed organizations to reduce critical vulnerabilities by 85% and cut Mean Time to Remediate (MTTR) by 60%, thanks to integrated patching and remediation workflows [14].
Tom Scheffler, Security Operations Manager at Cintas, summed up the platform’s efficiency:
"Qualys scans it, finds it, patches it. That's it. In terms of time, manpower, planning, and the cost reduction in savings of labor dollars...huge"
.
On top of that, Qualys automates compliance reporting for healthcare standards such as HIPAA, PCI DSS 4.0, and CIS benchmarks [31, 32].
sbb-itb-535baee
5. Rapid7 InsightVM
Rapid7 InsightVM offers a practical way to secure medical devices by emphasizing asset discovery and fingerprinting rather than diving deep into binary firmware inspection. The platform identifies critical details like open ports, running services, and operating systems (including proprietary RTOS) to classify devices across the network. This method is especially useful in healthcare, where traditional vulnerability scanners often fail to address firmware-specific challenges.
Firmware Analysis Depth
InsightVM uses fingerprinting to catalog medical devices without interrupting clinical operations. Joe Agnew, a Security Analyst at Rapid7, highlights the limitations of traditional scanners: “Information security should never harm a patient.” Instead, he recommends conducting detailed tests in pre-production environments. By identifying devices accurately, InsightVM lays the groundwork for more effective risk management.
Risk Prioritization
One standout feature of InsightVM is its Active Risk scoring model, which uses a scale from 1 to 1,000 - offering a more nuanced approach than standard CVSS metrics. The platform integrates real-world threat intelligence from Rapid7 Labs and its Emergent Threat Response program to identify vulnerabilities that are actively being exploited. It also uses AI-based CVSS scoring to predict severity levels based on historical data and assigns a CVSS score of 10.0 to any software or operating system that has reached end-of-life.
Security teams can further enhance risk prioritization by tagging medical devices based on their clinical functions or ePHI capabilities, ensuring that high-risk assets automatically receive greater attention. This approach aligns seamlessly with InsightVM's compliance-focused features.
Compliance Automation
InsightVM simplifies compliance by automating assessments for HIPAA, PCI DSS, and CIS standards. The platform updates its threat database every six hours, ensuring it captures the latest vulnerabilities. It also generates "Top Remediation" reports to guide security teams on immediate actions. Neil Johnson, Security Manager at Evercore, shares:
"We don't even have to wait for a scan to finish before we can start patching - we can do it straight away and then instantly see our risk score go down."
At a cost of $1.93 per asset per month for up to 500 assets [18], InsightVM offers an affordable solution for healthcare organizations managing complex medical device inventories.
6. Censinet RiskOps™

Censinet RiskOps™ brings together IT, Risk, Cybersecurity, and BioMed teams to tackle the challenges of medical device security and firmware risk in healthcare. With the growing complexity of the Internet of Medical Things (IoMT) - where modern healthcare settings often have over 10 connected devices per patient bed - this platform addresses a pressing need for streamlined risk management [19].
Risk Prioritization
The platform simplifies risk management by automatically assigning risk ratings and using its Digital Risk Catalog™ to compare vulnerabilities against industry benchmarks. This generates concise reports that help guide teams toward effective corrective actions. Instead of working in silos, healthcare teams can conduct quick security assessments and act on prioritized risks.
Censinet RiskOps™ also streamlines remediation with Automated Corrective Action Plans (CAPs). These plans allow teams to track progress, delegate tasks to specialists like BioMed staff, and maintain accountability. The platform’s dashboards offer filtered views for specific devices while also providing enterprise-wide insights for leadership. This ensures that critical firmware vulnerabilities are addressed promptly and effectively, from individual devices to the organizational level.
Additionally, these risk insights feed directly into compliance workflows, ensuring vulnerabilities are managed in line with regulatory standards.
