Ultimate Guide to Vendor Compliance Certification
Post Summary
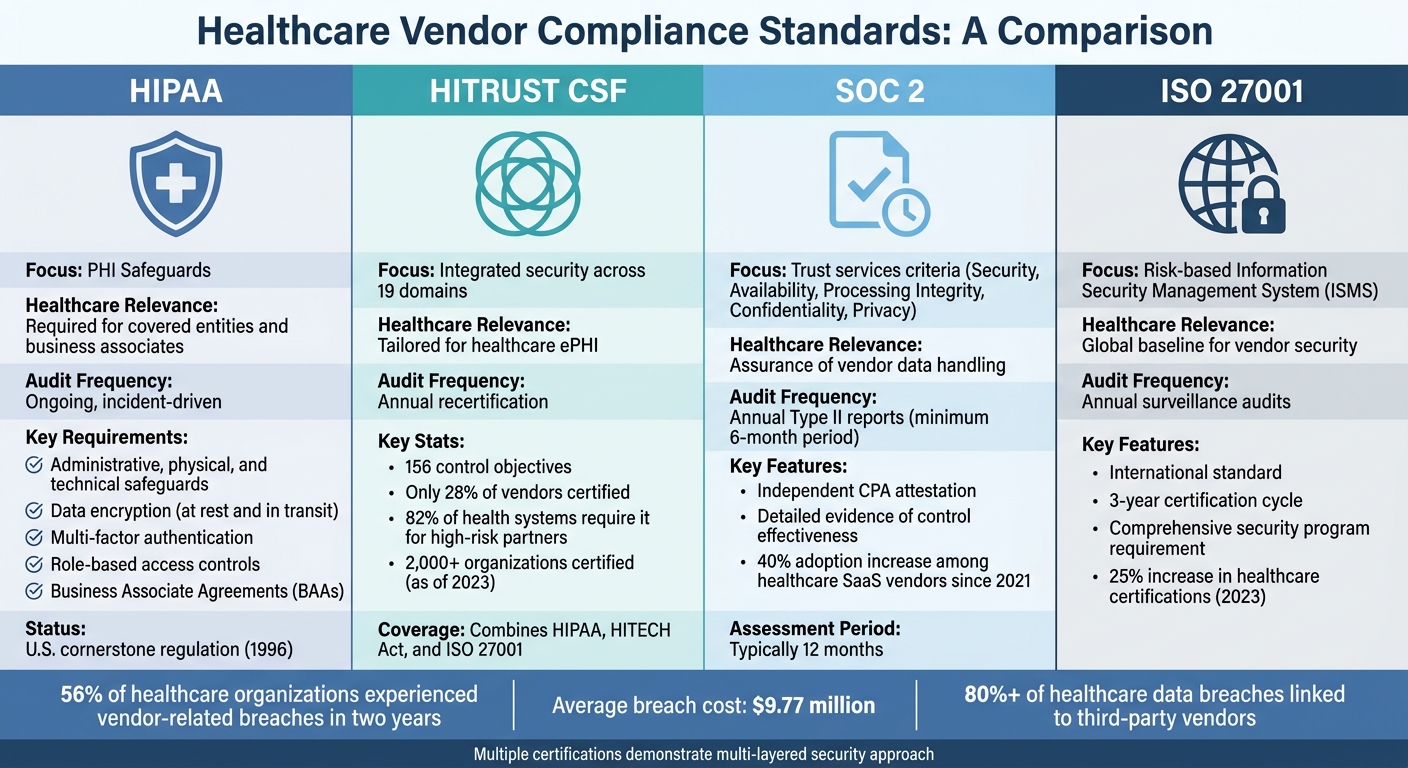
Vendor compliance certification ensures healthcare vendors meet strict regulatory and security standards, protecting sensitive patient data and reducing risks. With 56% of healthcare organizations experiencing vendor-related breaches in two years and breach costs averaging $9.77 million, certification is critical. Having a vendor breach response plan is equally vital to mitigate these costs. Frameworks like HIPAA, HITRUST, SOC 2, and ISO 27001 validate vendor practices, covering areas like data encryption, access controls, and incident response.
