Best Practices for Cloud-Based App Vulnerability Testing
Post Summary
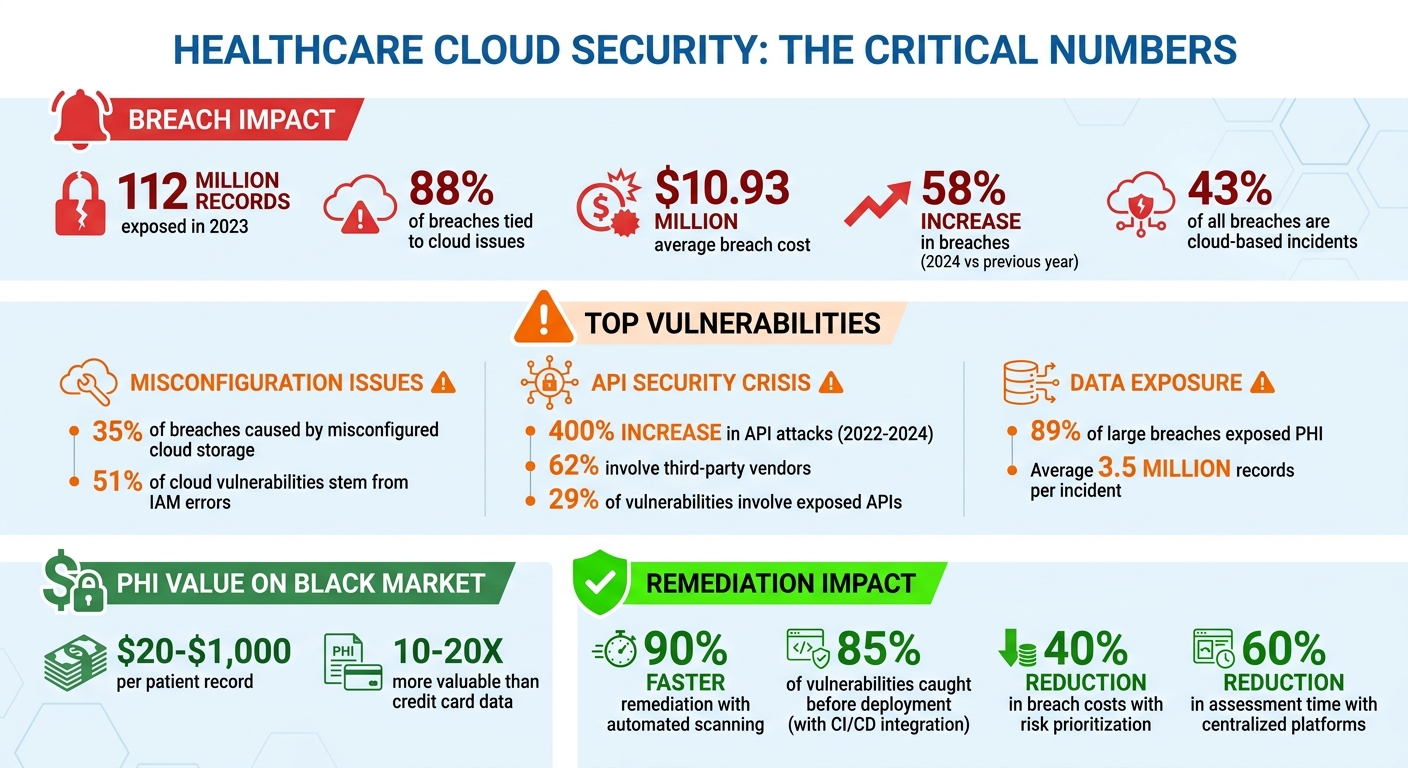
Healthcare organizations increasingly rely on cloud services, but this shift exposes them to significant security risks. In 2023, healthcare breaches exposed 112 million records, with 88% tied to cloud issues like misconfigurations and weak access controls. The financial impact is severe, with average breach costs reaching $10.93 million. These vulnerabilities make proactive cloud-based vulnerability testing critical for safeguarding sensitive data and maintaining compliance with regulations like HIPAA.