Compliance Automation
Censinet RiskOps™ takes the hassle out of compliance by automating the processing of Manufacturer Disclosure Statement for Medical Device Security (MDS2) forms. It supports both the 2013 and 2019 versions, capturing device-specific security details without the need for manual data entry. This automation includes parsing forms, gathering evidence, and managing a centralized digital inventory - creating a clear audit trail for both internal and external reviews.
Given that medical device security often receives minimal attention within healthcare cybersecurity practices [19], this centralized approach ensures that firmware vulnerabilities are actively monitored and resolved. By combining Automated CAPs with clear task assignments, the platform keeps BioMed and IT teams aligned and focused on addressing high-risk issues efficiently.
Feature Comparison Table
When selecting a tool, it's important to align your choice with your organization's specific needs, available resources, and device environment. Below is a comparison of tools, detailing their strengths, limitations, and ideal use cases.
Detects security flaws and quality issues in proprietary code during development, allowing early fixes.
Focuses only on proprietary code; requires integration with Software Composition Analysis (SCA) for third-party and open-source risks.
Best for development teams creating medical device firmware that demands secure, high-quality code.
Addresses software supply chain risks for both open-source and commercial third-party software, offering active and passive scanning.
Active scanning needs careful management to avoid disrupting critical devices; passive scanning may lack depth.
Suited for organizations managing complex software bills of materials and addressing supply chain risks.
A general-purpose vulnerability scanner offering broad coverage.
Not tailored to medical regulations or real-time operational needs; may cause device crashes or miss firmware-specific issues.
Works well in standard IT environments but not for specialized medical device firmware.
Provides enterprise-scale vulnerability management with detailed reporting.
Does not support medical device-specific protocols or real-time operational constraints.
Ideal for large IT infrastructures needing general vulnerability management.
Offers in-depth vulnerability assessment with risk prioritization features.
Traditional methods may not secure connected medical devices effectively, especially in no-patch scenarios.
Suitable for general enterprise security but limited for medical device firmware with patching constraints.
Brings IT, risk, cybersecurity, and biomedical teams together with risk prioritization and automated workflows.
Requires a commitment to collaborative workflows for risk management.
Best for healthcare organizations managing Internet of Medical Things (IoMT) environments.
These tools showcase varying strengths and challenges in addressing firmware vulnerabilities within healthcare settings. General IT scanners often fall short when dealing with the unique demands of medical environments, such as regulatory compliance, operational constraints, and patient safety concerns. As highlighted, combining Static Application Security Testing (SAST) with Software Composition Analysis (SCA) aligns with FDA guidelines, while risk-based prioritization helps address practical threats effectively [20][21].
Conclusion
Firmware vulnerability scanning tools play a critical role in safeguarding patient safety, meeting regulatory standards, and bolstering cybersecurity efforts in healthcare. With medical devices averaging 6.2 vulnerabilities per device and 62% of major vulnerabilities in U.S. hospitals left unaddressed, the risks are undeniable [22]. Add to that the staggering cost of a cyberattack - estimated at $80,000 per hour if hospital operations are disrupted - and it’s clear that proactive security measures are not just about compliance but also about financial survival [22].
Different tools cater to specific stages of the security lifecycle. For example, Parasoft C/C++test supports secure development by helping manufacturers write safer code from the outset. Tools like Finite State focus on managing software supply chain risks, while general-purpose scanners such as Nessus and Qualys provide broad IT coverage but lack the specialized features required for medical devices. For healthcare organizations managing complex IoMT environments, Censinet RiskOps™ offers a collaborative approach to risk management, bringing together IT, cybersecurity, and biomedical teams with automated workflows and risk prioritization. The right choice depends on your organization's unique security and compliance needs.
When selecting a solution, consider whether your priority lies in pre-market activities like static analysis and SBOM creation or post-market needs like real-time monitoring. Tools designed specifically for medical environments can reduce false positives by up to 95% compared to general-purpose scanners [1]. This precision is vital for maintaining operational efficiency and security.