Key points:
- HIPAA: Focuses on safeguarding Protected Health Information (PHI) with legal agreements and security measures.
- HITRUST: Combines multiple standards into a detailed framework, often required by healthcare organizations.
- SOC 2: Evaluates vendor security over time, offering transparency through audit reports.
- ISO 27001: Establishes global security benchmarks with a focus on risk management.
To achieve certification, vendors conduct third-party risk assessments, implement security controls, and use automation tools like Censinet RiskOps™ to streamline processes. Continuous monitoring, including regular reviews and certification tracking, ensures compliance stays current.
Healthcare organizations can simplify vendor compliance by leveraging automation and focusing on proactive risk management. This approach safeguards patient trust, reduces liability, and meets regulatory demands.
What Is HIPAA BAA Compliance For Third-party Vendor Access In Healthcare? - AI and Technology Law
sbb-itb-535baee
Regulations and Standards for Vendor Compliance
Healthcare Vendor Compliance Standards Comparison: HIPAA, HITRUST, SOC 2, and ISO 27001
Healthcare vendors are required to meet various regulatory standards to protect Protected Health Information (PHI). These standards - HIPAA, HITRUST, SOC 2, and ISO 27001 - offer clear benchmarks for evaluating vendor security and serve as the basis for vendor compliance certifications. Here's a closer look at the key standards driving vendor compliance.
HIPAA Compliance
HIPAA (Health Insurance Portability and Accountability Act of 1996) is the cornerstone of PHI protection in the United States. Vendors handling, storing, or transmitting patient data for healthcare organizations must adhere to HIPAA's Security Rule and Privacy Rule.
The Security Rule mandates administrative, physical, and technical safeguards for electronic PHI (ePHI). This includes measures like data encryption (both at rest and in transit), multi-factor authentication, role-based access controls, detailed audit logging, and a documented incident response plan. The Privacy Rule further governs how PHI can be used and disclosed, ensuring data remains protected throughout its lifecycle.
Business Associate Agreements (BAAs) are essential legal contracts that outline a vendor's HIPAA responsibilities. These agreements detail how PHI should be handled, breach notification protocols, and permissible uses of patient data. The U.S. Department of Health and Human Services (HHS) advises including audit rights and specific breach notification timelines in every BAA.
HITRUST Certification
While HIPAA establishes basic compliance requirements, HITRUST CSF (Common Security Framework) offers a more detailed and structured approach tailored to healthcare. HITRUST integrates elements from HIPAA, the HITECH Act, and ISO 27001 into a single framework that spans 19 domains and 156 control objectives.
Notably, only 28% of vendors have HITRUST certification, even though 82% of health systems require it for high-risk partners. This gap underscores the rigorous nature of HITRUST's assessment process. Independent assessors evaluate vendor controls in areas such as data protection, risk management, encryption, access control, incident response, and business continuity. To maintain certification, vendors must undergo annual reassessments.
HITRUST has become a benchmark for managing third-party risks in healthcare. Implementing a robust third-party risk management program is essential for navigating these complex standards. As of 2023, over 2,000 organizations have achieved certification, demonstrating their commitment to security beyond HIPAA's minimum requirements. Many healthcare organizations now require HITRUST certification as a prerequisite for vendor relationships, positioning it as a key differentiator in the industry.
SOC 2 and ISO 27001 Standards
SOC 2 and ISO 27001 complement HIPAA and HITRUST by offering additional frameworks to validate security practices. While HIPAA and HITRUST are healthcare-focused, these standards apply across industries.
SOC 2 Type II reports assess controls related to security, availability, processing integrity, confidentiality, and privacy over a minimum six-month period. Unlike certifications, SOC 2 provides audit attestations conducted by independent CPAs. These reports offer detailed evidence of a vendor's control effectiveness over time, typically spanning 12 months. Since 2021, SOC 2 Type II adoption among healthcare SaaS vendors has surged by 40%, reflecting increased demand for continuous monitoring.