Here’s what you need to know:
- Common Threats: Misconfigured cloud storage causes 35% of breaches. Identity and access management (IAM) errors account for 51% of cloud vulnerabilities, and API attacks in healthcare increased by 400% between 2022 and 2024.
- Testing Practices: Continuous automated scanning and integrating security checks into CI/CD pipelines are key to identifying and fixing vulnerabilities faster. Prioritizing high-risk issues based on their impact on patient safety and compliance is essential.
- Tools and Solutions: Platforms like Censinet RiskOps streamline vulnerability management with AI-driven assessments, automated workflows, and centralized reporting tailored for healthcare.
Healthcare Cloud Security Statistics: Breach Costs, Vulnerabilities, and Attack Trends 2023-2024
The Secret to Vulnerability Management in Healthcare | David Hazar
sbb-itb-535baee
Common Vulnerabilities in Healthcare Cloud Applications
Healthcare cloud applications face a unique set of threats that demand attention. Understanding these vulnerabilities is crucial for implementing robust cloud-based vulnerability testing.
Why PHI and Clinical Systems Are High-Value Targets
Protected Health Information (PHI) is an attractive prize for cybercriminals. On the black market, a single patient record can fetch anywhere from $20 to $1,000, depending on how detailed it is. That’s 10 to 20 times more than the value of stolen credit card data. Why? These records enable crimes like identity theft, insurance fraud, and even targeted phishing.
Clinical systems, such as electronic health records (EHRs) and telemedicine platforms, also face significant risks. Disrupting these systems can have life-threatening consequences. For example, in February 2023, Change Healthcare fell victim to a ransomware attack through a compromised Citrix portal in their cloud environment. This attack disrupted prescription processing nationwide for weeks, impacting over 100 million records. Faced with such stakes, healthcare organizations often feel compelled to pay substantial ransoms.
The numbers paint a grim picture. In 2024, healthcare data breaches increased by 58% compared to the previous year, with cloud-based incidents making up 43% of all cases. Alarmingly, PHI was exposed in 89% of large breaches, averaging 3.5 million records per incident. For eight years running, healthcare has been the most breached sector in the U.S., emphasizing the urgent need to address vulnerabilities in cloud environments.
How Cloud Misconfigurations Lead to Data Breaches
Misconfigured cloud storage is responsible for 35% of healthcare breaches. Even small mistakes, like leaving an S3 bucket unprotected or neglecting to enable encryption, can expose millions of patient records to unauthorized access.
A notable example occurred in August 2021 when the American Medical Collection Agency left an ElasticSearch instance unsecured in their cloud setup. This oversight exposed the PHI of 21.9 million patients, including sensitive details like Social Security numbers and medical diagnoses. The fallout was severe, culminating in a $6.5 million settlement. Similarly, in 2024, MultiPlan’s AWS misconfiguration left 600 gigabytes of PHI accessible through search engines due to default "public" settings that were never updated.
Identity and access management (IAM) issues are another major problem. 51% of healthcare cloud vulnerabilities stem from IAM errors, such as overly permissive roles that allow attackers to move freely within systems after gaining access. A case in point is the 2022 Banner Health breach, where default AWS settings exposed 4 terabytes of data because security groups allowed unauthorized inbound traffic. Beyond these configuration errors, vulnerabilities in system integrations further heighten risks.
API Security Risks and Third-Party Integration Vulnerabilities
APIs serve as the backbone of many healthcare applications, but they also create numerous entry points for attackers. Between 2022 and 2024, API attacks in healthcare surged by 400%, with 62% involving third-party vendors.
One of the most common API vulnerabilities is broken object-level authorization (BOLA). This flaw allows attackers to access other patients’ records simply by altering an ID number in a request. Many healthcare APIs still rely on outdated authentication methods, such as shared API keys, instead of using more secure options like OAuth flows with mutual TLS.