Integration is another key factor. Look for tools that seamlessly integrate into existing CI/CD workflows, enabling continuous reporting through platforms like GitHub Actions or Azure DevOps. Solutions that offer FDA-ready reporting - including formats like VEX, VDR, and SBOM - can also speed up regulatory compliance efforts.
Cybersecurity in healthcare is an ongoing process. Continuous monitoring and proactive defenses are essential to protect both patient data and lives. By combining secure development practices, transparency in the software supply chain, and robust operational risk management, healthcare organizations can create a resilient defense system that addresses the unique challenges of medical device security.
FAQs
How do I choose between source-code scanning and binary firmware scanning?
Choosing between source-code scanning and binary firmware scanning comes down to your security objectives and where you are in the device lifecycle.
For the best results, combining both methods can be effective. This approach provides early detection during development while offering a comprehensive view of vulnerabilities in the finished firmware.
Can firmware scanning be done safely without disrupting patient care?
Yes, firmware scanning can be performed safely without interfering with patient care. Tools such as the Medical Device Security Analyzer are designed to pinpoint vulnerabilities and recommend ways to address them, ensuring devices remain secure. Additionally, platforms like Censinet RiskOps™ offer continuous threat detection and real-time monitoring, making it easier to manage risks effectively while prioritizing patient safety.
What scan outputs are most helpful for FDA 524B and IEC 62304 compliance?
When it comes to meeting FDA 524B and IEC 62304 standards, certain scan outputs prove especially useful. These include vulnerability scan results, risk assessments, and FDA-ready reports.
Tools like Censinet RiskOps™ simplify this process by organizing critical evidence, automating the tracking of vulnerabilities, and ensuring smoother alignment with regulatory requirements.
Related Blog Posts
- Best Practices for FDA IoT Cybersecurity Compliance
- Study: 162 New Medical Device Vulnerabilities Found
- Why Patch Validation Matters for Medical Devices
- Medical Device Protocol Cybersecurity Basics
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":[{"@type":"Question","name":"How do I choose between source-code scanning and binary firmware scanning?","acceptedAnswer":{"@type":"Answer","text":"<p>Choosing between <strong>source-code scanning</strong> and <strong>binary firmware scanning</strong> comes down to your security objectives and where you are in the device lifecycle.</p> <ul> <li> <strong>Source-code scanning</strong>: This works well when you have access to the original code. It allows you to catch potential issues early during development, making it easier to address vulnerabilities before they become a problem. </li> <li> <strong>Binary scanning</strong>: This is more suited for assessing compiled firmware, especially when dealing with third-party components or already-deployed devices. It helps uncover vulnerabilities in the final product. </li> </ul> <p>For the best results, combining both methods can be effective. This approach provides early detection during development while offering a comprehensive view of vulnerabilities in the finished firmware.</p>"}},{"@type":"Question","name":"Can firmware scanning be done safely without disrupting patient care?","acceptedAnswer":{"@type":"Answer","text":"<p>Yes, firmware scanning can be performed safely without interfering with patient care. Tools such as the <strong><a href=\"https://www.censinet.com/perspectives/medical-device-security-analyzer\">Medical Device Security Analyzer</a></strong> are designed to pinpoint vulnerabilities and recommend ways to address them, ensuring devices remain secure. Additionally, platforms like <strong>Censinet RiskOps™</strong> offer continuous threat detection and real-time monitoring, making it easier to manage risks effectively while prioritizing patient safety.</p>"}},{"@type":"Question","name":"What scan outputs are most helpful for FDA 524B and IEC 62304 compliance?","acceptedAnswer":{"@type":"Answer","text":"<p>When it comes to meeting FDA 524B and IEC 62304 standards, certain scan outputs prove especially useful. These include <strong>vulnerability scan results</strong>, <strong>risk assessments</strong>, and <strong>FDA-ready reports</strong>.</p> <p>Tools like <em>Censinet RiskOps™</em> simplify this process by organizing critical evidence, automating the tracking of vulnerabilities, and ensuring smoother alignment with regulatory requirements.</p>"}}]}
Key Points:
Why do general IT vulnerability scanners fail to meet the specific requirements of medical device firmware security and what approach is required?