ISO 27001, an international standard for Information Security Management Systems (ISMS), requires vendors to establish and maintain a comprehensive security program. Certification lasts three years, with annual surveillance audits to ensure ongoing compliance. In 2023, ISO 27001 certifications in healthcare rose by 25%, highlighting the growing scrutiny on vendors and the importance of global security standards. Many vendors pursue SOC 2 and ISO 27001 alongside HIPAA and HITRUST to demonstrate a multi-layered approach to security.
Together, these standards provide a robust framework for vendor risk management and security validation.
| Standard | Focus | Healthcare Relevance | Audit Frequency |
|---|---|---|---|
| HIPAA | PHI safeguards | Required for covered entities and vendors | Ongoing, incident-driven |
| HITRUST CSF | Integrated security across 19 domains | Tailored for healthcare ePHI | Annual recertification |
| SOC 2 | Trust services criteria | Assurance of vendor data handling | Annual Type 2 reports |
| ISO 27001 | Risk-based ISMS | Global baseline for vendor security | Annual surveillance audits |
How to Achieve Vendor Compliance Certification
To meet compliance certification standards, vendors need a structured approach that combines risk assessments, security controls, and automation. By focusing on identifying vulnerabilities, implementing controls, and leveraging automation, healthcare vendors can align regulatory requirements with practical security measures.
Conducting Risk Assessments
Risk assessments are the cornerstone of compliance certification. Start by examining systems that handle PHI (Protected Health Information). Frameworks like NIST or HITRUST can guide you in identifying threats and common risk assessment questions.
Use a mix of automated vulnerability scans and human analysis to uncover weaknesses. For example, an automated scan might reveal unpatched software exposing PHI, while staff interviews could highlight gaps like weak password policies or unclear data-handling procedures.
Prioritize risks based on their level of exploitability, sensitivity, and regulatory impact. High-risk issues, such as unencrypted data transmission, should be addressed immediately. Common vulnerabilities to tackle first include outdated encryption protocols, insufficient access controls, and a lack of multi-factor authentication.
Once risks are identified and ranked, the next step is implementing security controls to mitigate them.
Implementing Security Controls
Security controls - both technical and administrative - are essential for reducing risks. On the technical side, implement encryption (AES-256) for PHI both at rest and in transit, configure firewalls and intrusion detection systems, and use role-based access control (RBAC) to limit data exposure. Adopting a zero-trust architecture can further minimize unauthorized access.
Administrative measures include employee training, incident response planning, and vendor management policies. Regular testing of these controls - preferably on a quarterly basis - ensures their continued effectiveness. Integrating these controls into DevOps pipelines allows for continuous validation, while annual breach simulation exercises can improve response times by up to 40%, according to experts. These exercises also fulfill audit requirements for preparedness documentation.
While manual controls are crucial, automation can significantly simplify the path to certification.
Using Automation Tools for Compliance
Automation tools can dramatically reduce the time and effort needed for certification. Platforms like Censinet RiskOps™ streamline risk assessments and evidence collection, cutting manual work by as much as 70%. With built-in HIPAA and HITRUST templates, real-time collaboration features, and dashboards for tracking risk scores and audit readiness, these tools make compliance more manageable. Exportable reports formatted for certifiers further simplify the process.
AI-powered features in these tools can analyze risk data, detect anomalies, and predict emerging threats. For instance, a medical device vendor used automation to identify IoT vulnerabilities, implement RBAC and encryption, and achieve HITRUST certification in just six months - 30% faster than traditional methods - while cutting breach risk by 60%, as post-certification metrics revealed.
Automation can reduce certification timelines by up to 50%. Experts recommend conducting quarterly mock audits to uncover gaps ahead of formal assessments. This proactive strategy ensures complete evidence coverage and smooths the path to a successful final audit.