Third-party integrations compound these risks. Take the 2023 MOVEit breach, for example. This incident exploited a vulnerability in third-party file transfer software, compromising 2,700 healthcare organizations. These vendors often have direct access to PHI through poorly secured API endpoints, which are rarely vetted thoroughly. According to the Cloud Security Alliance, 29% of healthcare cloud vulnerabilities involve exposed APIs, making them the second-largest attack surface after IAM issues.
Addressing these vulnerabilities is the first step toward safeguarding healthcare systems through rigorous cloud-based vulnerability testing practices.
Best Practices for Cloud-Based Vulnerability Testing
After identifying common cloud vulnerabilities, healthcare organizations need to implement structured testing practices to manage risks effectively. The strategies outlined below aim to reduce exposure time and prevent breaches from occurring.
Continuous Automated Scanning
Relying on manual assessments can’t keep up with the fast-paced nature of cloud deployments. Automated scanning tools, like AWS Inspector or Azure Defender, detect vulnerabilities in real time, allowing for quicker fixes. In fact, organizations using these tools report up to 90% faster remediation compared to those relying on quarterly manual scans. For critical assets, scheduling scans every 15–60 minutes is ideal. These tools work seamlessly with cloud providers through IAM roles, automatically flagging issues such as unpatched software, exposed S3 buckets, or misconfigured security groups. To ensure immediate action, set up alerts that notify teams via platforms like Slack or Microsoft Teams.
Taking this a step further, integrating these automated tools into CI/CD pipelines ensures vulnerabilities are caught even earlier, further reducing the risk of exposure.
Integrating Vulnerability Testing with CI/CD Pipelines
Embedding security tests directly into CI/CD pipelines is a game-changer. Tools like Snyk, SonarQube, or Checkmarx can create pre-production checkpoints, which are far less expensive and disruptive than addressing vulnerabilities after deployment. For example, Mayo Clinic integrated Snyk into their Azure DevOps pipelines, catching 85% of vulnerabilities before deployment and cutting their mean time to remediate from 14 days to just 2 days. Similarly, Cleveland Clinic used GitLab's security features to prevent over 200 high-risk issues annually, achieving zero PHI breaches.
Organizations that adopt this approach typically fix three times as many critical vulnerabilities before they reach production. Early detection during development, paired with a risk-based strategy, ensures that resources focus on the most critical threats.
Risk-Based Prioritization of Vulnerabilities
Not every vulnerability demands immediate attention. A risk-based approach evaluates CVSS scores alongside healthcare-specific concerns, such as impacts on PHI access, patient safety, and HIPAA compliance. Vulnerabilities affecting clinical systems should be prioritized due to their potential impact on patient safety and sensitive data.
Healthcare organizations should initially focus on the top 10% of vulnerabilities affecting clinical systems. According to the Verizon DBIR 2024, 60% of healthcare breaches stem from unaddressed misconfigurations. To stay on top of this, track key metrics like:
- Mean time to remediate critical issues under 48 hours
- Vulnerability density per 1,000 lines of code
- Remediation rates above 95% within SLA windows
High-risk vulnerabilities with CVSS scores of 9 or higher are 2.5 times more likely to be exploited in healthcare settings. However, prioritizing these risks effectively can reduce breach costs by 40%, as reported by the Ponemon Institute (2023).
Using Censinet RiskOps for Vulnerability Management

Censinet RiskOps™ simplifies vulnerability management for healthcare organizations, particularly those relying on cloud-based applications. Healthcare providers often face challenges like managing PHI, addressing vendor risks, and meeting HIPAA compliance. Censinet RiskOps centralizes these workflows, tailoring them specifically for healthcare delivery systems and their vendors. By incorporating established cloud vulnerability testing practices, it offers a unified platform to manage these complexities effectively.
Automated Workflows and AI-Powered Assessments
Censinet RiskOps™ automates the entire vulnerability assessment and remediation process, making risk management faster and more efficient. The platform integrates seamlessly with cloud environments like AWS and Azure, identifying misconfigurations and API vulnerabilities in real time. For example, it can instantly scan code commits in clinical applications to check for PHI exposure, cutting assessment times from weeks to just hours.