- Active scanning can harm patients and void warranties in clinical environments — General IT vulnerability scanners are designed for enterprise network environments where active scanning is a routine and reversible activity. In medical device environments, active scanning can disrupt device operation, affect clinical functions such as infusion pump dosing or patient monitoring alerts, and void manufacturer warranties — consequences that make active scanning an inappropriate default approach for deployed clinical devices.
- Firmware-specific vulnerabilities invisible to network-layer scanners — Vulnerabilities in medical device firmware embedded in compiled binary images — including hardcoded credentials, unsafe function calls, buffer overflows in proprietary code, and shadow components from legacy supplier drivers — are not visible to network-layer scanners that evaluate the device's external attack surface. Identifying these vulnerabilities requires either static source code analysis during development or binary analysis of compiled firmware images.
- 10+ connected devices per patient bed creating portfolio-scale scanning requirements — Modern healthcare settings average over 10 connected devices per patient bed — a density that means a mid-sized hospital may manage thousands of connected devices from dozens of manufacturers across multiple device categories. Scanning tools that require device-by-device manual configuration cannot scale to this portfolio density without dedicated staffing that most healthcare security teams do not have.
- FDA 524B and IEC 62304 compliance requiring tool-specific regulatory documentation — Section 524B requires SBOM documentation for all cyber device premarket submissions, and IEC 62304 requires software lifecycle documentation including static analysis tool validation records. General IT scanners do not provide the regulatory compliance automation — FDA 510(k) Qualification Kits, IEC 62304-certified analysis, SBOM generation in SPDX or CycloneDX — that medical device regulatory submissions require.
- Combining SAST with SCA aligning with FDA guidelines for firmware security — The FDA's guidance recommends combining Static Application Security Testing for proprietary code with Software Composition Analysis for third-party and open-source components — an approach that addresses both the code quality vulnerabilities detectable through static analysis and the supply chain vulnerabilities in components that static analysis of proprietary code alone cannot surface.
- Risk prioritization requiring clinical context beyond CVSS scores — CVSS scores reflect technical severity but not clinical impact. A vulnerability enabling unauthorized remote access to an infusion pump is more urgent than a high-CVSS vulnerability in an administrative reporting module regardless of their relative CVSS scores. Risk prioritization for medical devices must incorporate clinical function, patient safety impact, and network connectivity context that general IT risk scoring frameworks do not capture.
What makes Parasoft C/C++test the appropriate choice for medical device firmware development and what are its scope limitations?
- 2,500-plus checkers covering CWE, CERT, and MISRA as the compliance baseline — Parasoft's 2,500-plus checkers aligned with CWE common weakness enumeration, CERT secure coding standards, and MISRA guidelines provide the comprehensive early-stage vulnerability detection that safety-critical firmware development requires. These standards represent the security and safety requirements that FDA reviewers and IEC 62304 assessors will evaluate — making Parasoft's coverage alignment with these frameworks a compliance relevance advantage over general static analysis tools.
- TÜV SÜD IEC 62304 certification as the medical device regulatory differentiator — TÜV SÜD certification for IEC 62304 compliance is not a marketing claim — it is an independent third-party verification that Parasoft's analysis methodology meets the rigorous requirements for safety-critical medical device software development tools. This certification enables manufacturers to use Parasoft's analysis outputs directly in FDA submissions and IEC 62304 compliance documentation without additional tool validation effort.
- FDA 510(k) Qualification Kits eliminating manual tool validation documentation — FDA 510(k) submissions require tool validation documentation demonstrating that the software tools used in development are appropriate for their intended purpose. Parasoft's Qualification Kits automate the creation of this documentation — eliminating a significant manual effort that development teams building 510(k) submissions without automated documentation support must generate from scratch.