Using Censinet RiskOps™ for Vendor Compliance

Censinet RiskOps™ combines automation, AI, and real-time insights to simplify vendor compliance certification. Built on established risk assessment and automation practices, this platform enhances the efficiency of compliance processes. It’s tailored to support standards like HIPAA, HITRUST, SOC 2, and ISO 27001, seamlessly integrating with existing cybersecurity systems. For healthcare organizations managing vast networks of vendors, Censinet RiskOps™ tackles the challenges of meeting regulatory standards while maintaining operational efficiency.
Automating Risk Assessments
Censinet RiskOps™ reduces manual effort by up to 80% compared to traditional spreadsheet methods. The platform digitizes and standardizes questionnaires, collects vendor responses, and automatically scores risks based on criteria like HIPAA and HITRUST. This process condenses assessment timelines from weeks to days, enabling healthcare organizations to protect patient data, PHI, and medical devices more effectively through HIPAA-compliant vendor risk management.
Pre-built templates for compliance standards such as SOC 2 and ISO 27001 eliminate the need to develop custom frameworks. Organizations can further streamline preparation using a SOC 2 audit documentation checklist. Censinet's automated portals simplify evidence collection by allowing vendors to submit documentation directly, while AI tools validate responses against regulatory benchmarks in real time. This approach flags inconsistencies immediately, cutting review times in half and improving accuracy. As a result, organizations can complete three times more assessments annually without increasing staff.[1][2]
One example involves a major U.S. hospital network that used Censinet RiskOps™ to automate assessments for over 500 vendors. By integrating with existing systems to gather data on supply chain and clinical applications, the platform achieved a 95% vendor response rate within two weeks. This early identification of high-risk suppliers helped the hospital achieve HITRUST-aligned compliance certification ahead of schedule, saving approximately $200,000 in labor costs.[1]
These automation capabilities lay the groundwork for Censinet AI™ to take compliance management to the next level.
AI-Powered Compliance Management
With automated assessments in place, Censinet AI™ enhances risk management by introducing machine learning. Censinet AI™ analyzes vendor responses, predicts risk levels using historical data and industry benchmarks, and suggests real-time remediation actions. It monitors vendor security updates - like changes to medical device firmware - ensuring consistent compliance with HIPAA and SOC 2 without requiring manual reassessments. This approach shortens certification cycles by 40%.[1][3]
The AI also identifies risks proactively by recognizing patterns across multiple vendors, such as vulnerabilities to phishing attacks. Automated mapping to standards like ISO 27001 ensures no compliance gaps are overlooked, while adaptive learning improves assessments as new threats emerge. Cybersecurity leaders report a 60% reduction in compliance audit failures thanks to AI’s continuous benchmarking against evolving risks, including supply chain vulnerabilities.[1][4]
Real-Time Dashboards and Reporting
Customizable dashboards provide real-time insights into compliance scores, risk heat maps, overdue assessments, and trends like PHI exposure risks. Organizations can drill down into vendor-specific data, with alerts highlighting non-compliant areas. Executives can track certification progress through these dashboards, which are tailored to their needs.[1][2]
The platform also generates automated reports, including executive summaries, detailed risk registers, compliance gap analyses, and audit-ready exports aligned with HIPAA and HITRUST requirements. Users produce ten times more reports monthly, featuring visualizations like pie charts that break down risk categories (e.g., 35% supply chain, 25% data security). These reporting tools simplify board presentations and regulatory filings by eliminating the need for manual data compilation.[1]
Maintaining Compliance Through Continuous Monitoring
Vendor compliance certification isn't a one-and-done task - it requires constant attention. As vendor risks shift due to updated policies, expiring certifications, and new regulations, continuous monitoring becomes a must. With over 80% of healthcare data breaches linked to third-party vendors, effectively manage third-party risk is critical to avoid fines and security issues[6]. Relying on static certifications without ongoing tracking can leave organizations vulnerable.
By leveraging automated assessments, continuous monitoring ensures compliance stays up to date.
Tracking Updates and Renewals
Centralized tracking helps stay on top of vendor certification expirations and regulatory changes in real time. Subscribing to alerts from OCR and HHS ensures timely updates on HIPAA regulations. For instance, automated notifications sent 90 days before a certification expires give vendors enough time to renew. One hospital network avoided a $1.5M fine by catching a lapsed HIPAA attestation six months in advance[5].