The platform uses AI to analyze vulnerabilities, focusing on healthcare-specific threats. It prioritizes risks based on CVSS scores and their potential impact on HIPAA compliance. Machine learning capabilities predict breach risks from cloud misconfigurations and offer actionable recommendations, such as "patch this API endpoint within 24 hours." In fact, industry benchmarks highlight a 40% reduction in false positives, which helps streamline the triage process.
Censinet RiskOps also updates residual risk ratings automatically by pulling in vendor data. It identifies security gaps from questionnaire responses and generates corrective action plans (CAPs) with in-platform tracking. By connecting through webhooks and APIs, the platform integrates with CI/CD pipelines, automatically halting builds if critical vulnerabilities - like exposed PHI - are detected.
Centralized Risk Visualization and Reporting
In addition to automation, Censinet RiskOps provides centralized visualization tools that turn raw data into actionable insights. Interactive dashboards display vulnerability heat maps, real-time PHI metrics, and trends in misconfigurations. Users can drill down into third-party integrations or export HIPAA-compliant visuals for executive-level reporting. This centralized command center serves as a single source of truth for monitoring vulnerabilities across clinical applications, medical devices, and supply chains.
The platform also auto-generates detailed reports, including timelines of vulnerabilities, remediation progress, and HIPAA compliance mappings. Customizable templates feature risk scores and evidence logs from cloud scans, simplifying SOC 2 audit preparation with one-click PDF exports. According to industry data, organizations using Censinet reduce third-party risk assessment times by 60% and see a 35% improvement in compliance scores.
Table: Censinet RiskOps Plans for Vulnerability Testing
| Feature | Platform | Hybrid Mix | Managed Services |
|---|---|---|---|
| Automated Cloud Scans | Yes | Yes | Yes |
| AI Risk Prioritization | Basic | Advanced | Full |
| Custom API Integrations | Limited | Yes | Unlimited |
| 24/7 Monitoring | No | Partial | Yes |
| HIPAA Report Templates | Standard | Custom | Expert-reviewed |
| Risk Management Approach | Self-service software | Software + managed services | Fully outsourced |
The Platform plan is ideal for organizations with in-house security teams, offering full software access. The Hybrid Mix plan combines software with expert guidance and custom integrations, catering to specific organizational needs. For those requiring a more hands-off approach, the Managed Services plan delivers end-to-end support, including 24/7 monitoring, triage, and dedicated analysts for complex healthcare cloud environments. Pricing is tailored based on the organization’s size and specific requirements.
Compliance and Reporting for Healthcare Vulnerability Assessments
Meeting HIPAA Compliance Requirements
The HIPAA Security Rule (45 CFR § 164.308(a)(8)) mandates that healthcare organizations conduct thorough assessments of risks to electronic protected health information (ePHI). These assessments should be performed at least once a year or whenever significant changes occur within your cloud infrastructure. For cloud-based systems, vulnerability testing must address key areas such as access controls (§ 164.312(a)(1)), audit controls (§ 164.312(b)), and transmission security (§ 164.312(e)) to safeguard against unauthorized access and potential breaches.
It's critical to maintain detailed records of these assessments for six years. This includes documentation such as scan dates, results, and approver signatures. A real-world example highlights the importance of compliance: In September 2023, Change Healthcare faced a $22 million fine after unpatched Citrix vulnerabilities exposed PHI affecting one-third of Americans. The lack of timely assessments and proper documentation worsened the situation. Following this breach, the company revamped its protocols, reducing its mean time to remediate from 90 days to just 14 days by implementing quarterly audits and ensuring patches were applied within 48 hours of discovery.
In addition to HIPAA, other regulations like the HITECH Act require breach notifications and enhanced ePHI security measures. Meanwhile, NIST SP 800-53 fills in some of HIPAA's gaps by providing guidelines for incident response. Together, these frameworks help ensure your cloud vulnerability testing program meets both security and regulatory standards.
Next, let’s look at how to effectively translate vulnerability data into audit-ready reports.
Creating Audit-Ready Reports
Turning raw vulnerability data into well-organized, audit-ready reports is essential for demonstrating compliance. These reports should include several key elements:
- Executive Summary: A high-level overview of the findings.