- AI-powered Process Intelligence Engine for risk prioritization — The Process Intelligence Engine's AI-driven prioritization evaluates vulnerabilities by technical impact score, remediation complexity, and exploitation likelihood — combining dimensions that pure CVSS severity scoring ignores. This multi-dimensional prioritization helps development teams allocate remediation resources to the vulnerabilities with the highest combination of exploitability and impact rather than treating all high-severity findings as equally urgent.
- CI/CD pipeline integration enabling shift-left security in firmware development — Integrating Parasoft into CI/CD pipelines ensures that static analysis runs on every build automatically — detecting vulnerabilities when they are least expensive to fix rather than discovering them during pre-submission testing when code changes require the most rework. The shift-left security principle is particularly valuable for medical device firmware where late-stage vulnerability discovery can delay FDA submissions by months.
- Scope limitation requiring SCA integration for complete firmware security — Parasoft's static analysis covers proprietary code but does not address vulnerabilities in third-party libraries, open-source components, or binary-compiled elements from suppliers. Organizations using Parasoft must integrate a complementary Software Composition Analysis tool — such as the Finite State Platform — to achieve the complete firmware security coverage that FDA SBOM requirements and supply chain risk management demand.
What makes the Finite State Platform uniquely suited for medical device supply chain and binary firmware security and how does reachability analysis reduce false positives?
- Binary-first approach accessing firmware without source code — The Finite State Platform's binary-first approach enables vulnerability analysis of compiled firmware images without requiring access to proprietary source code — a critical capability for healthcare delivery organizations and independent security researchers who receive devices from manufacturers without source code disclosure. Automatic unpacking of over 130 binary formats across more than 30 architectures provides analysis coverage across the diverse firmware architectures present in medical device portfolios.
- Binary SCA revealing shadow components invisible to source code analysis — Binary SCA extracts component information directly from compiled binaries — including function names, control flow graphs, and symbols — revealing shadow components such as legacy code modules and supplier-provided drivers that only appear in the final compiled binary and that source code analysis performed during development would not capture. These shadow components represent a hidden vulnerability surface that is only visible through binary analysis.
- Reachability analysis cutting false positives by 80% — Reachability analysis evaluates whether a vulnerable code path can actually be executed during device runtime by analyzing call graphs and entry points. A vulnerability in a component that is never reachable during normal device operation is not an exploitable threat regardless of its CVSS score. By filtering vulnerabilities to only those with reachable execution paths, Finite State reduces false positives by up to 80% — enabling security teams to trust alerts as indicators of real exploitable vulnerabilities rather than theoretical risks.
- Dynamic SBOMs notifying teams when new CVEs affect previously scanned builds — Unlike static SBOMs that represent device composition at a point in time, Finite State's dynamic SBOMs continuously monitor previously scanned builds against newly published CVEs — notifying teams when a component present in an already-shipped device is newly identified as vulnerable. This continuous monitoring capability is essential for maintaining the postmarket surveillance that FDA regulations require for devices with 10 to 15 year operational lifespans.
- VEX document generation providing defensible not-affected justifications — Vulnerability Exploitability eXchange documents generated by the Finite State Platform provide defensible justifications for why specific listed vulnerabilities do not affect a particular device — based on reachability analysis demonstrating that the vulnerable code path cannot be executed. These VEX documents reduce the burden on healthcare facilities that would otherwise need to independently investigate every CVE listed in a device's SBOM.
- FDA 524B, EU CRA, ISO, and IEC 62304 compliance mapping with automated audit evidence — Automatic mapping of security findings to FDA 524B, EU Cyber Resilience Act, ISO, and IEC 62304 frameworks generates audit-ready evidence aligned with the specific compliance requirements of each framework — compressing compliance reporting from weeks to hours as organizations report from energy and utilities sectors have confirmed, and providing the multi-framework compliance documentation that increasingly globally-distributed medical device supply chains require.
How do Nessus and Qualys serve healthcare vulnerability management programs and what medical device-specific gaps must organizations address?