Tools like RSS feeds (e.g., HHS.gov) and quarterly regulatory scans can help document updates for frameworks like HITRUST or SOC 2. Platforms such as Censinet RiskOps™ simplify this with automated alerts for policy changes and approaching certification expirations[1].
These tools provide a solid base for conducting scheduled reviews to maintain compliance.
Scheduling Periodic Reviews
Automated alerts are just one piece of the puzzle - regular, scheduled reviews are equally important. High-risk vendors should be reviewed annually, while those handling PHI or medical devices may require semi-annual checks. These reviews should use updated questionnaires, recent control evidence, and the latest threat intelligence. Documenting findings ensures a clear audit trail. Review frequencies should align with certification requirements, with SOC 2 reports suggesting quarterly reviews and immediate action for material changes[7][8].
Key performance metrics, like maintaining 100% current vendor certifications and achieving remediation times under 30 days, are essential benchmarks. If a vendor’s SOC 2 report lapses during a review, escalate the issue immediately and set clear remediation plans with defined timelines. Platforms like Censinet RiskOps™ offer dashboards for real-time KPI tracking, helping executives monitor compliance trends and address risks before they lead to regulatory violations[1].
Conclusion
Vendor compliance certification plays a crucial role in shielding healthcare organizations from data breaches, regulatory fines, and operational disruptions. With 82% of breaches tied to third-party vendors and average costs reaching $10.1 million, the risks are too significant to ignore[1]. This guide laid out a clear framework: understanding key regulatory requirements, achieving certification through detailed risk assessments and strong security measures, and maintaining compliance with ongoing monitoring and regular reviews. This approach not only protects patient data but also strengthens operational integrity and simplifies the path to compliance.
While the certification process may seem daunting, automation has revolutionized how organizations tackle it. Automated compliance tools have enabled healthcare providers to cut their risk exposure by 50%, reduce assessment timelines from months to weeks, and decrease manual workloads by up to 70%[1]. Tools like Censinet RiskOps™ are leading this change, offering automated third-party risk assessments, AI-driven compliance management to identify gaps in real time, and user-friendly dashboards to monitor vendor performance across critical areas like patient data, medical devices, and supply chains.
The key to maintaining compliance over the long term is continuous monitoring. Features like automated renewal tracking, real-time alerts for policy changes, and scheduled reviews ensure certifications remain up to date, even as new threats emerge. By combining continuous monitoring with automated assessments, healthcare organizations can stay one step ahead of potential risks.
Ready to simplify your vendor compliance process? Start with a vendor risk assessment using Censinet RiskOps™. Visit censinet.com to schedule a demo and initiate quarterly reviews to keep pace with regulatory changes. The path to effective vendor compliance begins with the right tools and an unwavering focus on improvement.
FAQs
Which vendors should we certify first?
Healthcare organizations need to focus on certifying vendors that present the greatest risks to patient data, regulatory compliance, and operational security. This means prioritizing vendors who handle Protected Health Information (PHI), have access to clinical systems, or provide essential services like electronic health records (EHR) and cybersecurity.
Using risk-based assessments is key to sorting vendors by priority. Vendors managing sensitive data or operating under strict regulatory oversight should be at the top of the list for certification. This approach helps maintain both compliance and security standards.
What evidence should vendors provide for certification?
Vendors need to supply detailed documentation to verify their compliance and security measures. This includes security controls, compliance certifications (like SOC 2, HITRUST, or ISO 27001), HIPAA-related attestations, comprehensive risk assessments, audit reports, and up-to-date certification statuses. Providing these documents not only shows adherence to necessary standards but also supports effective risk management.
How often should vendors be reassessed after certification?
Vendors should be reviewed at least once a year. That said, depending on factors like their risk level, regulatory obligations, or the importance of the services they offer, more frequent evaluations might be necessary. Consistent reassessments help maintain compliance and tackle new risks as they arise.