- Methodology: A detailed explanation of the tools and processes used.
- Findings: Organized by severity, with CVSS scores for context.
- Remediation Timelines: Clear deadlines for addressing vulnerabilities.
- Verification Evidence: Screenshots, logs, or other proof of remediation.
Using standardized formats with timestamps in MM/DD/YYYY format ensures consistency for audits in the U.S. Additionally, organizing findings by severity helps prioritize risks effectively.
Quantitative metrics can further bolster your documentation. For example, you could point out that high-risk vulnerabilities decreased by 40% after testing or that a 99.9% compliance rate was achieved across cloud assets. Ascension Health provides a strong example: after a February 2024 cyberattack, their detailed audit report demonstrated zero repeat vulnerabilities, showcasing effective risk management and avoiding further penalties.
To streamline the process, integrate vulnerability testing data into centralized platforms that track remediation SLAs. Assign specific roles, such as appointing a security officer to oversee approvals, and ensure proper version control for all documentation. Alarmingly, only 24% of healthcare breaches in 2023 involved vulnerabilities that were fully remediated before the incident. This highlights significant gaps in compliance. With HIPAA fines totaling $6.85 million in 2023 for inadequate risk assessments, thorough documentation is not just a regulatory obligation - it’s a smart financial decision. These practices help ensure your cloud vulnerability testing program stays compliant while strengthening overall security.
Conclusion
Healthcare cloud applications are under constant threat from cyberattacks aimed at compromising PHI and clinical systems. With the cost of a single data breach exceeding $10 million, implementing proactive testing measures isn't just advisable - it's essential for safeguarding patient data and ensuring smooth operations.
A continuous, risk-focused approach to vulnerability testing - one that includes automated scanning and checks within CI/CD pipelines - can significantly reduce the time systems remain exposed and detect vulnerabilities before they escalate into breaches. This forward-thinking strategy also sets the stage for tools that simplify and enhance these protective measures.
For healthcare organizations, adopting purpose-built solutions can make all the difference. Censinet RiskOps™ offers a streamlined approach to vulnerability management, combining centralized risk visualization, AI-driven assessments, and automated workflows. These features are especially beneficial for IT teams navigating limited resources while addressing the complex demands of compliance frameworks like HIPAA, HITECH, and NIST.
With audit-ready reports that include timestamps, remediation deadlines, and verification evidence, organizations can demonstrate both compliance and a strong commitment to protecting PHI.
While automated vulnerability testing may cost between $50,000 and $200,000 annually, preventing even a single breach makes the investment worthwhile. By embracing these practices and leveraging tools like Censinet RiskOps™, healthcare providers can protect sensitive data, meet compliance standards, and bolster their overall cybersecurity defenses.
FAQs
How often should we scan our cloud assets for vulnerabilities?
Healthcare organizations must perform vulnerability scans on a regular basis. For environments that handle electronic Protected Health Information (ePHI), industry guidelines suggest conducting scans every quarter. Meanwhile, HIPAA mandates assessments of critical systems at least twice a year. These routine scans are crucial for maintaining compliance and safeguarding sensitive data from potential threats.
What should we prioritize first: IAM, misconfigurations, or APIs?
Healthcare organizations should start by tackling misconfigurations and insecure APIs, as these are frequent weaknesses that can result in data breaches and compliance issues. After addressing these vulnerabilities, the next step is to establish strong Identity and Access Management (IAM) practices. This approach ensures tighter access control and minimizes potential attack vectors. By focusing on these areas in sequence, organizations can deal with the most pressing risks in cloud environments while laying the groundwork for lasting security measures.
What documentation is needed for HIPAA vulnerability testing audits?
Healthcare organizations need to keep detailed records to ensure they can demonstrate compliance during HIPAA vulnerability testing audits. These records should include documented risk analyses, vulnerability scan reports, audit logs, access control records, and proof of technical safeguards like encryption measures and testing results. Having these materials on hand is crucial for showcasing adherence to HIPAA requirements.