- Nessus Offline Mode enabling assessment of air-gapped healthcare devices — Many medical devices operate in air-gapped or isolated network segments that prevent internet connectivity for security purposes. Nessus's Offline Mode enables thorough vulnerability assessments in these isolated environments without requiring internet access — a capability that most cloud-dependent scanning platforms cannot provide for devices that must remain disconnected from external networks for clinical or security reasons.
- Nessus VPR machine learning identifying the critical 3% of highest-risk vulnerabilities — Nessus's Vulnerability Priority Rating system evaluates over 109,000 vulnerabilities nightly using machine learning, identifying the critical 3% that represent the highest real-world risk. Combined with EPSS integration for exploitation probability, this nightly re-evaluation ensures that risk prioritization reflects the current threat landscape rather than static severity scores assigned at vulnerability disclosure.
- Qualys passive sensors monitoring clinical environments without disruption — Qualys's passive sensors monitor network traffic in real time to detect device vulnerabilities, APT traffic, and configuration anomalies without sending active scan traffic that could disrupt clinical device operation. This passive approach is specifically valuable in healthcare environments where clinical workflow continuity is a patient safety requirement and active scanning is not appropriate for all device categories.
- Qualys TruRisk reducing critical vulnerabilities by 85% and MTTR by 60% — Qualys's TruRisk engine aggregating threat intelligence from over 25 sources has enabled organizations to reduce critical vulnerabilities by 85% and cut Mean Time to Remediate by 60% through integrated patching and remediation workflows. These outcomes reflect the efficiency gains that organizations achieve when vulnerability prioritization is driven by aggregated threat intelligence rather than CVSS scores alone.
- Medical device-specific gaps requiring supplementary tools for both platforms — Neither Nessus nor Qualys is tailored to medical device-specific protocols, firmware binary analysis, or the operational constraints that clinical device management requires. Both platforms are well-suited for general healthcare IT infrastructure vulnerability management — servers, workstations, network equipment, and software applications — but require supplementary tools such as Finite State Platform or Censinet RiskOps™ to address firmware-specific vulnerabilities and IoMT risk management requirements.
- 450-plus Nessus pre-built compliance templates covering HIPAA and NIST 800-53 — Nessus's library of over 450 pre-built compliance templates covering HIPAA, NIST 800-53, CIS, and DISA STIG substantially reduces manual audit preparation effort for healthcare organizations with extensive compliance reporting obligations. The ability to deploy Nessus on devices such as Raspberry Pi for distributed or embedded system assessments extends scanning capabilities to medical device environments where full scanner appliance deployment is not practical.
How does Rapid7 InsightVM approach medical device security and what are the clinical environment constraints that limit its firmware analysis depth?
- Fingerprinting cataloging devices without disrupting clinical operations — InsightVM's device identification through fingerprinting — cataloging open ports, running services, operating systems, and device attributes — provides the device inventory visibility that risk management requires without sending active scan traffic that could affect clinical device operation. This non-disruptive identification approach reflects the principle that information security should never harm a patient — a constraint that shapes the appropriate scanning methodology for clinical environments.
- Active Risk 1-to-1,000 scoring model with real-world threat intelligence — InsightVM's Active Risk scoring model provides more granular risk differentiation than the 0-to-10 CVSS scale, incorporating real-world threat intelligence from Rapid7 Labs and the Emergent Threat Response program to identify vulnerabilities currently being actively exploited. AI-based CVSS scoring predicts severity based on historical data, and automatic assignment of a 10.0 CVSS score to end-of-life software ensures that unsupported legacy components in medical devices receive maximum risk attention.
- Clinical function tagging enabling patient safety-informed risk prioritization — The ability to tag medical devices by clinical function — identifying which devices are responsible for medication delivery, cardiac monitoring, ventilation, or ePHI access — enables risk prioritization that weights patient safety impact alongside technical severity. High-risk clinical function devices automatically receive elevated attention regardless of their network vulnerability score, aligning remediation prioritization with clinical risk rather than purely technical risk.
- Pre-production testing recommendation addressing no-patch clinical device constraints — InsightVM explicitly recommends conducting detailed vulnerability testing in pre-production environments for medical devices where testing in clinical deployment environments carries patient safety risk. This recommendation acknowledges the clinical constraint that distinguishes medical device security from enterprise IT security — not all vulnerabilities can be remediated through patching, and some testing activities that are routine in IT environments are inappropriate for clinical devices.
- End-of-life CVSS 10.0 assignment creating visibility for legacy medical device risk — Automatically assigning a CVSS score of 10.0 to any software or operating system that has reached end-of-life creates maximum-priority visibility for the legacy device vulnerability that the 73% of healthcare organizations operating equipment on outdated systems face. This automatic scoring ensures that end-of-life device risk is consistently reflected in risk dashboards rather than being underweighted against other vulnerability categories.
- Enterprise security positioning limiting deep firmware analysis capability — InsightVM is designed as an enterprise security platform and its medical device support is built on asset discovery and network-layer assessment rather than firmware binary analysis. For organizations requiring deep analysis of proprietary firmware code, binary component extraction, or supply chain dependency mapping, InsightVM requires supplementation with firmware-specific tools such as Parasoft or Finite State Platform.
How does Censinet RiskOps™ complement firmware scanning tools by addressing the healthcare-specific IoMT risk management requirements that technical scanners cannot satisfy?
- IoMT-specific risk management spanning IT, BioMed, and clinical teams — Technical firmware scanning tools identify vulnerabilities but do not manage the cross-functional response that medical device risk requires — coordinating IT security teams, BioMed engineers responsible for device maintenance, clinical staff managing patient care, and compliance officers tracking regulatory obligations. Censinet RiskOps™ provides the workflow infrastructure that converts firmware vulnerability findings into managed, accountable remediation activities across all four team dimensions.
- Automated MDS2 processing eliminating manual device security disclosure intake — Processing Manufacturer Disclosure Statements for Medical Device Security manually for hundreds or thousands of devices is an operational impossibility at the scale of modern healthcare IoMT environments. Censinet RiskOps™ automates MDS2 intake for both 2013 and 2019 versions — parsing forms, capturing device-specific security details, and building the centralized digital inventory that enables portfolio-level device security management without manual data entry.
- Digital Risk Catalog™ enabling benchmark-based vulnerability prioritization — The Digital Risk Catalog™ enables comparison of device vulnerabilities against industry benchmarks rather than evaluating each device's risk in isolation. This benchmarking context reveals whether a specific device's vulnerability profile is above or below the industry standard for that device category — enabling proportional remediation investment that reflects relative risk rather than absolute vulnerability count.
- Automated Corrective Action Plans with BioMed delegation and accountability tracking — Automated CAPs generated from vulnerability findings assign specific remediation tasks to the appropriate team — routing firmware patching tasks to BioMed specialists, network segmentation tasks to IT security, and compliance documentation to the compliance officer — with progress tracking and accountability that ensures findings are not lost in the handoff between teams or allowed to age without resolution.
- Dual dashboard visibility from device level to enterprise leadership — Filtered device-level dashboards enable biomedical engineers to manage their specific device portfolios, while enterprise-wide dashboards provide leadership with the organizational risk picture needed for strategic investment decisions and regulatory reporting. This dual visibility structure ensures that both operational teams and organizational leadership are working from the same risk data rather than generating separate reports for different audiences.
- Complementing technical scanners in the full medical device security stack — Censinet RiskOps™ is not a firmware scanner — it is the risk management infrastructure that makes firmware scanning findings actionable at healthcare portfolio scale. Organizations with the most effective medical device security programs use technical tools such as Finite State Platform for binary analysis, Parasoft for development-time static analysis, and passive network tools for deployed device monitoring, with Censinet RiskOps™ centralizing the findings, prioritizing by clinical impact, managing remediation workflows, and maintaining the compliance documentation that FDA postmarket surveillance and regulatory audits require.


